Privacy and Authentication: an Introduction to Cryptography
Total Page:16
File Type:pdf, Size:1020Kb
Load more
Recommended publications
-

Butler Lampson, Martin Abadi, Michael Burrows, Edward Wobber
Outline • Chapter 19: Security (cont) • A Method for Obtaining Digital Signatures and Public-Key Cryptosystems Ronald L. Rivest, Adi Shamir, and Leonard M. Adleman. Communications of the ACM 21,2 (Feb. 1978) – RSA Algorithm – First practical public key crypto system • Authentication in Distributed Systems: Theory and Practice, Butler Lampson, Martin Abadi, Michael Burrows, Edward Wobber – Butler Lampson (MSR) - He was one of the designers of the SDS 940 time-sharing system, the Alto personal distributed computing system, the Xerox 9700 laser printer, two-phase commit protocols, the Autonet LAN, and several programming languages – Martin Abadi (Bell Labs) – Michael Burrows, Edward Wobber (DEC/Compaq/HP SRC) Oct-21-03 CSE 542: Operating Systems 1 Encryption • Properties of good encryption technique: – Relatively simple for authorized users to encrypt and decrypt data. – Encryption scheme depends not on the secrecy of the algorithm but on a parameter of the algorithm called the encryption key. – Extremely difficult for an intruder to determine the encryption key. Oct-21-03 CSE 542: Operating Systems 2 Strength • Strength of crypto system depends on the strengths of the keys • Computers get faster – keys have to become harder to keep up • If it takes more effort to break a code than is worth, it is okay – Transferring money from my bank to my credit card and Citibank transferring billions of dollars with another bank should not have the same key strength Oct-21-03 CSE 542: Operating Systems 3 Encryption methods • Symmetric cryptography – Sender and receiver know the secret key (apriori ) • Fast encryption, but key exchange should happen outside the system • Asymmetric cryptography – Each person maintains two keys, public and private • M ≡ PrivateKey(PublicKey(M)) • M ≡ PublicKey (PrivateKey(M)) – Public part is available to anyone, private part is only known to the sender – E.g. -

Vigenère Cipher Cryptanalysis
Spring 2015 Chris Christensen MAT/CSC 483 Cryptanalysis of the Vigenère Cipher: Kasiski Test The keyword of a Vigenère cipher describes the rotation among the Caesar cipher alphabets that are used. That rotation leads to patterns that can be exploited by a cryptanalyst. If we know the length of the keyword, we can often determine the keyword and, hence, decrypt all messages encrypted with that keyword. Here is a ciphertext message that has been encrypted with a Vigenère cipher. nifon aicum niswt luvet vxshk nissx wsstb husle chsnv ytsro cdsoy nisgx lnona chvch gnonw yndlh sfrnh npblr yowgf unoca cossu ouoll iuvef issoe xgosa cpbew uormh lftaf cmwak bbbdv cqvek muvil qbgnh ntiri ljgig atwnv yuvev iorim cpbsb hxviv buvet vxshk uorim mjbdb pjrut fbueg ntgof yuwmx miodm ipdek uuswx lfjek sewfy yssnm zscmm bpgeb huvez ysaag usaew mffvb wfgim qpilw bbjeu yfbef vbfrt mtwnz uorig wpbvx hjsnm zpfag uhsnm npglb jbqrh mttrh huwek mpfak ljjen hbbnh ooqew vzdak udvum yucbx yoquf vffew vzonx hjumt lfgef vmwnz uxsiz bumag xbbtb kvotx xumpx qswtx l Assume that, somehow, we have discovered that the keyword has length five (which is conveniently the same as the size of the blocks). Then the first letter of each block is encrypted with the same row of the Vigenère square – they are encrypted with the same Caesar cipher. Similarly, the second letter of each block is encrypted with the same row – the same Caesar cipher. The third letters with the same Caesar cipher. The fourth letters with the same Caesar cipher. And, the fifth letters with the same Caesar cipher. -
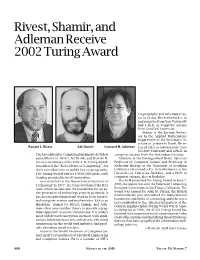
Rivest, Shamir, and Adleman Receive 2002 Turing Award, Volume 50
Rivest, Shamir, and Adleman Receive 2002 Turing Award Cryptography and Information Se- curity Group. He received a B.A. in mathematics from Yale University and a Ph.D. in computer science from Stanford University. Shamir is the Borman Profes- sor in the Applied Mathematics Department of the Weizmann In- stitute of Science in Israel. He re- Ronald L. Rivest Adi Shamir Leonard M. Adleman ceived a B.S. in mathematics from Tel Aviv University and a Ph.D. in The Association for Computing Machinery (ACM) has computer science from the Weizmann Institute. named RONALD L. RIVEST, ADI SHAMIR, and LEONARD M. Adleman is the Distinguished Henry Salvatori ADLEMAN as winners of the 2002 A. M. Turing Award, Professor of Computer Science and Professor of considered the “Nobel Prize of Computing”, for Molecular Biology at the University of Southern their contributions to public key cryptography. California. He earned a B.S. in mathematics at the The Turing Award carries a $100,000 prize, with University of California, Berkeley, and a Ph.D. in funding provided by Intel Corporation. computer science, also at Berkeley. As researchers at the Massachusetts Institute of The ACM presented the Turing Award on June 7, Technology in 1977, the team developed the RSA 2003, in conjunction with the Federated Computing code, which has become the foundation for an en- Research Conference in San Diego, California. The tire generation of technology security products. It award was named for Alan M. Turing, the British mathematician who articulated the mathematical has also inspired important work in both theoret- foundation and limits of computing and who was a ical computer science and mathematics. -

