Book of Abstracts
Total Page:16
File Type:pdf, Size:1020Kb
Load more
Recommended publications
-

Static Analysis the Workhorse of a End-To-End Securitye Testing Strategy
Static Analysis The Workhorse of a End-to-End Securitye Testing Strategy Achim D. Brucker [email protected] http://www.brucker.uk/ Department of Computer Science, The University of Sheffield, Sheffield, UK Winter School SECENTIS 2016 Security and Trust of Next Generation Enterprise Information Systems February 8–12, 2016, Trento, Italy Static Analysis: The Workhorse of a End-to-End Securitye Testing Strategy Abstract Security testing is an important part of any security development lifecycle (SDL) and, thus, should be a part of any software (development) lifecycle. Still, security testing is often understood as an activity done by security testers in the time between “end of development” and “offering the product to customers.” Learning from traditional testing that the fixing of bugs is the more costly the later it is done in development, security testing should be integrated, as early as possible, into the daily development activities. The fact that static analysis can be deployed as soon as the first line of code is written, makes static analysis the right workhorse to start security testing activities. In this lecture, I will present a risk-based security testing strategy that is used at a large European software vendor. While this security testing strategy combines static and dynamic security testing techniques, I will focus on static analysis. This lecture provides a introduction to the foundations of static analysis as well as insights into the challenges and solutions of rolling out static analysis to more than 20000 developers, distributed across the whole world. A.D. Brucker The University of Sheffield Static Analysis February 8–12., 2016 2 Today: Background and how it works ideally Tomorrow: (Ugly) real world problems and challenges (or why static analysis is “undecideable” in practice) Our Plan A.D. -

Sistemi Operativi Real-Time Marco Cesati Lezione R13 Sistemi Operativi Real-Time – II Schema Della Lezione
Sistemi operativi real-time Marco Cesati Lezione R13 Sistemi operativi real-time – II Schema della lezione Caratteristiche comuni VxWorks LynxOS Sistemi embedded e real-time QNX eCos Windows Linux come RTOS 15 gennaio 2013 Marco Cesati Dipartimento di Ingegneria Civile e Ingegneria Informatica Università degli Studi di Roma Tor Vergata SERT’13 R13.1 Sistemi operativi Di cosa parliamo in questa lezione? real-time Marco Cesati In questa lezione descriviamo brevemente alcuni dei più diffusi sistemi operativi real-time Schema della lezione Caratteristiche comuni VxWorks LynxOS 1 Caratteristiche comuni degli RTOS QNX 2 VxWorks eCos 3 LynxOS Windows Linux come RTOS 4 QNX Neutrino 5 eCos 6 Windows Embedded CE 7 Linux come RTOS SERT’13 R13.2 Sistemi operativi Caratteristiche comuni dei principali RTOS real-time Marco Cesati Corrispondenza agli standard: generalmente le API sono proprietarie, ma gli RTOS offrono anche compatibilità (compliancy) o conformità (conformancy) allo standard Real-Time POSIX Modularità e Scalabilità: il kernel ha una dimensione Schema della lezione Caratteristiche comuni (footprint) ridotta e le sue funzionalità sono configurabili VxWorks Dimensione del codice: spesso basati su microkernel LynxOS QNX Velocità e Efficienza: basso overhead per cambi di eCos contesto, latenza delle interruzioni e primitive di Windows sincronizzazione Linux come RTOS Porzioni di codice non interrompibile: generalmente molto corte e di durata predicibile Gestione delle interruzioni “separata”: interrupt handler corto e predicibile, ISR lunga -

