Hereby Granted, Provided That the Above Copyright Notice and This Permission Notice Appear in All Copies
Total Page:16
File Type:pdf, Size:1020Kb
Load more
Recommended publications
-

A Taxonomy of Accelerator Architectures and Their
A taxonomy of accelerator C. Cas$caval S. Chatterjee architectures and their H. Franke K. J. Gildea programming models P. Pattnaik As the clock frequency of silicon chips is leveling off, the computer architecture community is looking for different solutions to continue application performance scaling. One such solution is the multicore approach, i.e., using multiple simple cores that enable higher performance than wide superscalar processors, provided that the workload can exploit the parallelism. Another emerging alternative is the use of customized designs (accelerators) at different levels within the system. These are specialized functional units integrated with the core, specialized cores, attached processors, or attached appliances. The design tradeoff is quite compelling because current processor chips have billions of transistors, but they cannot all be activated or switched at the same time at high frequencies. Specialized designs provide increased power efficiency but cannot be used as general-purpose compute engines. Therefore, architects trade area for power efficiency by placing in the design additional units that are known to be active at different times. The resulting system is a heterogeneous architecture, with the potential of specialized execution that accelerates different workloads. While designing and building such hardware systems is attractive, writing and porting software to a heterogeneous platform is even more challenging than parallelism for homogeneous multicore systems. In this paper, we propose a taxonomy that allows us to define classes of accelerators, with the goal of focusing on a small set of programming models for accelerators. We discuss several types of currently popular accelerators and identify challenges to exploiting such accelerators in current software stacks. -
ARTIFICIAL INTELLIGENCE and ALGORITHMIC LIABILITY a Technology and Risk Engineering Perspective from Zurich Insurance Group and Microsoft Corp
White Paper ARTIFICIAL INTELLIGENCE AND ALGORITHMIC LIABILITY A technology and risk engineering perspective from Zurich Insurance Group and Microsoft Corp. July 2021 TABLE OF CONTENTS 1. Executive summary 03 This paper introduces the growing notion of AI algorithmic 2. Introduction 05 risk, explores the drivers and A. What is algorithmic risk and why is it so complex? ‘Because the computer says so!’ 05 B. Microsoft and Zurich: Market-leading Cyber Security and Risk Expertise 06 implications of algorithmic liability, and provides practical 3. Algorithmic risk : Intended or not, AI can foster discrimination 07 guidance as to the successful A. Creating bias through intended negative externalities 07 B. Bias as a result of unintended negative externalities 07 mitigation of such risk to enable the ethical and responsible use of 4. Data and design flaws as key triggers of algorithmic liability 08 AI. A. Model input phase 08 B. Model design and development phase 09 C. Model operation and output phase 10 Authors: D. Potential complications can cloud liability, make remedies difficult 11 Zurich Insurance Group 5. How to determine algorithmic liability? 13 Elisabeth Bechtold A. General legal approaches: Caution in a fast-changing field 13 Rui Manuel Melo Da Silva Ferreira B. Challenges and limitations of existing legal approaches 14 C. AI-specific best practice standards and emerging regulation 15 D. New approaches to tackle algorithmic liability risk? 17 Microsoft Corp. Rachel Azafrani 6. Principles and tools to manage algorithmic liability risk 18 A. Tools and methodologies for responsible AI and data usage 18 Christian Bucher B. Governance and principles for responsible AI and data usage 20 Franziska-Juliette Klebôn C. -
Invisible Labor, Invisible Play: Online Gold Farming and the Boundary Between Jobs and Games
Vanderbilt Journal of Entertainment & Technology Law Volume 18 Issue 3 Issue 3 - Spring 2016 Article 2 2015 Invisible Labor, Invisible Play: Online Gold Farming and the Boundary Between Jobs and Games Julian Dibbell Follow this and additional works at: https://scholarship.law.vanderbilt.edu/jetlaw Part of the Internet Law Commons, and the Labor and Employment Law Commons Recommended Citation Julian Dibbell, Invisible Labor, Invisible Play: Online Gold Farming and the Boundary Between Jobs and Games, 18 Vanderbilt Journal of Entertainment and Technology Law 419 (2021) Available at: https://scholarship.law.vanderbilt.edu/jetlaw/vol18/iss3/2 This Article is brought to you for free and open access by Scholarship@Vanderbilt Law. It has been accepted for inclusion in Vanderbilt Journal of Entertainment & Technology Law by an authorized editor of Scholarship@Vanderbilt Law. For more information, please contact [email protected]. VANDERBILT JOURNAL OF ENTERTAINMENT & TECHNOLOGY LAW VOLUME 18 SPRING 2016 NUMBER 3 Invisible Labor, Invisible Play: Online Gold Farming and the Boundary Between Jobs and Games Julian Dibbell ABSTRACT When does work become play and play become work? Courts have considered the question in a variety of economic contexts, from student athletes seeking recognition as employees to professional blackjack players seeking to be treated by casinos just like casual players. Here, this question is applied to a relatively novel context: that of online gold farming, a gray-market industry in which wage-earning workers, largely based in China, are paid to play fantasy massively multiplayer online games (MMOs) that reward them with virtual items that their employers sell for profit to the same games' casual players. -

