Intro to the Command Line J Fass | 19 June 2017 the Unix Philosophy
Total Page:16
File Type:pdf, Size:1020Kb
Load more
Recommended publications
-

Shell Scripting with Bash
Introduction to Shell Scripting with Bash Charles Jahnke Research Computing Services Information Services & Technology Topics for Today ● Introductions ● Basic Terminology ● How to get help ● Command-line vs. Scripting ● Variables ● Handling Arguments ● Standard I/O, Pipes, and Redirection ● Control Structures (loops and If statements) ● SCC Job Submission Example Research Computing Services Research Computing Services (RCS) A group within Information Services & Technology at Boston University provides computing, storage, and visualization resources and services to support research that has specialized or highly intensive computation, storage, bandwidth, or graphics requirements. Three Primary Services: ● Research Computation ● Research Visualization ● Research Consulting and Training Breadth of Research on the Shared Computing Cluster (SCC) Me ● Research Facilitator and Administrator ● Background in biomedical engineering, bioinformatics, and IT systems ● Offices on both CRC and BUMC ○ Most of our staff on the Charles River Campus, some dedicated to BUMC ● Contact: [email protected] You ● Who has experience programming? ● Using Linux? ● Using the Shared Computing Cluster (SCC)? Basic Terminology The Command-line The line on which commands are typed and passed to the shell. Username Hostname Current Directory [username@scc1 ~]$ Prompt Command Line (input) The Shell ● The interface between the user and the operating system ● Program that interprets and executes input ● Provides: ○ Built-in commands ○ Programming control structures ○ Environment -

State Notation Language and Sequencer Users' Guide
State Notation Language and Sequencer Users’ Guide Release 2.0.99 William Lupton ([email protected]) Benjamin Franksen ([email protected]) June 16, 2010 CONTENTS 1 Introduction 3 1.1 About.................................................3 1.2 Acknowledgements.........................................3 1.3 Copyright...............................................3 1.4 Note on Versions...........................................4 1.5 Notes on Release 2.1.........................................4 1.6 Notes on Releases 2.0.0 to 2.0.12..................................7 1.7 Notes on Release 2.0.........................................9 1.8 Notes on Release 1.9......................................... 12 2 Installation 13 2.1 Prerequisites............................................. 13 2.2 Download............................................... 13 2.3 Unpack................................................ 14 2.4 Configure and Build......................................... 14 2.5 Building the Manual......................................... 14 2.6 Test.................................................. 15 2.7 Use.................................................. 16 2.8 Report Bugs............................................. 16 2.9 Contribute.............................................. 16 3 Tutorial 19 3.1 The State Transition Diagram.................................... 19 3.2 Elements of the State Notation Language.............................. 19 3.3 A Complete State Program...................................... 20 3.4 Adding a -

