Cisco Nexus 9000V Guide First Published: 2016-10-31 Last Modified: 2018-02-12
Total Page:16
File Type:pdf, Size:1020Kb
Load more
Recommended publications
-
The Next Generation Cloud: the Rise of the Unikernel
The Next Generation Cloud: The Rise of the Unikernel A Xen Project publication April 2015 xenproject.org Docker and Linux container technologies dominate headlines today as a powerful, easy way to package applications, especially as cloud computing becomes more mainstream. While still a work-in-progress, they offer a simple, clean and lean way to distribute application workloads. With enthusiasm continuing to grow for container innovations, a related technology called unikernels is also beginning to attract attention. Known also for their ability to cleanly separate functionality at the component level, unikernels are developing a variety of new approaches to deploy cloud services. Traditional operating systems run multiple applications on a single machine, managing resources and isolating applications from one another. A unikernel runs a single application on a single virtual machine, relying instead on the hypervisor to isolate those virtual machines. Unikernels are constructed by using “library operating systems,” from which the developer selects only the minimal set of services required for an application to run. These sealed, fixed-purpose images run directly on a hypervisor without an intervening guest OS such as Linux. As well as improving upon container technologies, unikernels are also able to deliver impressive flexibility, speed and versatility for cross-platform environments, big data analytics and scale-out cloud computing. Like container-based solutions, this technology fulfills the promise of easy deployment, but unikernels also offer an extremely tiny, specialized runtime footprint that is much less vulnerable to attack. There are several up-and-coming open source projects to watch this year, including ClickOS, Clive, HaLVM, LING, MirageOS, Rump Kernels and OSv among others, with each of them placing emphasis on a different aspect of the unikernel approach. -

A Linux in Unikernel Clothing Lupine
A Linux in Unikernel Clothing Hsuan-Chi Kuo+, Dan Williams*, Ricardo Koller* and Sibin Mohan+ +University of Illinois at Urbana-Champaign *IBM Research Lupine Unikernels are great BUT: Unikernels lack full Linux Support App ● Hermitux: supports only 97 system calls Kernel LibOS + App ● OSv: ○ Fork() , execve() are not supported Hypervisor Hypervisor ○ Special files are not supported such as /proc ○ Signal mechanism is not complete ● Small kernel size ● Rumprun: only 37 curated applications ● Heavy ● Fast boot time ● Community is too small to keep it rolling ● Inefficient ● Improved performance ● Better security 2 Can Linux behave like a unikernel? 3 Lupine Linux 4 Lupine Linux ● Kernel mode Linux (KML) ○ Enables normal user process to run in kernel mode ○ Processes can still use system services such as paging and scheduling ○ App calls kernel routines directly without privilege transition costs ● Minimal patch to libc ○ Replace syscall instruction to call ○ The address of the called function is exported by the patched KML kernel using the vsyscall ○ No application changes/recompilation required 5 Boot time Evaluation Metrics Image size Based on: Unikernel benefits Memory footprint Application performance Syscall overhead 6 Configuration diversity ● 20 top apps on Docker hub (83% of all downloads) ● Only 19 configuration options required to run all 20 applications: lupine-general 7 Evaluation - Comparison configurations Lupine Cloud Operating Systems [Lupine-base + app-specific options] OSv general Linux-based Unikernels Kernel for 20 apps -

Governance in Collaborative Open Source Software Development Organizations: a Comparative Analysis of Two Case Studies
Governance in Collaborative Open Source Software Development Organizations: A Comparative Analysis of two Case Studies Master’s thesis Faculty of Business, Economics and Social Sciences University of Bern submitted to Dr. Matthias Stürmer Research Center for Digital Sustainability Institute of Information Systems by Winkelmann, Rahel from Siselen 11th semester Matriculation nr.: 09-127-788 Study address: Huberstrasse 22 3008 Bern (Tel. 078 758 58 96) (e-Mail: [email protected]) Bern, 20.01.2015 Abstract While loose cooperation among several actors is common in the open source sector, companies merging into a professionally governed collaborative open source software development organization across industries is an emerging phenomenon. The purpose of this thesis is to shed light on this new approach of software development by creating a framework for building a collaborative open source software development organization. A comparative analysis examines the governance models of two different collaborative open source software development organizations from the organizational, financial and legal perspective and reveals the autonomous and the affiliated organization type and their key characteristics. Based on these findings and by means of four expert interviews a framework consisting of eight criteria that need to be considered in order to build a collaborative open source software development organization is created. Zusammenfassung In der Open Source Branche ist es gängig, dass sich verschiedene Akteure zur Softwareentwicklung zu losen Konsortien zusammenschliessen. Unternehmen, welche sich im professionellen Rahmen zu einer Organisation zusammenschliessen um gemeinsam Open Source Software zu entwickeln, sind jedoch ein neues Phänomen. Der Zweck dieser Arbeit ist es Aufschluss über diesen neuen Ansatz von Softwareentwicklung zu geben. -

