11/10/2010 1 9 Data Link Protocols A. Asynchronous and Synchronous
Total Page:16
File Type:pdf, Size:1020Kb
Load more
Recommended publications
-

Macwise Version 19 User's Manual
[email protected] www.CarnationSoftware.com www.MacWise.com MacWise Version 19 User's Manual You can use Command F to find what you are looking for in this document. Introduction Terminal Emulation MacWise emulates ADDS Viewpoint, Wyse 50, Wyse 60, Wyse 370, Televideo TV 925, DEC VT100, VT220 and Prism terminals. Supports ANSI color. Esprit III color is also supported in Wyse 370 mode. MacWise allows a Macintosh to be used as a terminal -- connected to a host computer directly, by modem, or over the Internet. The emulators support video attributes such as dim, reverse, underline, 132-column modes, protected fields and graphic characters sent from the host computer, as well as enhanced Viewpoint mode. Features include phone list and dialer for modems, on-screen programmable function keys, connection scripts and more. Connectivity 1. Built in Modem 2. Telnet / TCP/IP 3. SSH Secure Shell 4. Serial ports via USB to Serial adaptor . 5. Also communicates directly with the Mac unix shell Telnet Telnet settings are under the Connection Menu. Select "Telnet" to enable telnet. Select "Telnet Connection..." to enter your Host IP address, port number and terminal type. =============================== KERMIT ================================ NOTE: If you are running Mac OS 10.13 or later, you need to also use Kermit. (There should be a check mark on "Kermit" under the Connection Menu.) Kermit is installed automatically when Mac OS 10.13 or later is detected. You can re-install kermit any time by selecting Kermit Installer from the Help Menu in MacWise. Echo Kermit Characters ( under the Connection Menu ) This is normally enabled when Kermit is enabled. -

Data Networks
Second Ed ition Data Networks DIMITRI BERTSEKAS Massachusetts Institute of Technology ROBERT GALLAGER Massachusetts Institute ofTechnology PRENTICE HALL, Englewood Cliffs, New Jersey 07632 2 Node A Node B Time at B --------- Packet 0 Point-to-Point Protocols and Links 2.1 INTRODUCTION This chapter first provides an introduction to the physical communication links that constitute the building blocks of data networks. The major focus of the chapter is then data link control (i.e., the point-to-point protocols needed to control the passage of data over a communication link). Finally, a number of point-to-point protocols at the network, transport, and physical layers are discussed. There are many similarities between the point-to-point protocols at these different layers, and it is desirable to discuss them together before addressing the more complex network-wide protocols for routing, flow control, and multiaccess control. The treatment of physical links in Section 2.2 is a brief introduction to a very large topic. The reason for the brevity is not that the subject lacks importance or inherent interest, but rather, that a thorough understanding requires a background in linear system theory, random processes, and modem communication theory. In this section we pro vide a sufficient overview for those lacking this background and provide a review and perspective for those with more background. 37 38 Point-to-Point Protocols and Links Chap. 2 In dealing with the physical layer in Section 2.2, we discuss both the actual com munication channels used by the network and whatever interface modules are required at the ends of the channels to transmit and receive digital data (see Fig 2.1). -
A Kermit File Transfer Protocol for the Apple II Series Personal Computers : John Patrick Francisco Lehigh University
Lehigh University Lehigh Preserve Theses and Dissertations 1986 A Kermit file transfer protocol for the Apple II series personal computers : John Patrick Francisco Lehigh University Follow this and additional works at: https://preserve.lehigh.edu/etd Part of the Electrical and Computer Engineering Commons Recommended Citation Francisco, John Patrick, "A Kermit file transfer protocol for the Apple II series personal computers :" (1986). Theses and Dissertations. 4628. https://preserve.lehigh.edu/etd/4628 This Thesis is brought to you for free and open access by Lehigh Preserve. It has been accepted for inclusion in Theses and Dissertations by an authorized administrator of Lehigh Preserve. For more information, please contact [email protected]. A KERMIT FILE TRANSFER PROTOCOL FOR THE APPLE II SERIES PERSONAL COMPUTERS (Using the Apple Pascal Operating system) by John Patrick Francisco A Thesis Presented to the Graduate Committee of Lehigh University in Candidacy for the Degree of Master of Science 1n• Computer Science Lehigh University March 1986 This thesis is accepted and approved in partial fulfillment of the requirements for the degree of Master of science.• (date) Professor in Charge -------------- --------------- Chairman of the Division Chairman of the Department • • -11- ACKNOWLEDGEMENTS It would be somewhat of an understatement to say this project was broad in scope as the disciplines involved ranged from Phychology to Electrical Engineering. Since the project required an extensive amount of detailed in formation in all fields, I was impelled to seek the help, advice and opinion of many. There were also numerous t friends and relatives upon whom I relied for both moral and financial support. -