Chapter 3 – Block Ciphers and the Data Encryption Standard
Chapter 3 –Block Ciphers and the Data Cryptography and Network Encryption Standard Security All the afternoon Mungo had been working on Stern's Chapter 3 code, principally with the aid of the latest messages which he had copied down at the Nevin Square drop. Stern was very confident. He must be well aware London Central knew about that drop. It was obvious Fifth Edition that they didn't care how often Mungo read their messages, so confident were they in the by William Stallings impenetrability of the code. —Talking to Strange Men, Ruth Rendell Lecture slides by Lawrie Brown Modern Block Ciphers Block vs Stream Ciphers now look at modern block ciphers • block ciphers process messages in blocks, each one of the most widely used types of of which is then en/decrypted cryptographic algorithms • like a substitution on very big characters provide secrecy /hii/authentication services – 64‐bits or more focus on DES (Data Encryption Standard) • stream ciphers process messages a bit or byte at a time when en/decrypting to illustrate block cipher design principles • many current ciphers are block ciphers – better analysed – broader range of applications Block vs Stream Ciphers Block Cipher Principles • most symmetric block ciphers are based on a Feistel Cipher Structure • needed since must be able to decrypt ciphertext to recover messages efficiently • bloc k cihiphers lklook like an extremely large substitution • would need table of 264 entries for a 64‐bit block • instead create from smaller building blocks • using idea of a product cipher 1 Claude -
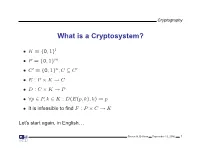
What Is a Cryptosystem?
Cryptography What is a Cryptosystem? • K = {0, 1}l • P = {0, 1}m • C′ = {0, 1}n,C ⊆ C′ • E : P × K → C • D : C × K → P • ∀p ∈ P, k ∈ K : D(E(p, k), k) = p • It is infeasible to find F : P × C → K Let’s start again, in English. Steven M. Bellovin September 13, 2006 1 Cryptography What is a Cryptosystem? A cryptosystem is pair of algorithms that take a key and convert plaintext to ciphertext and back. Plaintext is what you want to protect; ciphertext should appear to be random gibberish. The design and analysis of today’s cryptographic algorithms is highly mathematical. Do not try to design your own algorithms. Steven M. Bellovin September 13, 2006 2 Cryptography A Tiny Bit of History • Encryption goes back thousands of years • Classical ciphers encrypted letters (and perhaps digits), and yielded all sorts of bizarre outputs. • The advent of military telegraphy led to ciphers that produced only letters. Steven M. Bellovin September 13, 2006 3 Cryptography Codes vs. Ciphers • Ciphers operate syntactically, on letters or groups of letters: A → D, B → E, etc. • Codes operate semantically, on words, phrases, or sentences, per this 1910 codebook Steven M. Bellovin September 13, 2006 4 Cryptography A 1910 Commercial Codebook Steven M. Bellovin September 13, 2006 5 Cryptography Commercial Telegraph Codes • Most were aimed at economy • Secrecy from casual snoopers was a useful side-effect, but not the primary motivation • That said, a few such codes were intended for secrecy; I have some in my collection, including one intended for union use Steven M. -

