Traffic Analysis Resistant Infrastructure
Total Page:16
File Type:pdf, Size:1020Kb
Load more
Recommended publications
-

Poster: Introducing Massbrowser: a Censorship Circumvention System Run by the Masses
Poster: Introducing MassBrowser: A Censorship Circumvention System Run by the Masses Milad Nasr∗, Anonymous∗, and Amir Houmansadr University of Massachusetts Amherst fmilad,[email protected] ∗Equal contribution Abstract—We will present a new censorship circumvention sys- side the censorship regions, which relay the Internet traffic tem, currently being developed in our group. The new system of the censored users. This includes systems like Tor, VPNs, is called MassBrowser, and combines several techniques from Psiphon, etc. Unfortunately, such circumvention systems are state-of-the-art censorship studies to design a hard-to-block, easily blocked by the censors by enumerating their limited practical censorship circumvention system. MassBrowser is a set of proxy server IP addresses [14]. (2) Costly to operate: one-hop proxy system where the proxies are volunteer Internet To resist proxy blocking by the censors, recent circumven- users in the free world. The power of MassBrowser comes from tion systems have started to deploy the proxies on shared-IP the large number of volunteer proxies who frequently change platforms such as CDNs, App Engines, and Cloud Storage, their IP addresses as the volunteer users move to different a technique broadly referred to as domain fronting [3]. networks. To get a large number of volunteer proxies, we This mechanism, however, is prohibitively expensive [11] provide the volunteers the control over how their computers to operate for large scales of users. (3) Poor QoS: Proxy- are used by the censored users. Particularly, the volunteer based circumvention systems like Tor and it’s variants suffer users can decide what websites they will proxy for censored from low quality of service (e.g., high latencies and low users, and how much bandwidth they will allocate. -

An ISP-Scale Deployment of Tapdance
An ISP-Scale Deployment of TapDance Sergey Frolov Fred Douglas Will Scott Eric Wustrow Google Allison McDonald University of Colorado Boulder Benjamin VanderSloot University of Michigan Rod Hynes Michalis Kallitsis David G. Robinson Adam Kruger Merit Network Upturn Psiphon Steve Schultze Nikita Borisov J. Alex Halderman Georgetown University Law University of Illinois University of Michigan Center ABSTRACT network operators, who provide censorship circumvention In this talk, we will report initial results from the world’s functionality for any connection that passes through their net- first ISP-scale field trial of a refraction networking system. works. To accomplish this, clients make HTTPS connections Refraction networking is a next-generation censorship cir- to sites that they can reach, where such connections traverse cumvention approach that locates proxy functionality in the a participating network. The participating network operator middle of the network, at participating ISPs or other network recognizes a steganographic signal from the client and ap- operators. We built a high-performance implementation of pends the user’s requested data to the encrypted connection the TapDance refraction networking scheme and deployed it response. From the perspective of the censor, these connec- on four ISP uplinks with an aggregate bandwidth of 100 Gbps. tions are indistinguishable from normal TLS connections to Over one week of operation, our deployment served more sites the censor has not blocked. To block the refraction con- than 50,000 real users. The experience demonstrates that nections, the censor would need to block all connections that TapDance can be practically realized at ISP scale with good traverse a participating network. -

Threat Modeling and Circumvention of Internet Censorship by David Fifield
Threat modeling and circumvention of Internet censorship By David Fifield A dissertation submitted in partial satisfaction of the requirements for the degree of Doctor of Philosophy in Computer Science in the Graduate Division of the University of California, Berkeley Committee in charge: Professor J.D. Tygar, Chair Professor Deirdre Mulligan Professor Vern Paxson Fall 2017 1 Abstract Threat modeling and circumvention of Internet censorship by David Fifield Doctor of Philosophy in Computer Science University of California, Berkeley Professor J.D. Tygar, Chair Research on Internet censorship is hampered by poor models of censor behavior. Censor models guide the development of circumvention systems, so it is important to get them right. A censor model should be understood not just as a set of capabilities|such as the ability to monitor network traffic—but as a set of priorities constrained by resource limitations. My research addresses the twin themes of modeling and circumvention. With a grounding in empirical research, I build up an abstract model of the circumvention problem and examine how to adapt it to concrete censorship challenges. I describe the results of experiments on censors that probe their strengths and weaknesses; specifically, on the subject of active probing to discover proxy servers, and on delays in their reaction to changes in circumvention. I present two circumvention designs: domain fronting, which derives its resistance to blocking from the censor's reluctance to block other useful services; and Snowflake, based on quickly changing peer-to-peer proxy servers. I hope to change the perception that the circumvention problem is a cat-and-mouse game that affords only incremental and temporary advancements. -