A Rapid, Sensitive, Scalable Method for Precision Run-On Sequencing
bioRxiv preprint doi: https://doi.org/10.1101/2020.05.18.102277; this version posted May 19, 2020. The copyright holder for this preprint (which was not certified by peer review) is the author/funder, who has granted bioRxiv a license to display the preprint in perpetuity. It is made available under aCC-BY 4.0 International license. 1 A rapid, sensitive, scalable method for 2 Precision Run-On sequencing (PRO-seq) 3 4 Julius Judd1*, Luke A. Wojenski2*, Lauren M. Wainman2*, Nathaniel D. Tippens1, Edward J. 5 Rice3, Alexis Dziubek1,2, Geno J. Villafano2, Erin M. Wissink1, Philip Versluis1, Lina Bagepalli1, 6 Sagar R. Shah1, Dig B. Mahat1#a, Jacob M. Tome1#b, Charles G. Danko3,4, John T. Lis1†, 7 Leighton J. Core2† 8 9 *Equal contribution 10 1Department of Molecular Biology and Genetics, Cornell University, Ithaca, NY 14853, USA 11 2Department of Molecular and Cell Biology, Institute of Systems Genomics, University of 12 Connecticut, Storrs, CT 06269, USA 13 3Baker Institute for Animal Health, College of Veterinary Medicine, Cornell University, Ithaca, 14 NY 14853, USA 15 4Department of Biomedical Sciences, College of Veterinary Medicine, Cornell University, 16 Ithaca, NY 14853, USA 17 #aPresent address: Koch Institute for Integrative Cancer Research, Massachusetts Institute of 18 Technology, Cambridge, MA 02139, USA 19 #bPresent address: Department of Genome Sciences, University of Washington, Seattle, WA, 20 USA 21 †Correspondence to: [email protected] or [email protected] 22 1 bioRxiv preprint doi: https://doi.org/10.1101/2020.05.18.102277; this version posted May 19, 2020. The copyright holder for this preprint (which was not certified by peer review) is the author/funder, who has granted bioRxiv a license to display the preprint in perpetuity. -
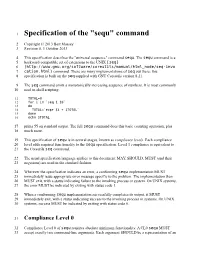
Specification of the "Sequ" Command
1 Specification of the "sequ" command 2 Copyright © 2013 Bart Massey 3 Revision 0, 1 October 2013 4 This specification describes the "universal sequence" command sequ. The sequ command is a 5 backward-compatible set of extensions to the UNIX [seq] 6 (http://www.gnu.org/software/coreutils/manual/html_node/seq-invo 7 cation.html) command. There are many implementations of seq out there: this 8 specification is built on the seq supplied with GNU Coreutils version 8.21. 9 The seq command emits a monotonically increasing sequence of numbers. It is most commonly 10 used in shell scripting: 11 TOTAL=0 12 for i in `seq 1 10` 13 do 14 TOTAL=`expr $i + $TOTAL` 15 done 16 echo $TOTAL 17 prints 55 on standard output. The full sequ command does this basic counting operation, plus 18 much more. 19 This specification of sequ is in several stages, known as compliance levels. Each compliance 20 level adds required functionality to the sequ specification. Level 1 compliance is equivalent to 21 the Coreutils seq command. 22 The usual specification language applies to this document: MAY, SHOULD, MUST (and their 23 negations) are used in the standard fashion. 24 Wherever the specification indicates an error, a conforming sequ implementation MUST 25 immediately issue appropriate error message specific to the problem. The implementation then 26 MUST exit, with a status indicating failure to the invoking process or system. On UNIX systems, 27 the error MUST be indicated by exiting with status code 1. 28 When a conforming sequ implementation successfully completes its output, it MUST 29 immediately exit, with a status indicating success to the invoking process or systems. -

The Linux Command Line
The Linux Command Line Fifth Internet Edition William Shotts A LinuxCommand.org Book Copyright ©2008-2019, William E. Shotts, Jr. This work is licensed under the Creative Commons Attribution-Noncommercial-No De- rivative Works 3.0 United States License. To view a copy of this license, visit the link above or send a letter to Creative Commons, PO Box 1866, Mountain View, CA 94042. A version of this book is also available in printed form, published by No Starch Press. Copies may be purchased wherever fine books are sold. No Starch Press also offers elec- tronic formats for popular e-readers. They can be reached at: https://www.nostarch.com. Linux® is the registered trademark of Linus Torvalds. All other trademarks belong to their respective owners. This book is part of the LinuxCommand.org project, a site for Linux education and advo- cacy devoted to helping users of legacy operating systems migrate into the future. You may contact the LinuxCommand.org project at http://linuxcommand.org. Release History Version Date Description 19.01A January 28, 2019 Fifth Internet Edition (Corrected TOC) 19.01 January 17, 2019 Fifth Internet Edition. 17.10 October 19, 2017 Fourth Internet Edition. 16.07 July 28, 2016 Third Internet Edition. 13.07 July 6, 2013 Second Internet Edition. 09.12 December 14, 2009 First Internet Edition. Table of Contents Introduction....................................................................................................xvi Why Use the Command Line?......................................................................................xvi -
Shell Variables
Shell Using the command line Orna Agmon ladypine at vipe.technion.ac.il Haifux Shell – p. 1/55 TOC Various shells Customizing the shell getting help and information Combining simple and useful commands output redirection lists of commands job control environment variables Remote shell textual editors textual clients references Shell – p. 2/55 What is the shell? The shell is the wrapper around the system: a communication means between the user and the system The shell is the manner in which the user can interact with the system through the terminal. The shell is also a script interpreter. The simplest script is a bunch of shell commands. Shell scripts are used in order to boot the system. The user can also write and execute shell scripts. Shell – p. 3/55 Shell - which shell? There are several kinds of shells. For example, bash (Bourne Again Shell), csh, tcsh, zsh, ksh (Korn Shell). The most important shell is bash, since it is available on almost every free Unix system. The Linux system scripts use bash. The default shell for the user is set in the /etc/passwd file. Here is a line out of this file for example: dana:x:500:500:Dana,,,:/home/dana:/bin/bash This line means that user dana uses bash (located on the system at /bin/bash) as her default shell. Shell – p. 4/55 Starting to work in another shell If Dana wishes to temporarily use another shell, she can simply call this shell from the command line: [dana@granada ˜]$ bash dana@granada:˜$ #In bash now dana@granada:˜$ exit [dana@granada ˜]$ bash dana@granada:˜$ #In bash now, going to hit ctrl D dana@granada:˜$ exit [dana@granada ˜]$ #In original shell now Shell – p. -
Pingdirectory Administration Guide Version
Release 7.3.0.3 Server Administration Guide PingDirectory | Contents | ii Contents PingDirectory™ Product Documentation................................................ 20 Overview of the Server............................................................................. 20 Server Features.................................................................................................................................20 Administration Framework.................................................................................................................21 Server Tools Location....................................................................................................................... 22 Preparing Your Environment....................................................................22 Before You Begin.............................................................................................................................. 22 System requirements..............................................................................................................22 Installing Java......................................................................................................................... 23 Preparing the Operating System (Linux).......................................................................................... 24 Configuring the File Descriptor Limits.................................................................................... 24 File System Tuning.................................................................................................................25 -

