Businesscom Sentinel PF Operating System Handbook
Total Page:16
File Type:pdf, Size:1020Kb
Load more
Recommended publications
-

MPLS-Based Metro Ethernet Networks a Tutorial • Paresh Khatri • 2018
MPLS-based Metro Ethernet Networks A tutorial • Paresh Khatri • 2018 1 © Nokia 2017 Public Agenda 1. Introduction 2. Introduction to Metro Ethernet Services 3. Traditional Metro Ethernet networks 4. Delivering Ethernet over MPLS 5. Summary 6. Questions 2 © Nokia 2017 Public introduction 3 © Nokia 2017 Public Introduction • Paresh Khatri ([email protected]) - Chief Architect – IP Routing & Transport APAC, Alcatel-Lucent • Key focus areas: - End-to-end network architectures - SDN/NFV - Large-scale IP/MPLS networks - L2/L3 VPNs - Carrier Ethernet - Next-generation mobile backhaul networks • Acknowledgements: - Some figures and text are provided courtesy of the Metro Ethernet Forum (MEF) 4 © Nokia 2017 Public introduction to metro ethernet services 5 © Nokia 2017 Public AGenda 2. Introduction to Metro Ethernet Services a) Why Metro Ethernet ? b) Attributes of Carrier Ethernet c) Carrier Ethernet Services defined by the MEF 6 © Nokia 2017 Public 2.1 Why Metro Ethernet ? 7 © Nokia 2017 Public Introduction to Metro Ethernet Services What is Metro Ethernet ? “… generally defined as the network that bridges or connects geographically separated enterprise LANs while also connecting across the WAN or backbone networks that are generally owned by service providers. The Metro Ethernet Networks provide connectivity services across Metro geography utilising Ethernet as the core protocol and enabling broadband applications” from “Metro Ethernet Networks – A Technical Overview” from the Metro Ethernet Forum 8 © Nokia 2017 Public Introduction to Metro -

Generating Synthetic Voip Traffic for Analyzing Redundant Openbsd
UNIVERSITY OF OSLO Department of Informatics Generating Synthetic VoIP Traffic for Analyzing Redundant OpenBSD-Firewalls Master Thesis Maurice David Woernhard May 23, 2006 Generating Synthetic VoIP Traffic for Analyzing Redundant OpenBSD-Firewalls Maurice David Woernhard May 23, 2006 Abstract Voice over IP, short VoIP, is among the fastest growing broadband technologies in the private and commercial sector. Compared to the Plain Old Telephone System (POTS), Internet telephony has reduced availability, measured in uptime guarantees per a given time period. This thesis makes a contribution towards proper quantitative statements about network availability when using two redun- dant, state synchronized computers, acting as firewalls between the Internet (WAN) and the local area network (LAN). First, methods for generating adequate VoIP traffic volumes for loading a Gigabit Ethernet link are examined, with the goal of using a minimal set of hardware, namely one regular desktop computer. pktgen, the Linux kernel UDP packet generator, was chosen for generating synthetic/artificial traffic, reflecting the common VoIP packet characteristics packet size, changing sender and receiver address, as well as typical UDP-port usage. pktgen’s three main parameters influencing the generation rate are fixed inter-packet delay, packet size and total packet count. It was sought to relate these to more user-friendly val- ues of amount of simultaneous calls, voice codec employed and call duration. The proposed method fails to model VoIP traffic accurately, mostly due to the cur- rently unstable nature of pktgen. However, it is suited for generating enough packets for testing the firewalls. Second, the traffic forwarding limit and failover behavior of the redun- dant, state-synchronized firewalls was examined. -
Navigating Network Migration Challenges: Upgrade Your 1GE
Navigating Network Migration Challenges: Upgrade Your 1GE Metro Ethernet Access Network to 10GE A White Paper from Telco Systems Upgrade Your 1GE Metro Ethernet Access Network to 10GE | 2 Intoduction Many businesses and service providers are migrating from • Service providers are finding it more difficult to live up to 1GE to 10GE networks as they attempt to avoid the obstacles their customers’ service level agreements (SLA) to presented by heavy bandwidth, while leveraging the benefits provide multiple services, which require more bandwidth that 10GE networking has to offer. The requirement for • Generating more revenue within the current limits of a more bandwidth has become a constant battle. As internet 1Gig network usage continues to increase with the popularity of data and streaming services, so does the demand for more bandwidth. As the gap between service revenues and the demand for From education (homework, e-learning, campus networks), higher bandwidth grows, providers are looking for ways to finance (online banking, stock trading, bill pay), and business better control their expenses while offering higher bandwidth purposes (company intranets, remote workers), to social media and more services to more customers. With the increasing (Facebook, Instagram, Twitter, Snapchat), political (campaigns demand for more bandwidth with OTT (over-the-top) and outreach) and personal purposes, data requirements applications like video streaming, Hulu, Netflix, and Amazon continue to rise – quicker than service providers can react. Prime becoming more popular, 1GE networks aren’t going to cut it anymore. In support of these activities, service providers are being driven to enhance their network capacities in their business Ethernet, To conquer these challenges, enterprises and service mobile backhaul, E-Rate, cloud networking, and SDN & NFV providers are migrating their 1GE networks to 10GE. -

