Symantec™ Data Loss Prevention Detection REST API 2.0 Reference Guide
Total Page:16
File Type:pdf, Size:1020Kb
Load more
Recommended publications
-

Freebsd File Formats Manual Libarchive-Formats (5)
libarchive-formats (5) FreeBSD File Formats Manual libarchive-formats (5) NAME libarchive-formats —archive formats supported by the libarchive library DESCRIPTION The libarchive(3) library reads and writes a variety of streaming archive formats. Generally speaking, all of these archive formats consist of a series of “entries”. Each entry stores a single file system object, such as a file, directory,orsymbolic link. The following provides a brief description of each format supported by libarchive,with some information about recognized extensions or limitations of the current library support. Note that just because a format is supported by libarchive does not imply that a program that uses libarchive will support that format. Applica- tions that use libarchive specify which formats theywish to support, though manyprograms do use libarchive convenience functions to enable all supported formats. TarFormats The libarchive(3) library can read most tar archives. However, itonly writes POSIX-standard “ustar” and “pax interchange” formats. All tar formats store each entry in one or more 512-byte records. The first record is used for file metadata, including filename, timestamp, and mode information, and the file data is stored in subsequent records. Later variants have extended this by either appropriating undefined areas of the header record, extending the header to multiple records, or by storing special entries that modify the interpretation of subsequent entries. gnutar The libarchive(3) library can read GNU-format tar archives. It currently supports the most popular GNU extensions, including modern long filename and linkname support, as well as atime and ctime data. The libarchive library does not support multi-volume archives, nor the old GNU long filename format. -

Managing Many Files with Disk Archiver (DAR)
Intro Manual demos Function demos Summary Managing many files with Disk ARchiver (DAR) ALEX RAZOUMOV [email protected] WestGrid webinar - ZIP file with slides and functions http://bit.ly/2GGR9hX 2019-May-01 1 / 16 Intro Manual demos Function demos Summary To ask questions Websteam: email [email protected] Vidyo: use the GROUP CHAT to ask questions Please mute your microphone unless you have a question Feel free to ask questions via audio at any time WestGrid webinar - ZIP file with slides and functions http://bit.ly/2GGR9hX 2019-May-01 2 / 16 Intro Manual demos Function demos Summary Parallel file system limitations Lustre object storage servers (OSS) can get overloaded with lots of small requests I /home, /scratch, /project I Lustre is very different from your laptop’s HDD/SSD I a bad workflow will affect all other users on the system Avoid too many files, lots of small reads/writes I use quota command to see your current usage I maximum 5 × 105 files in /home, 106 in /scratch, 5 × 106 in /project (1) organize your code’s output (2) use TAR or another tool to pack files into archives and then delete the originals WestGrid webinar - ZIP file with slides and functions http://bit.ly/2GGR9hX 2019-May-01 3 / 16 Intro Manual demos Function demos Summary TAR limitations TAR is the most widely used archiving format on UNIX-like systems I first released in 1979 Each TAR archive is a sequence of files I each file inside contains: a header + some padding to reach a multiple of 512 bytes + file content I EOF padding (some zeroed blocks) at the end of the -

CDE: Run Any Linux Application On-Demand Without Installation
CDE: Run Any Linux Application On-Demand Without Installation Philip J. Guo Stanford University [email protected] Abstract with compiling, installing, and configuring software and their myriad of dependencies. For example, the official There is a huge ecosystem of free software for Linux, but Google Chrome help forum for “install/uninstall issues” since each Linux distribution (distro) contains a differ- has over 5800 threads. ent set of pre-installed shared libraries, filesystem layout In addition, a study of US labor statistics predicts that conventions, and other environmental state, it is difficult by 2012, 13 million American workers will do program- to create and distribute software that works without has- ming in their jobs, but amongst those, only 3 million will sle across all distros. Online forums and mailing lists be professional software developers [24]. Thus, there are are filled with discussions of users’ troubles with com- potentially millions of people who still need to get their piling, installing, and configuring Linux software and software to run on other machines but who are unlikely their myriad of dependencies. To address this ubiqui- to invest the effort to create one-click installers or wres- tous problem, we have created an open-source tool called tle with package managers, since their primary job is not CDE that automatically packages up the Code, Data, and to release production-quality software. For example: Environment required to run a set of x86-Linux pro- grams on other x86-Linux machines. Creating a CDE • System administrators often hack together ad- package is as simple as running the target application un- hoc utilities comprised of shell scripts and custom- der CDE’s monitoring, and executing a CDE package re- compiled versions of open-source software, in or- quires no installation, configuration, or root permissions. -
IDOL Keyview PDF Export SDK 12.6 C Programming Guide
KeyView Software Version 12.6 PDF Export SDK C Programming Guide Document Release Date: June 2020 Software Release Date: June 2020 PDF Export SDK C Programming Guide Legal notices Copyright notice © Copyright 1997-2020 Micro Focus or one of its affiliates. The only warranties for products and services of Micro Focus and its affiliates and licensors (“Micro Focus”) are set forth in the express warranty statements accompanying such products and services. Nothing herein should be construed as constituting an additional warranty. Micro Focus shall not be liable for technical or editorial errors or omissions contained herein. The information contained herein is subject to change without notice. Documentation updates The title page of this document contains the following identifying information: l Software Version number, which indicates the software version. l Document Release Date, which changes each time the document is updated. l Software Release Date, which indicates the release date of this version of the software. To check for updated documentation, visit https://www.microfocus.com/support-and-services/documentation/. Support Visit the MySupport portal to access contact information and details about the products, services, and support that Micro Focus offers. This portal also provides customer self-solve capabilities. It gives you a fast and efficient way to access interactive technical support tools needed to manage your business. As a valued support customer, you can benefit by using the MySupport portal to: l Search for knowledge documents of interest l Access product documentation l View software vulnerability alerts l Enter into discussions with other software customers l Download software patches l Manage software licenses, downloads, and support contracts l Submit and track service requests l Contact customer support l View information about all services that Support offers Many areas of the portal require you to sign in. -