Sleep 2.1 Manual
Sleep 2.1 Manual "If you put a million monkeys at a million keyboards, one of them will eventually write a Java program. The rest of them will write Perl programs." -- Anonymous Raphael Mudge Sleep 2.1 Manual Revision: 06.02.08 Released under a Creative Commons Attribution-ShareAlike 3.0 License (see http://creativecommons.org/licenses/by-sa/3.0/us/) You are free: • to Share -- to copy, distribute, display, and perform the work • to Remix -- to make derivative works Under the following conditions: Attribution. You must attribute this work to Raphael Mudge with a link to http://sleep.dashnine.org/ Share Alike. If you alter, transform, or build upon this work, you may distribute the resulting work only under the same, similar or a compatible license. • For any reuse or distribution, you must make clear to others the license terms of this work. The best way to do this is with a link to the license. • Any of the above conditions can be waived if you get permission from the copyright holder. • Apart from the remix rights granted under this license, nothing in this license impairs or restricts the author's moral rights. Your fair use and other rights are in no way affected by the above. Table of Contents Introduction................................................................................................. 1 I. What is Sleep?...................................................................................................1 II. Manual Conventions......................................................................................2 III. -

Research Computing and Cyberinfrastructure Team
Research Computing and CyberInfrastructure team ! Working with the Linux Shell on the CWRU HPC 31 January 2019 7 February 2019 ! Presenter Emily Dragowsky KSL Data Center RCCI Team: Roger Bielefeld, Mike Warfe, Hadrian Djohari! Brian Christian, Emily Dragowsky, Jeremy Fondran, Cal Frye,! Sanjaya Gajurel, Matt Garvey, Theresa Griegger, Cindy Martin, ! Sean Maxwell, Jeno Mozes, Nasir Yilmaz, Lee Zickel Preface: Prepare your environment • User account ! # .bashrc ## cli essentials ! if [ -t 1 ] then bind '"\e[A": history-search-backward' bind '"\e[B": history-search-forward' bind '"\eOA": history-search-backward' bind '"\eOB": history-search-forward' fi ! This is too useful to pass up! Working with Linux • Preamble • Intro Session Linux Review: Finding our way • Files & Directories: Sample work flow • Shell Commands • Pipes & Redirection • Scripting Foundations • Shell & environment variables • Control Structures • Regular expressions & text manipulation • Recap & Look Ahead Rider Cluster Components ! rider.case.edu ondemand.case.edu University Firewall ! Admin Head Nodes SLURM Science Nodes Master DMZ Resource ! Data Manager Transfer Disk Storage Nodes Batch nodes GPU nodes SMP nodes Running a job: where is it? slide from Hadrian Djohari Storing Data on the HPC table from Nasir Yilmaz How data moves across campus • Buildings on campus are each assigned to a zone. Data connections go from every building to the distribution switch at the center of the zone and from there to the data centers at Kelvin Smith Library and Crawford Hall. slide -