Altair CP/M 2.2AT Ver 1.1 IOBYTE Implementation
Altair CP/M 2.2AT Ver 1.1 CP/M 2.2AT supports an Altair 8800 computer with both an Altair and Tarbell floppy controller installed. Drives A & B are Altair drives 0 & 1. Drives C & D are Tarbell drives 0 & 1. The boot drive is always Altair drive 0. The Altair controller can be either the 8" or the 5.25" (mini-disk) controller as selected by conditional assembly. The BIOS uses track buffering to improve disk performance. Compared to a non-buffered BIOS, perfor- mance of program with substantial disk I/O improves by 25% to 75%. For the Altair drives, the same disk layout used by the original versions of Altair CP/M 1.4 and 2.2 is used. For the Tarbell controller, the standard IBM SSSD soft-sectored format is used. This BIOS provides full IOBYTE support to allow use of a variety of standard Altair I/O boards. See IOBYTE below. During cold boot, the BIOS looks for a Teletype on the console port and if detected (based on baud rate), subsequently follows any CR to the console device with a NULL to give the Teletype carriage time to reach the left margin. The send null flag (SNDNULL) is located immediately following the MODE and IOBYTE in memory so it can be over-ridden if needed. This BIOS adds a disk select timeout for the Altair 8" floppy so if a non-present or empty drive is select- ed, it will eventually timeout. To still allow the operator time to insert a disk, close the door, and wait for the drive enable one-shot to expire, the default timeout is set to seven seconds. -

The Kermit File Transfer Protocol
THE KERMIT FILE TRANSFER PROTOCOL Frank da Cruz February 1985 This is the original manuscript of the Digital Press book Kermit, A File Transfer Protocol, ISBN 0-932976-88-6, Copyright 1987, written in 1985 and in print from 1986 until 2001. This PDF file was produced by running the original Scribe markup-language source files through the Scribe publishing package, which still existed on an old Sun Solaris computer that was about to be shut off at the end of February 2016, and then converting the resulting PostScript version to PDF. Neither PostScript nor PDF existed in 1985, so this result is a near miracle, especially since the last time this book was "scribed" was on a DECSYSTEM-20 for a Xerox 9700 laser printer (one of the first). Some of the tables are messed up, some of the source code comes out in the wrong font; there's not much I can do about that. Also (unavoidably) the page numbering is different from the printed book and of couse the artwork is missing. Bear in mind Kermit protocol and software have seen over 30 years of progress and development since this book was written. All information herein regarding the Kermit Project, how to get Kermit software, or its license or status, etc, is no longer valid. The Kermit Project at Columbia University survived until 2011 but now it's gone and all Kermit software was converted to Open Source at that time. For current information, please visit the New Open Source Kermit Project website at http://www.kermitproject.org (as long as it lasts). -

High-Level Data Link Control
ELEC3030 (EL336) Computer Networks S Chen High-Level Data Link Control • This class of data link layer protocols includes High-level Data Link Control (HDLC), Link Access Procedure Balanced (LAPB) for X.25, Link Access Procedure for D-channel (LAPD) for ISDN, and Logic Link Control (LLC) for FDDI • The frame format is: Flag Address Control Data FCS Flag Note that address and control bits 8 8 8 variable 16 8 can be extended to 16 bits, so bit position 12 3 4 5 6 7 8 N(S)=send sequence number N(R)=receive sequence number that sequence number is 7-bit Information: 0 N(S) P/F N(R) S=supervisory function bits P/F • Frame flag: 01111110, so bit Supervisory: 1 0 S N(R) M=unumbered function bits stuffing is used Unumbered: 1 1 M P/F M P/F=poll/final bit • Address: For multipoint operation, it is used to identify the terminal that transmits or receives the frame and, in point-to-point link, it is used to distinguish Commands from Responses (2nd bit for C/R: 0/1). The address is now extended to 16 bits (1st bit indicates long/short 16/8 bits) • Checksum: FCS contains the remainder of a 16-bit CRC calculation of the frame. It may be extended to 32 bits, using a 32-bit CRC • Control: Three types of frames, I, S and U frames. The old protocol uses a sliding window with 3-bit sequence number and the maximum window size is N = 7. The control field is now extended to 16 bits with 7-bit sequence number 60 ELEC3030 (EL336) Computer Networks S Chen HDLC (continue) • I-frames: carry user data. -

