Advanced Automated Administration with Windows Powershell MOC 10962
Total Page:16
File Type:pdf, Size:1020Kb
Load more
Recommended publications
-

Attacker Antics Illustrations of Ingenuity
ATTACKER ANTICS ILLUSTRATIONS OF INGENUITY Bart Inglot and Vincent Wong FIRST CONFERENCE 2018 2 Bart Inglot ◆ Principal Consultant at Mandiant ◆ Incident Responder ◆ Rock Climber ◆ Globetrotter ▶ From Poland but live in Singapore ▶ Spent 1 year in Brazil and 8 years in the UK ▶ Learning French… poor effort! ◆ Twitter: @bartinglot ©2018 FireEye | Private & Confidential 3 Vincent Wong ◆ Principal Consultant at Mandiant ◆ Incident Responder ◆ Baby Sitter ◆ 3 years in Singapore ◆ Grew up in Australia ©2018 FireEye | Private & Confidential 4 Disclosure Statement “ Case studies and examples are drawn from our experiences and activities working for a variety of customers, and do not represent our work for any one customer or set of customers. In many cases, facts have been changed to obscure the identity of our customers and individuals associated with our customers. ” ©2018 FireEye | Private & Confidential 5 Today’s Tales 1. AV Server Gone Bad 2. Stealing Secrets From An Air-Gapped Network 3. A Backdoor That Uses DNS for C2 4. Hidden Comment That Can Haunt You 5. A Little Known Persistence Technique 6. Securing Corporate Email is Tricky 7. Hiding in Plain Sight 8. Rewriting Import Table 9. Dastardly Diabolical Evil (aka DDE) ©2018 FireEye | Private & Confidential 6 AV SERVER GONE BAD Cobalt Strike, PowerShell & McAfee ePO (1/9) 7 AV Server Gone Bad – Background ◆ Attackers used Cobalt Strike (along with other malware) ◆ Easily recognisable IOCs when recorded by Windows Event Logs ▶ Random service name – also seen with Metasploit ▶ Base64-encoded script, “%COMSPEC%” and “powershell.exe” ▶ Decoding the script yields additional PowerShell script with a base64-encoded GZIP stream that in turn contained a base64-encoded Cobalt Strike “Beacon” payload. -
Powershell Integration with Vmware View 5.0
PowerShell Integration with VMware® View™ 5.0 TECHNICAL WHITE PAPER PowerShell Integration with VMware View 5.0 Table of Contents Introduction . 3 VMware View. 3 Windows PowerShell . 3 Architecture . 4 Cmdlet dll. 4 Communication with Broker . 4 VMware View PowerCLI Integration . 5 VMware View PowerCLI Prerequisites . 5 Using VMware View PowerCLI . 5 VMware View PowerCLI cmdlets . 6 vSphere PowerCLI Integration . 7 Examples of VMware View PowerCLI and VMware vSphere PowerCLI Integration . 7 Passing VMs from Get-VM to VMware View PowerCLI cmdlets . 7 Registering a vCenter Server . .. 7 Using Other VMware vSphere Objects . 7 Advanced Usage . 7 Integrating VMware View PowerCLI into Your Own Scripts . 8 Scheduling PowerShell Scripts . 8 Workflow with VMware View PowerCLI and VMware vSphere PowerCLI . 9 Sample Scripts . 10 Add or Remove Datastores in Automatic Pools . 10 Add or Remove Virtual Machines . 11 Inventory Path Manipulation . 15 Poll Pool Usage . 16 Basic Troubleshooting . 18 About the Authors . 18 TECHNICAL WHITE PAPER / 2 PowerShell Integration with VMware View 5.0 Introduction VMware View VMware® View™ is a best-in-class enterprise desktop virtualization platform. VMware View separates the personal desktop environment from the physical system by moving desktops to a datacenter, where users can access them using a client-server computing model. VMware View delivers a rich set of features required for any enterprise deployment by providing a robust platform for hosting virtual desktops from VMware vSphere™. Windows PowerShell Windows PowerShell is Microsoft’s command line shell and scripting language. PowerShell is built on the Microsoft .NET Framework and helps in system administration. By providing full access to COM (Component Object Model) and WMI (Windows Management Instrumentation), PowerShell enables administrators to perform administrative tasks on both local and remote Windows systems. -

Run-Commands-Windows-10.Pdf
