Session 5 - Main Theme Object Management Architectures
Total Page:16
File Type:pdf, Size:1020Kb
Load more
Recommended publications
-

Interaction Between Web Browsers and Script Engines
IT 12 058 Examensarbete 45 hp November 2012 Interaction between web browsers and script engines Xiaoyu Zhuang Institutionen för informationsteknologi Department of Information Technology Abstract Interaction between web browser and the script engine Xiaoyu Zhuang Teknisk- naturvetenskaplig fakultet UTH-enheten Web browser plays an important part of internet experience and JavaScript is the most popular programming language as a client side script to build an active and Besöksadress: advance end user experience. The script engine which executes JavaScript needs to Ångströmlaboratoriet Lägerhyddsvägen 1 interact with web browser to get access to its DOM elements and other host objects. Hus 4, Plan 0 Browser from host side needs to initialize the script engine and dispatch script source code to the engine side. Postadress: This thesis studies the interaction between the script engine and its host browser. Box 536 751 21 Uppsala The shell where the engine address to make calls towards outside is called hosting layer. This report mainly discussed what operations could appear in this layer and Telefon: designed testing cases to validate if the browser is robust and reliable regarding 018 – 471 30 03 hosting operations. Telefax: 018 – 471 30 00 Hemsida: http://www.teknat.uu.se/student Handledare: Elena Boris Ämnesgranskare: Justin Pearson Examinator: Lisa Kaati IT 12 058 Tryckt av: Reprocentralen ITC Contents 1. Introduction................................................................................................................................ -
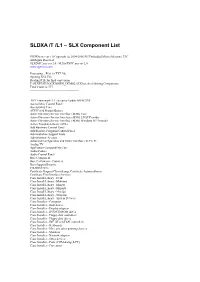
SLDXA /T /L1 – SLX Component List
SLDXA /T /L1 – SLX Component List SLDXA.exe ver 1.0 Copyright (c) 2004-2006 SJJ Embedded Micro Solutions, LLC All Rights Reserved SLXDiffC.exe ver 2.0 / SLXtoTXTC.exe ver 2.0 www.sjjmicro.com Processing... File1 to TXT file. Opening XSL File Reading RTF for final conversion F:\SLXTEST\LOCKDOWN_DEMO2.SLX has the following Components Total Count is: 577 -------------------------------------------------- .NET Framework 1.1 - Security Update KB887998 Accessibility Control Panel Accessibility Core ACPI Fixed Feature Button Active Directory Service Interface (ADSI) Core Active Directory Service Interface (ADSI) LDAP Provider Active Directory Service Interface (ADSI) Windows NT Provider Active Template Library (ATL) Add Hardware Control Panel Add/Remove Programs Control Panel Administration Support Tools Administrator Account Advanced Configuration and Power Interface (ACPI) PC Analog TV Application Compatibility Core Audio Codecs Audio Control Panel Base Component Base Performance Counters Base Support Binaries CD-ROM Drive Certificate Request Client & Certificate Autoenrollment Certificate User Interface Services Class Install Library - Desk Class Install Library - Mdminst Class Install Library - Mmsys Class Install Library - Msports Class Install Library - Netcfgx Class Install Library - Storprop Class Install Library - System Devices Class Installer - Computer Class Installer - Disk drives Class Installer - Display adapters Class Installer - DVD/CD-ROM drives Class Installer - Floppy disk controllers Class Installer - Floppy disk drives -