International Civil Aviation Organization
Guidance for the Implementation of National IP Networks INTERNATIONAL CIVIL AVIATION ORGANIZATION PROJECT RLA/06/901 GUIDANCE FOR THE IMPLEMENTATION OF NATIONAL DIGITAL NETWORKS THAT USE THE IP PROTOCOL, TO SUPPORT CURRENT AND FUTURE AERONAUTICAL APPLICATIONS Project RLA/06/901 Page 1 Guidance for the Implementation of National IP Networks The designations employed and the presentation of material in this publication do not imply the expression of any opinion whatsoever on the part of ICAO concerning the legal status of any country, territory, city or area or of its authorities, or concerning the delimination of its frontiers or boundaries. Project RLA/06/901 Page 2 Guidance for the Implementation of National IP Networks TABLE OF CONTENTS i. Table of Contents..................................................................................................................... 3 ii. Background.............................................................................................................................. 4 General Decision-Making Considerations ............................................................................... 5 Business ......................................................................................................................... 5 Industrial Support........................................................................................................... 5 Security Policies............................................................................................................. 5 Implementation ............................................................................................................. -
March-April 1992 23 Lsi
HE NSIDE TORIES Breaking the rules Teamwork, including a "Vulcan mind-meld," produced amazing results on a new family of HP computers. Passing the test Ned Barnholt, vice president and general manager of the Test and Measurement Organization, talks about the unfolding T&M revolution, page 6 Three parts, one whole 11 Chinese people in Hong Kong, Taipei and Bejing talk openly about a day when they'll be part of one vast, reunited country. Ifyou print them, they will come 14 We asked for your photos and (whew!) did you send them-more than 100 in all. Some of the best are included in this photo feature. Play it again, Len 18 HP Labs' Len Cutler gave up a promising musical career to be<.:ome the father ofthe world-famous HP atomic clock. Your Turn 21 page 22 It's another world 22 What has 75 countries, 60 currencies and is one of the most volatile parts of the world? HP's International Sales Branch. Letter from John Young 26 , .~ . .... ~ . ~ ExtraMeasure 28 ,. M.~.- .. r··'. m~ MEASURE ; lS ~ .' \\; . :'! Editor: Associa1e edilOfs: Graphic designer: Circulation: ., ." ... ., \. .' • Jay Coleman' Cornelio Bayley Thorncs J Brown Tricia Neal Chan On the cover: Jianhua Qi,- a BeHy Gerord' personnel rep In China Hewlett Packard's Beijing office, captures Measure is published six times a year for employees and associates of Hewlett-Packard Company. 11 is produced the beauty and majesty of the by Caporate Communications. Employee Communicalions Depanment. Mary Anne Easley. rncnager. Address Chinese Opera in Beijing with this correspondence 10 Measure. Hewlett-Packard Company, 2OBR. -