Proceedings 2005
LAC2005 Proceedings 3rd International Linux Audio Conference April 21 – 24, 2005 ZKM | Zentrum fur¨ Kunst und Medientechnologie Karlsruhe, Germany Published by ZKM | Zentrum fur¨ Kunst und Medientechnologie Karlsruhe, Germany April, 2005 All copyright remains with the authors www.zkm.de/lac/2005 Content Preface ............................................ ............................5 Staff ............................................... ............................6 Thursday, April 21, 2005 – Lecture Hall 11:45 AM Peter Brinkmann MidiKinesis – MIDI controllers for (almost) any purpose . ....................9 01:30 PM Victor Lazzarini Extensions to the Csound Language: from User-Defined to Plugin Opcodes and Beyond ............................. .....................13 02:15 PM Albert Gr¨af Q: A Functional Programming Language for Multimedia Applications .........21 03:00 PM St´ephane Letz, Dominique Fober and Yann Orlarey jackdmp: Jack server for multi-processor machines . ......................29 03:45 PM John ffitch On The Design of Csound5 ............................... .....................37 04:30 PM Pau Arum´ıand Xavier Amatriain CLAM, an Object Oriented Framework for Audio and Music . .............43 Friday, April 22, 2005 – Lecture Hall 11:00 AM Ivica Ico Bukvic “Made in Linux” – The Next Step .......................... ..................51 11:45 AM Christoph Eckert Linux Audio Usability Issues .......................... ........................57 01:30 PM Marije Baalman Updates of the WONDER software interface for using Wave Field Synthesis . 69 02:15 PM Georg B¨onn Development of a Composer’s Sketchbook ................. ....................73 Saturday, April 23, 2005 – Lecture Hall 11:00 AM J¨urgen Reuter SoundPaint – Painting Music ........................... ......................79 11:45 AM Michael Sch¨uepp, Rene Widtmann, Rolf “Day” Koch and Klaus Buchheim System design for audio record and playback with a computer using FireWire . 87 01:30 PM John ffitch and Tom Natt Recording all Output from a Student Radio Station . -

Extending the UHC LLVM Backend: Adding Support for Accurate Garbage Collection
Extending the UHC LLVM backend: Adding support for accurate garbage collection Paul van der Ende MSc Thesis October 18, 2010 INF/SCR-09-59 Daily Supervisors: Center for Software Technology dr. A. Dijkstra Dept. of Information and Computing Sciences drs. J.D. Fokker Utrecht University Utrecht, the Netherlands Second Supervisor: prof. dr. S.D. Swierstra Abstract The Utrecht Haskell Compiler has an LLVM backend for whole program analyse mode. This backend pre- viously used the Boehm-Weiser library for heap allocation and conservative garbage collection. Recently an accurate garbage collector for the UHC compiler has been developed. We wanted this new garbage collection library to work with the LLVM backend. But since this new collector is accurate, it needs cooperation with the LLVM backend. Functionality needs to be added to find the set of root references and traversing all live references. To find the root set, the bytecode interpreter backend currently uses static stack maps. This is where the problem arises. The LLVM compiler is known to do various aggressive transformations. These optimizations might change the stack layout described by the static stack map. So to avoid this problem we wanted to use the shadow-stack provided by the LLVM framework. This is a dynamic structure maintained on the stack to safely find the garbage collection roots. We expect that the shadow-stack approach comes with a runtime overhead for maintaining this information dynamically on the stack. So we did measure the impact of this method. We also measured the performance improvement of the new garbage collection method used and compare it with the other UHC backends. -
Avid Supported Video File Formats
Avid Supported Video File Formats 04.07.2021 Page 1 Avid Supported Video File Formats 4/7/2021 Table of Contents Common Industry Formats ............................................................................................................................................................................................................................................................................................................................................................................................... 4 Application & Device-Generated Formats .................................................................................................................................................................................................................................................................................................................................................................. 8 Stereoscopic 3D Video Formats ...................................................................................................................................................................................................................................................................................................................................................................................... 11 Quick Lookup of Common File Formats ARRI..............................................................................................................................................................................................................................................................................................................................................................4 -

