Yui Kee Computing Ltd
Total Page:16
File Type:pdf, Size:1020Kb
Load more
Recommended publications
-
Microsoft Security Intelligence Report
Microsoft Security Intelligence Report Volume 20 | July through December, 2015 This document is for informational purposes only. MICROSOFT MAKES NO WARRANTIES, EXPRESS, IMPLIED, OR STATUTORY, AS TO THE INFORMATION IN THIS DOCUMENT. This document is provided “as-is.” Information and views expressed in this document, including URL and other Internet website references, may change without notice. You bear the risk of using it. Copyright © 2016 Microsoft Corporation. All rights reserved. The names of actual companies and products mentioned herein may be the trademarks of their respective owners. Authors Charlie Anthe Dana Kaufman Anthony Penta Cloud and Enterprise Security Azure Active Directory Team Safety Platform Nir Ben Zvi Nasos Kladakis Ina Ragragio Enterprise and Cloud Group Azure Active Directory Team Windows and Devices Group Patti Chrzan Daniel Kondratyuk Tim Rains Microsoft Digital Crimes Unit Azure Active Directory Team Commercial Communications Bulent Egilmez Andrea Lelli Paul Rebriy Office 365 - Information Windows Defender Labs Bing Protection Geoff McDonald Stefan Sellmer Elia Florio Windows Defender Labs Windows Defender Labs Windows Defender Labs Michael McLaughlin Mark Simos Chad Foster Identity Services Enterprise Cybersecurity Bing Group Nam Ng Roger Grimes Enterprise Cybersecurity Vikram Thakur Microsoft IT Group Windows Defender Labs Paul Henry Niall O'Sullivan Alex Weinert Wadeware LLC Microsoft Digital Crimes Unit Azure Active Directory Team Beth Jester Daryl Pecelj Terry Zink Windows Defender Microsoft IT Information -

The Application Usage and Risk Report an Analysis of End User Application Trends in the Enterprise
The Application Usage and Risk Report An Analysis of End User Application Trends in the Enterprise 8th Edition, December 2011 Palo Alto Networks 3300 Olcott Street Santa Clara, CA 94089 www.paloaltonetworks.com Table of Contents Executive Summary ........................................................................................................ 3 Demographics ............................................................................................................................................. 4 Social Networking Use Becomes More Active ................................................................ 5 Facebook Applications Bandwidth Consumption Triples .......................................................................... 5 Twitter Bandwidth Consumption Increases 7-Fold ................................................................................... 6 Some Perspective On Bandwidth Consumption .................................................................................... 7 Managing the Risks .................................................................................................................................... 7 Browser-based Filesharing: Work vs. Entertainment .................................................... 8 Infrastructure- or Productivity-Oriented Browser-based Filesharing ..................................................... 9 Entertainment Oriented Browser-based Filesharing .............................................................................. 10 Comparing Frequency and Volume of Use -

What the Floc?