List of Requirements for Code Reviews
WP2 DIGIT B1 - EP Pilot Project 645 Deliverable 9: List of Requirements for Code Reviews Specific contract n°226 under Framework Contract n° DI/07172 – ABCIII April 2016 DIGIT Fossa WP2 – Governance and Quality of Software Code – Auditing of Free and Open Source Software. Deliverable 9: List of requirements for code reviews Author: Disclaimer The information and views set out in this publication are those of the author(s) and do not necessarily reflect the official opinion of the Commission. The content, conclusions and recommendations set out in this publication are elaborated in the specific context of the EU – FOSSA project. The Commission does not guarantee the accuracy of the data included in this study. All representations, warranties, undertakings and guarantees relating to the report are excluded, particularly concerning – but not limited to – the qualities of the assessed projects and products. Neither the Commission nor any person acting on the Commission’s behalf may be held responsible for the use that may be made of the information contained herein. © European Union, 2016. Reuse is authorised, without prejudice to the rights of the Commission and of the author(s), provided that the source of the publication is acknowledged. The reuse policy of the European Commission is implemented by a Decision of 12 December 2011. Document elaborated in the specific context of the EU – FOSSA project. Reuse or reproduction authorised without prejudice to the Commission’s or the authors’ rights. Page 2 of 51 DIGIT Fossa WP2 – Governance and Quality of Software Code – Auditing of Free and Open Source Software. Deliverable 9: List of requirements for code reviews Contents CONTENTS............................................................................................................................................ -
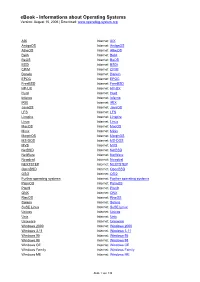
Ebook - Informations About Operating Systems Version: August 15, 2006 | Download
eBook - Informations about Operating Systems Version: August 15, 2006 | Download: www.operating-system.org AIX Internet: AIX AmigaOS Internet: AmigaOS AtheOS Internet: AtheOS BeIA Internet: BeIA BeOS Internet: BeOS BSDi Internet: BSDi CP/M Internet: CP/M Darwin Internet: Darwin EPOC Internet: EPOC FreeBSD Internet: FreeBSD HP-UX Internet: HP-UX Hurd Internet: Hurd Inferno Internet: Inferno IRIX Internet: IRIX JavaOS Internet: JavaOS LFS Internet: LFS Linspire Internet: Linspire Linux Internet: Linux MacOS Internet: MacOS Minix Internet: Minix MorphOS Internet: MorphOS MS-DOS Internet: MS-DOS MVS Internet: MVS NetBSD Internet: NetBSD NetWare Internet: NetWare Newdeal Internet: Newdeal NEXTSTEP Internet: NEXTSTEP OpenBSD Internet: OpenBSD OS/2 Internet: OS/2 Further operating systems Internet: Further operating systems PalmOS Internet: PalmOS Plan9 Internet: Plan9 QNX Internet: QNX RiscOS Internet: RiscOS Solaris Internet: Solaris SuSE Linux Internet: SuSE Linux Unicos Internet: Unicos Unix Internet: Unix Unixware Internet: Unixware Windows 2000 Internet: Windows 2000 Windows 3.11 Internet: Windows 3.11 Windows 95 Internet: Windows 95 Windows 98 Internet: Windows 98 Windows CE Internet: Windows CE Windows Family Internet: Windows Family Windows ME Internet: Windows ME Seite 1 von 138 eBook - Informations about Operating Systems Version: August 15, 2006 | Download: www.operating-system.org Windows NT 3.1 Internet: Windows NT 3.1 Windows NT 4.0 Internet: Windows NT 4.0 Windows Server 2003 Internet: Windows Server 2003 Windows Vista Internet: Windows Vista Windows XP Internet: Windows XP Apple - Company Internet: Apple - Company AT&T - Company Internet: AT&T - Company Be Inc. - Company Internet: Be Inc. - Company BSD Family Internet: BSD Family Cray Inc. -

Code Review Guide
CODE REVIEW GUIDE 2.0 RELEASE Project leaders: Larry Conklin and Gary Robinson Creative Commons (CC) Attribution Free Version at: https://www.owasp.org 1 F I 1 Forward - Eoin Keary Introduction How to use the Code Review Guide 7 8 10 2 Secure Code Review 11 Framework Specific Configuration: Jetty 16 2.1 Why does code have vulnerabilities? 12 Framework Specific Configuration: JBoss AS 17 2.2 What is secure code review? 13 Framework Specific Configuration: Oracle WebLogic 18 2.3 What is the difference between code review and secure code review? 13 Programmatic Configuration: JEE 18 2.4 Determining the scale of a secure source code review? 14 Microsoft IIS 20 2.5 We can’t hack ourselves secure 15 Framework Specific Configuration: Microsoft IIS 40 2.6 Coupling source code review and penetration testing 19 Programmatic Configuration: Microsoft IIS 43 2.7 Implicit advantages of code review to development practices 20 2.8 Technical aspects of secure code review 21 2.9 Code reviews and regulatory compliance 22 5 A1 3 Injection 51 Injection 52 Blind SQL Injection 53 Methodology 25 Parameterized SQL Queries 53 3.1 Factors to Consider when Developing a Code Review Process 25 Safe String Concatenation? 53 3.2 Integrating Code Reviews in the S-SDLC 26 Using Flexible Parameterized Statements 54 3.3 When to Code Review 27 PHP SQL Injection 55 3.4 Security Code Review for Agile and Waterfall Development 28 JAVA SQL Injection 56 3.5 A Risk Based Approach to Code Review 29 .NET Sql Injection 56 3.6 Code Review Preparation 31 Parameter collections 57 3.7 Code Review Discovery and Gathering the Information 32 3.8 Static Code Analysis 35 3.9 Application Threat Modeling 39 4.3.2. -