Improving Memory Management Security for C and C++
Improving memory management security for C and C++ Yves Younan, Wouter Joosen, Frank Piessens, Hans Van den Eynden DistriNet, Katholieke Universiteit Leuven, Belgium Abstract Memory managers are an important part of any modern language: they are used to dynamically allocate memory for use in the program. Many managers exist and depending on the operating system and language. However, two major types of managers can be identified: manual memory allocators and garbage collectors. In the case of manual memory allocators, the programmer must manually release memory back to the system when it is no longer needed. Problems can occur when a programmer forgets to release it (memory leaks), releases it twice or keeps using freed memory. These problems are solved in garbage collectors. However, both manual memory allocators and garbage collectors store management information for the memory they manage. Often, this management information is stored where a buffer overflow could allow an attacker to overwrite this information, providing a reliable way to achieve code execution when exploiting these vulnerabilities. In this paper we describe several vulnerabilities for C and C++ and how these could be exploited by modifying the management information of a representative manual memory allocator and a garbage collector. Afterwards, we present an approach that, when applied to memory managers, will protect against these attack vectors. We implemented our approach by modifying an existing widely used memory allocator. Benchmarks show that this implementation has a negligible, sometimes even beneficial, impact on performance. 1 Introduction Security has become an important concern for all computer users. Worms and hackers are a part of every day internet life. -

Practical Homomorphic Encryption and Cryptanalysis
Practical Homomorphic Encryption and Cryptanalysis Dissertation zur Erlangung des Doktorgrades der Naturwissenschaften (Dr. rer. nat.) an der Fakult¨atf¨urMathematik der Ruhr-Universit¨atBochum vorgelegt von Dipl. Ing. Matthias Minihold unter der Betreuung von Prof. Dr. Alexander May Bochum April 2019 First reviewer: Prof. Dr. Alexander May Second reviewer: Prof. Dr. Gregor Leander Date of oral examination (Defense): 3rd May 2019 Author's declaration The work presented in this thesis is the result of original research carried out by the candidate, partly in collaboration with others, whilst enrolled in and carried out in accordance with the requirements of the Department of Mathematics at Ruhr-University Bochum as a candidate for the degree of doctor rerum naturalium (Dr. rer. nat.). Except where indicated by reference in the text, the work is the candidates own work and has not been submitted for any other degree or award in any other university or educational establishment. Views expressed in this dissertation are those of the author. Place, Date Signature Chapter 1 Abstract My thesis on Practical Homomorphic Encryption and Cryptanalysis, is dedicated to efficient homomor- phic constructions, underlying primitives, and their practical security vetted by cryptanalytic methods. The wide-spread RSA cryptosystem serves as an early (partially) homomorphic example of a public- key encryption scheme, whose security reduction leads to problems believed to be have lower solution- complexity on average than nowadays fully homomorphic encryption schemes are based on. The reader goes on a journey towards designing a practical fully homomorphic encryption scheme, and one exemplary application of growing importance: privacy-preserving use of machine learning. -

