Office DDE – Code Execution Without Macros
Total Page:16
File Type:pdf, Size:1020Kb
Load more
Recommended publications
-

U3-1033 Ovation Netdde Server
Ovation NetDDE Server User Guide Section Title Page Summary of Changes Section 1. Introduction 1-1. Overview. 1-1 1-2. NetDDE Server Features. 1-1 1-3. DDE Overview . 1-2 1-3.1. Application or Service Name. 1-2 1-3.2. Topic . 1-2 1-3.3. Item . 1-3 1-3.4. Network DDE . 1-4 1-4. Limitations . 1-5 Section 2. Getting Started 2-1. Section Overview . 2-1 2-2. Requirements . 2-1 2-2.1. System . 2-1 2-2.2. Hardware . 2-1 2-2.3. Software . 2-2 2-2.4. License Server . 2-2 2-3. Setup . 2-4 2-3.1. Environment Variables Required for Setup. 2-5 2-3.2. Linked Libraries. 2-6 2-3.3. Files Installed During Setup. 2-7 2-3.4. Registry Entries . 2-8 2-3.5. Security . 2-10 2-4. Setup Procedure . 2-10 2-5. Configuration . 2-11 2-5.1. Permissions . 2-11 2-6. Un-installation. 2-11 Section 3. Using NetDDE 3-1. Section Overview . 3-1 3-2. Syntax for Calls. 3-1 Glossary Index 12/00 i U3-1033 (Rev 1) Westinghouse Process Control, Inc. Proprietary Class 2C Summary of Changes This revision of “Ovation NetDDE Server User Guide” (U3-1033) reflects the following changes: • System topic has now been changed to wwwdde_system. • DataCreate and DataOriginate topics are removed from the WDPF NetDDE Server. • The machine name must appear when the point information (or Item) link is created on the WDPF NetDDE Server machine or accessed remotely in Excel or any other DDE supported application. -

Winwedge Users Manual
Version 3.0 Professional Edition 1 License Agreement: ........................................................................................................................2 What is the Software Wedge? ........................................................................................................3 What can you do with the Software Wedge?..................................................................................3 Before You Begin ............................................................................................................................4 System Requirements .................................................................................................................4 Devices Compatible with the Software Wedge............................................................................4 What's New In Version 3.0 ..........................................................................................................5 Why Is It Called the Software Wedge?........................................................................................5 Who’s Using The Software Wedge.................................................................................................6 Getting Started................................................................................................................................7 Installing and Running the Software Wedge ...............................................................................7 How To Obtain Technical Support...............................................................................................7 -
The Old New Thing: Practical Development Throughout The
Praise for The Old New Thing “Raymond Chen is the original raconteur of Windows.” —Scott Hanselman, ComputerZen.com “Raymond has been at Microsoft for many years and has seen many nuances of Windows that others could only ever hope to get a glimpse of. With this book, Raymond shares his knowledge, experience, and anecdotal stories, allowing all of us to get a better understanding of the operating system that affects millions of people every day. This book has something for everyone, is a casual read, and I highly recommend it!” —Jeffrey Richter, Author/Consultant, Cofounder of Wintellect “Very interesting read. Raymond tells the inside story of why Windows is the way it is.” —Eric Gunnerson, Program Manager, Microsoft Corporation “Absolutely essential reading for understanding the history of Windows, its intricacies and quirks, and why they came about.” —Matt Pietrek, MSDN Magazine’s Under the Hood Columnist “Raymond Chen has become something of a legend in the software industry, and in this book you’ll discover why. From his