Century Commons' Internet Use
Total Page:16
File Type:pdf, Size:1020Kb
Load more
Recommended publications
-

Uila Supported Apps
Uila Supported Applications and Protocols updated Oct 2020 Application/Protocol Name Full Description 01net.com 01net website, a French high-tech news site. 050 plus is a Japanese embedded smartphone application dedicated to 050 plus audio-conferencing. 0zz0.com 0zz0 is an online solution to store, send and share files 10050.net China Railcom group web portal. This protocol plug-in classifies the http traffic to the host 10086.cn. It also 10086.cn classifies the ssl traffic to the Common Name 10086.cn. 104.com Web site dedicated to job research. 1111.com.tw Website dedicated to job research in Taiwan. 114la.com Chinese web portal operated by YLMF Computer Technology Co. Chinese cloud storing system of the 115 website. It is operated by YLMF 115.com Computer Technology Co. 118114.cn Chinese booking and reservation portal. 11st.co.kr Korean shopping website 11st. It is operated by SK Planet Co. 1337x.org Bittorrent tracker search engine 139mail 139mail is a chinese webmail powered by China Mobile. 15min.lt Lithuanian news portal Chinese web portal 163. It is operated by NetEase, a company which 163.com pioneered the development of Internet in China. 17173.com Website distributing Chinese games. 17u.com Chinese online travel booking website. 20 minutes is a free, daily newspaper available in France, Spain and 20minutes Switzerland. This plugin classifies websites. 24h.com.vn Vietnamese news portal 24ora.com Aruban news portal 24sata.hr Croatian news portal 24SevenOffice 24SevenOffice is a web-based Enterprise resource planning (ERP) systems. 24ur.com Slovenian news portal 2ch.net Japanese adult videos web site 2Shared 2shared is an online space for sharing and storage. -

Cisco SCA BB Protocol Reference Guide
Cisco Service Control Application for Broadband Protocol Reference Guide Protocol Pack #60 August 02, 2018 Cisco Systems, Inc. www.cisco.com Cisco has more than 200 offices worldwide. Addresses, phone numbers, and fax numbers are listed on the Cisco website at www.cisco.com/go/offices. THE SPECIFICATIONS AND INFORMATION REGARDING THE PRODUCTS IN THIS MANUAL ARE SUBJECT TO CHANGE WITHOUT NOTICE. ALL STATEMENTS, INFORMATION, AND RECOMMENDATIONS IN THIS MANUAL ARE BELIEVED TO BE ACCURATE BUT ARE PRESENTED WITHOUT WARRANTY OF ANY KIND, EXPRESS OR IMPLIED. USERS MUST TAKE FULL RESPONSIBILITY FOR THEIR APPLICATION OF ANY PRODUCTS. THE SOFTWARE LICENSE AND LIMITED WARRANTY FOR THE ACCOMPANYING PRODUCT ARE SET FORTH IN THE INFORMATION PACKET THAT SHIPPED WITH THE PRODUCT AND ARE INCORPORATED HEREIN BY THIS REFERENCE. IF YOU ARE UNABLE TO LOCATE THE SOFTWARE LICENSE OR LIMITED WARRANTY, CONTACT YOUR CISCO REPRESENTATIVE FOR A COPY. The Cisco implementation of TCP header compression is an adaptation of a program developed by the University of California, Berkeley (UCB) as part of UCB’s public domain version of the UNIX operating system. All rights reserved. Copyright © 1981, Regents of the University of California. NOTWITHSTANDING ANY OTHER WARRANTY HEREIN, ALL DOCUMENT FILES AND SOFTWARE OF THESE SUPPLIERS ARE PROVIDED “AS IS” WITH ALL FAULTS. CISCO AND THE ABOVE-NAMED SUPPLIERS DISCLAIM ALL WARRANTIES, EXPRESSED OR IMPLIED, INCLUDING, WITHOUT LIMITATION, THOSE OF MERCHANTABILITY, FITNESS FOR A PARTICULAR PURPOSE AND NONINFRINGEMENT OR ARISING FROM A COURSE OF DEALING, USAGE, OR TRADE PRACTICE. IN NO EVENT SHALL CISCO OR ITS SUPPLIERS BE LIABLE FOR ANY INDIRECT, SPECIAL, CONSEQUENTIAL, OR INCIDENTAL DAMAGES, INCLUDING, WITHOUT LIMITATION, LOST PROFITS OR LOSS OR DAMAGE TO DATA ARISING OUT OF THE USE OR INABILITY TO USE THIS MANUAL, EVEN IF CISCO OR ITS SUPPLIERS HAVE BEEN ADVISED OF THE POSSIBILITY OF SUCH DAMAGES. -

