GNU/Linux Command-Line Tools Summary
Total Page:16
File Type:pdf, Size:1020Kb
Load more
Recommended publications
-
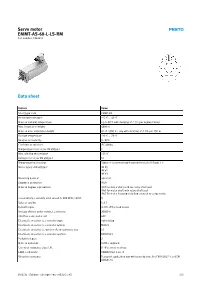
Servo Motor EMMT-AS-60-L-LS-RM Part Number: 5242213
Servo motor EMMT-AS-60-L-LS-RM Part number: 5242213 Data sheet Feature Value Short type code EMMT-AS Ambient temperature -15 °C ... 40 °C Note on ambient temperature Up to 80°C with derating of -1.5% per degree Celsius Max. installation height 4000 m Note on max. installation height As of 1,000 m: only with derating of -1.0% per 100 m Storage temperature -20 °C ... 70 °C Relative air humidity 0 - 90% Conforms to standard IEC 60034 Temperature class as per EN 60034-1 F Max. winding temperature 155 °C Rating class as per EN 60034-1 S1 Temperature monitoring Digital motor temperature transmission via EnDat® 2.2 Motor type to EN 60034-7 IM B5 IM V1 IM V3 Mounting position optional Degree of protection IP40 Note on degree of protection IP40 for motor shaft without rotary shaft seal IP65 for motor shaft with rotary shaft seal IP67 for motor housing including connection components Concentricity, coaxiality, axial runout to DIN SPEC 42955 N Balance quality G 2.5 Detent torque <1.0% of the peak torque Storage lifetime under nominal conditions 20000 h Interface code, motor out 60P Electrical connection 1, connection type Hybrid plug Electrical connection 1, connector system M23x1 Electrical connection 1, number of connections/cores 15 Electrical connection 1, connection pattern 00995913 Pollution degree 2 Note on materials RoHS-compliant Corrosion resistance class CRC 0 - No corrosion stress LABS-Conformity VDMA24364 zone III Vibration resistance Transport application test with severity level 2 to FN 942017-4 and EN 60068-2-6 10/2/21 - Subject to change - Festo AG & Co. -

RACF Tips Volume 3, Issue 1, January 2009
Volume 3 Issue 1 IPS RSH RACF T January For Administrators, Auditors, and Analysts 2009 Specifying a Replacement ID used to change a file's attributes for Program Control, APF Authorized, and Shared Library. with IRRRID00 . To generate commands to delete an ID and all references to it, use RACF's IRRRID00 utility. You simply enter the ID in the SYSIN DD Temporary Access with statement of the IRRRID00 job like so: CONNECT REVOKE(date) //SYSIN DD * USERX You may occasionally need to permit a user temporary access to a resource. One way to do If USERX is the owner of a profile or connect, so is to grant a group access to the resource IRRRID00 generates commands like: and connect the user to that group with a revoke date. The command to set the connect revoke CONNECT RDSADM GROUP(RACFSTC) OWNER(?USERX) date would look something like this: In these cases, you need to change ?USERX to CONNECT USERA GROUP(TEMPACC) REVOKE(1/20/09) a valid replacement ID. This can be done manually or with ISPF EDIT CHANGE. On the date specified with the revoke, RACF will no longer allow the user to have the access Alternatively, you can tell IRRRID00 which permitted to the group. If you want to remove the replacement ID to use when it builds the revoke date but leave the connect intact, enter: commands. If, for instance, you want to replace every occurrence of USERX with USERJ, enter CONNECT USERA GROUP(TEMPACC) NOREVOKE the following in the SYSIN DD: A banking client of ours used this capability to //SYSIN DD * govern access to APF-authorized libraries. -

LS-09EN. OS Permissions. SUID/SGID/Sticky. Extended Attributes
Operating Systems LS-09. OS Permissions. SUID/SGID/Sticky. Extended Attributes. Operating System Concepts 1.1 ys©2019 Linux/UNIX Security Basics Agenda ! UID ! GID ! Superuser ! File Permissions ! Umask ! RUID/EUID, RGID/EGID ! SUID, SGID, Sticky bits ! File Extended Attributes ! Mount/umount ! Windows Permissions ! File Systems Restriction Operating System Concepts 1.2 ys©2019 Domain Implementation in Linux/UNIX ! Two types domain (subjects) groups ! User Domains = User ID (UID>0) or User Group ID (GID>0) ! Superuser Domains = Root ID (UID=0) or Root Group ID (root can do everything, GID=0) ! Domain switch accomplished via file system. ! Each file has associated with it a domain bit (SetUID bit = SUID bit). ! When file is executed and SUID=on, then Effective UID is set to Owner of the file being executed. When execution completes Efective UID is reset to Real UID. ! Each subject (process) and object (file, socket,etc) has a 16-bit UID. ! Each object also has a 16-bit GID and each subject has one or more GIDs. ! Objects have access control lists that specify read, write, and execute permissions for user, group, and world. Operating System Concepts 1.3 ys©2019 Subjects and Objects Subjects = processes Objects = files (regular, directory, (Effective UID, EGID) devices /dev, ram /proc) RUID (EUID) Owner permissions (UID) RGID-main (EGID) Group Owner permissions (GID) +RGID-list Others RUID, RGID Others ID permissions Operating System Concepts 1.4 ys©2019 The Superuser (root) • Almost every Unix system comes with a special user in the /etc/passwd file with a UID=0. This user is known as the superuser and is normally given the username root. -