Introduction to Yasca
Introduction To Yasca Presented at NYPHP 24 February 2009 Michael V. Scovetta Agenda . Who Am I? . What is Yasca? . How does it work? . Requirements . How should I use it? . The Future of Yasca . Demonstration . Questions? 2 Who Am I? . Development . CA ~2002 . Perl, Java, PHP . Information Security . UBS ~2005 . Security Consulting . Cigital ~2008 . Architecture . CA ~2008 3 What is Yasca? . Yasca started as a set of perl scripts that grepped through source code looking for XSS vulnerabilities. <%=request.getParameter("foo")%> . <?=$_REQUEST["foo"]?> . Then I needed to do multi-line searches: . String s = request.getParameter("foo"); out.println(s); . As I wrote more rules, I found other scanners that already had many of them. So I made calls out to them. Then everything got nasty and I wrote it all from scratch again in PHP. 4 What is Yasca? . Yasca is an open-source tool that can help you analyze program source code. It leverages several static analysis tools. PMD (http://pmd.sourceforge.net/) . J-Lint (http://artho.com/jlint/) . Pixy (http://pixybox.seclab.tuwien.ac.at/pixy/) . FindBugs (http://findbugs.sourceforge.net/) . It can be used to scan virtually any file type, not only traditional source code. Yasca is written in command-line PHP and released under the BSD license. 5 How Does it Work? . Architecture based on plug-ins. "Major Plug-in" => calls another tool to do the scan . e.g. PMD, J-Lint, FindBugs, Pixy, Grep . "Minor Plug-in" => uses embedded logic . Relatively easy to write, extremely flexible Report Plug-in Yasca Plug-in Generator Plug-in Output /tmp/my_source_code 6 How Does it Work . -

Partitioners Track: Generating Security Vulnerabilities in Source Code
M. Meier,D.Reinhardt, S. Wendzel (Hrsg.): Sicherheit 2016, Lecture Notes in Informatics (LNI), Gesellschaft fur¨ Informatik, Bonn 2016 177 Partitioners Track: Generating Security Vulnerabilities in Source Code Felix Schuckert1 Abstract: This paper describes aframework, which modifies existing source code to generate secu- rity issues. An example plugin for generating SQL injection in Java source code is described. The generation process is based on static code analysis techniques likedataflowanalysis and abstract syntax trees. The framework is evaluated with the help of Java projects from GitHub.One modified project wassuccessfully used in acapture the flag event as achallenge. Keywords: Software security,sql injection, generating, static code analysis 1Introduction Modern software products usually have aconnection to the internet. All of them are ex- posed to attackers that want to exploit the software. The top security issues remained the same overthe last years. Software developers have to protect their software from attackers by developing secure software. As stated in the paper [PE09], software security can’tbe provided only by the operating system. The software must have no vulnerabilities as well. Developers usually write tests, if common security vulnerabilities in their programs do exist, butthis will not guarantee the security of the developed software. Instead it will ve- rify the defined function requirements [Ba]. Static code analyzer tools help to find existing security issues in source code. These issues have to be reviewed and fixed manually by software developers. Fixing such issues requires ahigh amount of skill in software secu- rity.Another problem is that some security issues might not be detected by using code analyzer.Atbest all software developers should have software security skills to prevent software security issues preemptively in the development process. -