Using the Component Object Model Interface
MQSeries for Windows NT V5R1 IBM Using the Component Object Model Interface SC34-5387-01 MQSeries for Windows NT V5R1 IBM Using the Component Object Model Interface SC34-5387-01 Note! Before using this information and the product it supports, be sure to read the general information under Appendix B, “Notices” on page 151. Second edition (April 1999) This edition applies to MQSeries for Windows NT V5.1 and to any subsequent releases and modifications until otherwise indicated in new editions. Copyright International Business Machines Corporation 1997,1999. All rights reserved. US Government Users Restricted Rights – Use, duplication or disclosure restricted by GSA ADP Schedule Contract with IBM Corp. Contents Contents About this book ..................................... v Who this book is for ................................... v MQSeries publications . vi MQSeries cross-platform publications ....................... vi MQSeries platform-specific publications ...................... ix MQSeries Level 1 product publications ....................... x Softcopy books . x MQSeries information available on the Internet .................. xii Where to find more information about ActiveX ................... xii Summary of changes ................................. xiii Changes for this edition ................................ xiii Chapter 1. Introduction . 1 MQSeries Automation Classes for ActiveX overview ................ 1 Chapter 2. Designing and programming using MQSeries Automation Classes for ActiveX .................................. 3 Designing -
Installing and Configuring Whatsup Gold V16.3
WhatsUp Gold v16.4 Installation and Conguration Guide Contents Installing and Configuring WhatsUp Gold using WhatsUp Setup Installation Overview ........................................................................................................................................................... 1 Overview ...................................................................................................................................................................... 1 Security considerations ......................................................................................................................................... 2 Standard WhatsUp Gold Installation ............................................................................................................................ 2 Distributed Installation ....................................................................................................................................................... 4 Installing WhatsUp Gold - Distributed (Central Site) ............................................................................... 4 Installing WhatsUp Gold - Distributed (Remote Site) .............................................................................. 6 Failover Installation .............................................................................................................................................................. 7 Installing WhatsUp Gold - Failover (Secondary Site) .............................................................................. -
Identity Provisioning to Masaryk University IT Services Based on Microsoft Environment
Masaryk University Faculty of Informatics Identity provisioning to Masaryk University IT services based on Microsoft environment Master’s Thesis Bc. David Štencel Brno, Spring 2019 Masaryk University Faculty of Informatics Identity provisioning to Masaryk University IT services based on Microsoft environment Master’s Thesis Bc. David Štencel Brno, Spring 2019 This is where a copy of the official signed thesis assignment and a copy ofthe Statement of an Author is located in the printed version of the document. Declaration Hereby I declare that this paper is my original authorial work, which I have worked out on my own. All sources, references, and literature used or excerpted during elaboration of this work are properly cited and listed in complete reference to the due source. Bc. David Štencel Advisor: Mgr. Kamil Malinka, Ph.D. i Acknowledgements I would like to thank my advisor Mgr. Kamil Malinka, Ph.D. for his professional guidance and experience. Also, I would like to thank Jan Izydorczyk, Mgr. Slávek Licehammer, and the rest of the Office 365 team at ICS for their collaboration, support, and patience during the creation of this master’s thesis. Finally, I would like to thank my family for all their support during my whole studies. iii Abstract The aim of the thesis is to design and implement an interconnection of university identity management system Perun with services run- ning in Microsoft environment. Resultant PowerShell scripts utilizing OpenSSH and PowerShell remoting allow data transmission from Perun to Windows hosts and launching service provisioning scripts. The thesis covers Active Directory and Office 365 as example target services, and a revised PowerShell web proxy that adjusts additional object settings within university Office 365. -

(RUNTIME) a Salud Total
Windows 7 Developer Guide Published October 2008 For more information, press only: Rapid Response Team Waggener Edstrom Worldwide (503) 443-7070 [email protected] Downloaded from www.WillyDev.NET The information contained in this document represents the current view of Microsoft Corp. on the issues discussed as of the date of publication. Because Microsoft must respond to changing market conditions, it should not be interpreted to be a commitment on the part of Microsoft, and Microsoft cannot guarantee the accuracy of any information presented after the date of publication. This guide is for informational purposes only. MICROSOFT MAKES NO WARRANTIES, EXPRESS OR IMPLIED, IN THIS SUMMARY. Complying with all applicable copyright laws is the responsibility of the user. Without limiting the rights under copyright, no part of this document may be reproduced, stored in or introduced into a retrieval system, or transmitted in any form, by any means (electronic, mechanical, photocopying, recording or otherwise), or for any purpose, without the express written permission of Microsoft. Microsoft may have patents, patent applications, trademarks, copyrights or other intellectual property rights covering subject matter in this document. Except as expressly provided in any written license agreement from Microsoft, the furnishing of this document does not give you any license to these patents, trademarks, copyrights, or other intellectual property. Unless otherwise noted, the example companies, organizations, products, domain names, e-mail addresses, logos, people, places and events depicted herein are fictitious, and no association with any real company, organization, product, domain name, e-mail address, logo, person, place or event is intended or should be inferred. -