Vysoké Učení Technické V Brně Detekcia Seedboxov V Sieti Bittorrent
VYSOKÉ UČENÍ TECHNICKÉ V BRNĚ BRNO UNIVERSITY OF TECHNOLOGY FAKULTA INFORMAČNÍCH TECHNOLOGIÍ FACULTY OF INFORMATION TECHNOLOGY ÚSTAV INFORMAČNÍCH SYSTÉMŮ DEPARTMENT OF INFORMATION SYSTEMS DETEKCIA SEEDBOXOV V SIETI BITTORRENT DETECTION OF SEEDBOXES INBITTORRENT NETWORK BAKALÁŘSKÁ PRÁCE BACHELOR’S THESIS AUTOR PRÁCE MARTIN GRNÁČ AUTHOR VEDOUCÍ PRÁCE Ing. LIBOR POLČÁK, Ph.D. SUPERVISOR BRNO 2018 Abstrakt Bakalárska práca sa venuje problematike sledovania a detekcie seedboxov v sieti BitTorrent za pomoci technológie netflow. V teoretickej časti je predstavená a popísaná architektúra P2P, základy a kľúčové pojmy architektúry BitTorrent a teoretická definícia seedboxu. Taktiež sú tu rozobrané metódy pomocou ktorých sa dá detekovať sieťová komunikácia a ďalej je uvedená analýza seedboxov v sieti a hľadanie ich charakteristík. Na základe týchto znalostí a sledovaní je navrhnutá sada nástrojov, ktoré napomáhajú ich detekcií. V praktickej časti je predstavená implementácia týchto nástrojov a výsledky ich testovania. Abstract Bachelor’s thesis is focused on issues with monitoring and detection of seedboxes in Bit- Torrent network with help of netflow technology. In the theoretical part of this thesis is introduced and described P2P architecture, basics and key terms of BitTorrent architec- ture and theoretical definition of seedbox. There are also described specific methods which can be used for detection of network communication and next there is described process of seedbox analysis in network and process of finding its characteristics. On base of this kno- wledge and observations is designed a set of tools,which help with detection of seedboxes. In the practical part of this work is presented implementation of these tools and results of testing these tools. Kľúčové slová BitTorrent, seedbox, detekcia, netflow, analýza, sieťová prevádzka, P2P, netflow Keywords BitTorrent, seedbox, detection, netflow, analysis, network traffic, P2P, netflow Citácia GRNÁČ, Martin. -

The Application Usage and Risk Report an Analysis of End User Application Trends in the Enterprise
The Application Usage and Risk Report An Analysis of End User Application Trends in the Enterprise 8th Edition, December 2011 Palo Alto Networks 3300 Olcott Street Santa Clara, CA 94089 www.paloaltonetworks.com Table of Contents Executive Summary ........................................................................................................ 3 Demographics ............................................................................................................................................. 4 Social Networking Use Becomes More Active ................................................................ 5 Facebook Applications Bandwidth Consumption Triples .......................................................................... 5 Twitter Bandwidth Consumption Increases 7-Fold ................................................................................... 6 Some Perspective On Bandwidth Consumption .................................................................................... 7 Managing the Risks .................................................................................................................................... 7 Browser-based Filesharing: Work vs. Entertainment .................................................... 8 Infrastructure- or Productivity-Oriented Browser-based Filesharing ..................................................... 9 Entertainment Oriented Browser-based Filesharing .............................................................................. 10 Comparing Frequency and Volume of Use -
Dakota Wesleyan University Community Code
Community Code Student Handbook Learning, leadership, faith and service Dakota Wesleyan University Community Code The Dakota Wesleyan University Community Code contains information regarding activities, services, regulations and policies that are important to Dakota Wesleyan University students. The student handbook is not intended to cover every situation that could occur at Dakota Wesleyan University. Anything that is not covered will be dealt with on a case-by-case basis. Additional information is provided in the Dakota Wesleyan University Catalog. Policies contained within this book are reviewed each year at the conclusion of the academic year. Dakota Wesleyan University reserves the right to change policies, fees, schedules and other regulations affecting students when necessary. For more information, call student life at 605-995-2960 or e-mail [email protected]. DWU provides an environment that supports the teaching/learning mission of the university. Living and learning on our campus is designed to provide a combination of support and independence and a general education that helps to develop an understanding and appreciation of life in a democratic society. Campus living also promotes student development in cooperation, leadership and other personal attributes. Why are you a DWU student? You will have your own answer to this question. Whether you hope to receive a stimulating academic challenge, find a career, meet new friends or enjoy the campus environment, it is important that you identity your goals and expectations in order to receive full benefit of your Wesleyan experience. There are reasons for attending college that may not be clear to you until years after your graduation. -