Reviewer's Guide
Episode® 6.5 Affordable transcoding for individuals and workgroups Multiformat encoding software with uncompromising quality, speed and control. The Episode Product Guide is designed to provide an overview of the features and functions of Telestream’s Episode products. This guide also provides product information, helpful encoding scenarios and other relevant information to assist in the product review process. Please review this document along with the associated Episode User Guide, which provides complete product details. Telestream provides this guide for informational purposes only; it is not a product specification. The information in this document is subject to change at any time. 1 CONTENTS EPISODE OVERVIEW ........................................................................................................... 3 Episode ($495 USD) ........................................................................................................... 3 Episode Pro ($995 USD) .................................................................................................... 3 Episode Engine ($4995 USD) ............................................................................................ 3 KEY BENEFITS ..................................................................................................................... 4 FEATURES ............................................................................................................................ 5 Highest quality ................................................................................................................... -
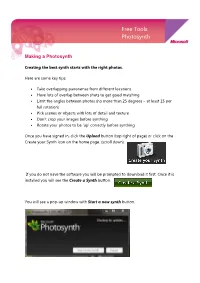
Free Tools Photosynth
Free Tools Photosynth Making a Photosynth Creating the best synth starts with the right photos. Here are some key tips: • Take overlapping panoramas from different locations • Have lots of overlap between shots to get good matching • Limit the angles between photos (no more than 25 degrees – at least 15 per full rotation) • Pick scenes or objects with lots of detail and texture • Don’t crop your images before synthing • Rotate your photos to be ‘up’ correctly before synthing Once you have signed in, click the Upload button (top right of page) or click on the Create your Synth icon on the home page. (scroll down). If you do not have the software you will be prompted to download it first. Once it is installed you will see the Create a Synth button. You will see a pop-up window with Start a new synth button. Give your synth a name, tags (descriptive words) and description. Click Add Photos, browse to your files add them. Then click on the Synth button at the bottom of the page. Photosynth will do the rest for you. Making a Panorama Many photosynths consist of photos shot from a single location. Our friends in Microsoft Research have developed a free, world class panoramic image stitcher called Microsoft Image Composite Editor (ICE for short.) ICE takes a set of overlapping photographs of a scene shot from a single camera location, and creates a single high-resolution image. Photosynth now has support for uploading, exploring and viewing ICE panoramas alongside normal synths. Here’s how to create a panorama in ICE and upload it to Photosynth: 1. -

(A/V Codecs) REDCODE RAW (.R3D) ARRIRAW
What is a Codec? Codec is a portmanteau of either "Compressor-Decompressor" or "Coder-Decoder," which describes a device or program capable of performing transformations on a data stream or signal. Codecs encode a stream or signal for transmission, storage or encryption and decode it for viewing or editing. Codecs are often used in videoconferencing and streaming media solutions. A video codec converts analog video signals from a video camera into digital signals for transmission. It then converts the digital signals back to analog for display. An audio codec converts analog audio signals from a microphone into digital signals for transmission. It then converts the digital signals back to analog for playing. The raw encoded form of audio and video data is often called essence, to distinguish it from the metadata information that together make up the information content of the stream and any "wrapper" data that is then added to aid access to or improve the robustness of the stream. Most codecs are lossy, in order to get a reasonably small file size. There are lossless codecs as well, but for most purposes the almost imperceptible increase in quality is not worth the considerable increase in data size. The main exception is if the data will undergo more processing in the future, in which case the repeated lossy encoding would damage the eventual quality too much. Many multimedia data streams need to contain both audio and video data, and often some form of metadata that permits synchronization of the audio and video. Each of these three streams may be handled by different programs, processes, or hardware; but for the multimedia data stream to be useful in stored or transmitted form, they must be encapsulated together in a container format. -

Online Media Business Models: Lessons from the Video Game Sector
Komorowski, M and Delaere, S. (2016). Online Media Business Models: Lessons from the Video Game Sector. Westminster Papers in Communication and Culture, 11(1), 103–123, DOI: http://dx.doi. org/10.16997/wpcc.220 RESEARCH ARTICLE Online Media Business Models: Lessons from the Video Game Sector Marlen Komorowski and Simon Delaere imec-SMIT, Vrije Universiteit, Brussels, BE Corresponding author: Marlen Komorowski ([email protected]) Today’s media industry is characterized by disruptive changes and business models have been acknowledged as a driving force for success. Current business model research manages only to grasp static descriptions while in reality media managers are struggling with the dynamics of the industry. This article aims to close this gap by investigating a new paradigm of online media business models. Based on three video game case studies of the massively multiplayer online role-playing game genre, this article explores a novel theoretical approach to explain the changes that can be made within business models. The article highlights the importance of changing processes within online media business models and emphasises that the video game sector is at the forefront of business innovation. Finally, it demonstrates that online media business model change is in a trade-off paradigm between capturing or offering potentially higher value per player vs. accessing a potentially larger player-base. Key words: Media industry; business model; process; disruption; video game sector Introduction Today’s media industry is characterized by disruptive transformations shaped by digitization. Digitization is not only generating new business opportunities but threatens traditional commercialization strategies and is proving highly unpredictable with regards to future market development.