Security Policy Page 1 of 20
Security Policy Page 1 of 20 Security Policy This security policy contains data to configure services and network security based on the server’s role, as well as data to configure registry and auditing settings. Server: VENGWIN207 Services Service Name Startup Mode Description Issues, manages, and removes X.509 certificates for such applications such as Active Directory Certificate S/MIME and SSL. If the service is stopped, Disabled Services certificates will not be issued. If this service is disabled, any services that explicitly depend on it will fail to start. AD DS Domain Controller service. If this service is stopped, users will be unable to log Active Directory Domain Services Disabled on to the network. If this service is disabled, any services that explicitly depend on it will fail to start. AD FS Web Agent Authentication The AD FS Web Agent Authentication Service Disabled Service validates incoming tokens and cookies. Adobe Acrobat Updater keeps your Adobe Adobe Acrobat Update Service Automatic software up to date. Sends logging messages to the logging database when logging is enabled for the Active Directory Rights Management Services role. If this service is disabled or stopped AdRmsLoggingService Disabled when logging is enabled, logging messages will be stored in local message queues and sent to the logging database when the service is started. Processes application compatibility cache Application Experience Disabled requests for applications as they are launched Provides administrative services for IIS, for example configuration history and Application Pool account mapping. If this Application Host Helper Service Disabled service is stopped, configuration history and locking down files or directories with Application Pool specific Access Control Entries will not work. -

Installation Instructions for Version 8 (TS M0) of the SAS System For
Installation Instructions for Release 8.1 (TS1M0) of the SAS® System for Microsoft® Windows® Table of Contents Chapter 1, Introduction.......................................................................................................... 1 Terminology and Symbols Used in this Document ................................................................... 1 SASROOT Directory .................................................................................................. 1 Types of Installation Configurations........................................................................... 1 Pre-installation Checklist........................................................................................................... 2 Proper Handling of Your Media................................................................................................ 3 SAS Setup Help for Installing the SAS System......................................................................... 3 Online Help for Using the SAS System..................................................................................... 3 The Help System......................................................................................................... 4 HTML Viewer............................................................................................................. 4 Exiting SAS Setup..................................................................................................................... 4 Additional Documentation ........................................................................................................4 -
Office DDE – Code Execution Without Macros
Cyber Threat Intelligence Report office DDe – coDe execution without macros teChniCal threat analysis Cyber Threat Intelligence (CTI) Team Telekom Security T-Systems International GmbH Contact: [email protected] Document ProPerties Version 1.1 ClassifiCation leVel Public filename CTI_Report_OFFICE_DDE_THREAT_ANALYSIS.docx Keywords Malicious office documents, DDE, dynamic data exchange Create date 11/07/2017 04:13:00 PM last Changed 13.04.2018 10:58:00 AM offiCe DDE – Code exeCution without maCros 1.1 Cyber Threat Intelligence Report office DDe – coDe execution without macros ........................................................................ 1 1 summary ............................................................................................................................ 3 2 Dynamic Data exchange (DDe) .......................................................................................... 4 3 subject of investigation .................................................................................................. 8 4 analysis ............................................................................................................................ 10 4.1 Distribution OF Locky/Trickbot ............................................................................................ 10 4.2 Distribution of Cerber .......................................................................................................... 14 4.3 Distribution of Vortex ......................................................................................................... -