Security Now! Transcript of Episode #811 Page 1 of 30 Transcript of Episode #811 What the FLoC? Description: This week we briefly, I promise, catch up with ProxyLogon news regarding Windows Defender and the Black Kingdom. We look at Firefox's next release which will be changing its Referer header policy for the better. We look at this week's most recent RCE disaster, a critical vulnerability in the open source MyBB forum software, and China's new CAID (China Anonymization ID). We then conclude by taking a good look at Google's plan to replace tracking with explicit recent browsing history profiling, which is probably the best way to understand FLoC (Federated Learning of Cohorts). And as a special bonus we almost certainly figure out why they named it something so awful. High quality (64 kbps) mp3 audio file URL: http://media.GRC.com/sn/SN-811.mp3 Quarter size (16 kbps) mp3 audio file URL: http://media.GRC.com/sn/sn-811-lq.mp3 SHOW TEASE: It's time for Security Now!. Steve Gibson is here. We've got a new fix for the Microsoft Exchange Server flaw. This one's automatic, thanks to Microsoft. We'll also take a look at some nice new features in Firefox 87. You can get it right now. And then, what the FLoC? We'll take a look at Google's proposal for replacing third-party cookies. Is it better? It's all coming up next on Security Now!. Leo Laporte: This is Security Now! with Steve Gibson, Episode 811, recorded Tuesday, March 23rd, 2021: What the FLoC? It's time for Security Now!, the show where we cover your privacy, your security, your safety online with this guy right here, Steve Gibson from GRC.com. -

Wechat About China's Tencent
We Build Connections QQ Weixin For Enterprises: For Users: For Tencent: • Access to vast user base • Always connected • Deepen user stickiness via broadened • Unified user log-in enables CRM and • Enjoy a wide range of integrated social product offerings targeted advertising entertainment and content offerings, built • Increase traffic conversion through • Online payment facilitates transactions upon IPs and tech innovations transactions and advertising • Integrate capabilities across different • Access to rich mix of services and • Tap into new opportunities as the products to facilitate digital upgrades, e.g., transact at fingertips economy digitizes Weixin, WeChat Work, Tencent Meeting WeChat about 2 China’s Tencent Chris Wheldon, co-Portfolio Manager of the Magellan High Conviction strategy, and Ryan Joyce, co-Head of Magellan’s Technology team, explain why Tencent is a high-quality business, why the strategy invested in the company recently, what risks the investment poses and why Tencent performed well during the pandemic’s Chris Wheldon Ryan Joyce initial stages. Tencent is one of the High Conviction Q1. strategy’s top five positions. Can you please tell us about the company? A: Tencent was founded in 1998 as a Chinese instant-messaging service and web portal named QQ and subsequently built itself into a PC-based social network similar to today’s Facebook. In 2011, Tencent launched the WeChat mobile app, now China’s leading social “WeChat’s 1.2 network and communications platform and core to the company’s billion users average success. WeChat’s 1.2 billion users average nearly 100 minutes per day, every day, on the app. -
Mobile Internet Business Models in China: Vertical Hierarchies, Horizontal Conglomerates, Or Business Groups?
BERKELEY ROUNDTABLE ON THE INTERNATIONAL ECONOMY BRIE Working Paper 2016-6 MOBILE INTERNET BUSINESS MODELS IN CHINA: VERTICAL HIERARCHIES, HORIZONTAL CONGLOMERATES, OR BUSINESS GROUPS? Kai Jia and Martin Kenney Mobile Internet Platform Business Models in China: Vertical Hierarchies, Horizontal Conglomerates, or Business Groups? July 27, 2016 Kai Jia Ph.D. Student Tsinghua University Beijing, China And Martin Kenney Community and Regional Development University of California, Davis [email protected] Acknowledgments: The authors thank Roger Bohn and John Zysman for helpful comments. The authors remain responsible for all remaining errors. 