How to Find out the IP Address of an Omron
Total Page:16
File Type:pdf, Size:1020Kb
Load more
Recommended publications
-

DC Console Using DC Console Application Design Software
DC Console Using DC Console Application Design Software DC Console is easy-to-use, application design software developed specifically to work in conjunction with AML’s DC Suite. Create. Distribute. Collect. Every LDX10 handheld computer comes with DC Suite, which includes seven (7) pre-developed applications for common data collection tasks. Now LDX10 users can use DC Console to modify these applications, or create their own from scratch. AML 800.648.4452 Made in USA www.amltd.com Introduction This document briefly covers how to use DC Console and the features and settings. Be sure to read this document in its entirety before attempting to use AML’s DC Console with a DC Suite compatible device. What is the difference between an “App” and a “Suite”? “Apps” are single applications running on the device used to collect and store data. In most cases, multiple apps would be utilized to handle various operations. For example, the ‘Item_Quantity’ app is one of the most widely used apps and the most direct means to take a basic inventory count, it produces a data file showing what items are in stock, the relative quantities, and requires minimal input from the mobile worker(s). Other operations will require additional input, for example, if you also need to know the specific location for each item in inventory, the ‘Item_Lot_Quantity’ app would be a better fit. Apps can be used in a variety of ways and provide the LDX10 the flexibility to handle virtually any data collection operation. “Suite” files are simply collections of individual apps. Suite files allow you to easily manage and edit multiple apps from within a single ‘store-house’ file and provide an effortless means for device deployment. -
Disk Clone Industrial
Disk Clone Industrial USER MANUAL Ver. 1.0.0 Updated: 9 June 2020 | Contents | ii Contents Legal Statement............................................................................... 4 Introduction......................................................................................4 Cloning Data.................................................................................................................................... 4 Erasing Confidential Data..................................................................................................................5 Disk Clone Overview.......................................................................6 System Requirements....................................................................................................................... 7 Software Licensing........................................................................................................................... 7 Software Updates............................................................................................................................. 8 Getting Started.................................................................................9 Disk Clone Installation and Distribution.......................................................................................... 12 Launching and initial Configuration..................................................................................................12 Navigating Disk Clone.....................................................................................................................14 -

