Applications of Multilinear Forms to Cryptography
Total Page:16
File Type:pdf, Size:1020Kb
Load more
Recommended publications
-

Multilinear Algebra and Applications July 15, 2014
Multilinear Algebra and Applications July 15, 2014. Contents Chapter 1. Introduction 1 Chapter 2. Review of Linear Algebra 5 2.1. Vector Spaces and Subspaces 5 2.2. Bases 7 2.3. The Einstein convention 10 2.3.1. Change of bases, revisited 12 2.3.2. The Kronecker delta symbol 13 2.4. Linear Transformations 14 2.4.1. Similar matrices 18 2.5. Eigenbases 19 Chapter 3. Multilinear Forms 23 3.1. Linear Forms 23 3.1.1. Definition, Examples, Dual and Dual Basis 23 3.1.2. Transformation of Linear Forms under a Change of Basis 26 3.2. Bilinear Forms 30 3.2.1. Definition, Examples and Basis 30 3.2.2. Tensor product of two linear forms on V 32 3.2.3. Transformation of Bilinear Forms under a Change of Basis 33 3.3. Multilinear forms 34 3.4. Examples 35 3.4.1. A Bilinear Form 35 3.4.2. A Trilinear Form 36 3.5. Basic Operation on Multilinear Forms 37 Chapter 4. Inner Products 39 4.1. Definitions and First Properties 39 4.1.1. Correspondence Between Inner Products and Symmetric Positive Definite Matrices 40 4.1.1.1. From Inner Products to Symmetric Positive Definite Matrices 42 4.1.1.2. From Symmetric Positive Definite Matrices to Inner Products 42 4.1.2. Orthonormal Basis 42 4.2. Reciprocal Basis 46 4.2.1. Properties of Reciprocal Bases 48 4.2.2. Change of basis from a basis to its reciprocal basis g 50 B B III IV CONTENTS 4.2.3. -

Multilinear Algebra
Appendix A Multilinear Algebra This chapter presents concepts from multilinear algebra based on the basic properties of finite dimensional vector spaces and linear maps. The primary aim of the chapter is to give a concise introduction to alternating tensors which are necessary to define differential forms on manifolds. Many of the stated definitions and propositions can be found in Lee [1], Chaps. 11, 12 and 14. Some definitions and propositions are complemented by short and simple examples. First, in Sect. A.1 dual and bidual vector spaces are discussed. Subsequently, in Sects. A.2–A.4, tensors and alternating tensors together with operations such as the tensor and wedge product are introduced. Lastly, in Sect. A.5, the concepts which are necessary to introduce the wedge product are summarized in eight steps. A.1 The Dual Space Let V be a real vector space of finite dimension dim V = n.Let(e1,...,en) be a basis of V . Then every v ∈ V can be uniquely represented as a linear combination i v = v ei , (A.1) where summation convention over repeated indices is applied. The coefficients vi ∈ R arereferredtoascomponents of the vector v. Throughout the whole chapter, only finite dimensional real vector spaces, typically denoted by V , are treated. When not stated differently, summation convention is applied. Definition A.1 (Dual Space)Thedual space of V is the set of real-valued linear functionals ∗ V := {ω : V → R : ω linear} . (A.2) The elements of the dual space V ∗ are called linear forms on V . © Springer International Publishing Switzerland 2015 123 S.R. -