2 ABSTRACT The current understanding of the dynamics of digital platforms and strategy for their concomitant ecosystems has emerged from an analysis of firms in Western market economies. Our contribution arises from a detailed study of the business strategies of the current leaders in the Chinese mobile internet industry—Tencent, Alibaba, and Baidu. We find that they have developed business models significantly different from those of US firms. We argue that these Chinese firms are developing a “platform business group” strategy predicated upon horizontal expansion through organic growth, acquisition, and the purchase of significant equity positions in vertical industries, such as ride sharing, online-to-offline commerce, and travel. As a generalization, their western counterparts were much more oriented toward vertical expansion integrating either upwards or downwards in their respective software stacks. A central component of the business group is an online payment system that operates with its other platforms to cross-feed traffic and use internal cross-platform personal data to customize its offerings to users. We show that the different environmental conditions in China versus Western market economies allow firms there to pursue different business strategies. -

ESG CASE STUDY, Tencent
ESG CASE STUDY FEDERATED HERMES INTERNATIONAL GROWTH EQUITY TEAM Tencent A multinational consumer technology conglomerate Founded in 1998 89,228 employees Headquarters: Shenzhen, China Martin Schulz Hanah Chang Portfolio manager EOS engager How Federated Hermes’ International Growth Equity team incorporates ESG The Federated Hermes International Growth Equity team’s investment approach integrates top-down country allocation and bottom-up stock selection. Rather than focusing purely on short-term cyclical opportunities, our top-down country analysis recognizes the importance of how markets and investment performance may be impacted over time by variables such as economic growth, liquidity, currencies, regulatory issues, fiscal and monetary policy and overall market sentiment. Likewise, we concentrate on a company’s growth rate with the goal of identifying securities capable of delivering improving and sustainable earnings growth over the mid to long term. We take that same long-range view when it comes to integrating environmental, social and governance factors into our investment process. We incorporate ESG factors holistically as part of both our top-down and bottom-up analysis. Integrating analysis of ESG factors offers a complementary stream of information to identify opportunities and potential risks at the country and security level that may not ordinarily be uncovered with traditional fundamental analysis. Investment thesis: Tencent Since 2010, Tencent has grown earnings-per-share by more than 28% (compounded annual growth rate) and is a leader in accelerating future Although not a household name to many Americans, Tencent is a social growth areas noted earlier. Continuing to demonstrate resilient funda- networking, e-commerce, cloud computing, music, fi ntech, internet mentals, Tencent’s powerful brand, low production costs and diversifi ed services, artifi cial intelligence and multiplayer online gaming jugger- revenue sources have enabled it to survive—and even thrive—during naut—as well as one of the world’s leading venture capital fi rms. -
Tencent Kubernetes Engine API Documentation
Tencent Kubernetes Engine Tencent Kubernetes Engine API Documentation Product Documentation ©2013-2019 Tencent Cloud. All rights reserved. Page 1 of 350 Tencent Kubernetes Engine Copyright Notice ©2013-2019 Tencent Cloud. All rights reserved. Copyright in this document is exclusively owned by Tencent Cloud. You must not reproduce, modify, copy or distribute in any way, in whole or in part, the contents of this document without Tencent Cloud's the prior written consent. Trademark Notice All trademarks associated with Tencent Cloud and its services are owned by Tencent Cloud Computing (Beijing) Company Limited and its affiliated companies. Trademarks of third parties referred to in this document are owned by their respective proprietors. Service Statement This document is intended to provide users with general information about Tencent Cloud's products and services only and does not form part of Tencent Cloud's terms and conditions. Tencent Cloud's products or services are subject to change. Specific products and services and the standards applicable to them are exclusively provided for in Tencent Cloud's applicable terms and conditions. ©2013-2019 Tencent Cloud. All rights reserved. Page 2 of 350 Tencent Kubernetes Engine Contents API Documentation History Introduction API Category Making API Requests Request Structure Common Params Signature v3 Signature Responses Cluster APIs DescribeClusterKubeconfig DescribeClusters CreateCluster DescribeClusterSecurity DeleteCluster ModifyClusterEndpointSP DescribeClusterEndpointVipStatus DescribeClusterEndpointStatus -

PLATINUM Targeted Attacks in South and Southeast Asia