Xerox® Colorqube 8580/8880 Color Printer 3 System Administrator Guide
Xerox® ColorQube® 8580 / 8880 Color Printer Imprimante couleur System Administrator Guide Guide de l’administrateur système © 2015 Xerox Corporation. All rights reserved. Unpublished rights reserved under the copyright laws of the United States. Contents of this publication may not be reproduced in any form without permission of Xerox Corporation. Copyright protection claimed includes all forms of matters of copyrightable materials and information now allowed by statutory or judicial law or hereinafter granted, including without limitation, material generated from the software programs which are displayed on the screen such as styles, templates, icons, screen displays, looks, and so on. Xerox® and Xerox and Design®, Phaser®, PhaserSMART®, PhaserMatch®, PhaserCal®, PhaserMeter™, CentreWare®, PagePack®, eClick®, PrintingScout®, Walk-Up®, WorkCentre®, FreeFlow®, SMARTsend®, Scan to PC Desktop®, MeterAssistant®, SuppliesAssistant®, Xerox Secure Access Unified ID System®, Xerox Extensible Interface Platform®, ColorQube®, Global Print Driver®, and Mobile Express Driver® are trademarks of Xerox Corporation in the United States and/or other countries. Adobe® Reader®, Adobe® Type Manager®, ATM™, Flash®, Macromedia®, Photoshop®, and PostScript® are trademarks of Adobe Systems Incorporated in the United States and/or other countries. Apple, Bonjour, EtherTalk, TrueType, iPad, iPhone, iPod, iPod touch, Mac and Mac OS are trademarks of Apple Inc., registered in the U.S. and other countries. AirPrint and the AirPrint logo are trademarks of Apple Inc. HP-GL®, HP-UX®, and PCL® are trademarks of Hewlett-Packard Corporation in the United States and/or other countries. IBM® and AIX® are trademarks of International Business Machines Corporation in the United States and/or other countries. Microsoft®, Windows Vista®, Windows®, and Windows Server® are trademarks of Microsoft Corporation in the United States and other countries. -
Cs-204: Computer Networks
CS-204: COMPUTER NETWORKS Lecture 5 Chapter 19- Network Layer: Logical Addressing Instructor: Dr. Vandana Kushwaha 1. INTRODUCTION Communication at the network layer is host-to-host (computer-to-computer); a computer somewhere in the world needs to communicate with another computer somewhere else in the world. Usually, computers communicate through the Internet. The packet transmitted by the sending computer may pass through several LANs or WANs before reaching the destination computer. For this level of communication, we need a global addressing scheme; we called this logical addressing or IP address. 2. IPv4 ADDRESSES An IPv4 address is a 32-bit address that uniquely and universally defines the connection of a device (for example, a computer or a router) to the Internet. IPv4 addresses are unique. They are unique in the sense that each address defines one, and only one, connection to the Internet. Two devices on the Internet can never have the same address at the same time. But by using some strategies, an address may be assigned to a device for a time period and then taken away and assigned to another device. On the other hand, if a device operating at the network layer has m connections to the Internet, it needs to have m addresses. A router is such a device which needs as many IP addresses as the number of ports are there in it. 2.1. Address Space A protocol such as IPv4 that defines addresses has an address space. An address space is the total number of addresses used by the protocol. If a protocol uses N bits to define an address, the address space is 2N because each bit can have two different values (0 or 1) and N bits can have 2N values. -
Multitech Bluetooth Network Access Point Administrator Guide S000619 Rev 1.2 for Use with Model: MT200B2E
MultiTech Bluetooth® Network Access Point Administrator Guide MultiTech Bluetooth Network Access Point Administrator Guide S000619 Rev 1.2 For use with model: MT200B2E Copyright This publication may not be reproduced, in whole or in part, without the specific and express prior written permission signed by an executive officer of Multi-Tech Systems, Inc. All rights reserved. Copyright © 2015 by Multi-Tech Systems, Inc. Multi-Tech Systems, Inc. makes no representations or warranties, whether express, implied or by estoppels, with respect to the content, information, material and recommendations herein and specifically disclaims any implied warranties of merchantability, fitness for any particular purpose and non- infringement. Multi-Tech Systems, Inc. reserves the right to revise this publication and to make changes from time to time in the content hereof without obligation of Multi-Tech Systems, Inc. to notify any person or organization of such revisions or changes. Trademarks MultiTech, MultiConnect, and the MultiTech logo are registered trademarks of Multi-Tech Systems, Inc. Bluetooth is a registered trademark of Bluetooth SIG, Inc. All other brand and product names are trademarks or registered trademarks of their respective companies. Contacting MultiTech Knowledge Base The Knowledge Base provides immediate access to support information and resolutions for all MultiTech products. Visit http://www.multitech.com/kb.go. Support Portal To create an account and submit a support case directly to our technical support team, visit: https://support.multitech.com Support Business Hours: M-F, 9am to 5pm CT Country By Email By Phone Europe, Middle East, Africa: [email protected] +(44) 118 959 7774 U.S., Canada, all others: [email protected] (800) 972-2439 or (763) 717-5863 World Headquarters Multi-Tech Systems, Inc. -

Problem Solving and Unix Tools
Problem Solving and Unix Tools Command Shell versus Graphical User Interface • Ease of use • Interactive exploration • Scalability • Complexity • Repetition Example: Find all Tex files in a directory (and its subdirectories) that have not changed in the past 21 days. With an interactive file roller, it is easy to sort files by particular characteristics such as the file extension and the date. But this sorting does not apply to files within subdirectories of the current directory, and it is difficult to apply more than one sort criteria at a time. A command line interface allows us to construct a more complex search. In unix, we find the files we are after by executing the command, find /home/nolan/ -mtime +21 -name ’*.tex’ To find out more about a command you can read the online man pages man find or you can execute the command with the –help option. In this example, the standard output to the screen is piped into the more command which formats it to dispaly one screenful at a time. Hitting the space bar displays the next page of output, the return key displays the next line of output, and the ”q” key quits the display. find --help | more Construct Solution in Pieces • Solve a problem by breaking down into pieces and building back up • Typing vs automation • Error messages - experimentation 1 Example: Find all occurrences of a particular string in several files. The grep command searches the contents of files for a regular expression. In this case we search for the simple character string “/stat141/FINAL” in all files in the directory WebLog that begin with the filename “access”. -