Enhancing System Transparency, Trust, and Privacy with Internet Measurement
Enhancing System Transparency, Trust, and Privacy with Internet Measurement by Benjamin VanderSloot A dissertation submitted in partial fulfillment of the requirements for the degree of Doctor of Philosophy (Computer Science and Engineering) in the University of Michigan 2020 Doctoral Committee: Professor J. Alex Halderman, Chair Assistant Professor Roya Ensafi Research Professor Peter Honeyman Assistant Professor Baris Kasikci Professor Kentaro Toyama Benjamin VanderSloot [email protected] ORCID iD: 0000-0001-6528-3927 © Benjamin VanderSloot 2020 ACKNOWLEDGEMENTS First and foremost, I thank my wife-to-be, Alexandra. Without her unwavering love and support, this dissertation would have remained unfinished. Without her help, the ideas here would not be as strong. Without her, I would not be here. Thanks are also due to my advisor, J. Alex Halderman, for giving me the independence and support I needed to find myself. I also thank Peter Honeyman for sharing his experience freely, both with history lessons and mentorship. Thank you Roya Ensafi, for watching out for me since we met. Thank you Baris Kasikci and Kentaro Toyama, for helping me out the door, in spite of the ongoing pandemic. I owe a great debt to my parents, Craig and Teresa VanderSloot, for raising me so well. No doubt the lessons about perseverance and hard work were put to good use. Your pride has been fuel to my fire for a very long time now. I also owe so much to my sister, Christine Kirbitz, for being the best example a little brother could hope for. I always had a great path to follow and an ear to share my problems with. -

BRKSEC-2011.Pdf
#CLUS About Garlic and Onions A little journey… Tobias Mayer, Technical Solutions Architect BRKSEC-2011 #CLUS Me… CCIE Security #14390, CISSP & Motorboat driving license… Working in Content Security & TLS Security tmayer{at}cisco.com Writing stuff at “blogs.cisco.com” #CLUS BRKSEC-2011 © 2018 Cisco and/or its affiliates. All rights reserved. Cisco Public 3 Agenda • Why anonymization? • Using Tor (Onion Routing) • How Tor works • Introduction to Onion Routing • Obfuscation within Tor • Domain Fronting • Detect Tor • I2P – Invisible Internet Project • Introduction to Garlic Routing • Conclusion #CLUS BRKSEC-2011 © 2018 Cisco and/or its affiliates. All rights reserved. Cisco Public 4 Cisco Webex Teams Questions? Use Cisco Webex Teams (formerly Cisco Spark) to chat with the speaker after the session How 1 Find this session in the Cisco Events App 2 Click “Join the Discussion” 3 Install Webex Teams or go directly to the team space 4 Enter messages/questions in the team space Webex Teams will be moderated cs.co/ciscolivebot#BRKSEC-2011 by the speaker until June 18, 2018. #CLUS © 2018 Cisco and/or its affiliates. All rights reserved. Cisco Public 5 Different Intentions Hide me from Government! Hide me from ISP! Hide me from tracking! Bypass Corporate Bypass Country Access Hidden policies restrictions (Videos…) Services #CLUS BRKSEC-2011 © 2018 Cisco and/or its affiliates. All rights reserved. Cisco Public 6 Browser Identity Tracking does not require a “Name” Tracking is done by examining parameters your browser reveals https://panopticlick.eff.org #CLUS BRKSEC-2011 © 2018 Cisco and/or its affiliates. All rights reserved. Cisco Public 7 Proxies EPIC Browser #CLUS BRKSEC-2011 © 2018 Cisco and/or its affiliates. -
People's Tech Movement to Kick Big Tech out of Africa Could Form a Critical Part of the Global Protests Against the Enduring Legacy of Racism and Colonialism
CONTENTS Acronyms ................................................................................................................................................ 1 1 Introduction: The Rise of Digital Colonialism and Surveillance Capitalism ..................... 2 2 Threat Modeling .......................................................................................................................... 8 3 The Basics of Information Security and Software ............................................................... 10 4 Mobile Phones: Talking and Texting ...................................................................................... 14 5 Web Browsing ............................................................................................................................ 18 6 Searching the Web .................................................................................................................... 23 7 Sharing Data Safely ................................................................................................................... 25 8 Email Encryption ....................................................................................................................... 28 9 Video Chat ................................................................................................................................... 31 10 Online Document Collaboration ............................................................................................ 34 11 Protecting Your Data ................................................................................................................ -