Oracle® Linux 7 Monitoring and Tuning the System
Oracle® Linux 7 Monitoring and Tuning the System F32306-03 October 2020 Oracle Legal Notices Copyright © 2020, Oracle and/or its affiliates. This software and related documentation are provided under a license agreement containing restrictions on use and disclosure and are protected by intellectual property laws. Except as expressly permitted in your license agreement or allowed by law, you may not use, copy, reproduce, translate, broadcast, modify, license, transmit, distribute, exhibit, perform, publish, or display any part, in any form, or by any means. Reverse engineering, disassembly, or decompilation of this software, unless required by law for interoperability, is prohibited. The information contained herein is subject to change without notice and is not warranted to be error-free. If you find any errors, please report them to us in writing. If this is software or related documentation that is delivered to the U.S. Government or anyone licensing it on behalf of the U.S. Government, then the following notice is applicable: U.S. GOVERNMENT END USERS: Oracle programs (including any operating system, integrated software, any programs embedded, installed or activated on delivered hardware, and modifications of such programs) and Oracle computer documentation or other Oracle data delivered to or accessed by U.S. Government end users are "commercial computer software" or "commercial computer software documentation" pursuant to the applicable Federal Acquisition Regulation and agency-specific supplemental regulations. As such, the use, reproduction, duplication, release, display, disclosure, modification, preparation of derivative works, and/or adaptation of i) Oracle programs (including any operating system, integrated software, any programs embedded, installed or activated on delivered hardware, and modifications of such programs), ii) Oracle computer documentation and/or iii) other Oracle data, is subject to the rights and limitations specified in the license contained in the applicable contract. -
Process Text Streams Using Filters
Process Text Streams Using Filters OBJECTIVE: Candidates should should be able to apply filters to text streams. 1 Process Text Streams Using Filters KeyKEY knowledge KNOWLEDGE area(s): AREAS: Send text files and output streams through text utility filters to modify the output using standard UNIX commands found in the GNU textutils package. 2 Process Text Streams Using Filters KEY FILES,TERMS, UTILITIES cat nl tail cut paste tr expand pr unexpand fmt sed uniq head sort wc hexdump split join tac 3 cat cat the editor - used as a rudimentary text editor. cat > short-message we are curious to meet penguins in Prague Crtl+D *Ctrl+D - command is used for ending interactive input. 4 cat cat the reader More commonly used to flush text to stdout. Options: -n number each line of output -b number only non-blank output lines -A show carriage return Example cat /etc/resolv.conf ▶ search mydomain.org nameserver 127.0.0.1 5 tac tac reads back-to-front This command is the same as cat except that the text is read from the last line to the first. tac short-message ▶ penguins in Prague to meet we are curious 6 head or tail using head or tail - often used to analyze logfiles. - by default, output 10 lines of text. List 20 first lines of /var/log/messages: head -n 20 /var/log/messages head -20 /var/log/messages List 20 last lines of /etc/aliases: tail -20 /etc/aliases 7 head or tail The tail utility has an added option that allows one to list the end of a text starting at a given line. -
Beginning Portable Shell Scripting from Novice to Professional
Beginning Portable Shell Scripting From Novice to Professional Peter Seebach 10436fmfinal 1 10/23/08 10:40:24 PM Beginning Portable Shell Scripting: From Novice to Professional Copyright © 2008 by Peter Seebach All rights reserved. No part of this work may be reproduced or transmitted in any form or by any means, electronic or mechanical, including photocopying, recording, or by any information storage or retrieval system, without the prior written permission of the copyright owner and the publisher. ISBN-13 (pbk): 978-1-4302-1043-6 ISBN-10 (pbk): 1-4302-1043-5 ISBN-13 (electronic): 978-1-4302-1044-3 ISBN-10 (electronic): 1-4302-1044-3 Printed and bound in the United States of America 9 8 7 6 5 4 3 2 1 Trademarked names may appear in this book. Rather than use a trademark symbol with every occurrence of a trademarked name, we use the names only in an editorial fashion and to the benefit of the trademark owner, with no intention of infringement of the trademark. Lead Editor: Frank Pohlmann Technical Reviewer: Gary V. Vaughan Editorial Board: Clay Andres, Steve Anglin, Ewan Buckingham, Tony Campbell, Gary Cornell, Jonathan Gennick, Michelle Lowman, Matthew Moodie, Jeffrey Pepper, Frank Pohlmann, Ben Renow-Clarke, Dominic Shakeshaft, Matt Wade, Tom Welsh Project Manager: Richard Dal Porto Copy Editor: Kim Benbow Associate Production Director: Kari Brooks-Copony Production Editor: Katie Stence Compositor: Linda Weidemann, Wolf Creek Press Proofreader: Dan Shaw Indexer: Broccoli Information Management Cover Designer: Kurt Krames Manufacturing Director: Tom Debolski Distributed to the book trade worldwide by Springer-Verlag New York, Inc., 233 Spring Street, 6th Floor, New York, NY 10013. -