What Is UNIX? the Directory Structure Basic Commands Find
What is UNIX? UNIX is an operating system like Windows on our computers. By operating system, we mean the suite of programs which make the computer work. It is a stable, multi-user, multi-tasking system for servers, desktops and laptops. The Directory Structure All the files are grouped together in the directory structure. The file-system is arranged in a hierarchical structure, like an inverted tree. The top of the hierarchy is traditionally called root (written as a slash / ) Basic commands When you first login, your current working directory is your home directory. In UNIX (.) means the current directory and (..) means the parent of the current directory. find command The find command is used to locate files on a Unix or Linux system. find will search any set of directories you specify for files that match the supplied search criteria. The syntax looks like this: find where-to-look criteria what-to-do All arguments to find are optional, and there are defaults for all parts. where-to-look defaults to . (that is, the current working directory), criteria defaults to none (that is, select all files), and what-to-do (known as the find action) defaults to ‑print (that is, display the names of found files to standard output). Examples: find . –name *.txt (finds all the files ending with txt in current directory and subdirectories) find . -mtime 1 (find all the files modified exact 1 day) find . -mtime -1 (find all the files modified less than 1 day) find . -mtime +1 (find all the files modified more than 1 day) find . -

INTRODUCTION to SUBNETTING How to Maximize Network Addresses
Volume 1 • Issue 8 September–October 2000 Introduction to Industrial Ethernet, Part 5. Part 4 was featured in Issue 6, the MAY–JUNE 2000. If you would like a copy, please send your request to EXTENSION [email protected] A Technical Supplement to control NETWORK © 2000 Contemporary Control Systems, Inc. INTRODUCTION TO SUBNETTING How to maximize network addresses. By George Thomas, Contemporary Controls INTRODUCTION address to distinguish it from the Class Addressing other computers. With IP In a previous article we discussed addressing, servers and IPv4 is called a classful system the Internet Protocol and the workstations are all termed hosts under RFC 761 with IP addresses structure of IP addresses. An IP but each address not only identifies being defined as belonging to one address identifies the source and a host but the address of the of five classes A, B, C, D or E. destination of a directed or unicast network on which the host resides. Classes A, B and C define different possible combinations of network message and is defined in RFC 761. This is because IP is an and host addresses. Class D is IPv4 is the most common version internetworking protocol that not reserved for multicasting. of IP addressing requiring 32-bit only allows communication Multicasting is the ability of one addresses. Although IPv6, the 128- between hosts on the same host to communicate with many bit version, will be used in the network, but communication other hosts with one transmission future, this article will restrict the between hosts on different and is beyond the scope of this discussion to IPv4. -

Lecture 17 the Shell and Shell Scripting Simple Shell Scripts
Lecture 17 The Shell and Shell Scripting In this lecture • The UNIX shell • Simple Shell Scripts • Shell variables • File System commands, IO commands, IO redirection • Command Line Arguments • Evaluating Expr in Shell • Predicates, operators for testing strings, ints and files • If-then-else in Shell • The for, while and do loop in Shell • Writing Shell scripts • Exercises In this course, we need to be familiar with the "UNIX shell". We use it, whether bash, csh, tcsh, zsh, or other variants, to start and stop processes, control the terminal, and to otherwise interact with the system. Many of you have heard of, or made use of "shell scripting", that is the process of providing instructions to shell in a simple, interpreted programming language . To see what shell we are working on, first SSH into unix.andrew.cmu.edu and type echo $SHELL ---- to see the working shell in SSH We will be writing our shell scripts for this particular shell (csh). The shell scripting language does not fit the classic definition of a useful language. It does not have many of the features such as portability, facilities for resource intensive tasks such as recursion or hashing or sorting. It does not have data structures like arrays and hash tables. It does not have facilities for direct access to hardware or good security features. But in many other ways the language of the shell is very powerful -- it has functions, conditionals, loops. It does not support strong data typing -- it is completely untyped (everything is a string). But, the real power of shell program doesn't come from the language itself, but from the diverse library that it can call upon -- any program. -
Learning Objectives ECHO Commands. Command. 10. Explain
. SA Learning Objectives After completing this chapter you will be able to: 1. List commands used in batch files. 2. List and explain batch file rules. 3. Use a batch file with a shortcut. 3. Explore the function of the REM, 4. Use the SHIFT command to move param- ECHO commands. eters. 4. Explain the use of batch files with shortcuts. 5. Use the IF command with strings for condi- 5. Explain the purpose and function of the tional processing. GOTO command. 6. Test for null values in a batch file. 6. Explain the purpose and function of the 7. Use the IF EXIST /IF SHIFT command. test for the existence of a file or a 7. Explain the purpose and function of the IF subdirectory. command. 8. Use the SET command. 8. Explain the purpose and function of the IF 9. Use the environment and environmental EXIST /IF variables in batch files. 9. Explain the purpose and function of the IF 10. Use the IF ERRORLEVEL command ERRORLEVEL command. XCOpy to write a batch file for testing exit 10. Explain the purpose and function of writing codes. programs. 11. Use the FOR...IN...OO command for repeti- 11. Explain the purpose and function of the tive processing. environment and environmental variables. 12. Use the CALL command in a batch file. 12. Explain the use of the SET command. 13. Explain the purpose and function of the Chapter Overview FOR...IN...OO command. You learned in Chapter 10 how to write simple 14. Explain the purpose and function of the batch files and use replaceable parameters. -