Run Commands Windows 10 by Bettertechtips.com Command Action Command Action documents Open Documents Folder devicepairingwizard Device Pairing Wizard videos Open Videos Folder msdt Diagnostics Troubleshooting Wizard downloads Open Downloads Folder tabcal Digitizer Calibration Tool favorites Open Favorites Folder dxdiag DirectX Diagnostic Tool recent Open Recent Folder cleanmgr Disk Cleanup pictures Open Pictures Folder dfrgui Optimie Drive devicepairingwizard Add a new Device diskmgmt.msc Disk Management winver About Windows dialog dpiscaling Display Setting hdwwiz Add Hardware Wizard dccw Display Color Calibration netplwiz User Accounts verifier Driver Verifier Manager azman.msc Authorization Manager utilman Ease of Access Center sdclt Backup and Restore rekeywiz Encryption File System Wizard fsquirt fsquirt eventvwr.msc Event Viewer calc Calculator fxscover Fax Cover Page Editor certmgr.msc Certificates sigverif File Signature Verification systempropertiesperformance Performance Options joy.cpl Game Controllers printui Printer User Interface iexpress IExpress Wizard charmap Character Map iexplore Internet Explorer cttune ClearType text Tuner inetcpl.cpl Internet Properties colorcpl Color Management iscsicpl iSCSI Initiator Configuration Tool cmd Command Prompt lpksetup Language Pack Installer comexp.msc Component Services gpedit.msc Local Group Policy Editor compmgmt.msc Computer Management secpol.msc Local Security Policy: displayswitch Connect to a Projector lusrmgr.msc Local Users and Groups control Control Panel magnify Magnifier -
View the Slides (Smith)
Network Shells Michael Smith Image: https://commons.wikimedia.org/wiki/File:Network-connections.png What does a Shell give us? ● A REPL ● Repeatability ● Direct access to system operations ● User-focused design ● Hierarchical context & sense of place Image: https://upload.wikimedia.org/wikipedia/commons/8/84/Bash_demo.png What does a Shell give us? ● A REPL ● Repeatability ● Direct access to system operations ● User-focused design ● Hierarchical context & sense of place Image: https://upload.wikimedia.org/wikipedia/commons/8/84/Bash_demo.png Management at a distance (netsh) Netsh: Configure DHCP servers with netsh -r RemoteMachine -u domain\username [RemoteMachine] netsh>interface [RemoteMachine] netsh interface>ipv6 [RemoteMachine] netsh interface ipv6>show interfaces Reference: https://docs.microsoft.com/en-us/windows-server/networking/technologies/netsh/netsh-contexts Management at a distance (netsh) Netsh: Configure DHCP servers with netsh Location-r RemoteMachine -u domain\username Hierarchical [RemoteMachine] netsh>interfacecontext Simpler [RemoteMachine] netsh interface>ipv6 commands [RemoteMachine] netsh interface ipv6>show interfaces Reference: https://docs.microsoft.com/en-us/windows-server/networking/technologies/netsh/netsh-contexts Management at a distance (WSMan) WSMan (in Powershell): Manage Windows remotely with Set-Location -Path WSMan:\SERVER01 Get-ChildItem -Path . Set-Item Client\TrustedHosts *.domain2.com -Concatenate Reference: https://docs.microsoft.com/en-us/powershell/module/microsoft.wsman.management/about/about_wsman_provider -

Revoke Obfuscation Report
Revoke-Obfuscation: PowerShell Obfuscation Detection Using Science Daniel Bohannon @danielhbohannon | Lee Holmes @Lee_Holmes Revoke-Obfuscation is the result of industry research collaboration between Daniel Bohannon - Senior Applied Security Researcher at Mandiant/FireEye, and Lee Holmes – Lead Security Architect of Azure ManaGement at Microsoft. Background By far the most prevalent delivery and execution vehicle for malware in the industry today is basic malicious executables and malicious documents. While not represented accurately by its popularity in the news, a small portion of the current malware ecosystem leverages PowerShell as part of its attack chain. Of malware that uses PowerShell, the most prevalent use is the garden-variety stager: an executable or document macro that launches PowerShell to download another executable and run it. Despite its relative statistical rarity, development of malicious and offense-focused PowerShell techniques has been a rich field of innovation. Commercial products have started to react to these techniques in several ways. Because they are often delivered as script files, Antivirus vendors have long had the ability to write signatures that block malicious PowerShell scripts. With the release of Windows 10, some vendors have additionally begun to implement support for Windows’ Antimalware Scan Interface. This interface gives Antivirus vendors the ability to implement deep content scanning, providing visibility as each stage of malware fetches and dynamically executes new instructions from a remote network location. In addition to antivirus signatures, many SIEM vendors have started to implement alerting based on command-line parameters that are frequently used in malicious contexts. Palo Alto provides an excellent survey of commonly-used malicious PowerShell command-line arguments in their post, Pulling Back the Curtains on EncodedCommand PowerShell Attacks. -
