Spectral, Energy and Computation Efficiency in Future 5G Wireless
Total Page:16
File Type:pdf, Size:1020Kb
Load more
Recommended publications
-
Energy Efficiency in Cellular Networks
Energy Efficiency in Cellular Networks Radha Krishna Ganti Indian Institute of Technology Madras [email protected] Millions 1G 2G:100Kbps2G: ~100Kb/s 3G:~1 Mb/s 4G: ~10 Mb/s Cellular Network will connect the IOT Source:Cisco Case Study: Mobile Networks in India • India has over 400,000 cell towers today • 70%+ sites have grid outages in excess of 8 hours a day; 10% are completely off-grid • Huge dependency on diesel generator sets for power backups – India imports 3 billion liters of diesel annually to support Cell Tower, DG Set, Grid these cell sites – CO2 emission exceeds 6 million metric tons a year – Energy accounts for ~25% of network opex for telcos • As mobile services expand to remote rural areas, enormity of this problem grows 4 Power consumption breakup Core network Radio access network Mobile devices 0.1 W x 7 B = 0.7 GW 2 kW x 5M = 10 GW 10 kW x 10K = 0.1 GW *Reference: Mid-size thermal plant output 0.5 GW Source: Peng Mobicomm 2011 Base station energy consumption 1500 W 60 W Signal processing 150 W 1000 W 100 W Air conditioning Power amplifier (PA) 200 W (10-20% efficiency) Power conversion 150 W Transmit power Circuit power Efficiency of PA Spectral Efficiency: bps/Hz (Shannon) Transmit power Distance Bandwidth Cellular Standard Spectral efficiency Noise power 1G (AMPS) 0.46 Spectral density 2G (GSM) 1.3 3G (WCDMA) 2.6 4G (LTE) 4.26 Energy Efficiency: Bits per Joule 1 Km 2 Km EE versus SE for PA efficiency of 20% Current status Source: IEEE Wireless Comm. -

Trade-Off Energy and Spectral Efficiency in 5G Massive MIMO System
Trade-off Energy and Spectral Efficiency in 5G Massive MIMO System Adeb Salh 1*, Nor Shahida Mohd Shah2*, Lukman Audah1, Qazwan Abdullah1, Norsaliza Abdullah3, Shipun A. Hamzah1, Abdu Saif1 1Faculty of Electrical and Electronic Engineering, Universiti Tun Hussein Onn Malaysia, Parit Raja, Batu Pahat, Johor, Malaysia. 2Faculty of Engineering Technology, Universiti Tun Hussein Onn Malaysia, Pagoh, Muar, Johor, Malaysia. 3Faculty of Applied Sciences and Technology, Universiti Tun Hussein Onn Malaysia, Pagoh, Muar, Johor, Malaysia. *Corresponding authors’ e-mail: [email protected], [email protected] to multiple single active users (UEs) in same time-frequency resource. The EE and SE cannot be simultaneously optimized. ABSTRACT It is still quasi-concave due to noise amplifier, a large number of antennas, and cost of hardware, which decreases the radio A massive multiple-input multiple-output (MIMO) system is frequency chains (RF) [7]-[15]. A large number of antennas in very important to optimize the trade-off energy-efficiency both linear precoder and decoder are needed to select the (EE) and spectral-efficiency (SE) in fifth-generation cellular optimal antenna to limit the noise with uncorrelated networks (5G). The challenges for the next generation depend interference. In addition, deploying more antennas causes on increasing the high data traffic in the wireless higher circuit power consumption. From the perspective of communication system for both EE and SE. In this paper, the energy-efficiency, the increasing base stations in the cellular trade-off EE and SE based on the first derivative of transmit networks reported that the total consumed energy in the whole antennas and transmit power in downlink massive MIMO network approximately 60-80% [16]-[20]. -

