Designing Security Architecture Solutions.Pdf
Total Page:16
File Type:pdf, Size:1020Kb
Load more
Recommended publications
-
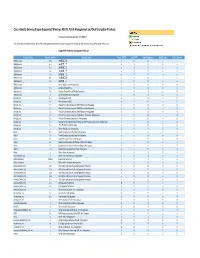
Cisco Identity Services Engine Supported Windows AV/AS/PM/DE
Cisco Identity Services Engine Supported Windows AS/AV, Patch Management and Disk Encryption Products Compliance Module Version 3.6.10363.2 This document provides Windows AS/AV, Patch Management and Disk Encryption support information on the the Cisco AnyConnect Agent Version 4.2. Supported Windows Antispyware Products Vendor_Name Product_Version Product_Name Check_FSRTP Set_FSRTP VirDef_Signature VirDef_Time VirDef_Version 360Safe.com 10.x 360安全卫士 vX X v v 360Safe.com 4.x 360安全卫士 vX X v v 360Safe.com 5.x 360安全卫士 vX X v v 360Safe.com 6.x 360安全卫士 vX X v v 360Safe.com 7.x 360安全卫士 vX X v v 360Safe.com 8.x 360安全卫士 vX X v v 360Safe.com 9.x 360安全卫士 vX X v v 360Safe.com x Other 360Safe.com Antispyware Z X X Z X Agnitum Ltd. 7.x Outpost Firewall Pro vX X X O Agnitum Ltd. 6.x Outpost Firewall Pro 2008 [AntiSpyware] v X X v O Agnitum Ltd. x Other Agnitum Ltd. Antispyware Z X X Z X AhnLab, Inc. 2.x AhnLab SpyZero 2.0 vv O v O AhnLab, Inc. 3.x AhnLab SpyZero 2007 X X O v O AhnLab, Inc. 7.x AhnLab V3 Internet Security 2007 Platinum AntiSpyware v X O v O AhnLab, Inc. 7.x AhnLab V3 Internet Security 2008 Platinum AntiSpyware v X O v O AhnLab, Inc. 7.x AhnLab V3 Internet Security 2009 Platinum AntiSpyware v v O v O AhnLab, Inc. 7.x AhnLab V3 Internet Security 7.0 Platinum Enterprise AntiSpyware v X O v O AhnLab, Inc. 8.x AhnLab V3 Internet Security 8.0 AntiSpyware v v O v O AhnLab, Inc. -
Cehv6 Program Guide.Indd
Page 1 Ethical Hacking and Countermeasures http://www.eccouncil.orghttp://www.eccouncil.org EC-CouncilEC-Council TM Page 2 CEH Certified Ethical Hacker http://www.eccouncil.org EC-Council Table of Contents Page 3 What is New in CEHv6? .............................................. Page 4 CEHv6 Fact Sheet ........................................................ Page 5 CEH Training Program ................................................ Page 9 Course Outline ............................................................ Page 10 Classroom Lecture Hours ............................................ Page 159 CEHv6 Labs ............................................................... Page 162 Module Briefi ng .......................................................... Page 178 CEHv6 Exam Objectives ............................................ Page 193 http://www.eccouncil.org EC-Council Lets’ Stop the Hackers Menace. Master the Hacking Technologies. Become a CEH. Page 4 http://www.eccouncil.org EC-Council CEH v6 Fact Sheet Page 5 1. What is the nature of the course change? CEHv6 has been updated with tons of new hacking tools, new hacking techniques and methodologies. The fl ow of the content is the same except each module is refreshed with more content. There are advanced modules added to the curriculum like Writing Windows Exploits, Reverse Engineering, Covert Hacking and Advanced Virus Writing Skills. The slides are updated to make them more presentable. There are over 67 modules in CEHv6. 2. Are there accompanying certifi cation changes? The CEHv6 exam will be available at Prometric Prime, Prometric APTC and VUC Centers on November 5th 2008. The old CEHv5 exam will still be available until June 3rd 2009. 3. How much will the new exam cost? The updated CEH v6 will cost USD 250. 4. What is the duration of the exam? The exam will be 4 hours with 150 questions. The passing score is 70% 5. -
Creating Smart Enterprises Leveraging Cloud, Big Data, Web, Social Media, Mobile and Iot Technologies
Creating Smart Enterprises Leveraging Cloud, Big Data, Web, Social Media, Mobile and IoT Technologies Creating Smart Enterprises Leveraging Cloud, Big Data, Web, Social Media, Mobile and IoT Technologies By Vivek Kale CRC Press Taylor & Francis Group 6000 Broken Sound Parkway NW, Suite 300 Boca Raton, FL 33487-2742 © 2018 Vivek Kale CRC Press is an imprint of Taylor & Francis Group, an Informa business No claim to original U.S. Government works Printed on acid-free paper International Standard Book Number-13: 978-1-4987-5128-5 (Hardback) This book contains information obtained from authentic and highly regarded sources. Reasonable efforts have been made to publish reliable data and information, but the author and publisher cannot assume