Vector Calculus and Differential Forms
Vector Calculus and Differential Forms John Terilla Math 208 Spring 2015 1 Vector fields Definition 1. Let U be an open subest of Rn.A tangent vector in U is a pair (p; v) 2 U × Rn: We think of (p; v) as consisting of a vector v 2 Rn lying at the point p 2 U. Often, we denote a tangent vector by vp instead of (p; v). For p 2 U, the set of all tangent vectors at p is denoted by Tp(U). The set of all tangent vectors in U is denoted T (U) For a fixed point p 2 U, the set Tp(U) is a vector space with addition and scalar multiplication defined by vp + wp = (v + w)p and αvp = (αv)p: Note n that as a vector space, Tp(U) is isomorphic to R . Definition 2. A vector field on U is a function X : U ! T (Rn) satisfying X(p) 2 Tp(U). Remark 1. Notice that any function f : U ! Rn defines a vector field X by the rule X(p) = f(p)p: Denote the set of vector fields on U by Vect(U). Note that Vect(U) is a vector space with addition and scalar multiplication defined pointwise (which makes sense since Tp(U) is a vector space): (X + Y )(p) := X(p) + Y (p) and (αX)(p) = α(X(p)): Definition 3. Denote the set of functions on the set U by Fun(U) = ff : U ! Rg. Let C1(U) be the subset of Fun(U) consisting of functions with continuous derivatives and let C1(U) be the subset of Fun(U) consisting of smooth functions, i.e., infinitely differentiable functions. -

Research Notices
AMERICAN MATHEMATICAL SOCIETY Research in Collegiate Mathematics Education. V Annie Selden, Tennessee Technological University, Cookeville, Ed Dubinsky, Kent State University, OH, Guershon Hare I, University of California San Diego, La jolla, and Fernando Hitt, C/NVESTAV, Mexico, Editors This volume presents state-of-the-art research on understanding, teaching, and learning mathematics at the post-secondary level. The articles are peer-reviewed for two major features: (I) advancing our understanding of collegiate mathematics education, and (2) readability by a wide audience of practicing mathematicians interested in issues affecting their students. This is not a collection of scholarly arcana, but a compilation of useful and informative research regarding how students think about and learn mathematics. This series is published in cooperation with the Mathematical Association of America. CBMS Issues in Mathematics Education, Volume 12; 2003; 206 pages; Softcover; ISBN 0-8218-3302-2; List $49;AII individuals $39; Order code CBMATH/12N044 MATHEMATICS EDUCATION Also of interest .. RESEARCH: AGul<lelbrthe Mathematics Education Research: Hothomatldan- A Guide for the Research Mathematician --lllll'tj.M...,.a.,-- Curtis McKnight, Andy Magid, and -- Teri J. Murphy, University of Oklahoma, Norman, and Michelynn McKnight, Norman, OK 2000; I 06 pages; Softcover; ISBN 0-8218-20 16-8; List $20;AII AMS members $16; Order code MERN044 Teaching Mathematics in Colleges and Universities: Case Studies for Today's Classroom Graduate Student Edition Faculty -

Ring (Mathematics) 1 Ring (Mathematics)
Ring (mathematics) 1 Ring (mathematics) In mathematics, a ring is an algebraic structure consisting of a set together with two binary operations usually called addition and multiplication, where the set is an abelian group under addition (called the additive group of the ring) and a monoid under multiplication such that multiplication distributes over addition.a[›] In other words the ring axioms require that addition is commutative, addition and multiplication are associative, multiplication distributes over addition, each element in the set has an additive inverse, and there exists an additive identity. One of the most common examples of a ring is the set of integers endowed with its natural operations of addition and multiplication. Certain variations of the definition of a ring are sometimes employed, and these are outlined later in the article. Polynomials, represented here by curves, form a ring under addition The branch of mathematics that studies rings is known and multiplication. as ring theory. Ring theorists study properties common to both familiar mathematical structures such as integers and polynomials, and to the many less well-known mathematical structures that also satisfy the axioms of ring theory. The ubiquity of rings makes them a central organizing principle of contemporary mathematics.[1] Ring theory may be used to understand fundamental physical laws, such as those underlying special relativity and symmetry phenomena in molecular chemistry. The concept of a ring first arose from attempts to prove Fermat's last theorem, starting with Richard Dedekind in the 1880s. After contributions from other fields, mainly number theory, the ring notion was generalized and firmly established during the 1920s by Emmy Noether and Wolfgang Krull.[2] Modern ring theory—a very active mathematical discipline—studies rings in their own right. -