Chapter 6: General Design Considerations
ch01i.book Page 194 Friday, March 26, 2004 10:08 AM This chapter covers the following topics: • Physical Security Issues • Layer 2 Security Considerations • IP Addressing Design Considerations • ICMP Design Considerations • Routing Considerations • Transport Protocol Design Considerations • DoS Design Considerations ch01i.book Page 195 Friday, March 26, 2004 10:08 AM C H A P T E R 6 General Design Considerations Many things difficult to design prove easy to performance. —Samuel Johnson, Rasselas: The History of Rasselas, Prince of Abissinia, 1759 A good scientist is a person with original ideas. A good engineer is a person who makes a design that works with as few original ideas as possible. There are no prima donnas in engineering. —Freeman Dyson, Physicist, Disturbing the Universe, 1979 At the beginning of any secure network design project, many best practices apply more or less uniformly to all areas of the design. This chapter presents these practices in a single location and then draws on them throughout the rest of the book. The designs presented in Chapter 13, “Edge Security Design,” Chapter 14, “Campus Security Design,” and Chapter 15, “Teleworker Security Design,” are based on many of the concepts described here and in the companion chapters (Chapters 7–11), which detail specific design considerations for certain technologies. The topics are presented in loose compliance with the seven-layer OSI model and, as such, cover a diverse set of topics. Chapter 1, “Network Security Axioms,” presented the security axioms; this chapter translates them into actionable guidance for secure network design. Physical Security Issues One common security truism is “Once you have physical access to a box, all bets are off.” This is a good beginning assumption for this section. -

Enterprise Ipv6 Deployment
Enterprise IPv6 Deployment Tim Martin CCIE #2020 BRKRST-2301 @bckcntryskr Agenda • General Design • Host Configuration • Access Layer • Routing Protocols • Data Center • WAN Deployment • Internet Edge • Conclusion Enterprise IPv6 Guidance • RFC 7381 enterprise IPv6 guidelines • Updated white paper – Cisco.com • No major change to 2/3 tier architecture Access Distribution Si Core Distribution Access WAN Data Center Internet BRKRST-2301 © 2017 Cisco and/or its affiliates. All rights reserved. Cisco Public 4 Global Address Assignment • Provider Allocated (PA) PA PI • From your ISP, single homed 2000::/3 2000::/3 • /48 - /60 IANA • Provider Independent (PI) Registries • Multi home, Multi provider /12 /12 RIR • /32 - /48 /32 • Local Internet Registry (LIR) ISP Org /32 /48 • Regional registry member • Acquire & manage space Level Four /48 • /29 - /32 Entity Subordinate /48 BRKRST-2301 © 2017 Cisco and/or its affiliates. All rights reserved. Cisco Public 5 Multinational Model • PA or PI from each region you operate in • Coordination of advertised space within each RIR • Most run PI from primary region as an LIR 2a00:0000::/12 2600:0000::/12 2400:0000::/12 2c00:0000::/12 2800:0000::/12 BRKRST-2301 © 2017 Cisco and/or its affiliates. All rights reserved. Cisco Public 6 Prefix Length Considerations • Anywhere a host exists /64 Hosts /64 • RFC 7421, rational for /64 Core /64 or /127 • Point to Point /127 • RFC 6164, cache exhaustion Pt 2 Pt • Reserve a /64, configure a /127 /127 Servers • Loopback or Anycast /128 /64 Loopback /128 Hosts /64 BRKRST-2301 -