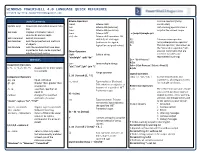
WINDOWS POWERSHELL 4.0 LANGUAGE QUICK REFERENCE Created By
WINDOWS POWERSHELL 4.0 LANGUAGE QUICK REFERENCE Created by http://powershellmagazine.com Useful Commands Bitwise Operators , Comma operator (Array -band Bitwise AND constructor) Update-Help Downloads and installs newest help -bor Bitwise OR (inclusive) . Dot-sourcing operator runs a files -bxor Bitwise OR (exclusive) script in the current scope Get-Help Displays information about -bnot Bitwise NOT . c:\scripts\sample.ps1 commands and concepts -shl, -shr Bitwise shift operators. Bit Get-Command Gets all commands shift left, bit shift right $( ) Subexpression operator Get-Member Gets the properties and methods (arithmetic for signed, @( ) Array subexpression operator of objects logical for unsigned values) & The call operator, also known as Get-Module Gets the modules that have been the "invocation operator," lets imported or that can be imported Other Operators you run commands that are into the current session -Split Splits a string stored in variables and “abcdefghi” -split “de” represented by strings. Operators $a = "Get-Process" -join Joins multiple strings & $a Assignment Operators “abc”,”def”,”ghi” -join “;” $sb = { Get-Process | Select –First 2 } =, +=, -=, *=, /=, %=, ++, -- Assigns one or more values & $sb to a variable .. Range operator Logical Operators 1..10 | foreach {$_ * 5} Comparison Operators -and, -or, -xor, -not, ! Connect expressions and -eq, -ne Equal, not equal statements, allowing you to test -is, -isnot Type evaluator (Boolean). -gt, -ge Greater than, greater than for multiple conditions Tells whether an object is an or equal to Redirection Operators instance of a specified .NET -lt, -le Less than, less than or >, >> The redirection operators enable Framework type. equal to you to send particular types of 42 –is [int] -replace changes the specified output (success, error, warning, elements of a value verbose, and debug) to files and -as Type convertor. -

How to Evade Application Whitelisting Using REGSVR32
EXTERNAL/INTERNAL, RED TEAM, RED TEAM TOOLS CASEY SMITH, COM+ SCRIPLETS, DLL, FOLLOW US 10 SUBTEE, WEVADE, WHITELISTING MAY 2017 How to Evade Application Whitelisting Using REGSVR32 Jo Thyer // I was recently working on a Red Team for a customer that was very much up to date with their defenses. This customer had tight egress controls, perimeter proxying, strong instrumentation, and very tight application whitelisting controls. My teammate and I knew that we would have to work very hard to get command and control outbound from this environment, and that would be after obtaining physical access (yet another signicant challenge). Create PDF in your applications with the Pdfcrowd HTML to PDF API PDFCROWD The week before going on-site, we began to LOOKING FOR research all of the various methods for SOMETHING? potential application whitelisting bypass. We assumed the best case defensive scenario whereby the customer would have all binary execution blocked with the exception of specic applications permitted. In prior tests SUBSCRIBE TO THE with other customers and this same BHISBLOG customer, we had used “rundll32.exe” to execute DLL content. This method is really useful if you can host shellcode Don't get left in the dark! Enter within a DLL, and have a nice controlled entry point. In the Metasploit case, the your email address and every DLL entry point is named “Control_RunDLL”. While this might evade time a post goes live you'll get instant notication! We'll also whitelisting, we also knew this old trick had been played before and we likely add you to our webcast list, so could not count on it again. -

Windows Powershell 1.0 Essentials
