Developing Security-Enhanced Model for Enterprise Network ﻟﻟﺷﺑﮐﺎت
Total Page:16
File Type:pdf, Size:1020Kb
Load more
Recommended publications
-
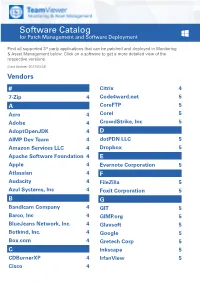
Software Catalog for Patch Management and Software Deployment
Software Catalog for Patch Management and Software Deployment Find all supported 3rd party applications that can be patched and deployed in Monitoring & Asset Management below. Click on a software to get a more detailed view of the respective versions. (Last Update: 2021/03/23) Vendors # Citrix 4 7-Zip 4 Code4ward.net 5 A CoreFTP 5 Acro 4 Corel 5 Adobe 4 CrowdStrike, Inc 5 AdoptOpenJDK 4 D AIMP Dev Team 4 dotPDN LLC 5 Amazon Services LLC 4 Dropbox 5 Apache Software Foundation 4 E Apple 4 Evernote Corporation 5 Atlassian 4 F Audacity 4 FileZilla 5 Azul Systems, Inc 4 Foxit Corporation 5 B G Bandicam Company 4 GIT 5 Barco, Inc 4 GIMP.org 5 BlueJeans Network, Inc. 4 Glavsoft 5 Botkind, Inc. 4 Google 5 Box.com 4 Gretech Corp 5 C Inkscape 5 CDBurnerXP 4 IrfanView 5 Cisco 4 Software Catalog for Patch Management and Software Deployment J P Jabra 5 PeaZip 10 JAM Software 5 Pidgin 10 Juraj Simlovic 5 Piriform 11 K Plantronics, Inc. 11 KeePass 5 Plex, Inc 11 L Prezi Inc 11 LibreOffice 5 Programmer‘s Notepad 11 Lightning UK 5 PSPad 11 LogMeIn, Inc. 5 Q M QSR International 11 Malwarebytes Corporation 5 Quest Software, Inc 11 Microsoft 6 R MIT 10 R Foundation 11 Morphisec 10 RarLab 11 Mozilla Foundation 10 Real 11 N RealVNC 11 Neevia Technology 10 RingCentral, Inc. 11 NextCloud GmbH 10 S Nitro Software, Inc. 10 Scooter Software, Inc 11 Nmap Project 10 Siber Systems 11 Node.js Foundation 10 Simon Tatham 11 Notepad++ 10 Skype Technologies S.A. -
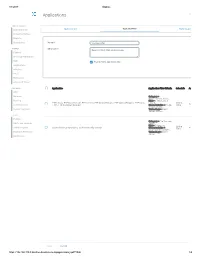
Applications Log Viewer
4/1/2017 Sophos Applications Log Viewer MONITOR & ANALYZE Control Center Application List Application Filter Traffic Shaping Default Current Activities Reports Diagnostics Name * Mike App Filter PROTECT Description Based on Block filter avoidance apps Firewall Intrusion Prevention Web Enable Micro App Discovery Applications Wireless Email Web Server Advanced Threat CONFIGURE Application Application Filter Criteria Schedule Action VPN Network Category = Infrastructure, Netw... Routing Risk = 1-Very Low, 2- FTPS-Data, FTP-DataTransfer, FTP-Control, FTP Delete Request, FTP Upload Request, FTP Base, Low, 4... All the Allow Authentication FTPS, FTP Download Request Characteristics = Prone Time to misuse, Tra... System Services Technology = Client Server, Netwo... SYSTEM Profiles Category = File Transfer, Hosts and Services Confe... Risk = 3-Medium Administration All the TeamViewer Conferencing, TeamViewer FileTransfer Characteristics = Time Allow Excessive Bandwidth,... Backup & Firmware Technology = Client Server Certificates Save Cancel https://192.168.110.3:4444/webconsole/webpages/index.jsp#71826 1/4 4/1/2017 Sophos Application Application Filter Criteria Schedule Action Applications Log Viewer Facebook Applications, Docstoc Website, Facebook Plugin, MySpace Website, MySpace.cn Website, Twitter Website, Facebook Website, Bebo Website, Classmates Website, LinkedIN Compose Webmail, Digg Web Login, Flickr Website, Flickr Web Upload, Friendfeed Web Login, MONITOR & ANALYZE Hootsuite Web Login, Friendster Web Login, Hi5 Website, Facebook Video -
Netcat and Trojans/Backdoors
Netcat and Trojans/Backdoors ECE4883 – Internetwork Security 1 Agenda Overview • Netcat • Trojans/Backdoors ECE 4883 - Internetwork Security 2 Agenda Netcat • Netcat ! Overview ! Major Features ! Installation and Configuration ! Possible Uses • Netcat Defenses • Summary ECE 4883 - Internetwork Security 3 Netcat – TCP/IP Swiss Army Knife • Reads and Writes data across the network using TCP/UDP connections • Feature-rich network debugging and exploration tool • Part of the Red Hat Power Tools collection and comes standard on SuSE Linux, Debian Linux, NetBSD and OpenBSD distributions. • UNIX and Windows versions available at: http://www.atstake.com/research/tools/network_utilities/ ECE 4883 - Internetwork Security 4 Netcat • Designed to be a reliable “back-end” tool – to be used directly