Chapter IX. Tensors and Multilinear Forms
Notes c F.P. Greenleaf and S. Marques 2006-2016 LAII-s16-quadforms.tex version 4/25/2016 Chapter IX. Tensors and Multilinear Forms. IX.1. Basic Definitions and Examples. 1.1. Definition. A bilinear form is a map B : V V C that is linear in each entry when the other entry is held fixed, so that × → B(αx, y) = αB(x, y)= B(x, αy) B(x + x ,y) = B(x ,y)+ B(x ,y) for all α F, x V, y V 1 2 1 2 ∈ k ∈ k ∈ B(x, y1 + y2) = B(x, y1)+ B(x, y2) (This of course forces B(x, y)=0 if either input is zero.) We say B is symmetric if B(x, y)= B(y, x), for all x, y and antisymmetric if B(x, y)= B(y, x). Similarly a multilinear form (aka a k-linear form , or a tensor− of rank k) is a map B : V V F that is linear in each entry when the other entries are held fixed. ×···×(0,k) → We write V = V ∗ . V ∗ for the set of k-linear forms. The reason we use V ∗ here rather than V , and⊗ the⊗ rationale for the “tensor product” notation, will gradually become clear. The set V ∗ V ∗ of bilinear forms on V becomes a vector space over F if we define ⊗ 1. Zero element: B(x, y) = 0 for all x, y V ; ∈ 2. Scalar multiple: (αB)(x, y)= αB(x, y), for α F and x, y V ; ∈ ∈ 3. Addition: (B + B )(x, y)= B (x, y)+ B (x, y), for x, y V . -

A Decade of Lattice Cryptography
Full text available at: http://dx.doi.org/10.1561/0400000074 A Decade of Lattice Cryptography Chris Peikert Computer Science and Engineering University of Michigan, United States Boston — Delft Full text available at: http://dx.doi.org/10.1561/0400000074 Foundations and Trends R in Theoretical Computer Science Published, sold and distributed by: now Publishers Inc. PO Box 1024 Hanover, MA 02339 United States Tel. +1-781-985-4510 www.nowpublishers.com [email protected] Outside North America: now Publishers Inc. PO Box 179 2600 AD Delft The Netherlands Tel. +31-6-51115274 The preferred citation for this publication is C. Peikert. A Decade of Lattice Cryptography. Foundations and Trends R in Theoretical Computer Science, vol. 10, no. 4, pp. 283–424, 2014. R This Foundations and Trends issue was typeset in LATEX using a class file designed by Neal Parikh. Printed on acid-free paper. ISBN: 978-1-68083-113-9 c 2016 C. Peikert All rights reserved. No part of this publication may be reproduced, stored in a retrieval system, or transmitted in any form or by any means, mechanical, photocopying, recording or otherwise, without prior written permission of the publishers. Photocopying. In the USA: This journal is registered at the Copyright Clearance Center, Inc., 222 Rosewood Drive, Danvers, MA 01923. Authorization to photocopy items for in- ternal or personal use, or the internal or personal use of specific clients, is granted by now Publishers Inc for users registered with the Copyright Clearance Center (CCC). The ‘services’ for users can be found on the internet at: www.copyright.com For those organizations that have been granted a photocopy license, a separate system of payment has been arranged. -

The Best Nurturers in Computer Science Research
The Best Nurturers in Computer Science Research Bharath Kumar M. Y. N. Srikant IISc-CSA-TR-2004-10 http://archive.csa.iisc.ernet.in/TR/2004/10/ Computer Science and Automation Indian Institute of Science, India October 2004 The Best Nurturers in Computer Science Research Bharath Kumar M.∗ Y. N. Srikant† Abstract The paper presents a heuristic for mining nurturers in temporally organized collaboration networks: people who facilitate the growth and success of the young ones. Specifically, this heuristic is applied to the computer science bibliographic data to find the best nurturers in computer science research. The measure of success is parameterized, and the paper demonstrates experiments and results with publication count and citations as success metrics. Rather than just the nurturer’s success, the heuristic captures the influence he has had in the indepen- dent success of the relatively young in the network. These results can hence be a useful resource to graduate students and post-doctoral can- didates. The heuristic is extended to accurately yield ranked nurturers inside a particular time period. Interestingly, there is a recognizable deviation between the rankings of the most successful researchers and the best nurturers, which although is obvious from a social perspective has not been statistically demonstrated. Keywords: Social Network Analysis, Bibliometrics, Temporal Data Mining. 1 Introduction Consider a student Arjun, who has finished his under-graduate degree in Computer Science, and is seeking a PhD degree followed by a successful career in Computer Science research. How does he choose his research advisor? He has the following options with him: 1. Look up the rankings of various universities [1], and apply to any “rea- sonably good” professor in any of the top universities. -