T-Metro 200 Carrier Ethernet Multi-Service Ces Aggregation
T-Metro 200 carrier ethernet multi-service ces aggregation The T-Metro 200 is a feature-rich multiservice access device designed to increase service provider revenues and deliver a complete portfolio of voice, data and video services. The T-Metro family of products supports a wide variety of technologies including Ethernet, circuit emulation services (CES), MPLS, OAM (operations, administration and maintenance) tools and hierarchical quality of service (HQoS). This rich combination of technologies PRODUCT HIGHLIGHTS allows service providers to deliver an enhanced service offering while Enhanced Ethernet services, maintaining competitive pricing. features and capabilities The T-Metro 200 provides access to advanced data services such as virtual – 802.1ad provider bridges for Ethernet private LAN services (VPLS), virtual private wire services (VPWS) and IP virtual based L2VPN services private network (IP-VPN) services. In addition, the T-Metro product line enables – Super VLAN for traffic isolation service providers to carry native TDM traffic transparently across packet – Fast-Ring with sub 50ms recovery switched networks (PSN), using various circuit emulation techniques. The TDM traffic is encapsulated in Ethernet or IP frames to emulate the functionality of a – IEEE 802.3ad link aggregation TDM circuit, ensuring that all original feature-sets are preserved. Circuit Emulation Services deliver traditional voice or leased line Designed for Metro Ethernet Services services Convergence of voice, data and video services over a single Ethernet-based – Structured agnostic traffic over infrastructure is transforming the way enterprises and service providers packet (SAToP) conduct their businesses. The T-Metro 200’s versatility, advanced feature-set, – CES over packet switched networks wire speed performance and robust design makes it an ideal convergence (CESoPSN) platform for metro applications, either in a bridged metro Ethernet or MPLS – T1/E1; DS3/T3, OC-3/STM-1 environment. -

ISP Column an Occasional Column on Things Internet
The ISP Column An occasional column on things Internet Hunting the Bogon May 2004 There were a number of "adventure" games in the late 1970's and early 80's. By today's standards the original versions of these computer games were not just primitive, they make banging the rooks together look sophisticated. But at the time they were a pointer to the use of computers as something more than just numerical calculators, or business machines. Programs could be imaginative and even fun (well ok, 'fun' was different then!). One of the more widespread early versions of this kind of game was "Hunt the Wumpus'. The web being what it is these days you can meander back to 1976 at http://www.atariarchives.org/bcc1/showpage.php?page=247 For those who want a first-hand experience of 1970's computer games, check out: http://www.taylor.org/~patrick/wumpus/ As far as I can tell the only difference is that the original games proceeded at a pace that could only be described as glacial! What's a "Bogon"? Good question. The word bogon probably has lots of meanings in various contexts, but in the context of the Internet address realm a bogon refers to the use of an address or, more generally a route object, that is not duly authorized by the entity to which the address, or resource, was originally assigned. I must admit that I've yet to hear of any other word that succinctly takes that rather long- winded phrase and sums it up with one word! There are two kinds of bogon objects in the inter-domain space - the first is the advertisement of IP addresses, and the second is the use of Autonomous System numbers within the AS Path attribute. -

ARIN 2005 Annual Report
Public Participation Leading to Positive Results Applying the principles of stewardship, ARIN, a nonprofit corporation, allocates Internet Protocol resources; develops consensus-based policies; and facilitates the advancement of the Internet through information ission Statement and educational outreach. M The American Registry for Internet Numbers (ARIN) publishes annual reports to document for its community Contents the operations and activities of the organization. The ARIN at a Glance . 4 audited financial statements for fiscal year 2005 will be published separately in mid-2006. Year in Review . 6 To view this report online or to review the annual reports and financial statements from previous years, please visit Reports & Updates . 9 the ARIN website at: Global Community Activities . 17 www.arin.net/about_us/corp_docs/annual_rprt.html Internet Number © ARIN Resource Policy . 19 All Rights Reserved. “ARIN” and the ARIN logo are registered trademarks 2005 Statistics . 23 Reg. U.S. Pat. & Tm. Off. oward the end of 2005, ARIN marked its eighth year of operation and service to the Internet community. Throughout its existence, there have been many changes both within the ARIN region and throughout the Internet as a whole, while at the same time ARIN’s mission has remained the same. Our Tcommitments to stewardship of Internet number resources and providing registration, organizational, and policy facilitation services have never been stronger. One of the most recent major changes took place in April 2005, when ICANN officially recognized AfriNIC as the fifth Regional Internet Registry. Encompassing the entire continent of Africa, AfriNIC now covers a region previously served by APNIC, ARIN, and the RIPE NCC. -