Blocking-Resistant Communication Through Domain Fronting
Proceedings on Privacy Enhancing Technologies 2015; 2015 (2):46–64 David Fifield*, Chang Lan, Rod Hynes, Percy Wegmann, and Vern Paxson Blocking-resistant communication through domain fronting Abstract: We describe “domain fronting,” a versatile 1 Introduction censorship circumvention technique that hides the re- mote endpoint of a communication. Domain fronting Censorship is a daily reality for many Internet users. works at the application layer, using HTTPS, to com- Workplaces, schools, and governments use technical and municate with a forbidden host while appearing to com- social means to prevent access to information by the net- municate with some other host, permitted by the cen- work users under their control. In response, those users sor. The key idea is the use of different domain names at employ technical and social means to gain access to the different layers of communication. One domain appears forbidden information. We have seen an ongoing conflict on the “outside” of an HTTPS request—in the DNS re- between censor and censored, with advances on both quest and TLS Server Name Indication—while another sides, more subtle evasion countered by more powerful domain appears on the “inside”—in the HTTP Host detection. header, invisible to the censor under HTTPS encryp- Circumventors, at a natural disadvantage because tion. A censor, unable to distinguish fronted and non- the censor controls the network, have a point working fronted traffic to a domain, must choose between allow- in their favor: the censor’s distaste for “collateral dam- ing circumvention traffic and blocking the domain en- age,” incidental overblocking committed in the course of tirely, which results in expensive collateral damage. -
Download Or Upload
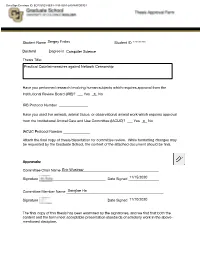
DocuSign Envelope ID: ECF321E3-5E94-4153-9254-2A048AFD03E4 Student Name ______________________________Sergey Frolov _______ Student ID___________________********* ___ Doctoral______________ Degree in ______________________________Computer Science _____________________________ Thesis Title: Practical Countermeasures against Network Censorship Have you performed research involving human subjects which requires approval from the Institutional Review Board (IRB)? ___ Yes ___X No IRB Protocol Number ________________ Have you used live animals, animal tissue, or observational animal work which requires approval from the Institutional Animal Care and Use Committee (IACUC)? ___ Yes ___X No IACUC Protocol Number _______________ Attach the final copy of thesis/dissertation for committee review. While formatting changes may be requested by the Graduate School, the content of the attached document should be final. Approvals: Committee Chair Name ______________________________________________________Eric Wustrow Signature _____________________________________ Date Signed _________________11/15/2020 Committee Member Name ______________________________________________________Sangtae Ha Signature _____________________________________ Date Signed _________________11/10/2020 The final copy of this thesis has been examined by the signatories, and we find that both the content and the form meet acceptable presentation standards of scholarly work in the above- mentioned discipline. DocuSign Envelope ID: ECF321E3-5E94-4153-9254-2A048AFD03E4 Practical Countermeasures -

Domain Shadowing: Leveraging Content Delivery Networks for Robust Blocking-Resistant Communications
Domain Shadowing: Leveraging Content Delivery Networks for Robust Blocking-Resistant Communications Mingkui Wei Cybersecurity Engineering George Mason University, Fairfax, VA, 22030 Abstract according to the Host header but have the TLS connection still appear to belong to the allowed domain. The blocking- We debut domain shadowing, a novel censorship evasion resistance of domain fronting derives from the significant technique leveraging content delivery networks (CDNs). Do- “collateral damage”, i.e., to disable domain fronting, the censor main shadowing exploits the fact that CDNs allow their cus- needs to block users from accessing the entire CDN, resulting tomers to claim arbitrary domains as the back-end. By set- in all domains on the CDN inaccessible. Because today’s ting the front-end of a CDN service as an allowed domain Internet relies heavily on web caches and many high-profile and the back-end a blocked one, a censored user can access websites also use CDNs to distribute their content, completely resources of the blocked domain with all “indicators”, includ- blocking access to a particular CDN may not be a feasible ing the connecting URL, the SNI of the TLS connection, and option for the censor. Because of its strong blocking-resistant the Host header of the HTTP(S) request, appear to belong power, domain fronting has been adopted by many censorship to the allowed domain. Furthermore, we demonstrate that evasion systems since it has been proposed [24, 28, 34, 36]. domain shadowing can be proliferated by domain fronting, In the last two years, however, many CDNs began to disable a censorship evasion technique popularly used a few years domain fronting by enforcing the match between the SNI and ago, making it even more difficult to block. -