or easily driven by other programs/scripts • Very powerful in combination with scripting languages (eg. Perl) “If you were on a desert island, Netcat would be your tool of choice!” - Ed Skoudis ECE 4883 - Internetwork Security 5 Netcat – Major Features • Outbound or inbound connections • TCP or UDP, to or from any ports • Full DNS forward/reverse checking, with appropriate warnings • Ability to use any local source port • Ability to use any locally-configured network source address • Built-in port-scanning capabilities, with randomizer ECE 4883 - Internetwork Security 6 Netcat – Major Features (contd) • Built-in loose source-routing capability • Can read command line arguments from standard input • Slow-send mode, one line every N seconds • Hex dump of transmitted and received data • Optional ability to let another program service established connections • Optional telnet-options responder ECE 4883 - Internetwork Security 7 Netcat (called ‘nc’) • Can run in client/server mode • Default mode – client • Same executable for both modes • client mode nc [dest] [port_no_to_connect_to] • listen mode (-l option) nc –l –p [port_no_to_connect_to] ECE 4883 - Internetwork Security 8 Netcat – Client mode Computer with netcat in Client mode 1. -

The Application Usage and Risk Report an Analysis of End User Application Trends in the Enterprise
The Application Usage and Risk Report An Analysis of End User Application Trends in the Enterprise 8th Edition, December 2011 Palo Alto Networks 3300 Olcott Street Santa Clara, CA 94089 www.paloaltonetworks.com Table of Contents Executive Summary ........................................................................................................ 3 Demographics ............................................................................................................................................. 4 Social Networking Use Becomes More Active ................................................................ 5 Facebook Applications Bandwidth Consumption Triples .......................................................................... 5 Twitter Bandwidth Consumption Increases 7-Fold ................................................................................... 6 Some Perspective On Bandwidth Consumption .................................................................................... 7 Managing the Risks .................................................................................................................................... 7 Browser-based Filesharing: Work vs. Entertainment .................................................... 8 Infrastructure- or Productivity-Oriented Browser-based Filesharing ..................................................... 9 Entertainment Oriented Browser-based Filesharing .............................................................................. 10 Comparing Frequency and Volume of Use -

Metadefender Core V4.12.2
MetaDefender Core v4.12.2 © 2018 OPSWAT, Inc. All rights reserved. OPSWAT®, MetadefenderTM and the OPSWAT logo are trademarks of OPSWAT, Inc. All other trademarks, trade names, service marks, service names, and images mentioned and/or used herein belong to their respective owners. Table of Contents About This Guide 13 Key Features of Metadefender Core 14 1. Quick Start with Metadefender Core 15 1.1. Installation 15 Operating system invariant initial steps 15 Basic setup 16 1.1.1. Configuration wizard 16 1.2. License Activation 21 1.3. Scan Files with Metadefender Core 21 2. Installing or Upgrading Metadefender Core 22 2.1. Recommended System Requirements 22 System Requirements For Server 22 Browser Requirements for the Metadefender Core Management Console 24 2.2. Installing Metadefender 25 Installation 25 Installation notes 25 2.2.1. Installing Metadefender Core using command line 26 2.2.2. Installing Metadefender Core using the Install Wizard 27 2.3. Upgrading MetaDefender Core 27 Upgrading from MetaDefender Core 3.x 27 Upgrading from MetaDefender Core 4.x 28 2.4. Metadefender Core Licensing 28 2.4.1. Activating Metadefender Licenses 28 2.4.2. Checking Your Metadefender Core License 35 2.5. Performance and Load Estimation 36 What to know before reading the results: Some factors that affect performance 36 How test results are calculated 37 Test Reports 37 Performance Report - Multi-Scanning On Linux 37 Performance Report - Multi-Scanning On Windows 41 2.6. Special installation options 46 Use RAMDISK for the tempdirectory 46 3. Configuring Metadefender Core 50 3.1. Management Console 50 3.2. -