high-level reminiscences on the design of the Windows Start button to his low-level discussions of GlobalAlloc that only your inner-geek could love, The Old New Thing is a captivating collection of anecdotes that will help you to truly appreciate the difficulty inherent in designing and writing quality software.” —Stephen Toub, Technical Editor, MSDN Magazine This page intentionally left blank THE OLD NEW THING This page intentionally left blank THE OLD NEW THING Practical Development ThroughoutT the Evolution of Windows Raymond Chen Upper Saddle River, NJ • Boston • Indianapolis • San Francisco New York • Toronto • Montreal • London • Munich • Paris • Madrid Capetown • Sydney • Tokyo • Singapore • Mexico City Many of the designations used by manufacturers and sellers to distinguish their products are claimed as trademarks. -

Technical Information, You Will Find Several Different Types of Symbols Are Used to Identify Different Sections of Text
Technical FAST/TOOLS R10.01 Information System Hardening Windows 7/8, Windows Server 2008/2012 TI 50A01A10-02EN (Rev. 1.0) Yokogawa Electric Corporation TI 50A01A10-02EN 2-9-32, Nakacho, Musashino-shi, Tokyo, 180-8750 Japan ©Copyright June 2015 (YK) Tel.: 81-422-52-2006 Fax.: 81-422-52-2540 1st Edition June 30, 2015 (YK) Blank Page i Introduction n Purpose In order to protect systems from network related security vulnerabilities, it is important to harden the operating system on which the application is running. This document describes the hardening procedure to be followed for FAST/TOOLS R10.01 systems running Microsoft operating systems. n Validity This document is primarily intended for internal Yokogawa use when engineering projects that use FAST/TOOLS on Microsoft operating systems. n Definitions, Abbreviations and Acronyms AV : Antivirus software DMZ : DeMilitarized Zone GSC : Global SCADA Center SCADA : Supervisory Control And Data Acquisition n References [1] McAfee VirusScan Enterprise version 8.8, YHQ recommended antivirus software. [2] IT Security Guide for System Products (Common Information) TI30A15B30-01E. All Rights Reserved Copyright © 2015, Yokogawa Electric Corporation TI 50A01A10-02EN June 30, 2015-00 ii n Symbol Marks Throughout this Technical Information, you will find several different types of symbols are used to identify different sections of text. This section describes these icons. CAUTION Identifies instructionsthat must be observed in order to avoid physical injury and electric shock or death to the operator. IMPORTANT Identifies importantinformation required to understand operations or functions. TIP Identifies additionalinformation. SEE ALSO Identifies asource to be referred to. n Trademark • FAST/TOOLS is registered trademark of Yokogawa Electric Corporation. -
Abstract Functions, 281 Accelerators, 215–216 Accessibility, 57, 472–480
Chen_Rev_Index 12/6/06 11:09 AM Page 497 Index Abstract functions, 281 Application Compatibility Toolkit, 287–288 Accelerators, 215–216 Application Data vs. My Documents, 450–451 Accessibility, 57, 472–480 Application Verifier, 288 Active Accessibility feature, 480 Arithmetic library for Calc, 337 AddRef method, 274 Arrows,up-down controls,354–355 Address spaces, large, 451–455 Auto-reset events, 112–114 Adjustor thunks, 274–275 Advanced Options dialog, 2–3, 57 Background operations in power management, All Programs list, 403–404 455–457 Alt key for blinking caret, 343–344 Backward compatibility, 283 Alt+Esc hotkey, 58 16-bit DOS and Windows, 288–290 Alt+Tab order, 58–59 BIOS clock, 301–302 Always on top, 58, 436 bugs in, 293–294 Analog clocks, 51 Deer Hunter, 293 Animal-named functions, 22–23 DirectX video driver, 298–299 Animations, stealing, 305 Display Control Panel, 308–309 ANSI code page, 379–390 drive letters, 292–293 converting with Unicode, 391–392 error code, 297–298 UTF-8 as, 431–432 GetWindowText, 45–46 ANSI strings, 164 hardware, 141–142 Anti-aliased fonts, 459–462 intentional crashes, 283 Anti-piracy holograms, 25–26 listview controls, 300–301 Anti-symmetry rule, 243 operating system patches, 299–300 AOL CDs, 487 Printers Control Panel, 306–307 497 Chen_Rev_Index 12/6/06 11:09 AM Page 498 498 index Backward compatibility (Continued) BS_* button styles, 232, 234 QueryInterface, 303–305 “Bug Bunny,” 494 reserved filenames, 290–292 Bug reports, whimsical, 482–483 Shell Folders key, 294–296 Bugs undocumented behavior, 286–288 -