Linux Shell Script to Find Kernel Version from Multiple Servers Linux Shell Script That Will Login to Server Via Ssh and Get Kernel Version Via Uname -R Command
Linux Shell Script To Find Kernel Version From Multiple Servers Linux shell script that will login to server via ssh and get kernel version via uname -r command. List of all the servers are in server_list.txt file, script will take name by name and try to ssh with the root user and run uname -r command. Output will be written to variable and after into file with servername. This script helps system administrator who manage large linux servers , to take reports of what linux versions running. Here I have used uname -r but you can edit and use your own command as per your requirements. Source : http://linoxide.com/linux-shell-script/kernel-version-multiple/ Linux Shell Script #!/bin/bash #we user variable serverlist to keep there path to file with server names serverlist=’server_list.txt’ #we write in variable all server list servers=`cat $serverlist` #we use variable result to keep there path to file with result result=’result.txt’ #this print header to file with resilt using \t\t to add 2 tab symbols echo -e “Servername \t\t kernel version”> $result #this get each line of serverlist one by one and write to server variable for server in $servers do #this login to server by ssh and get uname -r kernel=`ssh root@${server} “uname -r”` #this write server name and kernel version separated by 2 tab to result file echo -e “$server \t\t $kernel” >> $result #end of for loop. done server_list.txt file # cat server_list.txt dev Linux Shell Script To Find Kernel Version From Multiple Servers 1 www.linoxide.com web1 svn Shell Script Output ./kernel_version.sh centos_node1@bobbin:~/Documents/Work/Bobbin$ cat result.txt Servername kernel version dev 3.3.8-gentoo web1 3.2.12-gentoo svn 3.2.12-gentoo Linux Shell Script To Find Kernel Version From Multiple Servers 2 www.linoxide.com. -
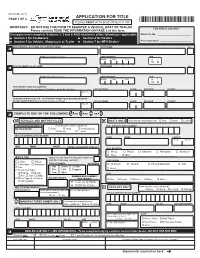
Application for Title (MV-82TON)
MV-82TON (9/21) APPLICATION FOR TITLE PAGE 1 OF 2 PLEASE PRINT WITH BLUE OR BLACK INK *MV-82TON* IMPORTANT– DO NOT USE THIS FORM TO REGISTER A VEHICLE, BOAT OR TRAILER FOR OFFICE USE ONLY Please carefully READ THE INFORMATION ON PAGE 2 of this form. Batch File No. __________________________ Everyone must complete Sections 1, 3 and 6 AND whichever of the following is applicable: •• Section 2 for Co-Owners • Section 4 for Dealers •• Section 5 for Vehicle, Motorcycle or Trailer • Section 7 for MFH Dealers Proof Submitted ________________________ NEW OWNER’S LAST NAME (OR COMPANY NAME) FIRST NAME M.I. 1 ID NO. (from Driver LIcense) DATE OF BIRTH SEX Month Day Year M F •••• NEW CO-OWNER’S LAST NAME FIRST NAME M.I. 2 ID NO. (from Driver LIcense) DATE OF BIRTH SEX Month Day Year M F •••• NEW OWNER’S MAILING ADDRESS (include Street Number and Name, Rural Deliery and/or Box Number) CITY OR TOWN STATE ZIP CODE COUNTY Apt. No. ADDRESS WHERE YOU LIVE – IF DIFFERENT FROM YOUR MAILING ADDRESS – DO NOT GIVE PO BOX (Include Street Number and Name) CITY OR TOWN STATE ZIP CODE COUNTY Apt. No. 3 COMPLETE ONE OF THE FOLLOWING: A OR B OR C OR D • •• •• A VEHICLES AND MOTORCYCLES B BOATS ONLY How was the boat obtained?•• New Used Leased FOR OFFICE USE ONLY How was the vehicle obtained?•• HULL IDENTIFICATION NUMBER MILEAGE BRAND •• New ••Used ••Lease Buyout •••••••Salvage ••Leased VEHICLE IDENTIFICATION NUMBER YEAR MAKE LENGTH Feet Inches YEAR MAKE COLOR ODOMETER READING IN MILES * HULL MATERIAL ••• •••Wood ••Plastic • •Inflatable ••Fiberglass ••Aluminum •