NBAR2 Standard Protocol Pack 1.0
NBAR2 Standard Protocol Pack 1.0 Americas Headquarters Cisco Systems, Inc. 170 West Tasman Drive San Jose, CA 95134-1706 USA http://www.cisco.com Tel: 408 526-4000 800 553-NETS (6387) Fax: 408 527-0883 © 2013 Cisco Systems, Inc. All rights reserved. CONTENTS CHAPTER 1 Release Notes for NBAR2 Standard Protocol Pack 1.0 1 CHAPTER 2 BGP 3 BITTORRENT 6 CITRIX 7 DHCP 8 DIRECTCONNECT 9 DNS 10 EDONKEY 11 EGP 12 EIGRP 13 EXCHANGE 14 FASTTRACK 15 FINGER 16 FTP 17 GNUTELLA 18 GOPHER 19 GRE 20 H323 21 HTTP 22 ICMP 23 IMAP 24 IPINIP 25 IPV6-ICMP 26 IRC 27 KAZAA2 28 KERBEROS 29 L2TP 30 NBAR2 Standard Protocol Pack 1.0 iii Contents LDAP 31 MGCP 32 NETBIOS 33 NETSHOW 34 NFS 35 NNTP 36 NOTES 37 NTP 38 OSPF 39 POP3 40 PPTP 41 PRINTER 42 RIP 43 RTCP 44 RTP 45 RTSP 46 SAP 47 SECURE-FTP 48 SECURE-HTTP 49 SECURE-IMAP 50 SECURE-IRC 51 SECURE-LDAP 52 SECURE-NNTP 53 SECURE-POP3 54 SECURE-TELNET 55 SIP 56 SKINNY 57 SKYPE 58 SMTP 59 SNMP 60 SOCKS 61 SQLNET 62 SQLSERVER 63 SSH 64 STREAMWORK 65 NBAR2 Standard Protocol Pack 1.0 iv Contents SUNRPC 66 SYSLOG 67 TELNET 68 TFTP 69 VDOLIVE 70 WINMX 71 NBAR2 Standard Protocol Pack 1.0 v Contents NBAR2 Standard Protocol Pack 1.0 vi CHAPTER 1 Release Notes for NBAR2 Standard Protocol Pack 1.0 NBAR2 Standard Protocol Pack Overview The Network Based Application Recognition (NBAR2) Standard Protocol Pack 1.0 is provided as the base protocol pack with an unlicensed Cisco image on a device. -

Copyright Infringement (DMCA)
Copyright Infringement (DMCA) Why it is important to understand the DMCA: Kent State University (KSU) is receiving more and more copyright infringement notices every semester, risking the loss of ‘safe harbor’ status. Resident students, KSU faculty, staff, and student employees, and the University itself could be at risk of costly litigation, expensive fines, damage to reputation, and possible jail time. What you need to know about KSU’s role: ● KSU is not a policing organization. ● KSU does not actively monitor computing behavior. ● KSU reacts to infringement notices generated by agents of the copyright holders ● KSU expends a significant amount of time/money protecting the identity of students by maintaining ‘safe harbor’ status KSU is ‘the good guy’ – we’re focused on educating our community What you need to know if your student receives a copyright infringement notice: They were identified as using P2P software and illegally sharing copyrighted material (whether downloading to their computer or allowing others to download from their computer). They will be informed of the notice via email, and their network connection to external resources (sites outside of KSU) will be disabled to maintain ‘safe harbor’ status until such time as they have complied with the University’s requirements under the DMCA. They can face sanctions ranging from blocked connectivity to dismissal from the University. Definition of terms: DMCA: The Digital Millennium Copyright Act of 1998 was signed into law in the United States to protect the intellectual property rights of copyright holders of electronic media (music, movies, software, games, etc.). The DMCA allows KSU to operate as an OSP. -