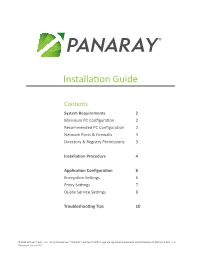
Installation Guide
® Installation Guide Contents System Requirements 2 Minimum PC Configuration 2 Recommended PC Configuration 2 Network Ports & Firewalls 3 Directory & Registry Permissions 3 Installation Procedure 4 Application Configuration 6 Encryption Settings 6 Proxy Settings 7 Quote Service Settings 8 Troubleshooting Tips 10 © 2016 William O’Neil + Co. All rights reserved. “PANARAY” and the PANARAY logo are registered trademarks and trademarks of William O’Neil + Co. Document Version 4.0 System Requirements This section describes the system requirements needed to install and run PANARAY. Minimum PC Configuration Operating System Microsoft Windows 7 Intel Core 2 or AMD dual-core processor running at 2.1Ghz or CPU Intel single core processor with hyper-threading running at 2.10 Ghz RAM 4 Gb Available Disk Space 100 Mb Display Resolution 1280 X 1024 Video Card Video card with 512MB shared video memory and support for DirectX 9 2 Mbps network connection and <200 ms latency when pinging Network Connection tomcat.services.panaray.com Application Framework Microsoft .Net Framework version 4.5.1 Full Adobe Acrobat Reader – Version 9 Software Suggestions Microsoft Excel – Version 2002 Microsoft Windows Media Player – Version 10 Recommended PC Configuration Operating System Microsoft Windows 7 – 64 bit CPU Intel Core 2 or AMD dual-core processor at 2.80 Ghz or faster RAM 6 Gb Available Disk Space 250 Mb Display Resolution 1920 X 1200; multiple monitors are supported Video Card Video card with 512MB dedicated video memory and support for DirectX 10 10 Mbps network connection and <100 ms latency when pinging Network Connection tomcat.services.panaray.com. Application Framework Microsoft .Net Framework version 4.5.1 Full Adobe Acrobat Reader – Version 9 or later Software Suggestions Microsoft Excel – Version 2002 or later Microsoft Windows Media Player – Version 10 or later If you have any questions regarding PANARAY system requirements, please contact Institutional Client Services at [email protected]. -

The Zetafax API Toolkit: Automating Fax Processes
Zetafax API toolkit Zetafax API Toolkit The Zetafax API Toolkit: automating fax processes Zetafax has an API Toolkit that makes it easy to fax-enable existing applications and to automate the process of faxing. The Zetafax API Toolkit provides a set of tools, ranging from embedded addressing to the more complex C language libraries and COM (Component Object Model) technology. Overview The standard method of submitting a fax using Zetafax is to use the client program or your e-mail program to manually specify the recipients and settings such as the coversheet and letterhead. Using the API Toolkit, there are five additional ways of submitting a fax to the Zetafax server. These methods have been designed to make automatic faxing from other applications not only feasible, but also extremely easy to implement. The API Toolkit can also be used to fax enable your existing applications. Fax-enabling your applications The Zetafax API Toolkit lets you send and receive faxes without the need to use the Zetafax Client or your e-mail program. There are many reasons why you may API Toolkit - at a glance benefit from fax-enabling your existing programs. For example, your company may be producing critical documents such as sales proposals, invoices and purchase • Fax-enable all business orders on various systems. These systems can easily be adapted to output a batch of applications documents to single or multiple submit files that the Zetafax server can send • Submit personalized fax broadcasts overnight, thus cutting costs on telephone calls. Or you may simply want to add with the click of a mouse faxing capabilities to your custom developed programs. -
Hostaccess Developer's Guide