Avm Faculdade Integrada Pós-Graduação Em Docência Do Ensino Superior
1 AVM FACULDADE INTEGRADA PÓS-GRADUAÇÃO EM DOCÊNCIA DO ENSINO SUPERIOR O ENGRANDECER ACADÊMICO UTILIZANDO FERRAMENTAS DE CÓDIGO ABERTO. Por: Rodrigo Bastos Farias Orientadores: Prof. Dr. Vilson Sérgio de Carvalho e Profª. Ana Paula Oliveira. Rio de Janeiro 2014 2 AVM FACULDADE INTEGRADA PÓS-GRADUAÇÃO EM DOCÊNCIA DO ENSINO SUPERIOR O ENGRADECER ACADÊMICO UTILIZANDO FERRAMENTAS DE CÓDIGO ABERTO. Apresentação de monografia ao Instituto A Vez do Mestre. Como requisito parcial para obtenção do grau de especialista em Docência do Ensino Superior. Por: Rodrigo Bastos Farias Rio de Janeiro 2014 3 AGRADECIMENTOS Agradeço a todos aqueles que direta ou indiretamente contribuíram para a elaboração desta monografia e, de modo especial, ao Professor Doutor Vilson Sérgio de Carvalho, pelo incentivo constante e pela segura orientação. 4 DEDICATÓRIA Ao Senhor DEUS, fonte da minha vida e saúde. Aos meus avós, pais, esposa, filha e amigos, pelo incentivo e carinho constantes. E a Todos que contribuíram para a realização desta monografia. 5 EPÍGRAFE ―A tendência democrática de escola não pode consistir apenas em que um operário manual se torne qualificado, mas em que cada cidadão possa se tornar governante‖ (ANTONIO GRAMSCI) ―Uma pessoa com ubuntu está aberta e disponível aos outros, não-preocupada em julgar os outros como bons ou maus, e tem consciência de que faz parte de algo maior e que é tão diminuída quanto seus semelhantes que são diminuídos ou humilhados, torturados ou oprimidos.‖. (ARCEBISPO DESMOND TUTU) 6 RESUMO Esse documento presente ratifica -

C.B.S.E. PAPER Informatics with CBSE 2018 Marking Class–XII Practices Scheme Delhi/Outside Delhi
SOLVED C.B.S.E. PAPER Informatics with CBSE 2018 Marking Class–XII Practices Scheme Delhi/Outside Delhi Time : 3 Hours Max. Marks : 70 General Instructions : (i) All questions are compulsory. (ii) Answer the questions after carefully reading the text. 1. (a) ABC Company wants to link its computers in the Head office in New Delhi to its office in Sydney. Name the type of Network that will be formed. Which communication media should be used to form this Network ? 2 (b) Which of the following is/are not communication media ? (i) Microwaves (ii) Optical Fiber cable (iii) Node (iv) Radio waves Identify which of the above mentioned communication media are Wired media and which ones are Wireless media. (c) Write two examples each of software in the following categories : (i) Open Source Operating System 2 (ii) Open Source Web Browser (d) Expand the following terms : 2 (i) GSM (ii) IP (e) Name the devices : (i) This device constantly looks at all the data entering and exiting your connection. It can block or reject data in response to an established rule. (ii) This device connects multiple nodes to form a network. It redirects the received information only to the intended node(s). 2 2. (a) Identify the invalid variable names. State the reason if invalid. 1 (i) Marks Unit (ii) Product _1 (iii) Sales123 (iv) 2Marks (b) Write the data type of variables that should be used to store : 1 (i) Marks of students (ii) Grades of students (Grade can be 'A' or 'B' or 'C') (c) Write examples of any two properties and any two methods of jButton component. -

Opensource Software Im Alltag
OpensourceOpensource SoftwareSoftware imim AlltagAlltag -- IstIst dasdas möglich?möglich? Willkommen zum Xing Stammtisch Alexander Demmler – 25.11.2016 © A. Demmler 2016 www.lacunasolutions.com 1 Marktanteile Desktop Systeme 2016 © A. Demmler 2016 www.lacunasolutions.com 2 Webserver Systeme © A. Demmler 2016 www.lacunasolutions.com 3 Einsatz von OSS in US Unternehmen: Northbridge Eine Venture Capital Company. Game changers disrupt existing markets. They also create new multi-billion dollar markets and have the potential to change the way we live and work. http://www.northbridge.com © A. Demmler 2016 www.lacunasolutions.com 4 Was bedeutet OpenSource? • OpenSource Software (OSS) ist professionelle Software unter einer alternativen Entwicklungs- und Vertriebsform • OpenSource ist nicht Linux - aber Linux ist auch OpenSource! • OpenSource bedeutet ein Stück Freiheit: - freie Auswahl - Freiheit ob und wieviel man bezahlt - Freiheit in der Nutzung © A. Demmler 2016 www.lacunasolutions.com 5 Was ist die Community? • Die Community besteht aus - Entwicklern + Beratern + Anwendern + Hobbyisten - grossen Unternehmen (HP, IBM, SUN) - Distributoren wie SUSE, RedHat, Ubuntu u.a. • Die Community entwickelt und pflegt gemeinsam die Software und bietet Unterstützung (Support) • Die Community ist kein Club von Hackern, Freaks und anderen Bösewichten! © A. Demmler 2016 www.lacunasolutions.com 6 Das Geschäftsmodell Freie Software Dienstleistungen (Kosten) Basis Version Erweiterungen Download im WWW Service + Support Online Support Schulungen Zusatzeinkünfte Werbung + Sponsoren © A. Demmler 2016 www.lacunasolutions.com 7 Lizenzrechtliches • Softwarecode (Quellen) sind offen gelegt: - Verbreitung und Nutzung sind ausdrücklich erlaubt - Veränderung (Anpassung, Erweiterung) erlaubt - Quellcode muss offengelegt werden • Es gibt historisch bedingt verschiedene Lizenzmodelle. (GPL, OSL, CPL, EPL u.a) • EU Initiative um Lizenzen vereinen: http://ec.europa.eu ACHTUNG: Auch hier gelten Vorschriften! Computerwoche: http://www.computerwoche.de © A. -