Version 7.8-Systemd
Linux From Scratch Version 7.8-systemd Created by Gerard Beekmans Edited by Douglas R. Reno Linux From Scratch: Version 7.8-systemd by Created by Gerard Beekmans and Edited by Douglas R. Reno Copyright © 1999-2015 Gerard Beekmans Copyright © 1999-2015, Gerard Beekmans All rights reserved. This book is licensed under a Creative Commons License. Computer instructions may be extracted from the book under the MIT License. Linux® is a registered trademark of Linus Torvalds. Linux From Scratch - Version 7.8-systemd Table of Contents Preface .......................................................................................................................................................................... vii i. Foreword ............................................................................................................................................................. vii ii. Audience ............................................................................................................................................................ vii iii. LFS Target Architectures ................................................................................................................................ viii iv. LFS and Standards ............................................................................................................................................ ix v. Rationale for Packages in the Book .................................................................................................................... x vi. Prerequisites -

Linux Toolsettoolset (Part(Part A)A)
[Software[Software Development]Development] LinuxLinux ToolSetToolSet (part(part A)A) Davide Balzarotti Eurecom – Sophia Antipolis, France 1 If Unix can Do It, You Shouldn't As a general rule: Don't implement your own code unless you have a solid reason why common tools won't solve the problem Modern Linux distributions are capable of performing a lot of tasks Most of the hard problems have already been solved (by very smart people) for you... … you just need to know where to look … and choose the right tool for your job 2 Different Tools for Different Jobs Locate the data Extract the data Filter the data Modify the data 3 Getting Help Any Linux distribution comes with thousands of files in /usr/bin Knowing each command is difficult Knowing each option of each command is practically impossible The most useful skill is to know where to look for help Google knows all the answers (if you know how to pose the right questions) help ± documentation for the shell builtin commands cmd --help ± most of the programs give you some help if you ask 4 The Manual Unix man pages were introduced in 1971 to have an online documentation of all the system commands The pages are organized in 8 sections: 1. general commands 5. file formats 2. system calls 6. games 3. C functions 7. misc 4. special files 8. admin commands CAL(1) BSD General Commands Manual CAL(1) NAME cal, ncal - displays a calendar and the date of easter SYNOPSIS cal [-3jmy] [[month] year] ncal [-jJpwy] [-s country_code] [[month] year] ncal [-Jeo] [year] DESCRIPTION The cal utility displays a simple calendar in traditional format and ncal offers an alternative layout, more options and the date of easter 5 Other forms of Help info ± access the Info pages Official documentation of the GNU project Simple hypertext apropos ± searches for keywords in the header lines of all the manpages balzarot:~> apropos calendar cal (1) - displays a calendar and the date of easter calendar (1) - reminder service gcal (1) - a program for calculating and printing calendars. -