Free Open Source Vnc
Free open source vnc click here to download TightVNC - VNC-Compatible Remote Control / Remote Desktop Software. free for both personal and commercial usage, with full source code available. TightVNC - VNC-Compatible Remote Control / Remote Desktop Software. It's completely free but it does not allow integration with closed-source products. UltraVNC: Remote desktop support software - Remote PC access - remote desktop connection software - VNC Compatibility - FileTransfer - Encryption plugins - Text chat - MS authentication. This leading-edge, cloud-based program offers Remote Monitoring & Management, Remote Access &. Popular open source Alternatives to VNC Connect for Linux, Windows, Mac, Self- Hosted, BSD and Free Open Source Mac Windows Linux Android iPhone. Download the original open source version of VNC® remote access technology. Undeniably, TeamViewer is the best VNC in the market. Without further ado, here are 8 free and some are open source VNC client/server. VNC remote access software, support server and viewer software for on demand remote computer support. Remote desktop support software for remote PC control. Free. All VNCs Start from the one piece of source (See History of VNC), and. TigerVNC is a high- performance, platform-neutral implementation of VNC (Virtual Network Computing), Besides the source code we also provide self-contained binaries for bit and bit Linux, installers for Current list of open bounties. VNC (Virtual Network Computing) software makes it possible to view and fully- interact with one computer from any other computer or mobile. Find other free open source alternatives for VNC. Open source is free to download and remember that open source is also a shareware and freeware alternative. -

Remote Process Control Over the Internet
Session 1520 Remote Process Control over the Internet Mark Smith Purdue University North Central Abstract This paper presents remote process control over the Internet using remote-control computing software. Remote-control computing software allows you to connect to remote computers from your computer and control those systems. You can monitor and control attached system processes, provide problem solving assistance, upload and download files, and even change system parameters. This paper describes what remote-control computing is, who the major players in the industry are, and how it can be used to monitor and control remote processes. A case study of remote-control computing software in operation is also presented, describing how one off-the-shelf package was setup to monitor and control a plant floor production system. Introduction Networking technologies, and especially the Internet, have become a major component of application systems. As we teach the design and implementation of process control systems in the Engineering curriculum, we must recognize that these systems will require capabilities for control and support from remote locations. For example, the need for remote control may be driven by the high cost of a particular process. The Oak Ridge National Laboratory uses remote process control at its High Temperature Materials Laboratory to allow researches from across the country to use a million-dollar electron microscope1. Even when control of the process is not required across the country, there are times when it is helpful (or even critical) to monitor another node on a LAN. For example, Conquergood describes in his research the ability to monitor and control potentially high voltages from one location by gathering voltage information from PCs doing data acquisition from various plant processes2. -
VNC User Guide 7 About This Guide