Spectral Efficiency in the Wideband Regime Sergio Verdú, Fellow, IEEE
IEEE TRANSACTIONS ON INFORMATION THEORY, VOL. 48, NO. 6, JUNE 2002 1319 Spectral Efficiency in the Wideband Regime Sergio Verdú, Fellow, IEEE Invited Paper Abstract—The tradeoff of spectral efficiency (b/s/Hz) versus en- as a synonym of asymptotic optimality in the low-power ergy-per-information bit is the key measure of channel capacity in regime. Using this criterion, Golay [3] showed that (1) can the wideband power-limited regime. This paper finds the funda- be approached by on–off keying (pulse position modulation) mental bandwidth–power tradeoff of a general class of channels in the wideband regime characterized by low, but nonzero, spectral with very low duty cycle, a signaling strategy whose error efficiency and energy per bit close to the minimum value required probability was analyzed in [4]. for reliable communication. A new criterion for optimality of sig- Enter fading. Jacobs [5] and Pierce [6] noticed not only that naling in the wideband regime is proposed, which, in contrast to (1) is achieved if all the energy is concentrated in one message- the traditional criterion, is meaningful for finite-bandwidth com- dependent frequency slot, but also that the limiting rate in (1) munication. is unexpectedly robust: it is achievable even if the orthogonal Index Terms—Antenna arrays, channel capacity, fading chan- signaling undergoes fading which is unknown to the receiver (a nels, noisy channels, spectral efficiency, wideband regime. result popularized by Kennedy [7]). Since only one frequency (or time) slot carries energy, this type of orthogonal signaling I. INTRODUCTION not only is extremely “peaky” but requires that the number of slots grows exponentially with the number of information bits. -

Spectral Efficiency and BER Analysis in 802.16E Standard
Spectral Efficiency and BER Analysis In 802.16e Standard A thesis submitted in partial fulfilment of the requirements for the award of the Degree of MASTER of ENGINEERING in ELECTRONICS AND COMMUNICATION ENGINEERING Submitted by: SHYAM PRATAP SINGH Roll No. 800861013 Under the guidance of: Dr. KULBIR SINGH Assistant Professor, ECED DEPARTMENT OF ELECTRONICS AND COMMUNICATION ENGINEERING THAPAR UNIVERSITY PATIALA-147004, Punjab, INDIA. June 2010 ABSTRACT Spectrum being nature’s gift; needs most wise use of it. OFDM system is an excellent way to utilize the spectrum. OFDM is a parallel data transmission system which promises the high data rate with minimum degradation of the quality of service relative to serial communication techniques. In OFDM, a single channel utilizes multiple sub-carriers on adjacent frequencies. In addition the sub- carriers in an OFDM system are overlapping to maximize spectral efficiency. Ordinarily, overlapping adjacent channels can interfere with one another. However, sub-carriers in an OFDM system are precisely orthogonal to one another. Thus, they are able to overlap without interfering. As a result, OFDM systems are able to maximize spectral efficiency without causing adjacent channel interference. In order to obtain the orthogonality the subcarrier frequencies must be spaced by a multiple of the inverse of symbol duration. Other than spectral efficiency OFDM has many advantages, as immunity to impulse interference, resilient to RF interference, robustness to channel fading, resistance to multipath, much lower computational complexity(collectively, they reduces bit error rate ). Also, WiMAX being one of the standards which is using OFDM, has excellent spectral efficiency but there are no limits for researcher’s, that is inspiration for “spectral-efficiency and BER analysis in 802.16e”. -