Securing Networks with Mikrotik Router OS
Securing Networks with Mikrotik Router OS Speaker: Tom Smyth, CTO Wireless Connect Ltd. Location: New Orleans Date: 28-09-2012 1 ©2006-2012 WirelessConnect.eu Wireless Connect Ltd. ✔Irish Company Incorporated in 2006 ✔Operate an ISP in the centre of Ireland. ✔Good Infrastructure Expertise. ✔ Certified MikroTik Partners ✔Training ✔Certified OEM Integrators ✔Consultants ✔Value Added Reseller 2 ©2006-2012 WirelessConnect.eu Speaker Profile: ✔Studied BEng. Mechanical & Electronic Engineering, DCU,Ireland ✔Has been working in Industry since 2000 ✔Server Infrastructure Engineer ✔Systems / Network Administrator ✔Internet Security Consultant ✔1st MikroTik Certified Trainer in June 2007 in Ireland 3 ©2006-2012 WirelessConnect.eu Security Information sources ✔ENISA –http://www.enisa.europa.eu/ ✔OWASP http://owasp.org ✔Rits Group – http://www.ritsgroup.com/ ✔ISAS – http://www.isas.ie/ ✔SANS Institute – http://sans.org ✔CIS Centre for Internet Security – http://cisecurity.org/ ✔NIST Computer Security http://csrc.nist.gov/ ✔Open BSD – http://OpenBSD.org/ ✔Spamhaus.org – http://spamhaus.org ✔nmap.org – http://nmap.org ✔ha.ckers.org – http://ha.ckers.org/ 4 ©2006-2012 WirelessConnect.eu Router OS ✔Highly Versatile ✔Highly Customisable ✔Highly Cost Effective ✔Allows one to manage Security Threats in many Ways 5 ©2006-2012 WirelessConnect.eu What Can MikroTik Router OS Do ? ✔It is a Stateful Firewall ✔It is a Web Proxy ✔It is a Socks Proxy ✔It is a DNS Cache / Proxy ✔It is a Router ✔It is an IPSEC Concentrator ✔It is an IDS – Intrusion Detection System -
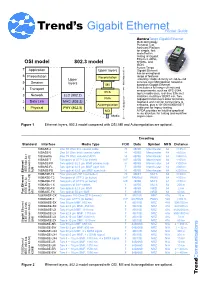
Gigabit Ethernet Pocket Guide
GbE.PocketG.fm Page 1 Friday, March 3, 2006 9:43 AM Carrier Class Ethernet, Metro Ethernet tester, Metro Ethernet testing, Metro Ethernet installation, Metro Ethernet maintenance, Metro Ethernet commissioning, Carrier Class Ethernet tester, Carrier Class Ethernet testing, Carrier Class Ethernet installation, Carrier Class Ethernet maintenance, Gigabit Ethernet tester, Gigabit Ethernet testing, Gigabit Ethernet installation, Gigabit Ethernet maintenance, Gigabit Ethernet commissioning, Gigabit Ethernet protocols, 1000BASE-T tester, 1000BASE-LX test, 1000BASE-SX test, 1000BASE-T testing, 1000BASE-LX testing Trend’s Gigabit EthernetPocket Guide AuroraTango Gigabit Ethernet Multi-technology Personal Test Assistant Platform for simple, fast and effective testing of Gigabit Ethernet, ADSL, OSI model 802.3 model SHDSL, and ISDN. Aurora Tango 7 Application Upper layers Gigabit Ethernet has an exceptional 6 Presentation Reconciliation range of features Upper ensuring reliable delivery of end-to-end 5 Session layers services over Metropolitan networks MII Media independent based on Gigabit Ethernet. 4 It includes a full range of tests and Transport measurements, such as RFC-2544, PCS top ten addresses, real-time Ethernet 3 Network LLC (802.2) statistics, multilayer BERT, etc. Two PMA Gigaport transceivers allow terminate, 2 Data Link MAC (803.3) loopback and monitor connections to Autonegotiation networks, plus a 10/100/1000BASE-T Physical cable port for legacy testing. 1 PHY (802.3) dependent Media MDI A PDA provides an intuitive graphical menu -