Windows PowerShell Essentials Windows PowerShell Essentials Windows PowerShell Essentials – Edition 1.0 © 2009 Payload Media. This eBook is provided for personal use only. Unauthorized use, reproduction and/or distribution strictly prohibited. All rights reserved. The content of this book is provided for informational purposes only. Neither the publisher nor the author offers any warranties or representation, express or implied, with regard to the accuracy of information contained in this book, nor do they accept any liability for any loss or damage arising from any errors or omissions. Find more eBooks at www.ebookfrenzy.com 2 © 2009 Payload Media Windows PowerShell Essentials Table of Contents Chapter 1. Installing Windows PowerShell ............................................................................... 10 1.1 Installing Windows PowerShell on Windows Server 2008 ............................................ 10 1.2 Performing a Windows Server 2008 PowerShell Command Line Installation ............... 10 1.3 Installing PowerShell on Windows Server 2003, XP and Vista Systems ........................ 11 Chapter 2. The Basics of the Windows PowerShell Interactive Shell ....................................... 13 2.1 The Windows PowerShell Command Prompt ................................................................ 13 2.2 PowerShell Command Line Editing Keys ........................................................................ 14 2.3 PowerShell Command Completion ............................................................................... -
Windows Powershell Best Practices Windows Powershell Best Practices
Windows PowerShell Best Practices Windows PowerShell Best Practices Expert recommendations, pragmatically applied Automate system administration using Windows PowerShell best practices—and optimize your operational efficiency. With this About the Author practical guide, Windows PowerShell expert and instructor Ed Ed Wilson, MCSE, CISSP, is a well-known Wilson delivers field-tested tips, real-world examples, and candid scripting expert and author of “Hey Windows Scripting Guy!”—one of the most popular advice culled from administrators across a range of business and blogs on Microsoft TechNet. He’s written technical scenarios. If you’re an IT professional with Windows several books on Windows scripting PowerShell experience, this book is ideal. for Microsoft Press, including Windows PowerShell 2.0 Best Practices and Windows PowerShell Scripting Guide. Discover how to: PowerShell • Use Windows PowerShell to automate Active Directory tasks • Explore available WMI classes and methods with CIM cmdlets • Identify and track scripting opportunities to avoid duplication • Use functions to encapsulate business logic and reuse code • Design your script’s best input method and output destination • Test scripts by checking their syntax and performance • Choose the most suitable method for running remote commands • Manage software services with Desired State Configuration Wilson BEST PRACTICES microsoft.com/mspress ISBN 978-0-7356-6649-8 U.S.A. $59.99 55999 Canada $68.99 [Recommended] 9 780735 666498 Operating Systems/Windows Server Celebrating 30 years! Ed Wilson 666498_Win_PowerShell_Best_Practices.indd 1 4/11/14 10:30 AM Windows PowerShell Best Practices Ed Wilson 666498_book.indb 1 12/20/13 10:50 AM Published with the authorization of Microsoft Corporation by: O’Reilly Media, Inc. -

Office 365+ RAP Prerequisites and Requirements
Office 365+ RAP Prerequisites and Requirements How to prepare for your Office 365+ Assessment for HIPAA/HITRUST/PCI DSS/NIST Cybersecurity framework. The tool that will be downloaded from the Risk Assessment Program will be used to connect to each of your Office 365 Tenant(s) and retrieve information from them. Once the data is collected and the survey completed, the online Assessment tool will analyze the data. At a high level, your steps to success are: 1. Install prerequisites on your Tools machine and configure your environment 2. Run discovery and prerequisites checks 3. Collect data from your Office 365 Tenant(s) 4. Complete the online survey A Prerequisite checklist is provided following the Requirements sections, links to the additional software required for the Tools machine which you will need to install are provided below, and detailed steps are provided later in this document. Operating System Requirements The Tool runs on the following versions of Windows • Windows 8.1, installed by default • Windows Server 2012 R2, installed by default • Windows 7 with Service Pack 1, install Windows Management Framework 4.0 to run Windows PowerShell 4.0 • Windows Server 2008 R2 with Service Pack 1, install Windows Management Framework 4.0 to run Windows PowerShell 4.0 Microsoft .NET Framework Requirements The Tool requires the full installation of Microsoft .NET Framework 4.5. Windows 8.1 and Windows Server 2012 R2 include Microsoft .NET Framework 4.5 by default. To install Microsoft .NET Framework 4.5 (dotNetFx45_Full_setup.exe), see Microsoft .NET Framework 4.5 on the Microsoft Download Center. -