U3-1033 Ovation Netdde Server
Ovation NetDDE Server User Guide Section Title Page Summary of Changes Section 1. Introduction 1-1. Overview. 1-1 1-2. NetDDE Server Features. 1-1 1-3. DDE Overview . 1-2 1-3.1. Application or Service Name. 1-2 1-3.2. Topic . 1-2 1-3.3. Item . 1-3 1-3.4. Network DDE . 1-4 1-4. Limitations . 1-5 Section 2. Getting Started 2-1. Section Overview . 2-1 2-2. Requirements . 2-1 2-2.1. System . 2-1 2-2.2. Hardware . 2-1 2-2.3. Software . 2-2 2-2.4. License Server . 2-2 2-3. Setup . 2-4 2-3.1. Environment Variables Required for Setup. 2-5 2-3.2. Linked Libraries. 2-6 2-3.3. Files Installed During Setup. 2-7 2-3.4. Registry Entries . 2-8 2-3.5. Security . 2-10 2-4. Setup Procedure . 2-10 2-5. Configuration . 2-11 2-5.1. Permissions . 2-11 2-6. Un-installation. 2-11 Section 3. Using NetDDE 3-1. Section Overview . 3-1 3-2. Syntax for Calls. 3-1 Glossary Index 12/00 i U3-1033 (Rev 1) Westinghouse Process Control, Inc. Proprietary Class 2C Summary of Changes This revision of “Ovation NetDDE Server User Guide” (U3-1033) reflects the following changes: • System topic has now been changed to wwwdde_system. • DataCreate and DataOriginate topics are removed from the WDPF NetDDE Server. • The machine name must appear when the point information (or Item) link is created on the WDPF NetDDE Server machine or accessed remotely in Excel or any other DDE supported application. -

The Component Object Model Specification Version 0.9 October 24, 1995
http://scottge.wordpress.com The Component Object Model Specification Version 0.9 October 24, 1995 This document contains the specification to the Component Object Model (COM), an architecture and supporting infrastructure for building, using, and evolving component software in a robust manner. This specification contains the standard APIs supported by the COM Library, the standard suites of interfaces supported or used by software written in a COM environment, along with the network protocols used by COM in support of distributed computing. This specification is still in draft form, and thus subject to change. Note: This document is an early release of the final specification. It is meant to specify and accompany software that is still in development. Some of the information in this documentation may be inaccurate or may not be an accurate representation of the functionality of the final specification or software. Microsoft assumes no responsibility for any damages that might occur either directly or indirectly from these inaccuracies. Microsoft may have trademarks, copyrights, patents or pending patent applications, or other intellectual property rights covering subject matter in this document. The furnishing of this document does not give you a license to these trademarks, copyrights, patents, or other intellectual property rights. Copyright ? 1992-95 Microsoft Corporation. All Rights Reserved The Component Object Model Specification The Component Object Model The Component Object Model Specification Draft Version 0.9, October 24, 1995 Microsoft Corporation and Digital Equipment Corporation Copyright ? 1992-95 Microsoft Corporation. Microsoft does not make any representation or warranty regarding the Specification or any product or item developed based on the Specification. -
An Introduction to Windows Operating System
EINAR KROGH AN INTRODUCTION TO WINDOWS OPERATING SYSTEM Download free eBooks at bookboon.com 2 An Introduction to Windows Operating System 2nd edition © 2017 Einar Krogh & bookboon.com ISBN 978-87-403-1935-4 Peer review by Høgskolelektor Lars Vidar Magnusson, Høgskolen i Østfold Download free eBooks at bookboon.com 3 AN INTRODUCTION TO WINDOWS OPERATING SYSTEM CONTENTS CONTENTS Introduction 9 1 About Windows history 10 1.1 MS-DOS 10 1.2 The first versions of Windows 11 1.3 Windows NT 12 1.4 Windows versions based on Windows NT 13 1.5 Windows Server 15 1.6 Control Questions 17 2 The tasks of an operating system 18 2.1 About the construction of computers 19 2.2 Central tasks for an operating system 20 2.3 Control Questions 22 �e Graduate Programme I joined MITAS because for Engineers and Geoscientists I wanted real responsibili� www.discovermitas.comMaersk.com/Mitas �e Graduate Programme I joined MITAS because for Engineers and Geoscientists I wanted real responsibili� Maersk.com/Mitas Month 16 I wwasas a construction Month 16 supervisorI wwasas in a construction the North Sea supervisor in advising and the North Sea Real work helpinghe foremen advising and IInternationalnternationaal opportunities ��reeree wworkoro placements solves Real work problems helpinghe foremen IInternationalnternationaal opportunities ��reeree wworkoro placements solves problems Download free eBooks at bookboon.com Click on the ad to read more 4 AN INTRODUCTION TO WINDOWS OPERATING SYSTEM CONTENTS 3 Some concepts and terms of the Windows operating system 23 3.1