A Covert Encryption Method for Applications in Electronic Data Interchange
Technological University Dublin ARROW@TU Dublin Articles School of Electrical and Electronic Engineering 2009-01-01 A Covert Encryption Method for Applications in Electronic Data Interchange Jonathan Blackledge Technological University Dublin, [email protected] Dmitry Dubovitskiy Oxford Recognition Limited, [email protected] Follow this and additional works at: https://arrow.tudublin.ie/engscheleart2 Part of the Digital Communications and Networking Commons, Numerical Analysis and Computation Commons, and the Software Engineering Commons Recommended Citation Blackledge, J., Dubovitskiy, D.: A Covert Encryption Method for Applications in Electronic Data Interchange. ISAST Journal on Electronics and Signal Processing, vol: 4, issue: 1, pages: 107 -128, 2009. doi:10.21427/D7RS67 This Article is brought to you for free and open access by the School of Electrical and Electronic Engineering at ARROW@TU Dublin. It has been accepted for inclusion in Articles by an authorized administrator of ARROW@TU Dublin. For more information, please contact [email protected], [email protected]. This work is licensed under a Creative Commons Attribution-Noncommercial-Share Alike 4.0 License A Covert Encryption Method for Applications in Electronic Data Interchange Jonathan M Blackledge, Fellow, IET, Fellow, BCS and Dmitry A Dubovitskiy, Member IET Abstract— A principal weakness of all encryption systems is to make sure that the ciphertext is relatively strong (but not that the output data can be ‘seen’ to be encrypted. In other too strong!) and that the information extracted is of good words, encrypted data provides a ‘flag’ on the potential value quality in terms of providing the attacker with ‘intelligence’ of the information that has been encrypted. -

Chapter 3 – Block Ciphers and the Data Encryption Standard
Symmetric Cryptography Chapter 6 Block vs Stream Ciphers • Block ciphers process messages into blocks, each of which is then en/decrypted – Like a substitution on very big characters • 64-bits or more • Stream ciphers process messages a bit or byte at a time when en/decrypting – Many current ciphers are block ciphers • Better analyzed. • Broader range of applications. Block vs Stream Ciphers Block Cipher Principles • Block ciphers look like an extremely large substitution • Would need table of 264 entries for a 64-bit block • Arbitrary reversible substitution cipher for a large block size is not practical – 64-bit general substitution block cipher, key size 264! • Most symmetric block ciphers are based on a Feistel Cipher Structure • Needed since must be able to decrypt ciphertext to recover messages efficiently Ideal Block Cipher Substitution-Permutation Ciphers • in 1949 Shannon introduced idea of substitution- permutation (S-P) networks – modern substitution-transposition product cipher • These form the basis of modern block ciphers • S-P networks are based on the two primitive cryptographic operations we have seen before: – substitution (S-box) – permutation (P-box) (transposition) • Provide confusion and diffusion of message Diffusion and Confusion • Introduced by Claude Shannon to thwart cryptanalysis based on statistical analysis – Assume the attacker has some knowledge of the statistical characteristics of the plaintext • Cipher needs to completely obscure statistical properties of original message • A one-time pad does this Diffusion -