Tensor Complexes: Multilinear Free Resolutions Constructed from Higher Tensors
Tensor complexes: Multilinear free resolutions constructed from higher tensors C. Berkesch, D. Erman, M. Kummini and S. V. Sam REPORT No. 7, 2010/2011, spring ISSN 1103-467X ISRN IML-R- -7-10/11- -SE+spring TENSOR COMPLEXES: MULTILINEAR FREE RESOLUTIONS CONSTRUCTED FROM HIGHER TENSORS CHRISTINE BERKESCH, DANIEL ERMAN, MANOJ KUMMINI, AND STEVEN V SAM Abstract. The most fundamental complexes of free modules over a commutative ring are the Koszul complex, which is constructed from a vector (i.e., a 1-tensor), and the Eagon– Northcott and Buchsbaum–Rim complexes, which are constructed from a matrix (i.e., a 2-tensor). The subject of this paper is a multilinear analogue of these complexes, which we construct from an arbitrary higher tensor. Our construction provides detailed new examples of minimal free resolutions, as well as a unifying view on a wide variety of complexes including: the Eagon–Northcott, Buchsbaum– Rim and similar complexes, the Eisenbud–Schreyer pure resolutions, and the complexes used by Gelfand–Kapranov–Zelevinsky and Weyman to compute hyperdeterminants. In addition, we provide applications to the study of pure resolutions and Boij–S¨oderberg theory, including the construction of infinitely many new families of pure resolutions, and the first explicit description of the differentials of the Eisenbud–Schreyer pure resolutions. 1. Introduction In commutative algebra, the Koszul complex is the mother of all complexes. David Eisenbud The most fundamental complex of free modules over a commutative ring R is the Koszul a complex, which is constructed from a vector (i.e., a 1-tensor) f = (f1, . , fa) R . The next most fundamental complexes are likely the Eagon–Northcott and Buchsbaum–Rim∈ complexes, which are constructed from a matrix (i.e., a 2-tensor) ψ Ra Rb. -

Algebraic Pseudorandom Functions with Improved Efficiency from the Augmented Cascade*
Algebraic Pseudorandom Functions with Improved Efficiency from the Augmented Cascade* DAN BONEH† HART MONTGOMERY‡ ANANTH RAGHUNATHAN§ Department of Computer Science, Stanford University fdabo,hartm,[email protected] September 8, 2020 Abstract We construct an algebraic pseudorandom function (PRF) that is more efficient than the classic Naor- Reingold algebraic PRF. Our PRF is the result of adapting the cascade construction, which is the basis of HMAC, to the algebraic settings. To do so we define an augmented cascade and prove it secure when the underlying PRF satisfies a property called parallel security. We then use the augmented cascade to build new algebraic PRFs. The algebraic structure of our PRF leads to an efficient large-domain Verifiable Random Function (VRF) and a large-domain simulatable VRF. 1 Introduction Pseudorandom functions (PRFs), first defined by Goldreich, Goldwasser, and Micali [GGM86], are a fun- damental building block in cryptography and have numerous applications. They are used for encryption, message integrity, signatures, key derivation, user authentication, and many other cryptographic mecha- nisms. Beyond cryptography, PRFs are used to defend against denial of service attacks [Ber96, CW03] and even to prove lower bounds in learning theory. In a nutshell, a PRF is indistinguishable from a truly random function. We give precise definitions in the next section. The fastest PRFs are built from block ciphers like AES and security is based on ad-hoc inter- active assumptions. In 1996, Naor and Reingold [NR97] presented an elegant PRF whose security can be deduced from the hardness of the Decision Diffie-Hellman problem (DDH) defined in the next section. -