responsibility for the validity of all materials or the consequences of their use. The authors and publishers have attempted to trace the copyright holders of all material reproduced in this publication and apologize to copyright holders if permission to publish in this form has not been obtained. If any copyright material has not been acknowledged please write and let us know so we may rectify in any future reprint. Except as permitted under U.S. Copyright Law, no part of this book may be reprinted, reproduced, transmitted, or utilized in any form by any electronic, mechanical, or other means, now known or hereafter invented, including photocopying, microfilming, and recording, or in any information storage or retrieval system, without written permission from the publishers. For permission to photocopy or use material electronically from this work, please access www.copyright.com (http://www.copyright.com/) or contact the Copyright Clearance Center, Inc. -

31 Network Security, Threats, Authentication, Authorization, and Securing Devices
31 network Security, threats, authentication, authorization, and Securing devices WenbIn Luo IntroductIon by intercepting the network traffic, keyboard logging, or simply guessing, then the attacker can get into all their other Nowadays, almost all the information is stored electroni- accounts that share the same password. Also, if an insider in cally in computers, network servers, mobile devices, or one system compromises their password, their accounts in other storage media. We cannot protect electronic infor- other systems are also compromised. mation in a cabinet in the same way we protected physical In this chapter, first, we will review private key encryp- documents in the past. We have to come up with new tech- tion and public key encryption techniques. Then, we will give niques to protect the information from unauthorized access, examples of how to perform private key encryption, public use, or manipulation. The easiest way to protect electronic key encryption, and digital signing using GPG. Second, we data is to encrypt it so that people cannot figure out what will discuss some of the threats, which a computer system it contains without knowing the secret keys. Over the last or user may face, and how they work. Third, we will exam- several decades, two major types of encryption techniques ine some existing authentication techniques and take a look have been invented: private key encryption and public key at various authorization methods, especially those used on a encryption. Linux system. Finally, the last topic will be on how to secure Private key encryption, which is also called symmetric devices. encryption, scrambles the original data with a secret key. -

Kryptografia
Wiosna 2016. Kryptografia dziedzina wiedzy zajmująca się zasadami, narzędziami i metodami przekształcania danych w celu ukrycia zawartych w nich informacji, zapobiegania możliwości tajnego ich modyfikowania lub eliminacji dostępu do nich osobom niepowołanym Kryptografia ogranicza się do przekształcania informacji za pomocą jednego lub więcej „tajnych parametrów” (np. szyfrów) i/lub związanego z tym zarządzaniem kluczami Klucze do szyfrowania dowolnego dokumentu elektronicznego, przez praktycznie nieograniczoną liczbę osób można stosować jeden, ten sam komputerowy program szyfrujący Klucz kodowy zazwyczaj szereg cyfr, od których zależy sposób przekształcania (szyfrowania) określonej informacji im więcej cyfr, tym bardziej skuteczny jest sposób kodowania (trudniej jest odszyfrować tak zmienioną informację) Kryptografia (symetryczny klucz) Tajne/poufne Tajne/poufne ................... ................... amdh$%&*^(()987 Lkjhgfd<?><L:PIYU kryptowanie dekryptowanie INTERNET Metody klucza tajnego (symetryczne) • DES (Data/Digital Encryption Standard) • 3DES (Triple DES) • RC4 (Ron’s Code 4) • IDEA (International Data Encryption Algorithm) • Blowfish • Twofish • AES (Advanced Encryption Standard) Szymon Sokół; [email protected] Uczelniane Centrum Informatyki Akademii Górniczo-Hutniczej w Krakowie RSA Ideę algorytmu (RSA) szyfrowania z wykorzystaniem powiązanych ze sobą dwóch kluczy – prywatnego i publicznego opracowali w 1977 roku Ron Rivest, Adi Shamir oraz Adleman. Szyfrowanie symetryczne • Istnieją dwie popularne metody szyfrowania symetrycznego. -
Designing Security Architecture Solutions