PLATINUM Targeted attacks in South and Southeast Asia Windows Defender Advanced Threat Hunting Team This document is for informational purposes only. MICROSOFT MAKES NO WARRANTIES, EXPRESS, IMPLIED, OR STATUTORY, AS TO THE INFORMATION IN THIS DOCUMENT. This document is provided “as-is.” Information and views expressed in this document, including URL and other Internet website references, may change without notice. You bear the risk of using it. Copyright © 2016 Microsoft Corporation. All rights reserved. The names of actual companies and products mentioned herein may be the trademarks of their respective owners. Table of contents PLATINUM: Targeted attacks in South and Southeast Asia........................................... 4 Adversary profile ............................................................................................................................ 4 Methods of attack .......................................................................................................................... 6 Technical details ............................................................................................................................. 11 Dipsind ................................................................................................................................................................................ 11 JPIN ..................................................................................................................................................................................... 15 adbupd .............................................................................................................................................................................. -

Tencent Cloud Comunication Solutions for China
Tencent Cloud Comunication Solutions for China 28.10.2020 © 2020 Tencent Cloud, LLC. All rights reserved. AGENDA • Tencent: “A Chinese Digital Dragon” • The Chinese opportunity • Who is Tencent? • Globalization strategy • Public Cloud • Cloud Communication Solutions • Tencent VooV Meeting • WeChat Work • Tencent Cloud Conference & Exhibition © 2020 Tencent Cloud, LLC. All rights reserved. - Tencent, “A Chinese Digital Dragon” 4 Founded in 1998 and headquartered in Tencent by the numbers: Shenzhen, Tencent is one of the largest • 550+ billion USD market capitalization** technology companies in the world and a global leader in messaging, social media, gaming, • 1.203+ billion monthly active Weixin/WeChat mobile payment, music streaming, digital users* literature, video and other digital content services. • 112 million video subscriptions* • #1 Mobile Payment in China by monthly active users and daily active users* • 62,000+ employees* *As of March 2020 **As of June 10, 2020 © 2020 Tencent Cloud, LLC. All rights reserved. Tencent - User Centric 360-Degree Ecosystem 6 TEG PCG IEG WXG CSIG CDG Technical Platform & Content Interactive Weixin (WeChat) Cloud & Smart Industries Corporate & Engineering Group Group Entertainment Group Group Group Development Group Tencent QQ Tencent Games WeChat Tencent Cloud Tencent Fintech Big Data Tencent YouTu QQ zone Tencent Tencent Tencent e-Sports Marketing WeChat Pay Transit QR Code AI Lab Tencent App Store Solution Tencent Maps WeiShi Timi Studio Tencent Security WeChat Work Platform Smart Retail Tencent News Lightspeed & Mr. Translator Tencent Quantum Studio QQ Mail Data Center QQ Browser Tencent Mobile Manager Tencent Animation Tencent PC Manager Aurora Studio WeRead Tencent Pictures Tencent Miying Next Studio Auto intelligence Penguin Pictures Mini Program Tencent HealthCare Tencent Video MOREFUN Official Tencent Autonomous Studio Account Driving Kuai Bao Tencent Classroom © 2020 Tencent Cloud, LLC. -
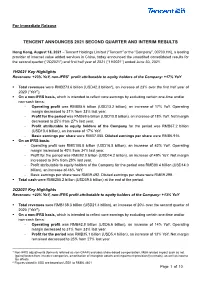
Tencent Announces 2021 Second Quarter and Interim Results
For Immediate Release TENCENT ANNOUNCES 2021 SECOND QUARTER AND INTERIM RESULTS Hong Kong, August 18, 2021 – Tencent Holdings Limited (“Tencent” or the “Company”, 00700.HK), a leading provider of Internet value added services in China, today announced the unaudited consolidated results for the second quarter (“2Q2021”) and first half year of 2021 (“1H2021”) ended June 30, 2021. 