5G Vision and Requirements of 5G Forum, Korea
5G Vision and Requirements Of 5G Forum, Korea Prof. Yongwan Park [[email protected]] Feb. 2014 Service Subcommittee Chair 5G Forum, Korea 01 Mobile Communication Trend 02 5G Service Vision 03 5G System Requirement 04 5G Forum, Korea Mobile Communication Trend Smart Super-fast Cost Giga Welfare Infra Devices Hyper Effective Service Demand Explosion Connection Systems Demand x10 ~ x1000 Connecting all Need New Solution Driven by display National wide 5Billion devices derives new to resolve ARPU tech. & Giga knowledge based to business models reduction over networks service for all people 5Trillion CAPEX/OPEX (AR, Hologram, UHD) in need Service Trend • Multimedia Services will Require More and More Bandwidth • Mobile Cloud Services are Growing Rapidly • Augmented Reality/Virtual Reality Services will Become Common • Social Networking Services will be Expanded with Rich Contents • M2M Devices Proliferate & High Data Rate Media-Based M2M Service will Grow • Personalized Services will be Integrated into Daily Life (LBS, u-health) Device Trend Penetration of Smartphone Terminals Device Environmental Trend • The spread of smartphones will continue to rise • Slim & High Resolution, Flexible Display will be worldwide introduced - Traffic share : 44.2%(‘12) → 67.5%(‘17) • Smartphones generate tremendous traffic (compared with feature phones) - Smartphone : 24times ↑, Tablet : 122times ↑ Network Trend Traffic Explosion Status of Mobile Subscribers(Korea) Unit : person 54,514,397 60,000,000 50,000,000 38,160,077 SK 40,000,000 KT 23,993,469 30,000,000 -
CTIA Spectrum Efficiency
Smarter and More Efficient: How America’s Wireless Industry Maximizes Its Spectrum 1 Executive Summary The wireless industry is always looking for more spectrum As 5G is deployed, the demands on wireless networks are to meet the growing demand for mobile data, power the only going to increase. 5G will enable a massive increase connectivity that creates jobs and grows the economy, in the number of wirelessly-connected devices, and and sustain the networks that hundreds of millions of the significant increase in 5G network speeds will drive Americans rely upon every day. further increases in data across wireless networks. But as the industry works with policymakers and federal Facing this explosion in mobile data traffic, wireless agencies to find new spectrum to bring to market, wireless providers have taken aggressive efforts to maximize providers are also investing heavily to make more efficient their limited spectrum resources. As Verizon CEO Hans use of the spectrum holdings they have today. Vestberg said, “[T]here are billions of dollars going into spectrum efficiency every day.”2 The reason is simple: Spectral efficiency is not an academic exercise for U.S. efficient use of industry’s spectrum resources is critical wireless providers. It’s essential. Facing a hockey stick to consumers’ mobile experience. increase of mobile data growth, wireless providers must look at all strategies to increase network capacity— Spectrum efficiency has also been a hallmark of the U.S. incorporating new, more efficient wireless technologies focus on flexible, exclusive-use licensing—a framework into their networks and deploying densified infrastructure. that has driven America’s wireless leadership. -

Hybrid Adaptive Bias OFDM-Based IM/DD Visible Light Communication System
hv photonics Article Hybrid Adaptive Bias OFDM-Based IM/DD Visible Light Communication System Huandong Hong † and Zhengquan Li *,† Jiangsu Provincial Engineering Laboratory of Pattern Recognition and Computational Intelligence, Jiangnan University, Wuxi 214122, China; [email protected] * Correspondence: [email protected]; Tel.: +86-138-6183-7081 † These authors contributed equally to this work. Abstract: Conventional optical orthogonal frequency division multiplexing (OFDM) schemes, such as adaptively biased optical OFDM (ABO-OFDM) and hybrid asymmetrically clipped optical OFDM (HACO-OFDM), are unable to tap all the resources of the subcarriers and only achieve relatively high power efficiency. In this paper, a hybrid adaptive bias optical OFDM (HABO-OFDM) scheme for visible light communication (VLC) is proposed to improve spectral efficiency and power efficiency. In the proposed HABO-OFDM scheme, different optical OFDM components are combined for transmission at the same time, and the adaptive bias is designed to ensure the non-negativity, as well as obtaining significantly high power efficiency. Meanwhile, the implementation complexity of the HABO-OFDM receiver is notably lower than the conventional superimposed optical OFDM schemes. Simulation results show that the proposed HABO-OFDM scheme outperforms ABO-OFDM and HACO-OFDM in terms of both peak-to-average-power ratio (PAPR) and power efficiency. The PAPR performance of HABO-OFDM is about 3.2 dB lower than that of HACO-OFDM and 1.7 dB lower than that of ABO-OFDM. Moreover, we can see that the Eb(elec)/N0 required for HABO-OFDM to reach the BER target is lower than the other two schemes at the Bit rate/Normalized bandwidth range of 3.5 to 8.75, which means that the power efficiency of HABO-OFDM is higher in this range. -