TEAMFLY Team-Fly® Designing Security Architecture Solutions Jay Ramachandran Wiley Computer Publishing John Wiley & Sons, Inc. Designing Security Architecture Solutions Designing Security Architecture Solutions Jay Ramachandran Wiley Computer Publishing John Wiley & Sons, Inc. Publisher: Robert Ipsen Editor: Carol Long Managing Editor: Micheline Frederick Developmental Editor: Adaobi Obi Text Design & Composition: D&G Limited, LLC Designations used by companies to distinguish their products are often claimed as trademarks. In all instances where John Wiley & Sons, Inc., is aware of a claim, the product names appear in initial capital or ALL CAPITAL LETTERS. Readers, however, should contact the appropriate companies for more complete information regarding trademarks and registration. This book is printed on acid-free paper. Copyright © 2002 by Jay Ramachandran. All rights reserved. Published by John Wiley & Sons, Inc. Published simultaneously in Canada. No part of this publication may be reproduced, stored in a retrieval system or transmitted in any form or by any means, electronic, mechanical, photocopying, recording, scanning or otherwise, except as permitted under Sections 107 or 108 of the 1976 United States Copyright Act, without either the prior written permission of the Publisher, or authoriza- tion through payment of the appropriate per-copy fee to the Copyright Clearance Center, 222 Rosewood Drive, Danvers, MA 01923, (978) 750-8400, fax (978) 750-4744. Requests to the Publisher for permission should be addressed to the Permissions Department, John Wiley & Sons, Inc., 605 Third Avenue, New York, NY 10158-0012, (212) 850-6011, fax (212) 850-6008, E-Mail: PERMREQ @ WILEY.COM. This publication is designed to provide accurate and authoritative information in regard to the subject matter covered. -
Cisco Anyconnect ISE Posture Windows Support Charts for Compliance Module V3.6.11428.2
Cisco AnyConnect ISE Posture Windows Support Charts for Compliance Module v3.6.11428.2 August 2, 2017 © 2017 Cisco and/or its affiliates. All rights reserved. This document is Cisco public. Page 1 of 65 Contents Anti-Virus .................................................................................................................................................................................... 3 Anti-Spyware ............................................................................................................................................................................ 43 Patch Management................................................................................................................................................................... 59 Disk Encryption ........................................................................................................................................................................ 61 ©2017 Cisco and/or its affiliates. All rights reserved. This document is Cisco Public. Page 2 of 65 This document lists the Windows OS anti-virus, anti-spyware, patch management, and disk encryption products that are supported by the ISE Posture Agent. The Windows compliance modules are version 3.6.11428.2. Anti-Virus Definition State Product Name Product Version Live Update Min. Compliance Module Version Check 360Safe.com 360 Antivirus 1.x yes yes 3.4.16.1 360 Antivirus 3.x yes - 3.5.5767.2 360 Total Security 4.x yes - 3.6.9335.2 360 Total Security 5.x yes - 3.6.9872.2 360 Total Security 6.x yes - 3.6.9908.2 360 Total Security 7.x yes - 3.6.10231.2 360 Total Security 8.x yes - 3.6.10547.2 360天擎 6.x - - 3.6.11017.2 360杀毒 1.x yes - 3.4.13.1 360杀毒 2.x yes - 3.4.25.1 360杀毒 3.x - - 3.5.2101.2 360杀毒 4.x - - 3.5.6528.2 360杀毒 5.x yes - 3.6.8769.2 Other 360Safe.com Antivirus x - - 3.5.2101.2 AEC, spol. s r.o. Other AEC, spol. s r.o. Antivirus x - - 3.5.2101.2 TrustPort Antivirus 2.x - yes 3.4.8.1 Agnitum Ltd. -

Exploratory Workhop "Information Security Management - in the 21St Century"