Cross Products, Automorphisms, and Gradings 3
CROSS PRODUCTS, AUTOMORPHISMS, AND GRADINGS ALBERTO DAZA-GARC´IA, ALBERTO ELDUQUE, AND LIMING TANG Abstract. The affine group schemes of automorphisms of the multilinear r- fold cross products on finite-dimensional vectors spaces over fields of character- istic not two are determined. Gradings by abelian groups on these structures, that correspond to morphisms from diagonalizable group schemes into these group schemes of automorphisms, are completely classified, up to isomorphism. 1. Introduction Eckmann [Eck43] defined a vector cross product on an n-dimensional real vector space V , endowed with a (positive definite) inner product b(u, v), to be a continuous map X : V r −→ V (1 ≤ r ≤ n) satisfying the following axioms: b X(v1,...,vr), vi =0, 1 ≤ i ≤ r, (1.1) bX(v1,...,vr),X(v1,...,vr) = det b(vi, vj ) , (1.2) There are very few possibilities. Theorem 1.1 ([Eck43, Whi63]). A vector cross product exists in precisely the following cases: • n is even, r =1, • n ≥ 3, r = n − 1, • n =7, r =2, • n =8, r =3. Multilinear vector cross products X on vector spaces V over arbitrary fields of characteristic not two, relative to a nondegenerate symmetric bilinear form b(u, v), were classified by Brown and Gray [BG67]. These are the multilinear maps X : V r → V (1 ≤ r ≤ n) satisfying (1.1) and (1.2). The possible pairs (n, r) are again those in Theorem 1.1. The exceptional cases: (n, r) = (7, 2) and (8, 3), are intimately related to the arXiv:2006.10324v1 [math.RT] 18 Jun 2020 octonion, or Cayley, algebras. -
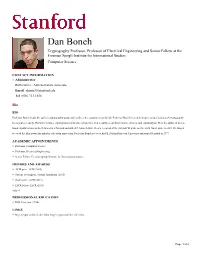
Dan Boneh Cryptography Professor, Professor of Electrical Engineering and Senior Fellow at the Freeman Spogli Institute for International Studies Computer Science
Dan Boneh Cryptography Professor, Professor of Electrical Engineering and Senior Fellow at the Freeman Spogli Institute for International Studies Computer Science CONTACT INFORMATION • Administrator Ruth Harris - Administrative Associate Email [email protected] Tel (650) 723-1658 Bio BIO Professor Boneh heads the applied cryptography group and co-direct the computer security lab. Professor Boneh's research focuses on applications of cryptography to computer security. His work includes cryptosystems with novel properties, web security, security for mobile devices, and cryptanalysis. He is the author of over a hundred publications in the field and is a Packard and Alfred P. Sloan fellow. He is a recipient of the 2014 ACM prize and the 2013 Godel prize. In 2011 Dr. Boneh received the Ishii award for industry education innovation. Professor Boneh received his Ph.D from Princeton University and joined Stanford in 1997. ACADEMIC APPOINTMENTS • Professor, Computer Science • Professor, Electrical Engineering • Senior Fellow, Freeman Spogli Institute for International Studies HONORS AND AWARDS • ACM prize, ACM (2015) • Simons investigator, Simons foundation (2015) • Godel prize, ACM (2013) • IACR fellow, IACR (2013) 4 OF 6 PROFESSIONAL EDUCATION • PhD, Princeton (1996) LINKS • http://crypto.stanford.edu/~dabo: http://crypto.stanford.edu/~dabo Page 1 of 2 Dan Boneh http://cap.stanford.edu/profiles/Dan_Boneh/ Teaching COURSES 2021-22 • Computer and Network Security: CS 155 (Spr) • Cryptocurrencies and blockchain technologies: CS 251 (Aut) •