1H2021 Key Highlights Revenues: +23% YoY, non-IFRS1 profit attributable to equity holders of the Company: +17% YoY ▪ Total revenues were RMB273.6 billion (USD42.3 billion2), an increase of 23% over the first half year of 2020 (“YoY”). ▪ On a non-IFRS basis, which is intended to reflect core earnings by excluding certain one-time and/or non-cash items: - Operating profit was RMB85.6 billion (USD13.2 billion), an increase of 17% YoY. Operating margin decreased to 31% from 33% last year. - Profit for the period was RMB69.6 billion (USD10.8 billion), an increase of 18% YoY. Net margin decreased to 25% from 27% last year. - Profit attributable to equity holders of the Company for the period was RMB67.2 billion (USD10.4 billion), an increase of 17% YoY. - Basic earnings per share were RMB7.055. Diluted earnings per share were RMB6.916. ▪ On an IFRS basis: - Operating profit was RMB108.8 billion (USD16.8 billion), an increase of 42% YoY. Operating margin increased to 40% from 34% last year. - Profit for the period was RMB92.0 billion (USD14.2 billion), an increase of 49% YoY. Net margin increased to 34% from 28% last year. - Profit attributable to equity holders of the Company for the period was RMB90.4 billion (USD14.0 billion), an increase of 46% YoY. -

Free-Fall: Hacking Tesla from Wireless to Can Bus
FREE-FALL: HACKING TESLA FROM WIRELESS TO CAN BUS Sen Nie, Ling Liu, Yuefeng Du Keen Security Lab of Tencent {snie, dlingliu, davendu}@tencent.com ABSTRACT In today's world of connected cars, security is of vital importance. The security of these cars is not only a technological issue, but also an issue of human safety. In our research, we focused on perhaps the most famous connected car model: Tesla. In September 2016, our team (Keen Security Lab of Tencent) successfully implemented a remote attack on the Tesla Model S in both Parking and Driving mode. [1-3] This remote attack utilized a complex chain of vulnerabilities. We have proved that we can gain entrance from wireless (Wi-Fi/Cellular), compromise many in-vehicle systems like IC, CID, and Gateway, and then inject malicious CAN messages into the CAN Bus. Just 10 days after we submitted our research to Tesla, Tesla responded with an update using their OTA mechanism and introduced the code signing protection into Tesla cars. Our paper will be in three parts: our research, Tesla's response, and the follow-up. We will, for the first time, share the details of the whole attack chain on the Tesla, and then reveal the implementation of Tesla's OTA and Code Signing features. Furthermore, we'll explore the new mitigation on Tesla and share our thoughts on them. TARGET VERSION We have successfully tested our vulnerabilities on Tesla Model S P85 and P75, the latest version at that time was as follows. Version Model S gw:/firmware.rc (Build Number) P85 v7.1(2.28.60) fileCrc 502224ba P75 v7.1(2.32.23) fileCrc e3deeaab Table 1 Tested version REMOTE ATTACK SURFACE The truth is that we found our browser exploit first, then we think a contactless approach should be achieved. -

Live Video Broadcasting FAQ
FAQ Product Introduction Live Video Broadcasting FAQ Product Introduction ©2013-2018 Tencent Cloud. All rights reserved. Page 1 of 35 FAQ Product Introduction Copyright Notice ©2013-2018 Tencent Cloud. All rights reserved. Copyright in this document is exclusively owned by Tencent Cloud. You must not reproduce, modify, copy or distribute in any way, in whole or in part, the contents of this document without Tencent Cloud's the prior written consent. Trademark Notice All trademarks associated with Tencent Cloud and its services are owned by Tencent Cloud Computing (Beijing) Company Limited and its affiliated companies. Trademarks of third parties referred to in this document are owned by their respective proprietors. Service Statement This document is intended to provide users with general information about Tencent Cloud's products and services only and does not form part of Tencent Cloud's terms and conditions. Tencent Cloud's products or services are subject to change. Specific products and services and the standards applicable to them are exclusively provided for in Tencent Cloud's applicable terms and conditions. ©2013-2018 Tencent Cloud. All rights reserved. Page 2 of 35 FAQ Product Introduction Contents FAQ Basics of LVB Video Stutter Instant Broadcasting Reduce Latency Pushing Failure Watching LVB Failure Increase Definition Compatibility with Apple ATS Delete IDs of Channel Hosting Mode & LVB Code Access Mode Difference Between Stream Interruption and Stream Suspension ©2013-2018 Tencent Cloud. All rights reserved. Page 3 of 35 FAQ Product Introduction FAQ Basics of LVB Last updated:2018-07-24 16:09:24 1. What are Push, LVB and VOD? Push: This refers to the process in which VJs push local video and audio sources to Tencent Video Cloud servers.