REGIONAL DEPARTMENT OF DEFENSE RESOURCES MANAGEMENT STUDIES THE 8th EXPLORATORY WORKHOP "INFORMATION SECURITY MANAGEMENT - IN THE 21ST CENTURY" ISSN: 2286 - 2765 ISSN-L: 2286 - 2765 COORDINATOR: Professor Habil Ph.D. eng. CEZAR VASILESCU National Defense University “Carol I” Publishing House Bucharest 2015 THE 8th EXPLORATORY WORKHOP "INFORMATION SECURITY MANAGEMENT - IN THE 21ST CENTURY" 11 June 2015 Proceedings of the workshop unfolded during the Information Security Management Course Conducted by the Regional Department of Defense Resources Management Studies 25 May – 19 June 2015 Braşov ROMÂNIA 2 of 321 C O N T E N T S 1. LEGAL AND ETHICAL ASPECTS OF INFORMATION SECURITY AND PRIVACY - Carmen FLOREA (Romania) 2. ASPЕCTS CОNCЕRNING TОR NЕTWОRK IMPLICATIОNS IN NATIОNAL SЕCURITY - Marius GHЕОRGHЕVICI (Romania) 3. SECURITY OVER PUBLIC INTERNET CHANNELS - Artem BAKUTA (Ukraine) 4. DIOFANTUS METHOD FOR DETERMINING THE PROBABILITY OF OCCURRENCE OF DAMAGE FOR BOUNDARY RISKS OF INFORMATION SECURITY - Vitalii BEZSHTANKO (Ukraine) 5. CYBERWAR-MYTH OR REALITY - Mircea TONCEANU (Romania) 6. HANDLING DESTRUCTIVE MALWARE - Denis-Nicolae FLORESCU (Romania) 7. INFORMATION SECURITY IN SWITZERLAND’S BANKS - Laura Maria SABOSLAI FOTIN (Romania) 8. STUDY ON THE PROTECTION MECHANISM TO SECURE INFORMATION EXCHANGE AND E-MAIL WITHIN AN INTRANET BASED ON PKI AND INFORMATION TECHNOLOGIES - Oleg CHIRILENCO (R. of Moldova) 9. OVERVIEW OF SECURITY IMPLICATIONS OF INTERNET OF THINGS IN MILITARY ORGANIZATIONS - Ștefan-Ciprian ARSENI (Romania) 10. SECURITY POLICIES AND AWARENESS IN THE SCHOOL ESTABLISHEMENT - Sadraoui ROSTOM (Jordan) 11. SECURITY ISSUES AND KEY MANAGEMENT IN MANETs - Marin DUMITRANA (Romania) 12. ANATHOMY OF A HACK - Suren OHANOV (Armenia) 3 of 321 13. INFORMATION SECURITY MANAGEMENT IN AN E- GOVERNMENT ENVIRONMENT - Lotfi HACHANA (Tunisia) 14. -

How to Communicate Securely in Repressive Environments
How to Communicate Securely in Repressive Environments A Guide for Improving Digital Security - Updated June 28, 2009 This draft guide is intended for political activists operating in non-permissive environments and those supporting their efforts. Introduction Core to effective strategic nonviolent action is the need to remain proactive and on the offensive; the rationale being that both the resistance movement and repressive regime have an equal amount of time allocated when the show-down begins. If the movement becomes idle at any point, this may give the regime the opportunity to regain the upper hand, or vice versa. The same principle is found in Clausewitz’s writings on war . Nonviolent resistance movements are typically driven by students, i.e., young people, who are increasingly born digital natives . With expanding access to mobile phones, social networking software and online platforms for user-generated content such as blogs, the immediate financial cost of speaking out against repressive regimes is virtually nil. So resistance movements are likely to make even more use of new communication technology and digital media in the future. In fact, they already are. At the same time, however, the likelihood and consequences of getting caught are high, especially for those political activists without any background or training in digital security. Indeed, recent research by Digital Democracy research suggests that organizational hierarchies are being broken down as youth adopt new technologies. While this empowers them they are also put at risk since they don’t tend to be as consequence-conscious as their adult counterparts. Empire Strikes Back It is no myth that repressive regimes are becoming increasingly more savvy in their ability to effectively employ sophisticated filtering, censoring, monitoring technologies (often courtesy of American companies like Cisco) to crack down on resistance movements. -

A Worldwide Survey of Encryption Products
A Worldwide Survey of Encryption Products Bruce Schneier Kathleen Seidel Saranya Vijayakumar Berkman Center for Internet Independent Researcher Harvard College and Society [email protected] [email protected] Harvard University [email protected] February 11, 2016 Version 1.0 Introduction Data security is a worldwide problem, and there is a wide world of encryption solutions available to help solve this problem. Most of these products are developed and sold by for-profit entities, although some are created as free open-source projects. They are available, either for sale or free download, all over the world. In 1999, a group of researchers from George Washington University attempted to survey the worldwide market for encryption products [HB+99]. The impetus for their survey was the ongoing debate about US encryption export controls. By collecting information about 805 hardware and software encryption products from 35 countries outside the US, the researchers showed that