HostAccess Developer’s Guide Disclaimer Every effort has been made to ensure that the information contained within this publication is accurate and up-to-date. However, Rogue Wave Software, Inc. does not accept liability for any errors or omissions. Rogue Wave Software, Inc. continuously develops its products and services. We therefore reserve the right to alter the information within this publication without notice. Any changes will be included in subsequent editions of this publication. As the computing industry lacks consistent standards, Rogue Wave Software, Inc. cannot guarantee that its products will be compatible with any combination of systems you choose to use them with. While we may be able to help, you must determine for yourself the compatibility in any particular instance of Rogue Wave Software, Inc. products and your hardware/software environment. Rogue Wave Software, Inc. acknowledges that certain proprietary programs, products or services may be mentioned within this publication. These programs, products or services are distributed under Trademarks or Registered Trademarks of their vendors and/or distributors in the relevant country. Your right to copy this publication, in either hard-copy (paper) or soft-copy (electronic) format, is limited by copyright law. You must obtain prior authorization from Rogue Wave Software, Inc. before copying, adapting or making compilations of this publication. HostAccess is a trademark of Quovadx Ltd in the United Kingdom and is a registered trademark in the USA. Microsoft is a registered trademark and Windows is a trademark of the Microsoft Corporation. Other brands and their products are trademarks or registered trademarks of their respected holders and should be noted as such. -

DCS Gateway (KGTW)
DCS Gateway (KGTW) for providing OPC data to SuiteLink/DDE Clients User Manual Draft Ver 1.x Rev 1.0 DR 550 10 KLINKMANN AUTOMATION P.O. Box 38 FIN-00371 Helsinki Finland tel. int. + 358 9 5404940 fax int. + 358 9 5413541 www.klinkmann.com Klinkmann Automation KGTW i Table Of Contents Overview ........................................................................................................................ 1 Communication Protocols .............................................................................................. 2 Accessing Remote Items via the KGTW ....................................................................... 3 Installing the KGTW....................................................................................................... 4 KGTW general functionality ........................................................................................... 4 Configuring the KGTW .................................................................................................. 5 Server Settings Command ......................................................................................... 6 OPC Server Settings Command ................................................................................ 7 Saving of the KGTW Configuration File ..................................................................... 8 Configuration File Location ........................................................................................ 9 Topic Definition Command ........................................................................................ -

Application Access – Activex® Tun Plus 2014 - Version 15.0.0 Issued December 2013 Copyright © 1989-2014 Esker S.A
Application Access – ActiveX® Tun Plus 2014 - Version 15.0.0 Issued December 2013 Copyright © 1989-2014 Esker S.A. All rights reserved. Copyright © 1998-2008 The OpenSSL Project. All rights reserved. Copyright © 1995-1998 Eric Young ([email protected]). All rights reserved. Copyright © 1995-2005 The Cryptix Foundation Limited. All rights reserved. Copyright © 1995 Tatu Ylonen <[email protected]>, Espoo, Finland. All rights reserved Copyright © 1998 CORE SDI S.A., Buenos Aires, Argentina. All rights reserved Copyright © 1995, 1996 by David Mazieres <[email protected]> Copyright © 1983, 1990, 1992, 1993, 1995 The Regents of the University of California. All rights reserved. Copyright © 1998-2003 by Neil Hodgson [email protected]. All Rights Reserved. For additional information, conditions of use, and disclaimers, see copyright.pdf file. Use and duplicate only in accordance with the Software License Agreement: Tun Products. Esker, the Esker logo, Esker Pro, Extending the Reach of Information, Tun, and Tun Emul are trademarks, registered trademarks or service marks of Esker S.A. in the