VNC® User Guide Version 5.3 December 2015 Trademarks RealVNC, VNC and RFB are trademarks of RealVNC Limited and are protected by trademark registrations and/or pending trademark applications in the European Union, United States of America and other jursidictions. Other trademarks are the property of their respective owners. Protected by UK patent 2481870; US patent 8760366 Copyright Copyright © RealVNC Limited, 2002-2015. All rights reserved. No part of this documentation may be reproduced in any form or by any means or be used to make any derivative work (including translation, transformation or adaptation) without explicit written consent of RealVNC. Confidentiality All information contained in this document is provided in commercial confidence for the sole purpose of use by an authorized user in conjunction with RealVNC products. The pages of this document shall not be copied, published, or disclosed wholly or in part to any party without RealVNC’s prior permission in writing, and shall be held in safe custody. These obligations shall not apply to information which is published or becomes known legitimately from some source other than RealVNC. Contact RealVNC Limited Betjeman House 104 Hills Road Cambridge CB2 1LQ United Kingdom www.realvnc.com Contents About This Guide 7 Chapter 1: Introduction 9 Principles of VNC remote control 10 Getting two computers ready to use 11 Connectivity and feature matrix 13 What to read next 17 Chapter 2: Getting Connected 19 Step 1: Ensure VNC Server is running on the host computer 20 Step 2: Start VNC -

K1000 Ultravnc Guide
K1000 UltraVNC Guide What is Ultra VNC? UltraVNC (sometimes written uVNC) is an open source application for the Microsoft Windows operating system that uses the VNC protocol to control another computer's screen remotely. How it works A VNC system consists of a client, a server , and a communication protocol • The VNC server is the program on the machine that shares its screen. The server passively allows the client to take control of it. • The VNC client (or viewer) is the program that watches, controls, and interacts with the server. The client controls the server. • The VNC protocol (RFB) is very simple, based on one graphic primitive from server to client ("Put a rectangle of pixel data at the specified X,Y position") and event messages from client to server. Example Tutorial UltraVNC in this document: Creating a complete UltraVNC MSI Package for the K1000. - To create a complete MSI package, this tutorial will use a simple third party tool which will collect all your settings your require and bundle it together into a MSI file which can then be deployed from the K1000. Tutorial - UltraVNC MSI Package I. Install the UlraVNC MSI creator. A. Download VNCed MSI creator from here. (http://prdownloads.sourceforge.net/vnced/VNCed_UltraVNC_MSI_CREATOR_121.zip?download) B. Unzip VNCed MSI creator zip file Indigo Mountain Co Reg No: 7039194 Registered VAT No: 113 2991 31 II. Configure UltraVNC Settings A. Inside the VNCed folder run: UltraVNC 1.0.9.6.1 - STEP1.config_ultravnc_64bit_settings.bat for x64 UltraVNC 1.0.9.6.1 - STEP1.config_ultravnc_settings.bat for x86 Indigo Mountain Co Reg No: 7039194 Registered VAT No: 113 2991 31 B. -

Unpermitted Resources
Process Check and Unpermitted Resources Common and Important Virtual Machines Parallels VMware VirtualBox CVMCompiler Windows Virtual PC Other Python Citrix Screen/File Sharing/Saving .exe File Name VNC, VPN, RFS, P2P and SSH Virtual Drives ● Dropbox.exe ● Dropbox ● OneDrive.exe ● OneDrive ● <name>.exe ● Google Drive ● etc. ● iCloud ● etc. Evernote / One Note ● Evernote_---.exe ● onenote.exe Go To Meeting ● gotomeeting launcher.exe / gotomeeting.exe TeamViewer ● TeamViewer.exe Chrome Remote ● remoting_host.exe www.ProctorU.com ● [email protected] ● 8883553043 Messaging / Video (IM, IRC) / .exe File Name Audio Bonjour Google Hangouts (chrome.exe - shown as a tab) (Screen Sharing) Skype SkypeC2CPNRSvc.exe Music Streaming ● Spotify.exe (Spotify, Pandora, etc.) ● PandoraService.exe Steam Steam.exe ALL Processes Screen / File Sharing / Messaging / Video (IM, Virtual Machines (VM) Other Saving IRC) / Audio Virtual Box Splashtop Bonjour ● iChat ● iTunes ● iPhoto ● TiVo ● SubEthaEdit ● Contactizer, ● Things ● OmniFocuse phpVirtualBox TeamViewer MobileMe Parallels Sticky Notes Team Speak VMware One Note Ventrilo Windows Virtual PC Dropbox Sandboxd QEM (Linux only) Chrome Remote iStumbler HYPERBOX SkyDrive MSN Chat Boot Camp (dual boot) OneDrive Blackboard Chat CVMCompiler Google Drive Yahoo Messenger Office (Word, Excel, Skype etc.) www.ProctorU.com ● [email protected] ● 8883553043 2X Software Notepad Steam AerooAdmin Paint Origin AetherPal Go To Meeting Spotify Ammyy Admin Jing Facebook Messenger AnyDesk -