restricting the export of encryption products did nothing to reduce their availability around the world, while at the same time putting US companies at a competitive disadvantage in the information security market. Seventeen years later, we have tried to replicate this survey. Findings We collected information on as many encryption products as we could find anywhere in the world. This is a summary of our findings: We have identified 865 hardware or software products incorporating encryption from 55 different countries. This includes 546 encryption products from outside the US, representing two-thirds of the total. Table 1 summarizes the number of products from each country. The most common non-US country for encryption products is Germany, with 112 products. -

EC-Council Course Catalogs
Education Services EC-Council Course Catalogs ITPro Global Coyright by ITPro Global ® 2009 Educational Services Educational Services EC-Council Certification Path Senior Security Forensics Advanced Disaster Recovery Specialist Certified VoIP Secure Programmer Lawyers Investigator Penetration Testing The Senior Specialist for Disaster Professional The Programmer's role is and Corporate Ideal candidates include Recovery is responsible for all aspects An expert level lead to define, develop, test, Attorneys This position is responsible for those individuals that of the IT Disaster Recovery Plan. engineer with a strong analyze, and maintain responding to and Deals with computer have the abilities to Provides oversight and guidance for all technical background in new software applications for leading security investiga- crime investigations conduct either an disaster recovery related activities IP networking, experi- in .NET. This includes tions of varying types. within the IT department. writing, coding, testing, and are qualified to application or network enced in designing carrier handle Cyberspace, based penetration test, grade ATM, IP and MPLS and analyzing software Functions include the design, allegations or which includes initial Manages all aspects of IT disaster enabled networks to programs and applica- implementation and creation downloading identification of recovery including the development, support the newest as tions. of plans, strategies and actions pornography, vulnerabilities through a implementation and testing of a well as the legacy necessary for a successful solicitation of minors, Job Roles variety of software tools, comprehensive IT Disaster recovery technologies for mobile Candidate will work with security investigations hacking/cracking, and then exploiting plan. Responsible for developing, networks and applica- network administrators, Based On program. -
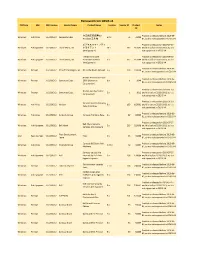
Removed from OESIS V4 Platform SDK SDK Version Vendor Name Product Name Version Vendor ID Product Notes ID
Removed from OESIS v4 Platform SDK SDK Version Vendor Name Product Name Version Vendor ID Product Notes ID 卡巴斯基反病毒6.0 Product is released before 2010-06- Windows Anti-Virus 3.6.10363.2 Kaspersky Labs 6.0.x 76 76008 Windows工作站 01, so it is not supported in OESIS V4 ビジネスセキュリティ Product is released on 2010-07-27 Windows Anti-Spyware 3.6.10363.2 Trend Micro, Inc. クライアント 16.x 167 167045 and it is before 2013-01-01, so it is (AntiSpyware) not supported in OESIS V4 Trend Micro Core Product is released on 2010-06-30 Windows Anti-Spyware 3.6.10363.2 Trend Micro, Inc. Protection Module 1.x 167 167044 and it is before 2013-01-01, so it is [AntiSpyware] not supported in OESIS V4 Product is released before 2010-06- Windows Firewall 3.6.10363.2 Kerio Technologies, Inc. Kerio WinRoute Firewall 6.x 203 203000 01, so it is not supported in OESIS V4 Norton Personal Firewall Product is released before 2010-06- Windows Firewall 3.6.10363.2 Symantec Corp. 2006 (Symantec 8.x 1 1049 01, so it is not supported in OESIS V4 Corporation) Product is released on 2010-11-30 Norton 360 (Symantec Windows Firewall 3.6.10363.2 Symantec Corp. 5.x 1 1013 and it is before 2013-01-01, so it is Corporation) not supported in OESIS V4 Product is released on 2010-06-30 Verizon Internet Security Windows Anti-Virus 3.6.10363.2 Verizon 9.x 169 169001 and it is before 2013-01-01, so it is Suite Anti-Virus not supported in OESIS V4 Product is released before 2010-06- Windows Anti-Virus 3.6.10363.2 Comodo Group Comodo AntiVirus Beta 2.x 92 92003 01, so it is not supported in OESIS V4