Erlang on Physical Machine
on $ whoami Name: Zvi Avraham E-mail: [email protected] /ˈkɒm. pɑː(ɹ)t. mɛntl̩. aɪˌzeɪ. ʃən/ Physicalization • The opposite of Virtualization • dedicated machines • no virtualization overhead • no noisy neighbors – nobody stealing your CPU cycles, IOPS or bandwidth – your EC2 instance may have a Netflix “roommate” ;) • Mostly used by ARM-based public clouds • also called Bare Metal or HPC clouds Sandbox – a virtual container in which untrusted code can be safely run Sandbox examples: ZeroVM & AWS Lambda based on Google Native Client: A Sandbox for Portable, Untrusted x86 Native Code Compartmentalization in terms of Virtualization Physicalization No Virtualization Virtualization HW-level Virtualization Containerization OS-level Virtualization Sandboxing Userspace-level Virtualization* Cloud runs on virtual HW HARDWARE Does the OS on your Cloud instance still supports floppy drive? $ ls /dev on Ubuntu 14.04 AWS EC2 instance • 64 teletype devices? • Sound? • 32 serial ports? • VGA? “It’s DUPLICATED on so many LAYERS” Application + Configuration process* OS Middleware (Spring/OTP) Container Managed Runtime (JVM/BEAM) VM Guest Container OS Container Guest OS Hypervisor Hardware We run Single App per VM APPS We run in Single User mode USERS Minimalistic Linux OSes • Embedded Linux versions • DamnSmall Linux • Linux with BusyBox Min. Linux OSes for Containers JeOS – “Just Enough OS” • CoreOS • RancherOS • RedHat Project Atomic • VMware Photon • Intel Clear Linux • Hyper # of Processes and Threads per OS OSv + CLI RancherOS processes CoreOS threads -