Imperial College of Science and Technology, University of London, Department of Computing
Imperial College of Science and Technology, University of London, Department of Computing. HIGH EFFICIENCY, CHARACTER-ORIENTED, LOCAL AREA NETWORKS by Martin Cripps This thesis is submitted in partial fulfilment of the requirements for the degree of Doctor of Philosophy and the Diploma of Imperial College of Science and Technology, January 1988. For Clare Attempt the end His reasons are as two grains of wheat but never stand to doubt hid in two bushels of chaff. nothing's so hard You shall seek all day ere you find them but search and when you have found them will find it out they are not worth the search. Robert Herrick (1591-1674) William Shakespeare (1564-1616) 1 ABSTRACT This thesis explores the problem of interconnecting character-oriented devices over local area networks by investigating significant aspects of hardware, software, protocol and operational factors. It proposes effective and efficient solutions which were tested during a full-scale experiment The results of that experiment demonstrate convenient, cost-effective and reliable operation. The novelty of this investigation arises from its character-oriented approach. Much work has been carried out by others on local area networks which transfer blocks of data efficiently, however, a large majority of installed devices operate on a character-by-character basis and will continue so to do for some considerable time. This study is approached through analysis of the low efficiency of international standard networks for this class of device which defines the scope of this work. An original analysis of the potential mechanisms which can be used to give high efficiency and low delay for this class of transfer is then derived. -
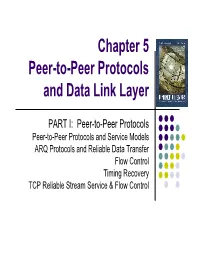
Chapter 5 Peer-To-Peer Protocols and Data Link Layer
Chapter 5 Peer-to-Peer Protocols and Data Link Layer PART I: Peer-to-Peer Protocols Peer-to-Peer Protocols and Service Models ARQ Protocols and Reliable Data Transfer Flow Control Timing Recovery TCP Reliable Stream Service & Flow Control Chapter 5 Peer-to-Peer Protocols and Data Link Layer PART II: Data Link Controls Framing Point-to-Point Protocol High-Level Data Link Control Link Sharing Using Statistical Multiplexing Chapter Overview z Peer-to-Peer protocols: many protocols involve the interaction between two peers z Service Models are discussed & examples given z Detailed discussion of ARQ provides example of development of peer-to-peer protocols z Flow control, TCP reliable stream, and timing recovery z Data Link Layer z Framing z PPP & HDLC protocols z Statistical multiplexing for link sharing Chapter 5 Peer-to-Peer Protocols and Data Link Layer Peer-to-Peer Protocols and Service Models Peer-to-Peer Protocols zzz zzz z Peer-to-Peer processes execute layer-n protocol to provide service to n + 1 peer process n + 1 peer process layer-(n+1) z Layer-(n+1) peer calls SDU SDU layer-n and passes PDU Service Data Units n peer process n peer process (SDUs) for transfer z Layer-n peers exchange Protocol Data Units (PDUs) to effect transfer n – 1 peer process n – 1 peer process z Layer-n delivers SDUs to destination layer-(n+1) peer zzz zzz Service Models z The service model specifies the information transfer service layer-n provides to layer-(n+1) z The most important distinction is whether the service is: z Connection-oriented z Connectionless z Service model possible features: z Arbitrary message size or structure z Sequencing and Reliability z Timing, Pacing, and Flow control z Multiplexing z Privacy, integrity, and authentication Connection-Oriented Transfer Service z Connection Establishment z Connection must be established between layer-(n+1) peers z Layer-n protocol must: Set initial parameters, e.g. -

Infrastructure Layers Dr
Infrastructure Internet perspective Change in point of view Internet standards do not discuss Data Link + Physical Layers Hardware developers define standards Infrastructure Internet Layer Model Internet application Application Layers Expects Internet services from OS Internet Aware Local + remote ports Transport Service requirements Network End-to-end IP routing + forwarding Data Link Layer — hardware management Not Internet Infrastructure Physical Layer — hardware Aware Computer Networks — Hadassah College — Fall 2015 Infrastructure Layers Dr. Martin Land 1 Computer Networks — Hadassah College — Fall 2015 Infrastructure Layers Dr. Martin Land 2 Infrastructure Infrastructure Engineering perspective Economic perspective Infrastructure layers Enormous investment in existing equipment Bottom-up design physical bits Global network of hardware nodes + transmission lines Physical layer (PHY) Developed to provide many services Internet (IP-based unreliable connectionless) just one service Defines physical transmission of bits Exploits a physical technology Most developed before Internet Telegraph — 1794 Data Link layer (DL) defines management of Physical Layer Telephone — 1876 How to make physical technology do what we want Teletype modem — 1943 Infrastructure management Digital telephone — 1962 Delivering data messages — 10% of effort Internet opened to public — 1992 Making hardware work correctly — 90% of effort Hardware updates OAM = Operations+Administration+Maintenance Replacement of manufactured hardware Application assumes infrastructure -

Serial-HOWTO.Pdf
Serial HOWTO Serial HOWTO Table of Contents Serial HOWTO...................................................................................................................................................1 David S.Lawyer [email protected] original by Greg Hankins.....................................................................1 1. Introduction..........................................................................................................................................1 2. Quick Help...........................................................................................................................................1 3. How the Hardware Transfers Bytes.....................................................................................................1 4. Serial Port Basics.................................................................................................................................1 5. Multiport Serial Boards/Cards/Adapters..............................................................................................2 6. Servers for Serial Ports........................................................................................................................2 7. Configuring Overview.........................................................................................................................2 8. Locating the Serial Port: IO address, IRQs..........................................................................................2 9. Configuring the Serial Driver (high-level) "stty"................................................................................2