Netstat Statistics Comparison with Perl by Noah Davids
Netstat Statistics Comparison with Perl By Noah Davids Comparing sets of numeric output can be tiresome. Using the output from the netstat command helps diagnose problems. Over time, the changes in the statistics reported can be very informative.This article explains how this network specialist and Perl novice decided to write a program to do the comparison for him. INTRODUCTION THE SCRIPT Comparing sets of numeric output can be tedious, especially when The script expects as input a file with the following format: the numbers are large and there are a lot of them. Unfortunately it is Some number of random lines something I have to do fairly often. As a network support specialist, I Line with unique string indicating start of data set 1 often use the output from the netstat command to help diagnose Some fixed number of lines with the format: problems. Changes in the statistics reported over time can be very enlightening. In addition, as part of the support process, I have to LABEL NUMBER LABEL NUMBER LABEL include those differences in my written analysis. Punching the long numbers into a calculator and copying the answer back out is a drag. Some number of random lines Using cut and paste helps only marginally. Line with the same unique string indicating start of data 2 To make my life simpler, I decided to write a program to do the Some fixed number of lines with the format: comparison for me. However, I support four different operating sys- tems, and while each has a netstat command, the format and content LABEL NUMBER LABEL NUMBER LABEL of the output varies with each OS. -

ANSWERS ΤΟ EVEN-Numbered
8 Answers to Even-numbered Exercises 2.1. WhatExplain the following unexpected are result: two ways you can execute a shell script when you do not have execute permission for the file containing the script? Can you execute a shell script if you do not have read permission for the file containing the script? You can give the name of the file containing the script as an argument to the shell (for example, bash scriptfile or tcsh scriptfile, where scriptfile is the name of the file containing the script). Under bash you can give the following command: $ . scriptfile Under both bash and tcsh you can use this command: $ source scriptfile Because the shell must read the commands from the file containing a shell script before it can execute the commands, you must have read permission for the file to execute a shell script. 4.3. AssumeWhat is the purpose ble? you have made the following assignment: $ person=zach Give the output of each of the following commands. a. echo $person zach b. echo '$person' $person c. echo "$person" zach 1 2 6.5. Assumengs. the /home/zach/grants/biblios and /home/zach/biblios directories exist. Specify Zach’s working directory after he executes each sequence of commands. Explain what happens in each case. a. $ pwd /home/zach/grants $ CDPATH=$(pwd) $ cd $ cd biblios After executing the preceding commands, Zach’s working directory is /home/zach/grants/biblios. When CDPATH is set and the working directory is not specified in CDPATH, cd searches the working directory only after it searches the directories specified by CDPATH. -

Transcriptome-Wide M a Detection with DART-Seq
Transcriptome-wide m6A detection with DART-Seq Kate D. Meyer ( [email protected] ) Duke University School of Medicine https://orcid.org/0000-0001-7197-4054 Method Article Keywords: RNA, epitranscriptome, RNA methylation, m6A, methyladenosine, DART-Seq Posted Date: September 23rd, 2019 DOI: https://doi.org/10.21203/rs.2.12189/v1 License: This work is licensed under a Creative Commons Attribution 4.0 International License. Read Full License Page 1/7 Abstract m6A is the most abundant internal mRNA modication and plays diverse roles in gene expression regulation. Much of our current knowledge about m6A has been driven by recent advances in the ability to detect this mark transcriptome-wide. Antibody-based approaches have been the method of choice for global m6A mapping studies. These methods rely on m6A antibodies to immunoprecipitate methylated RNAs, followed by next-generation sequencing to identify m6A-containing transcripts1,2. While these methods enabled the rst identication of m6A sites transcriptome-wide and have dramatically improved our ability to study m6A, they suffer from several limitations. These include requirements for high amounts of input RNA, costly and time-consuming library preparation, high variability across studies, and m6A antibody cross-reactivity with other modications. Here, we describe DART-Seq (deamination adjacent to RNA modication targets), an antibody-free method for global m6A detection. In DART-Seq, the C to U deaminating enzyme, APOBEC1, is fused to the m6A-binding YTH domain. This fusion protein is then introduced to cellular RNA either through overexpression in cells or with in vitro assays, and subsequent deamination of m6A-adjacent cytidines is then detected by RNA sequencing to identify m6A sites.