Major Qualifying Project
Network Anomaly Detection Utilizing Robust Principal Component Analysis Major Qualifying Project Advisors: PROFESSORS LANE HARRISON,RANDY PAFFENROTH Written By: AURA VELARDE RAMIREZ ERIK SOLA PLEITEZ A Major Qualifying Project WORCESTER POLYTECHNIC INSTITUTE Submitted to the Faculty of the Worcester Polytechnic Institute in partial fulfillment of the requirements for the Degree of Bachelor of Science in Computer Science. AUGUST 24, 2017 - MARCH 2, 2018 ABSTRACT n this Major Qualifying Project, we focus on the development of a visualization-enabled anomaly detection system. We examine the 2011 VAST dataset challenge to efficiently Igenerate meaningful features and apply Robust Principal Component Analysis (RPCA) to detect any data points estimated to be anomalous. This is done through an infrastructure that promotes the closing of the loop from feature generation to anomaly detection through RPCA. We enable our user to choose subsets of the data through a web application and learn through visualization systems where problems are within their chosen local data slice. In this report, we explore both feature engineering techniques along with optimizing RPCA which ultimately lead to a generalized approach for detecting anomalies within a defined network architecture. i TABLE OF CONTENTS Page List of Tables v List of Figures vii 1 Introduction 1 1.1 Introduction .......................................... 1 2 VAST Dataset Challenge3 2.1 2011 VAST Dataset...................................... 3 2.2 Attacks in the VAST Dataset ................................ 6 2.3 Avoiding Data Snooping ................................... 7 2.4 Previous Work......................................... 8 3 Anomalies in Cyber Security9 3.1 Anomaly detection methods................................. 9 4 Feature Engineering 12 4.1 Feature Engineering Process ................................ 12 4.2 Feature Selection For a Dataset.............................. -

Ncircle IP360
VULNERABILITY MANAGEMENT TECHNOLOGY REPORT nCircle IP360 OCTOBER 2006 www.westcoastlabs.org 2 VULNERABILITY MANAGEMENT TECHNOLOGY REPORT CONTENTS nCircle IP360 nCircle, 101 Second Street, Suite 400, San Francisco, CA 94105 Phone: +1 (415) 625 5900 • Fax: +1 (415) 625 5982 Test Environment and Network ................................................................3 Test Reports and Assessments ................................................................4 Checkmark Certification – Standard and Premium ....................................5 Vulnerabilities..........................................................................................6 West Coast Labs Vulnerabilities Classification ..........................................7 The Product ............................................................................................8 Developments in the IP360 Technology ....................................................9 Test Report ............................................................................................10 Test Results ............................................................................................17 West Coast Labs Conclusion....................................................................18 Security Features Buyers Guide ..............................................................19 West Coast Labs, William Knox House, Britannic Way, Llandarcy, Swansea, SA10 6EL, UK. Tel : +44 1792 324000, Fax : +44 1792 324001. www.westcoastlabs.org VULNERABILITY MANAGEMENT TECHNOLOGY REPORT 3 TEST ENVIRONMENT