Tcc Engenharia Eletrica
UNIVERSIDADE DO SUL DE SANTA CATARINA MAX BACK SISTEMA EMBARCADO COM RTOS: UMA ABORDAGEM PRÁTICA E VOLTADA A PORTABILIDADE Palhoça 2018 MAX BACK SISTEMA EMBARCADO COM RTOS: UMA ABORDAGEM PRÁTICA E VOLTADA A PORTABILIDADE Trabalho de Conclusão de Curso apresentado ao Curso de Graduação em Engenharia Elétrica com ênfase em Telemática da Universidade do Sul de Santa Catarina como requisito parcial à obtenção do título de Engenheiro Eletricista. Orientador: Prof. Djan de Almeida do Rosário, Esp. Eng. Palhoça 2018 Dedico este trabalho а Deus, por ser o verdadeiro princípio e fim de todas as coisas (das que valem a pena). AGRADECIMENTOS Agradeço a minha esposa Gizele e meus filhos, Eric e Thomas, meus pais e a toda minha família que, com muito carinho е apoio, não mediram esforços para que eu chegasse até esta etapa de minha vida. Agradeço aos professores do curso por terem transmitido seu conhecimento a mim e meus colegas com tanto empenho e dedicação. Não existe triunfo sem perda, não há vitória sem sofrimento, não há liberdade sem sacrifício. (O Senhor dos Anéis – J.R.R. Tolkien, 1954) RESUMO A crescente demanda pelo desenvolvimento de solução conectadas entre sistemas já existentes, assim como a ampliação do uso destes sistemas embarcados mostram a importância de soluções robustas, de tempo real, com ciclos de desenvolvimento cada vez mais curtos e necessidade de reaproveitamento de código. Este trabalho apresenta a seleção do sistema operacional de tempo real FreeRTOS e o experimento de sua utilização como base para o desenvolvimento de um controlador wearable (vestível) em duas plataformas de hardware diferentes, implementando a solução inicialmente em uma delas e depois portando para a outra plataforma, desenvolvendo principalmente a programação específica do novo hardware e procurando manter a parte da aplicação inalterada e independente de plataforma. -

Sistemas Operativos Modernos Compilación Bibliográfica
SISTEMAS OPERATIVOS MODERNOS COMPILACIÓN BIBLIOGRÁFICA Katherine Osorio Lopez 906538 Docente: Carlos Hernan Gomez Materia: Sistemas Operativos UNIVERSIDAD NACIONAL DE COLOMBIA Facultad de Administración Departamento de Informática y Computación Manizales Noviembre 2015 Tabla de contenido INTRODUCCIÓN ........................................................................................................................... 5 HISTORIA Y EVOLUCIÓN DE LOS SISTEMAS Y LA EMPRESA O GRUPO EMPRESARIAL QUE LO RESPALDA ..................................................................................... 6 DESCRIPCIÓN GENERAL DE LOS DISTINTOS SISTEMAS OPERATIVOS/SUBTEMAS (CARACTERISTICAS GENERALES, AMBIENTE, PLATAFORMA) .......................................................................................................................... 10 SISTEMA OPERATIVO ZORIN ................................................................................................ 15 i. Presentación ......................................................................................................................... 15 ii. Estructura y Componentes del sistema ........................................................................... 16 iii. Plataformas sobre las que trabaja ................................................................................... 17 iv. Proceso de Instalación ...................................................................................................... 17 v. Gestión de procesos y del procesador ...........................................................................