The Copyright Crusade
The Copyright Crusade Abstract During the winter and spring of 2001, the author, chief technology officer in Viant's media and entertainment practice, led an extensive inqUiry to assess the potential impact of extant Internet file-sharing capabilities on the business models of copyright owners and holders. During the course of this project he and his associates explored the tensions that exist or may soon exist among peer-to-peer start-ups, "pirates" and "hackers," intellectual property companies, established media channels, and unwitting consumers caught in the middle. This research report gives the context for the battleground that has emerged, and calls upon the players to consider new, productive solutions and business models that support profitable, legal access to intellectual property via digital media. by Andrew C Frank. eTO [email protected] Viant Media and Entertainment Reinhold Bel/tIer [email protected] Aaron Markham [email protected] assisted by Bmre Forest ~ VI ANT 1 Call to Arms Well before the Internet. it was known that PCs connected to two-way public networks posed a problem for copyright holders. The problem first came to light when the Software Publishers Association (now the Software & Information Industry Association), with the backing of Microsoft and others, took on computer Bulletin Board System (BBS) operators in the late 1980s for facilitating trade in copyrighted computer software, making examples of "sysops" (as system operators were then known) by assisting the FBI in orchestrat ing raids on their homes. and taking similar legal action against institutional piracy in high profile U.S. businesses and universities.' At the same time. -
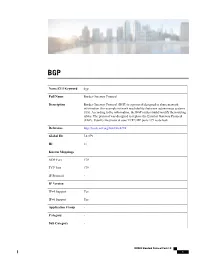
Bgp Name/CLI Keyword Border Gateway Protocol Full Name Border
BGP Name/CLI Keyword bgp Full Name Border Gateway Protocol Description Border Gateway Protocol (BGP) is a protocol designed to share network information (for example network reachability) between autonomous systems (AS). According to the information, the BGP routers build/modify their routing tables. The protocol was designed to replace the Exterior Gateway Protocol (EGP). Usually the protocol uses TCP/UDP ports 179 as default. Reference http://tools.ietf.org/html/rfc4274 Global ID L4:179 ID 11 Known Mappings UDP Port 179 TCP Port 179 IP Protocol - IP Version IPv4 Support Yes IPv6 Support Yes Application Group - Category - Sub Category - NBAR2 Standard Protocol Pack 1.0 1 BGP P2P Technology No Encrypted No Tunnel No Underlying Protocols - • BITTORRENT, page 4 • CITRIX, page 5 • DHCP, page 6 • DIRECTCONNECT, page 7 • DNS, page 8 • EDONKEY, page 9 • EGP, page 10 • EIGRP, page 11 • EXCHANGE, page 12 • FASTTRACK, page 13 • FINGER, page 14 • FTP, page 15 • GNUTELLA, page 16 • GOPHER, page 17 • GRE, page 18 • H323, page 19 • HTTP, page 20 • ICMP, page 21 • IMAP, page 22 • IPINIP, page 23 • IPV6-ICMP, page 24 • IRC, page 25 • KAZAA2, page 26 • KERBEROS, page 27 • L2TP, page 28 • LDAP, page 29 • MGCP, page 30 NBAR2 Standard Protocol Pack 1.0 2 BGP • NETBIOS, page 31 • NETSHOW, page 32 • NFS, page 33 • NNTP, page 34 • NOTES, page 35 • NTP, page 36 • OSPF, page 37 • POP3, page 38 • PPTP, page 39 • PRINTER, page 40 • RIP, page 41 • RTCP, page 42 • RTP, page 43 • RTSP, page 44 • SAP, page 45 • SECURE-FTP, page 46 • SECURE-HTTP, page 47 • SECURE-IMAP, -