Carrier Ethernet Configuration Guide, Cisco IOS Release 12.2SR
Carrier Ethernet Configuration Guide, Cisco IOS Release 12.2SR Americas Headquarters Cisco Systems, Inc. 170 West Tasman Drive San Jose, CA 95134-1706 USA http://www.cisco.com Tel: 408 526-4000 800 553-NETS (6387) Fax: 408 527-0883 THE SPECIFICATIONS AND INFORMATION REGARDING THE PRODUCTS IN THIS MANUAL ARE SUBJECT TO CHANGE WITHOUT NOTICE. ALL STATEMENTS, INFORMATION, AND RECOMMENDATIONS IN THIS MANUAL ARE BELIEVED TO BE ACCURATE BUT ARE PRESENTED WITHOUT WARRANTY OF ANY KIND, EXPRESS OR IMPLIED. USERS MUST TAKE FULL RESPONSIBILITY FOR THEIR APPLICATION OF ANY PRODUCTS. THE SOFTWARE LICENSE AND LIMITED WARRANTY FOR THE ACCOMPANYING PRODUCT ARE SET FORTH IN THE INFORMATION PACKET THAT SHIPPED WITH THE PRODUCT AND ARE INCORPORATED HEREIN BY THIS REFERENCE. IF YOU ARE UNABLE TO LOCATE THE SOFTWARE LICENSE OR LIMITED WARRANTY, CONTACT YOUR CISCO REPRESENTATIVE FOR A COPY. The Cisco implementation of TCP header compression is an adaptation of a program developed by the University of California, Berkeley (UCB) as part of UCB’s public domain version of the UNIX operating system. All rights reserved. Copyright © 1981, Regents of the University of California. NOTWITHSTANDING ANY OTHER WARRANTY HEREIN, ALL DOCUMENT FILES AND SOFTWARE OF THESE SUPPLIERS ARE PROVIDED “AS IS” WITH ALL FAULTS. CISCO AND THE ABOVE-NAMED SUPPLIERS DISCLAIM ALL WARRANTIES, EXPRESSED OR IMPLIED, INCLUDING, WITHOUT LIMITATION, THOSE OF MERCHANTABILITY, FITNESS FOR A PARTICULAR PURPOSE AND NONINFRINGEMENT OR ARISING FROM A COURSE OF DEALING, USAGE, OR TRADE PRACTICE. IN NO EVENT SHALL CISCO OR ITS SUPPLIERS BE LIABLE FOR ANY INDIRECT, SPECIAL, CONSEQUENTIAL, OR INCIDENTAL DAMAGES, INCLUDING, WITHOUT LIMITATION, LOST PROFITS OR LOSS OR DAMAGE TO DATA ARISING OUT OF THE USE OR INABILITY TO USE THIS MANUAL, EVEN IF CISCO OR ITS SUPPLIERS HAVE BEEN ADVISED OF THE POSSIBILITY OF SUCH DAMAGES. -
Carrier Ethernet Tutorial
Carrier . Ethernet Raj Jain Washington University in Saint Louis Saint Louis, MO 63130 [email protected] These slides and audio/video recordings of this class lecture are at: http://www.cse.wustl.edu/~jain/cse570-19/ Washington University in St. Louis http://www.cse.wustl.edu/~jain/cse570-19/ ©2019 Raj Jain 6-1 Overview 1. Enterprise vs Carrier Ethernet 2. UNI vs Peer-to-Peer Signaling 3. Metro Ethernet 4. Ethernet Provider Bridge (PB) 5. Provider Backbone Network (PBB) 6. Connection Oriented Ethernet Note: Although these technologies were originally developed for carriers, they are now used inside multi-tenant data centers Washington(clouds) University in St. Louis http://www.cse.wustl.edu/~jain/cse570-19/ ©2019 Raj Jain 6-2 Enterprise vs. Carrier Ethernet Enterprise Carrier Distance: up to 2km Up to 100 km Scale: Few K MAC addresses Millions of MAC Addresses 4096 VLANs Millions of VLANs Q-in-Q Protection: Spanning tree Shortest Path Routing Path determined by spanning Traffic engineered path tree Simple service SLA Priority ⇒ Aggregate QoS Need per-flow QoS No performance/Error Need performance/BER monitoring (OAM) Washington University in St. Louis http://www.cse.wustl.edu/~jain/cse570-19/ ©2019 Raj Jain 6-3 Carriers vs. Enterprise We need to exchange topology for Sorry, We can’t tell you optimal routing. anything about our internal network. Washington University in St. Louis http://www.cse.wustl.edu/~jain/cse570-19/ ©2019 Raj Jain 6-4 Network Hierarchy Provider Provider Backbone Provider Customer Bridge Network Bridge Network Bridge Network Customer Network (PBN) (PBBN) (PBN) Network Backbone Provider Provider Core Core Core Bridge Bridge Bridge Customer Provider Provider Customer Edge Edge Backbone Edge Edge Bridge Bridge Provider Backbone Edge Provider Bridge Bridge Edge Edge Bridge Edge Bridge Bridge Bridge Washington University in St.