Powershell Commands Guide R16.5
Arcserve® Replication and High Availability PowerShell Commands Guide r16.5 Pre-release Document, only for reference This Documentation, which includes embedded help systems and electronically distributed materials, (hereinafter referred to as the “Documentation”) is for your informational purposes only and is subject to change or withdrawal by Arcserve at any time. This Documentation may not be copied, transferred, reproduced, disclosed, modified or duplicated, in whole or in part, without the prior written consent of Arcserve. This Documentation is confidential and proprietary information of Arcserve and may not be disclosed by you or used for any purpose other than as may be permitted in (i) a separate agreement between you and Arcserve governing your use of the Arcserve software to which the Documentation relates; or (ii) a separate confidentiality agreement between you and Arcserve. Notwithstanding the foregoing, if you are a licensed user of the software product(s) addressed in the Documentation, you may print or otherwise make available a reasonable number of copies of the Documentation for internal use by you and your employees in connection with that software, provided that all Arcserve copyright notices and legends are affixed to each reproduced copy. The right to print or otherwise make available copies of the Documentation is limited to the period during which the applicable license for such software remains in full force and effect. Should the license terminate for any reason, it is your responsibility to certify in writing to Arcserve that all copies and partial copies of the Documentation have been returned to Arcserve or destroyed. TO THE EXTENT PERMITTED BY APPLICABLE LAW, ARCSERVE PROVIDES THIS DOCUMENTATION “AS IS” WITHOUT WARRANTY OF ANY KIND, INCLUDING WITHOUT LIMITATION, ANY IMPLIED WARRANTIES OF MERCHANTABILITY, FITNESS FOR A PARTICULAR PURPOSE, OR NONINFRINGEMENT. -

Chapter 1. the Powershell Console
Chapter 1. The PowerShell Console Welcome to PowerShell! This chapter will introduce you to the PowerShell console and show you how to configure it, including font colors and sizes, editing and display options. Topics Covered: Starting PowerShell First Steps with the Console o Incomplete and Multi-Line Entries o Important Keyboard Shortcuts o Deleting Incorrect Entries o Overtype Mode o Command History: Reusing Entered Commands o Automatically Completing Input o Scrolling Console Contents o Selecting and Inserting Text o QuickEdit Mode o Standard Mode Customizing the Console o Opening Console Properties o Defining Options o Specifying Fonts and Font Sizes o Setting Window and Buffer Size o Selecting Colors o Directly Assigning Modifications in PowerShell o Saving Changes Piping and Routing o Piping: Outputting Information Page by Page o Redirecting: Storing Information in Files Summary Starting PowerShell On Windows 7 and Server 2008 R2, Windows PowerShell is installed by default. To use PowerShell on older systems, you need to download and install it. The update is free. The simplest way to find the appropriate download is to visit an Internet search engine and search for "KB968930 Windows XP" (replace the operating system with the one you use). Make sure you pick the correct update. It needs to match your operating system language and architecture (32-bit vs. 64-bit). After you installed PowerShell, you'll find PowerShell in the Accessories program group. Open this program group, click on Windows PowerShell and then launch the PowerShell executable. On 64-bit systems, you will also find a version marked as (x86) so you can run PowerShell both in the default 64-bit environment and in an extra 32-bit environment for backwards compatibility.