Ellsworth Public Schools Student Handbook
Ellsworth School “Home of the Panthers” School Year 2020-2021 513 South Broadway Street Ellsworth, MN. 56129 Telephone: 507-967-2242 Table of Contents School Calendar Page 3 Welcome/Mission and Vision Statement/About our District Page 4 Professional Staff Page 5 Attendance Rules and Regulations Page 6 Nobles County Attendance Program Page 7 Technology Rules and Procedures Page 10 District Internet Policy Page 10 Student Technology Page 12 Chromebook Policy Page 13 Discipline Page 15 General Rules of Behavior Page 15 Infraction Levels Page 17 ISS/OSS/Expulsion Page 18 Academic and School Policies Page 19 Locker/Vehicle/Personal Searches and Monitoring Page 19 Academic Honesty Page 19 Grading Scale and Honor Roles/Make-Up Work/Open Campus Page 20 Study Halls/ExtraCurricular Fees/Student Driving/Sportsmanship Page 21 Free and Reduced Lunch/Activity Tickets Page 22 School closings/Academic Assistance Program/PSEO Page 23 Transportation Page 24 Bus Rules and Regulations Page 24 Student Health and Safety Page 27 Safety Drills/Safety Equipment Page 27 Medication Policy/Health Records/Immunizations Page 28 1 Ellsworth District #514 Policies Page 29 Equal Opportunity/Nondiscrimination/Harassment Page 29 Bullying Prohibition Page 30 Protection and Privacy or Student Records/Medication/Disability Page 31 Student Sex Nondiscrimination/Internet Use/Hazing Prohibition Page 32 Pledge of Allegiance/Peace Officer and Crisis Team/Wellness Page 33 Parental Involvement for Title 1/Curriculum and Instruction Goals Page 34 Agreement Form Page 35 Bus Transportation -
ELFIQ APP OPTIMIZER White Paper V1.03 - May 2015 CONTENTS Introduction
ELFIQ APP OPTIMIZER White Paper V1.03 - May 2015 CONTENTS Introduction ...............................................................................................................................................................................3 Signature-Based Recognition vs. ACL’s ................................................................................................................3 Detection Engine ...................................................................................................................................................................3 Using Groups or Individual Applications .............................................................................................................3 Actions Once an Application is Detected ...........................................................................................................3 Appendix A: Application List ........................................................................................................................................ 4 martellotech.com elfiq.com 2 INTRODUCTION The Elfiq AppOptimizer is designed to give organizations full control over their existing and future bandwidth, guaranteeing key applications such as Citrix XenDesktop or Skype get priority treatment and undesirables such as peer-to-peer file transfers or games are limited or no longer permitted. It is an add-on-module that provides application-layer deep packet inspection (layer 7) classification and control, including Mobile, Social Networking, P2P, Instant Messaging, -

Criminal Indictment in International, Internet-Based Child Pornography
UNITED STATES DISTRICT COURT NORTHERN DISTRICT OF ILLINOIS EASTERN DIVISION UNITED STATES OF AMERICA ) No. 06 CR 33 ) v. ) ) BRIAN A. ANNORENO, ) Violations: Title 18, also known as “Acidburn,” ) United States Code, GREGORY J. SWEEZER, ) Sections 371, 2251(a), 2252A(a)(1), also known as “Behrplus_925,” ) 2252A(a)(2)(A), and 2252A(a)(5)(B) LISA A. WINEBRENNER, ) also known as “HumbleDuchess” ) COUNT ONE The SPECIAL FEBRUARY 2005-1 GRAND JURY charges: 1. At times material to the indictment: a. “Kiddypics & Kiddyvids” was the name of an Internet chat room that existed for the purpose of facilitating the trading of child pornography. b. The “Kiddypics & Kiddyvids” chat room (hereinafter “the chat room”) was hosted on the Internet through the software program WinMX. The WinMX program provided to individuals who entered the chat room the ability to engage in online conversations, or “chats.” Although participants could enter the chat room from computers in locations around the world, all chat communications traveled through one “host” computer. c. The WinMX program also allowed for “peer-to-peer” file sharing, by which individuals participating in the chat room could select files from their personal computers and make those files available for other individuals in the chat room to directly download. Individuals in the chat room could use the “peer-to-peer” aspect of the WinMX program to make available to other members of the chat room selected visual image files. d. Individuals communicating in the chat room chose “screen names” upon entering the chat room. When an individual posted a message in the chat room, the individual’s screen name would precede the posted message.