SIGOPS Annual Report 2012
SIGOPS Annual Report 2012 Fiscal Year July 2012-June 2013 Submitted by Jeanna Matthews, SIGOPS Chair Overview SIGOPS is a vibrant community of people with interests in “operatinG systems” in the broadest sense, includinG topics such as distributed computing, storaGe systems, security, concurrency, middleware, mobility, virtualization, networkinG, cloud computinG, datacenter software, and Internet services. We sponsor a number of top conferences, provide travel Grants to students, present yearly awards, disseminate information to members electronically, and collaborate with other SIGs on important programs for computing professionals. Officers It was the second year for officers: Jeanna Matthews (Clarkson University) as Chair, GeorGe Candea (EPFL) as Vice Chair, Dilma da Silva (Qualcomm) as Treasurer and Muli Ben-Yehuda (Technion) as Information Director. As has been typical, elected officers agreed to continue for a second and final two- year term beginning July 2013. Shan Lu (University of Wisconsin) will replace Muli Ben-Yehuda as Information Director as of AuGust 2013. Awards We have an excitinG new award to announce – the SIGOPS Dennis M. Ritchie Doctoral Dissertation Award. SIGOPS has lonG been lackinG a doctoral dissertation award, such as those offered by SIGCOMM, Eurosys, SIGPLAN, and SIGMOD. This new award fills this Gap and also honors the contributions to computer science that Dennis Ritchie made durinG his life. With this award, ACM SIGOPS will encouraGe the creativity that Ritchie embodied and provide a reminder of Ritchie's leGacy and what a difference a person can make in the field of software systems research. The award is funded by AT&T Research and Alcatel-Lucent Bell Labs, companies that both have a strong connection to AT&T Bell Laboratories where Dennis Ritchie did his seminal work. -

Cryptography: DH And
1 ì Key Exchange Secure Software Systems Fall 2018 2 Challenge – Exchanging Keys & & − 1 6(6 − 1) !"#ℎ%&'() = = = 15 & 2 2 The more parties in communication, ! $ the more keys that need to be securely exchanged Do we have to use out-of-band " # methods? (e.g., phone?) % Secure Software Systems Fall 2018 3 Key Exchange ì Insecure communica-ons ì Alice and Bob agree on a channel shared secret (“key”) that ì Eve can see everything! Eve doesn’t know ì Despite Eve seeing everything! ! " (alice) (bob) # (eve) Secure Software Systems Fall 2018 Whitfield Diffie and Martin Hellman, 4 “New directions in cryptography,” in IEEE Transactions on Information Theory, vol. 22, no. 6, Nov 1976. Proposed public key cryptography. Diffie-Hellman key exchange. Secure Software Systems Fall 2018 5 Diffie-Hellman Color Analogy (1) It’s easy to mix two colors: + = (2) Mixing two or more colors in a different order results in + + = the same color: + + = (3) Mixing colors is one-way (Impossible to determine which colors went in to produce final result) https://www.crypto101.io/ Secure Software Systems Fall 2018 6 Diffie-Hellman Color Analogy ! # " (alice) (eve) (bob) + + $ $ = = Mix Mix (1) Start with public color ▇ – share across network (2) Alice picks secret color ▇ and mixes it to get ▇ (3) Bob picks secret color ▇ and mixes it to get ▇ Secure Software Systems Fall 2018 7 Diffie-Hellman Color Analogy ! # " (alice) (eve) (bob) $ $ Mix Mix = = Eve can’t calculate ▇ !! (secret keys were never shared) (4) Alice and Bob exchange their mixed colors (▇,▇) (5) Eve will -

Codebusters Coaches Institute Notes
BEING COVER AGENT FIXED DELAY, PILOT RIGHT PLANE, CATCH SMALL RADIO (CODEBUSTERS) This is the first year CodeBusters will be a National event. A few changes have been made since the North Carolina trial event last year. 1. The Atbash Cipher has been added. 2. The running key cipher has been removed. 3. K2 alphabets have been added in addition to K1 alphabets 4. Hill Cipher decryption has been added with a given decryption matrix. 5. The points scale has been doubled, but the timing bonus has been increased by only 50% in order to further balance the test. 1 TYPES OF PROBLEMS 1.1 ARISTOCRAT (EASY TO HARD DIFFICULTY) http://www.cryptograms.org/tutorial.php An Aristocrat is the typical Crypto-quote you see in the newspaper. Word spaces are preserved. No letter will stand for itself and the replacement table is given as a guide (but doesn’t need to be filled in by the team to get credit). FXP PGYAPYF FIKP ME JAKXPT AY FXP GTAYFMJTGF THE EASIEST TYPE OF CIPHER IS THE ARISTOCRAT A B C D E F G H I J K L M N O P Q R S T U V W X Y Z Frequency 4 1 6 3 1 2 2 2 6 3 3 4 Replacement I F T A Y C P O E R H S 1.2 ARISTOCRATS WITH SPELLING AND/OR GRAMMAR ERRORS (MEDIUM TO VERY HARD DIFFICULTY) For these, either words will be misspelled or grammatical errors introduced. From a student perspective, it is what they might expect when someone finger fumbles a text message or has a bad voice transcription. -