Symantec Web Security Service Policy Guide
Web Security Service Policy Guide Version 6.10.4.1/OCT.12.2018 Symantec Web Security Service/Page 2 Policy Guide/Page 3 Copyrights Copyright © 2018 Symantec Corp. All rights reserved. Symantec, the Symantec Logo, the Checkmark Logo, Blue Coat, and the Blue Coat logo are trademarks or registered trademarks of Symantec Corp. or its affiliates in the U.S. and other coun- tries. Other names may be trademarks of their respective owners. This document is provided for informational purposes only and is not intended as advertising. All warranties relating to the information in this document, either express or implied, are disclaimed to the maximum extent allowed by law. The information in this document is subject to change without notice. THE DOCUMENTATION IS PROVIDED "AS IS" AND ALL EXPRESS OR IMPLIED CONDITIONS, REPRESENTATIONS AND WARRANTIES, INCLUDING ANY IMPLIED WARRANTY OF MERCHANTABILITY, FITNESS FOR A PARTICULAR PURPOSE OR NON-INFRINGEMENT, ARE DISCLAIMED, EXCEPT TO THE EXTENT THAT SUCH DISCLAIMERS ARE HELD TO BE LEGALLY INVALID. SYMANTEC CORPORATION SHALL NOT BE LIABLE FOR INCIDENTAL OR CONSEQUENTIAL DAMAGES IN CONNECTION WITH THE FURNISHING, PERFORMANCE, OR USE OF THIS DOCUMENTATION. THE INFORMATION CONTAINED IN THIS DOCUMENTATION IS SUBJECT TO CHANGE WITHOUT NOTICE. Symantec Corporation 350 Ellis Street Mountain View, CA 94043 www.symantec.com Policy Guide/Page 4 Symantec Web Security Service Policy Guide The Symantec Web Security Service solutions provide real-time protection against web-borne threats. As a cloud-based product, the Web Security Service leverages Symantec's proven security technology as well as the WebPulse™ cloud com- munity of over 75 million users. -
A Comprehensive Overview Last Updated: January
Project ACRN: A Comprehensive Overview Last updated: January 19, 2021 Content ❖ Introduction ❖ Architecture ❖ Value Proposition ❖ Key Capabilities ❖ Scenarios Introduction ACRN™ is a flexible, lightweight reference hypervisor, built with real-time and safety-criticality in mind, optimized to streamline embedded development through an open source platform. - A Linux Foundation Project Launched in March 2018 - Version 1.0 released in May 2019 - Version 2.0 released in June 2020 Overallarchitecture ACRN is a registered trademark of the Linux Foundation. *Other names and brands may be claimed as the property of others. Value Proposition - ACRN Small Footprint • Optimized for resource-constrained devices • Small codebase: less than 40,000 vs. >156,000 lines of code for datacenter-centric hypervisors Functional Safety & Hard Real-time • Heterogeneous Workloads Consolidation • Supports also the most demanding workloads: safety-critical and real- time Open-source with Flexible License • Permissive BSD license enables proprietary Guest OS • Business-friendly to adopt, modify and integrate • True open source with a vibrant Community ACRN reduces system deployment complexity, enables heterogeneous architectures, and provide TCO advantages Key Capabilities Functional Safety Hard Real-time MISRA-C Compliance Support hard or soft RT VM FuSa certification targeted Optimized for RT, e.g. no VMExit*, cache isolation Security & Isolation Rich I/O Mediation Full isolation for mixed criticality workloads Graphics, Audio, USB… Intel VT backed isolation Industry -

Vms, Unikernels and Containers: Experiences on the Performance of Virtualiza�On Technologies
VMs, Unikernels and Containers: Experiences on the Performance of Virtualizaon Technologies Felipe Huici, Filipe Manco, Jose Mendes, Simon Kuenzer NEC Europe Ltd. (Heidelberg) In the Beginning… VM In the Beginning… “Tinyfied VMs” VM In the Beginning… “Tinyfied VMs” unikernels VM In the Beginning… “Tinyfied VMs” containers unikernels VM In the Beginning… “Tinyfied VMs” containers unikernels VM Virt. Technology Benchmarking • Metrics: – VM Image and memory consump=on – VM creaon =me – Delay – Throughput Virt. Technology Benchmarking • Metrics: – VM Image and memory consump=on – VM creaon =me – Delay – Throughput higher lower overhead overhead Virt. Technology Benchmarking • Metrics: – VM Image and memory consump=on – VM creaon =me – Delay – Throughput higher lower overhead overhead Virt. Technology Benchmarking • Metrics: – VM Image and memory consump=on – VM creaon =me – Delay – Throughput higher lower overhead overhead Virt. Technology Benchmarking • Metrics: – VM Image and memory consump=on – VM creaon =me – Delay – Throughput higher lower overhead overhead Virt. Technology Benchmarking • Metrics: – VM Image and memory consump=on – VM creaon =me – Delay – Throughput higher lower overhead overhead Virt. Technology Benchmarking • Metrics: – VM Image and memory consump=on – VM creaon =me – Delay – Throughput ? higher lower overhead overhead Virt. Technology Benchmarking • Metrics: – VM Image and memory consump=on – VM creaon =me – Delay – Throughput higher lower overhead overhead Virt. Technology Benchmarking • Metrics: – VM Image and memory consump=on – VM creaon =me – Delay – Throughput ? higher lower overhead overhead Virtualizaon Technology Benchmarking • Metrics: – VM image and memory consump=on: ls, top, xl – VM creaon =me: SYN flood + RST detec=on – Throughput: iperf, guest to host (TCP traffic) – RTT: ping flood • VM-based tests run on both Xen and KVM • Hardware: x86_64 server with an Intel Xeon E5-1630 v3 3.7GHz CPU (4 cores), 32GB RAM. -