Increasing Spectral Efficiency in Wifi6 Networks Using OBSS/PD
1 More WiFi for Everyone: Increasing Spectral Efficiency in WiFi6 Networks using OBSS/PD Mechanism Ali Karakoc¸, Mehmet S¸ukr¨ u¨ Kuran, Member IEEE, and H. Birkan Yilmaz, Member, IEEE Abstract This study aims to enhance spatial reuse by using the new features of IEEE 802.11ax WLANs. Since the wireless medium is a shared medium and there may be multiple basic service sets (BSS) in the same vicinity, BSSs may overlap, and interference occurs. In this situation, BSSs cannot transmit simultaneously due to the exposed node problem. The IEEE 802.11ax standard has a couple of mechanisms to resolve these spectral efficiency problems. One of the most effective mechanisms that address these problems is the overlapping BSS preamble detection (OBSS/PD) mechanism. OBSS/PD mechanism uses the color mechanism to distinguish OBSS signals. By using a signal threshold, the mechanism can ignore some of the signals, which cause interference. In this paper, we propose a rate-adaptive dynamic OBSS/PD threshold algorithm that tracks the changes in transmission rate and dynamically adjusts the threshold step by step considering the changes. I. INTRODUCTION HIS paper focuses on the WiFi standard IEEE 802.11ax and its features related to spatial reuse. Among the various features T being proposed in WiFi6, one of them is the OBSS-PD mechanism. In dense environments, if there are overlapping BSSs using the same channels, the traffic belonging to these BSSs must share the channel and contend for access. Before performing the transmission, each node should check whether the medium is in an idle state or not. -

ENERGY and SPECTRAL EFFICIENCY of VERY LARGE MULTIUSER MIMO SYSTEMS 3 Propagation
Energy and Spectral Efficiency of Very Large Multiuser MIMO Systems Hien Quoc Ngo, Erik G. Larsson and Thomas L. Marzetta Linköping University Post Print N.B.: When citing this work, cite the original article. ©2013 IEEE. Personal use of this material is permitted. However, permission to reprint/republish this material for advertising or promotional purposes or for creating new collective works for resale or redistribution to servers or lists, or to reuse any copyrighted component of this work in other works must be obtained from the IEEE. Hien Quoc Ngo, Erik G. Larsson and Thomas L. Marzetta, Energy and Spectral Efficiency of Very Large Multiuser MIMO Systems, 2013, IEEE Transactions on Communications, (61), 4, 1436-1449. http://dx.doi.org/10.1109/TCOMM.2013.020413.110848 Post print available at: Linköping University Electronic Press http://urn.kb.se/resolve?urn=urn:nbn:se:liu:diva-85224 IEEE TRANSACTIONS ON COMMUNICATIONS, VOL. XX, NO. X, XXX 2012 1 Energy and Spectral Efficiency of Very Large Multiuser MIMO Systems Hien Quoc Ngo, Erik G. Larsson, and Thomas L. Marzetta Abstract—A multiplicity of autonomous terminals simultane- Recently, there has been a great deal of interest in MU- ously transmits data streams to a compact array of antennas. MIMO with very large antenna arrays at the BS. Very large ar- The array uses imperfect channel-state information derived rays can substantially reduce intracell interference with simple from transmitted pilots to extract the individual data streams. The power radiated by the terminals can be made inversely signal processing [8]. We refer to such systems as “very large proportional to the square-root of the number of base station MU-MIMO systems” here, and with very large we mean arrays antennas with no reduction in performance. -
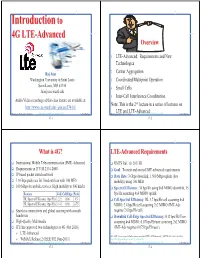
Introduction Toto 4G4G LTELTE--Advancedadvanced Overview
IntroductionIntroduction toto 4G4G LTELTE--AdvancedAdvanced Overview 1. LTE-Advanced: Requirements and New Technologies Raj Jain 2. Carrier Aggregation Washington University in Saint Louis 3. Coordinated Multipoint Operation Saint Louis, MO 63130 4. Small Cells [email protected] 5. Inter-Cell Interference Coordination Audio/Video recordings of this class lecture are available at: Note: This is the 2nd lecture in a series of lectures on http://www.cse.wustl.edu/~jain/cse574-16/ Washington University in St. Louis http://www.cse.wustl.edu/~jain/cse574-16/ ©2016 Raj Jain WashingtonLTE University and in St. LouisLTE-Advancedhttp://www.cse.wustl.edu/~jain/cse574-16/ ©2016 Raj Jain 17-1 17-2 What is 4G? LTE-Advanced Requirements International Mobile Telecommunication (IMT) Advanced UMTS Rel. 10, 2011H1 Requirements in ITU M.2134-2008 Goal: To meet and exceed IMT-advanced requirements IP based packet switch network Data Rate: 3 Gbps downlink, 1.500 Mbps uplink (low 1.0 Gbps peak rate for fixed services with 100 MHz mobility) using 100 MHz 100 Mbps for mobile services. High mobility to 500 km/hr Spectral Efficiency: 30 bps/Hz using 8x8 MIMO downlink, 15 Feature Cell Cell Edge Peak bps/Hz assuming 4x4 MIMO uplink DL Spectral Efficiency (bps/Hz) 2.2 0.06 15 Cell Spectral Efficiency: DL 3.7 bps/Hz/cell assuming 4x4 UL Spectral Efficiency (bps/Hz) 1.4 0.03 6.75 MIMO, 2.4 bps/Hz/cell assuming 2x2 MIMO (IMT-Adv Seamless connectivity and global roaming with smooth requires 2.6 bps/Hz/cell) handovers Downlink Cell-Edge Spectral Efficiency: 0.12 bps/Hz/User High-Quality Multimedia assuming 4x4 MIMO, 0.07 bps/Hz/user assuming 2x2 MIMO ITU has approved two technologies as 4G (Oct 2010) (IMT-Adv requires 0.075 bps/Hz/user) ¾ LTE-Advanced Ref: 3GPP, “Requirements for Further Advancements for E-UTRA (LTE-Advanced),,” 3GPP TR 36.913 v8.0.1 (03/2009), ¾ WiMAX Release 2 (IEEE 802.16m-2011) http://www.3gpp.org/ftp/specs/archive/36_series/36.913/ Washington University in St. -