The Linux Command Line
The Linux Command Line Fifth Internet Edition William Shotts A LinuxCommand.org Book Copyright ©2008-2019, William E. Shotts, Jr. This work is licensed under the Creative Commons Attribution-Noncommercial-No De- rivative Works 3.0 United States License. To view a copy of this license, visit the link above or send a letter to Creative Commons, PO Box 1866, Mountain View, CA 94042. A version of this book is also available in printed form, published by No Starch Press. Copies may be purchased wherever fine books are sold. No Starch Press also offers elec- tronic formats for popular e-readers. They can be reached at: https://www.nostarch.com. Linux® is the registered trademark of Linus Torvalds. All other trademarks belong to their respective owners. This book is part of the LinuxCommand.org project, a site for Linux education and advo- cacy devoted to helping users of legacy operating systems migrate into the future. You may contact the LinuxCommand.org project at http://linuxcommand.org. Release History Version Date Description 19.01A January 28, 2019 Fifth Internet Edition (Corrected TOC) 19.01 January 17, 2019 Fifth Internet Edition. 17.10 October 19, 2017 Fourth Internet Edition. 16.07 July 28, 2016 Third Internet Edition. 13.07 July 6, 2013 Second Internet Edition. 09.12 December 14, 2009 First Internet Edition. Table of Contents Introduction....................................................................................................xvi Why Use the Command Line?......................................................................................xvi -
BSCW Administrator Documentation Release 7.2.1
BSCW Administrator Documentation Release 7.2.1 OrbiTeam Software Oct 10, 2019 CONTENTS 1 How to read this Manual1 2 Installation of the BSCW server3 2.1 General Requirements........................................3 2.2 Security considerations........................................4 2.3 EU - General Data Protection Regulation..............................4 2.4 Upgrading to BSCW 7.2.1......................................5 2.4.1 Upgrading on Unix..................................... 13 2.4.2 Upgrading on Windows................................... 17 3 Installation procedure for Unix 19 3.1 System requirements......................................... 19 3.2 Installation.............................................. 20 3.3 Software for BSCW Preview..................................... 25 3.4 Configuration............................................. 29 3.4.1 Apache HTTP Server Configuration............................ 29 3.4.2 BSCW instance configuration............................... 33 3.4.3 Administrator account................................... 35 3.4.4 De-Installation....................................... 35 3.5 Database Server Startup, Garbage Collection and Backup..................... 36 3.5.1 BSCW Startup....................................... 36 3.5.2 Garbage Collection..................................... 37 3.5.3 Backup........................................... 37 3.6 Folder Mail Delivery......................................... 38 3.6.1 BSCW mail delivery agent (MDA)............................. 38 3.6.2 Local Mail Transfer Agent -

Linux Hardening Techniques Vasudev Baldwa Ubnetdef, Spring 2021 Agenda
Linux Hardening Techniques Vasudev Baldwa UBNetDef, Spring 2021 Agenda 1. What is Systems Hardening? 2. Basic Principles 3. Updates & Encryption 4. Monitoring 5. Services 6. Firewalls 7. Logging What is System Hardening? ⬡ A collection of tools, techniques, and best practices to reduce vulnerability in technology applications, systems, infrastructure, firmware, and other areas ⬡ 3 major areas: OS vs Software vs Network ⬠ When have we done hardening in this class before? ⬠ This lecture is focusing mostly on OS and software level Why Harden? ⬡ Firewalls can only get us so far, what happens when at attack is inside the network? ⬠ If you have nothing protecting your systems you are in trouble ⬡ We want some kind of secondary protection A Few Cybersecurity Principles ⬡ Zero Trust Security ⬠ Instead of assuming everything behind the firewall is safe, Zero Trust verifies each request as though it originates from an unsecure network ⬡ Principle of Least Privilege ⬠ Only privileges needed to complete a task should be allowed ⬠ Users should not have domain administrator/root privileges ⬡ Principle of Least Common Mechanism ⬠ Mechanisms used to access resources should not be shared in order to avoid the transmission of data. ⬠ Shared resources should not be used to access resources The Threat Model ⬡ A process by which potential threats can be identified and prioritized. ⬠ If you have a web server that feeds input to a mysql database, then protecting against mysql injections would be prioritized in your model. 2 considerations ⬡ *nix like is a very -

Australian Open Source Industry & Community Report 2008
The Australian Open Source Industry & Community Report 2008 Sponsors & Industry Community Map of Education & Supporters Respondents Skills 5 9 11 12 15 Careers & Innovation The Market Business Opinion Employment Development 17 19 19 21 23 Methodology. The Australian Open Source Industry & Community Report was Promotion commissioned and executed by Waugh Partners, with the financial support of sponsors, NICTA, IBM and Fujitsu. The Census was directly promoted through a national roadshow which traveled to every capital city, on several mailing lists including Linux We worked closely with psychometricians and statisticians provided by Australia, Open Source Industry Australia and user groups around the NICTA, our primary research partner, to ensure the end-to-end quality country, and through direct contact with Open Source community of the research. While our sponsors and supporters provided feedback members and companies. Indirect promotion included blogging, media at numerous points throughout the project lifecycle, this report is the coverage, and notification to members of the Australia Computer result of independent analysis by Waugh Partners. It is based on data Society, AIIA, OzZope and numerous other organisations. collected through a pair of online surveys held between October and December 2007. Projections Community We have been very careful to make conservative projections, particularly related to industry revenue. The community survey was aimed at “individuals who contribute to Open Source projects and communities in any capacity, not just Our projected industry and export revenue figures are based upon software development”, and received 315 complete and legitimate the projected industry size and spread of companies compared to the responses, with 66 incomplete.