Elementary Cryptanalysis Classification of Cryptanalytic Attacks
12 Elementary Cryptography Elementary Cryptanalysis The most direct attack on a cryptosystem is an exhaustive key search attack. The key size therefore provides a lower bound on the security of a cryptosystem. As an example we compare the key sizes of several of the cryptosystems we have introduced so far. We assume that the alphabet for each is the 26 character alphabet. Substitution ciphers: Simple substitution ciphers: 26! Affine substitution ciphers: ϕ(26) · 26 = 12 · 26 = 312 Translation substitution ciphers: 26 Transposition ciphers: Transposition ciphers (of block length m): m! Enigma : Rotor choices (3 of 5): 60 Rotor positions: 263 = 17576 Plugboard settings: 105578918576 Total combinations: 111339304373506560 The size of the keyspace is a naive measure, but provides an upper bound on the security of a cryptosystem. This measure ignores any structure, like character frequencies, which might remain intact following encryption. Classification of Cryptanalytic Attacks We do not consider enumeration of all keys a valid cryptanalytic attack, since no well- designed cryptosystem is susceptible to such an approach. The types of legitimate attacks which we consider can be classified in three categories. 1. Ciphertext-only Attack. 2. Known Plaintext Attack. 3. Chosen Plainext Attack. Ciphertext-only Attack. The cryptanalyst intercepts one or more messages all encoded with the same encryption algorithm. Goal: Recover the original plaintext or plaintexts, to discover the deciphering key or find an algorithm for deciphering subsequent messages enciphered with the same key. Known Plaintext Attack. The cryptanalyst has access to not only the ciphertext, but also the plaintext for one or more of the messages. Goal: Recover the deciphering key or find an algorithm for deciphering subsequent mes- sages (or the remaining plaintext) enciphered which use the same key. -

The Mathemathics of Secrets.Pdf
THE MATHEMATICS OF SECRETS THE MATHEMATICS OF SECRETS CRYPTOGRAPHY FROM CAESAR CIPHERS TO DIGITAL ENCRYPTION JOSHUA HOLDEN PRINCETON UNIVERSITY PRESS PRINCETON AND OXFORD Copyright c 2017 by Princeton University Press Published by Princeton University Press, 41 William Street, Princeton, New Jersey 08540 In the United Kingdom: Princeton University Press, 6 Oxford Street, Woodstock, Oxfordshire OX20 1TR press.princeton.edu Jacket image courtesy of Shutterstock; design by Lorraine Betz Doneker All Rights Reserved Library of Congress Cataloging-in-Publication Data Names: Holden, Joshua, 1970– author. Title: The mathematics of secrets : cryptography from Caesar ciphers to digital encryption / Joshua Holden. Description: Princeton : Princeton University Press, [2017] | Includes bibliographical references and index. Identifiers: LCCN 2016014840 | ISBN 9780691141756 (hardcover : alk. paper) Subjects: LCSH: Cryptography—Mathematics. | Ciphers. | Computer security. Classification: LCC Z103 .H664 2017 | DDC 005.8/2—dc23 LC record available at https://lccn.loc.gov/2016014840 British Library Cataloging-in-Publication Data is available This book has been composed in Linux Libertine Printed on acid-free paper. ∞ Printed in the United States of America 13579108642 To Lana and Richard for their love and support CONTENTS Preface xi Acknowledgments xiii Introduction to Ciphers and Substitution 1 1.1 Alice and Bob and Carl and Julius: Terminology and Caesar Cipher 1 1.2 The Key to the Matter: Generalizing the Caesar Cipher 4 1.3 Multiplicative Ciphers 6