Symantec Web Security Service Policy Guide
Web Security Service Policy Guide Revision: NOV.07.2020 Symantec Web Security Service/Page 2 Policy Guide/Page 3 Copyrights Broadcom, the pulse logo, Connecting everything, and Symantec are among the trademarks of Broadcom. The term “Broadcom” refers to Broadcom Inc. and/or its subsidiaries. Copyright © 2020 Broadcom. All Rights Reserved. The term “Broadcom” refers to Broadcom Inc. and/or its subsidiaries. For more information, please visit www.broadcom.com. Broadcom reserves the right to make changes without further notice to any products or data herein to improve reliability, function, or design. Information furnished by Broadcom is believed to be accurate and reliable. However, Broadcom does not assume any liability arising out of the application or use of this information, nor the application or use of any product or circuit described herein, neither does it convey any license under its patent rights nor the rights of others. Policy Guide/Page 4 Symantec WSS Policy Guide The Symantec Web Security Service solutions provide real-time protection against web-borne threats. As a cloud-based product, the Web Security Service leverages Symantec's proven security technology, including the WebPulse™ cloud community. With extensive web application controls and detailed reporting features, IT administrators can use the Web Security Service to create and enforce granular policies that are applied to all covered users, including fixed locations and roaming users. If the WSS is the body, then the policy engine is the brain. While the WSS by default provides malware protection (blocks four categories: Phishing, Proxy Avoidance, Spyware Effects/Privacy Concerns, and Spyware/Malware Sources), the additional policy rules and options you create dictate exactly what content your employees can and cannot access—from global allows/denials to individual users at specific times from specific locations. -

The Open Virtual Machine Format Whitepaper for OVF Specification
The Open Virtual Machine Format Whitepaper for OVF Specification version 0.9 OVF Whitepaper 0.9 VMware, Inc. 3401 Hillview Ave., Palo Alto CA, 94304 USA Tel 877-486-9273 Fax 650-427-5001 www.vmware.com XenSource, Inc. 2300 Geng Road, Suite 2500, Palo Alto, CA 94303 www.xensource.com Copyright © VMware, Inc. and XenSource, Inc. All rights reserved. VMware, the VMware “boxes” logo and design, Virtual SMP and VMotion are registered trademarks or trademarks of VMware, Inc. in the United States and/or other jurisdictions. Xen, XenSource, the “Circle Xen” logo and derivatives thereof are registered trademarks or trademarks of XenSource, Inc. in the United States and other countries. Microsoft, Windows and Windows NT are registered trademarks of Microsoft Corporation. Linux is a registered trademark of Linus Torvalds. All other marks and names mentioned herein may be trademarks of their respective companies. No part of this specification (whether in hardcopy or electronic form) may be reproduced, stored in a retrieval system, or transmitted, in any form or by any means, electronic, mechanical, photocopying, recording, or otherwise, without the prior written permission of VMware, Inc. (VMware), and XenSource, Inc. (XenSource) except as otherwise permitted under copyright law or the terms of that certain Teaming and Non-Disclosure Agreement between VMware and XenSource dated March 23, 2007, as amended from time to time. Please note that the content in this specification is protected under copyright law even if it is not distributed with software -