U.S., France and other countries. The following are trademarks of their respective owners in the United States and other countries: Microsoft, Windows, BackOffice, MS-DOS, XENIX are registered trademarks of Microsoft Corp. Netscape and Netscape Navigator are registered trademarks of Netscape Communications Corp. IBM, AS/400, and AIX are registered trademarks of IBM Corp. SCO is a registered trademark of Caldera International, Inc. NetWare is a registered trademark of Novell, Inc. Sun, Sun Microsystems and Java are trademarks of Sun Microsystems, Inc. Oracle is a registered trademark of Oracle Corp. Informix is a registered trademark of Informix Software Inc. -

Integrating with Goldmine API Specifications and Examples Goldmine Versions 5 Through 9
Integrating with GoldMine API Specifications and Examples GoldMine Versions 5 through 9 490 N. McCarthy Blvd., Suite 100 Milpitas, CA 95035 USA TEL: 800.776.7889 www.heatsoftware.com Rev: 90-05-27-15 Copyright © 2005-2015 HEAT Software USA Inc. All Rights Reserved USE OF THIS SOFTWARE, SUBSCRIPTION SERVICES, AND RELATED USER DOCUMENTATION IS SUBJECT TO THE TERMS AND CONDITIONS OF THE APPLICABLE HEAT SOFTWARE END-USER LICENSE AGREEMENT, HEAT CLOUD SUBSCRIPTION SERVICES AGREEMENT, AND ANY TERMS OF SERVICE (“SUBSCRIPTION AGREEMENT”). YOU MUST AGREE TO THE TERMS AND CONDITIONS OF THE SUBSCRIPTION AGREEMENT IN ORDER TO USE THE SOFTWARE AND SUBSCRIPTION SERVICE. WARNING: The software described in this manual and its related user documentation is protected by copyright law. In no event, shall any part of the software or related user documentation be copied, reproduced, distributed, transmitted, stored in a retrieval system, or translated into any language, without the express written permission of HEAT Software USA Inc. HEAT Software Trademark Information The following are trademarks of HEAT Software USA Inc. and/or its affiliates in the United States and/or other countries: GoldMine®, GoldSync®, GoldMine® Answer Wizard™, GoldMine® Management Intelligence™, GoldMine® Manager's Console™, iGoldMine™, HEAT®, HEAT® Service & Support™, HEAT® PowerDesk™, iHEAT™, HEAT® Self Service™, HEAT® Manager's Console™, HEAT® Answer Wizard™, HEAT® Quick Start Wizard™, InfoCenter®, Automated Processes™, First Level Support®, enteo®, DeviceWall®, Centennial Discovery®, Discovery Dashboard®, MicroAudit®, SAM™, The HEAT Is On™, and other HEAT Software products and brands. Other Trademark Information Microsoft® SQL Server™ is Copyright© 2008, Microsoft Corporation. All rights reserved. This software includes software developed by the Apache Software Foundation (http://www.apache.org/). -
Pc-Based Applications Programming on the Srs Control System
PC-BASED APPLICATIONS PROGRAMMING ON THE SRS CONTROL SYSTEM B.G.Martlew, H.L.Owen, M.J.Pugh, W.R.Rawlinson, S.L.Smith CLRC Daresbury Laboratory, Warrington, WA4 4AD, UK. Abstract and considerable difficulty in multi-tasking. For these reasons it was decided to switch to Windows NT. This The CERN PC-based ISOLDE control system has been has proved to be a very much more stable system which installed at the SRS electron storage ring at Daresbury can successfully multi-task many control system Laboratory. The use of Windows NT for the control applications as well as simplifiying system installation consoles together with PC and VME front-end computers and maintanence. running under several operating systems has resulted in a flexible and reliable system for accelerator control. The 1.2.2 OS-9 VME systems as Front End Computers (FEC) implementation and philosophy of control application The original DOS FEC has been supplemented by porting programs, based around a suite of Microsoft Visual Basic the server code to OS-9. This was originally necessary in and Excel programs, is described. In particular, the use of order to interface to an existing VME/OS-9 based sub- Excel to provide adaptable programs online allows rapid system used for control of the storage ring beam steering generation of new control functions; orbit correction and and orbit diagnostics systems [3]. It has since proved to servoing at the application level are described as be a very versatile and inexpensive (especially in 3U examples of this. format) alternative to DOS-based PCs.