Predictroute: a Network Path Prediction Toolkit
PredictRoute: A Network Path Prediction Toolkit RACHEE SINGH, University of Massachusetts, Amherst, USA DAVID TENCH, University of Massachusetts, Amherst, USA PHILLIPA GILL, University of Massachusetts, Amherst, USA ANDREW MCGREGOR, University of Massachusetts, Amherst, USA Accurate prediction of network paths between arbitrary hosts on the Internet is of vital importance for network operators, cloud providers, and academic researchers. We present PredictRoute, a system that predicts network paths between hosts on the Internet using historical knowledge of the data and control plane. In addition to feeding on freely available traceroutes and BGP routing tables, PredictRoute optimally explores network paths towards chosen BGP prefixes. PredictRoute’s strategy for exploring network paths discovers 4X more autonomous system (AS) hops than other well-known strategies used in practice today. Using a corpus of traceroutes, PredictRoute trains probabilistic models of routing towards prefixes on the Internet to predict network paths and their likelihood. PredictRoute’s AS-path predictions differ from the measured path byat most 1 hop, 75% of the time. We expose PredictRoute’s path prediction capability via a REST API to facilitate its inclusion in other applications and studies. We additionally demonstrate the utility of PredictRoute in improving real-world applications for circumventing Internet censorship and preserving anonymity online. CCS Concepts: • Mathematics of computing ! Paths and connectivity problems; Markov networks; • Net- works ! Routing protocols; Wide area networks; Public Internet. Additional Key Words and Phrases: network measurement; Internet path prediction ACM Reference Format: Rachee Singh, David Tench, Phillipa Gill, and Andrew McGregor. 2021. PredictRoute: A Network Path Prediction Toolkit . Proc. ACM Meas. Anal. Comput. Syst. -

By Israa Alsars
QATAR UNIVERSITY COLLEGE OF ENGINEERING [Free Chain: Enabling Freedom of Expression through Public Blockchains ] BY ISRAA ALSARSOUR A Thesis Submitted to the Faculty of the College of Engineering in Partial Fulfillment of the Requirements for the Degree of Masters of Science in Computing Masters of Science in Computing June 2021 © 2021 Israa Alsarsour. All Rights Reserved. COMMITTEE PAGE The members of the Committee approve the Thesis of Israa Alsarsour defended on 19/04/2021. Qutaiba M. Malluhi Thesis/Dissertation Supervisor Abdelaziz Bouras Committee Member Aiman Erbad Committee Member Devrim Unal Committee Member Approved: Khalifa Nasser Al-Khalifa, Dean, College of Engineering ii ABSTRACT ALSARSOUR, ISRAA SALEM, Masters : June :2021, Masters of Science in Computing Title: Free Chain: Enabling Freedom of Expression through Public Blockchains Supervisor of Thesis: Qutaibah M, Malluhi. Everyone should have the right to expression and opinion without interference. Nevertheless, Internet censorship is often misused to block freedom of speech. The distributed ledger technology provides a globally shared database geographically dispersed and cannot be controlled by a central authority. Blockchain is an emerging technology that enabled distributed ledgers and has recently been employed for building various types of applications. This thesis demonstrates a unique application of blockchain technologies to create a platform supporting freedom of expression. The thesis adopts permissionless and public blockchains to leverage their advantages of providing an on-chain immutable and tamper-proof publication medium. The study shows the blockchain potential for delivering a censorship-resistant publication platform. The thesis presents and evaluates possible methods for building such a system using the Bitcoin and Ethereum blockchain networks. -

The Use of TLS in Censorship Circumvention
The use of TLS in Censorship Circumvention Sergey Frolov Eric Wustrow University of Colorado Boulder University of Colorado Boulder [email protected] [email protected] Abstract—TLS, the Transport Layer Security protocol, has TLS [54], and adoption continues to grow as more websites, quickly become the most popular protocol on the Internet, already services, and applications switch to TLS. used to load over 70% of web pages in Mozilla Firefox. Due to its ubiquity, TLS is also a popular protocol for censorship Given the prevalence of TLS, it is commonly used by circumvention tools, including Tor and Signal, among others. circumvention tools to evade Internet censorship. Because However, the wide range of features supported in TLS makes censors can easily identify and block custom protocols [30], it possible to distinguish implementations from one another by circumvention tools have turned to using existing protocols. what set of cipher suites, elliptic curves, signature algorithms, and TLS offers a convenient choice for these tools, providing other extensions they support. Already, censors have used deep plenty of legitimate cover traffic from web browsers and packet inspection (DPI) to identify and block popular circumven- other TLS user, protection of content from eavesdroppers, and tion tools based on the fingerprint of their TLS implementation. several libraries to choose from that support it. In response, many circumvention tools have attempted to mimic popular TLS implementations such as browsers, but this However, simply using TLS for a transport protocol is technique has several challenges. First, it is burdensome to keep not enough to evade censors. Since TLS handshakes are not up with the rapidly-changing browser TLS implementations, and encrypted, censors can identify a client’s purported support for know what fingerprints would be good candidates to mimic.