Design a System That “Just Works” the Arm Serverready Program and Beyond
Design a System that “Just Works” The Arm ServerReady Program and Beyond November 2019 White Paper 1 Contents Page Topic 3 Executive Summary 3 1. Introduction 3 2. Arm ServerReady Program 3 2.1 Background and History 4 2.2 Arm Standards-Based Approach 6 3. Arm Server Advisory Committee (ServerAC) 6 3.1 ServerAC Development Process 8 4. Arm Server Standards 8 4.1 Server Base System Architecture (SBSA) 8 4.2 Server Base Boot Requirements (SBBR) 9 4.3 Server Base Security Guide (SBSG) 10 4.4 Server Base Manageability Requirements (SBMR) 11 5. Architectural Compliance Suites 12 5.1 Arm ServerReady Players and Responsibilities 15 6. Conclusion 16 7. Glossary 2 Executive Summary This whitepaper describes the ServerReady program, certification process, and Arm’s standards-based approach to system development. This approach is not limited to servers, it is suitable for other use cases, including edge and client devices, if standard operating systems are used. The intended audience is Arm-based processors and systems developers and integrators. By reading this paper, you will learn about Arm’s standards- based approach for development, and how to design and certify systems with the Arm ServerReady program. 1. Introduction In order to design a system that “just works” for the end user, with the ability to install and run standard operating systems (e.g. Windows, RHEL, VMWare, etc…) out-of-the-box, a set of minimum hardware and firmware requirements must be followed. For the Arm Ecosystem, such a need first surfaced in the server segment. The Arm ServerReady compliance program provides this “just works” solution for servers, enabling partners to deploy Arm servers with confidence. -
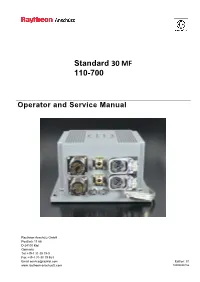
Operator and Service Manual Standard 30 MF
Standard 30 MF 110-700 Operator and Service Manual Raytheon Anschütz GmbH Postfach 11 66 D-24100 Kiel Germany Tel +49-4 31-30 19-0 Fax +49-4 31-30 19 464 Email [email protected] Edition: 01 www.raytheon-anschuetz.com 10000000756 Dieses Dokument sowie dessen Inhalt sind This document and its content are copyright urheberrechtlich geschützt. Die Weitergabe, protected. Distribution, reproduction and Vervielfältigung und Speicherung sowie die storage as well as translation and exploitation Übersetzung wie auch Verwendung dieses of this document and its content, in whole or Dokuments oder dessen Inhalts, als Ganzes in parts and regardless of what form, are oder in Teilen und egal in welcher Form, ist prohibited without prior express written ohne vorherige ausdrückliche schriftliche permission. Offenders will be held liable for Genehmigung nicht gestattet. the payment of damages. Zuwiderhandlungen verpflichten zu Schadenersatz. Änderungen dieses Dokuments und dessen Changes and modification to this document Inhalt bleiben vorbehalten. and its content reserved. Standard 30 MF 110-700 Operator and Service Manual This manual has been drawn up as a description and reference work. It will help answer questions and will solve problems in the quickest possible manner. Before operating the equipment read and follow the instructions and hints provided in this manual. For this purpose refer to the table of contents and read the corresponding chapters thoroughly. If you have any further questions, please contact us at the following address: RAYTHEON ANSCHÜTZ GMBH Tel. +49 431 / 3019 - 0 Zeyestr. 16 - 24 Fax +49 431 / 3019 - 291 D-24106 Kiel Germany All rights reserved. -

FVD: a High-Performance Virtual Machine Image Format for Cloud
FVD: a High-Performance Virtual Machine Image Format for Cloud Chunqiang Tang IBM T.J. Watson Research Center [email protected] http://www.research.ibm.com/people/c/ctang/ Note: This paper describes the copy-on-write, copy- 1 Introduction on-read, and adaptive prefetching capabilities of FVD. The compact image capability of FVD is described Cloud Computing is widely considered as the next big separately in a companion paper entitled “Compact thing in IT evolution. In a Cloud like Amazon EC2 [1], Image Support in Fast Virtual Disk (FVD)”, which the storage space for virtual machines’ virtual disks can is available at https://researcher.ibm.com/ be allocated from multiple sources: the host’s direct- researcher/view project.php?id=1852 attached storage (DAS, i.e., local disk), network-attached storage (NAS), or storage area network (SAN). These op- Abstract tions offer different performance, reliability, and avail- ability at different prices. DAS is at least several times This paper analyzes the gap between existing hyper- cheaper than NAS and SAN, but DAS limits the avail- visors’ virtual disk capabilities and the requirements in ability and mobility of VMs. a Cloud, and proposes a solution called FVD (Fast Vir- tual Disk). FVD consists of an image format and a To get the best out of the different technologies, a block device driver designed for QEMU. Despite the ex- Cloud usually offers a combination of block-device stor- istence of many popular virtual machine (VM) image age services to VMs. For instance, Amazon Web Ser- formats, FVD came out of our unsatisfied needs in the vices (AWS) [2] offers to a VM both ephemeral storage IBM Cloud.