Analysis and Evaluation of Spectral Efficiency in Multihop Transmission
NTT DoCoMo Technical Journal Vol. 7 No.4 Analysis and Evaluation of Spectral Efficiency in Multihop Transmission We analyze and evaluate spatial wireless spectral efficien- capacity because wireless resources such as frequency bands, cy, when adaptive rate control is applied to multihop spread code and time slots are consumed in relaying process. transmission where wireless nodes located between trans- Moreover, losses in terms of multiple-access control are also a mitting and receiving nodes act as relaying nodes, and concern because the number of transmitting nodes is greater in clarified its effects. This research was conducted jointly multihop transmission compared to single-hop transmission. with the Yoshida laboratory (Professor Susumu Yoshida), However, assuming that the access control operates in an ideal Graduate School of Informatics, Kyoto University. manner (i.e., the losses due to multiple access are zero), this study uses mathematical models to analyze the impacts of mul- Atsushi Fujiwara tihop transmission on system capacity and demonstrates that multihop transmission can significantly contribute to expansion 1. Introduction of the system capacity. In preparation for rolling out various services making use of wireless transmission, issues such as “expanding coverage” and 2. Bandwidth Efficiency of Multihop “increasing spectral efficiency” are very important, considering Transmission the limited availability of frequency resources. 2.1 Adaptive Modulation in Single-Hop Transmission In wireless transmission in general, it is not possible to The purpose of this research is to clarify the spectral effi- assume that the transmission power output of a transmitting ciency of wireless communication using multihop transmission. node can be increased without limit due to restrictions posed by We thus use “bandwidth efficiency,” which is the maximum the equipment itself as well as various regulations. -

Mobile Broadband Explosion, Rysavy Research/4G Americas, August 2013 Page 2 Advanced Receivers
Table of Contents INTRODUCTION........................................................................................................ 4 DATA EXPLOSION ..................................................................................................... 7 Data Consumption ................................................................................................... 7 Cloud Computing ................................................................................................... 10 Technology Drives Demand ..................................................................................... 11 Wireless Vs. Wireline .............................................................................................. 11 Bandwidth Management ......................................................................................... 14 Market and Deployment .......................................................................................... 16 SPECTRUM DEVELOPMENTS .................................................................................... 18 Incentive Auctions ................................................................................................. 20 NTIA-Managed Spectrum ........................................................................................ 20 3550 to 3650 MHz “Small-Cell” Band ........................................................................ 20 Harmonization ....................................................................................................... 21 Unlicensed Spectrum .............................................................................................