Forcepoint DLP Supported File Formats and Size Limits
Forcepoint DLP Supported File Formats and Size Limits Supported File Formats and Size Limits | Forcepoint DLP | v8.8.1 This article provides a list of the file formats that can be analyzed by Forcepoint DLP, file formats from which content and meta data can be extracted, and the file size limits for network, endpoint, and discovery functions. See: ● Supported File Formats ● File Size Limits © 2021 Forcepoint LLC Supported File Formats Supported File Formats and Size Limits | Forcepoint DLP | v8.8.1 The following tables lists the file formats supported by Forcepoint DLP. File formats are in alphabetical order by format group. ● Archive For mats, page 3 ● Backup Formats, page 7 ● Business Intelligence (BI) and Analysis Formats, page 8 ● Computer-Aided Design Formats, page 9 ● Cryptography Formats, page 12 ● Database Formats, page 14 ● Desktop publishing formats, page 16 ● eBook/Audio book formats, page 17 ● Executable formats, page 18 ● Font formats, page 20 ● Graphics formats - general, page 21 ● Graphics formats - vector graphics, page 26 ● Library formats, page 29 ● Log formats, page 30 ● Mail formats, page 31 ● Multimedia formats, page 32 ● Object formats, page 37 ● Presentation formats, page 38 ● Project management formats, page 40 ● Spreadsheet formats, page 41 ● Text and markup formats, page 43 ● Word processing formats, page 45 ● Miscellaneous formats, page 53 Supported file formats are added and updated frequently. Key to support tables Symbol Description Y The format is supported N The format is not supported P Partial metadata -

Hydraspace: Computational Data Storage for Autonomous Vehicles
HydraSpace: Computational Data Storage for Autonomous Vehicles Ruijun Wang, Liangkai Liu and Weisong Shi Wayne State University fruijun, liangkai, [email protected] Abstract— To ensure the safety and reliability of an The current vehicle data logging system is designed autonomous driving system, multiple sensors have been for capturing a wide range of signals of traditional CAN installed in various positions around the vehicle to elim- bus data, including temperature, brakes, throttle settings, inate any blind point which could bring potential risks. Although the sensor data is quite useful for localization engine, speed, etc. [4]. However, it cannot handle sensor and perception, the high volume of these data becomes a data because both the data type and the amount far burden for on-board computing systems. More importantly, exceed its processing capability. Thus, it is urgent to the situation will worsen with the demand for increased propose efficient data computing and storage methods for precision and reduced response time of self-driving appli- both CAN bus and sensed data to assist the development cations. Therefore, how to manage this massive amount of sensed data has become a big challenge. The existing of self-driving techniques. As it refers to the installed vehicle data logging system cannot handle sensor data sensors, camera and LiDAR are the most commonly because both the data type and the amount far exceed its used because the camera can show a realistic view processing capability. In this paper, we propose a computa- of the surrounding environment while LiDAR is able tional storage system called HydraSpace with multi-layered to measure distances with laser lights quickly [5], [6]. -
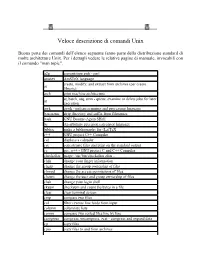
Unix Command
Veloce descrizione di comandi Unix Buona parte dei comandi dell’elenco seguente fanno parte della distribuzione standard di molte architetture Unix. Per i dettagli vedere le relative pagine di manuale, invocabili con il comando "man topic". a2p convertitore awk - perl amstex AmSTeX language create, modify, and extract from archives (per creare ar librerie) arch print machine architecture at, batch, atq, atrm - queue, examine or delete jobs for later at execution awk gawk - pattern scanning and processing language basename strip directory and suffix from filenames bash GNU Bourne-Again SHell bc An arbitrary precision calculator language bibtex make a bibliography for (La)TeX c++ GNU project C++ Compiler cal displays a calendar cat concatenate files and print on the standard output cc gcc, g++ - GNU project C and C++ Compiler checkalias usage: /usr/bin/checkalias alias .. chfn change your finger information chgrp change the group ownership of files chmod change the access permissions of files chown change the user and group ownership of files chsh change your login shell cksum checksum and count the bytes in a file clear clear terminal screen cmp compare two files col filter reverse line feeds from input column columnate lists comm compare two sorted files line by line compress compress, uncompress, zcat - compress and expand data cp copy files cpio copy files to and from archives tcsh - C shell with file name completion and command line csh editing csplit split a file into sections determined by context lines cut remove sections from each -

Backing up Linux - Ii
BACKING UP LINUX - II 1 Software recommendations, disrecommendations and examples This chapter describes some details and examples of a number or programs. Please note that there are far more backup programs in existence than the ones I mention here. The reason I mention these, is because these are the ones I have a lot experience with, and it shows how to apply or consider the concepts described above, in practice. Sometimes as specifically refer to the GNU version of an application, the standard version on Linux installations, which can be fundamentally different than the classic version, so keep that in mind. 1.1. Dar First a word of caution. It's highly recommended that you use version 2.3.3 (most recent stable release at the time of writing) or newer because it contains a major bugfix. Read the announcement on Dar's news list for more info. Dar is very well thought through and has solutions for classic pitfalls. For example, it comes with a statically compiled binary which you can copy on (the first disk of) your backup. It supports automatic archive slicing, and has an option to set the size of the first slice separately, so you have some space on the first disk left for making a boot CD, for example. It also lets you run a command between each slice, so you can burn it on CD, or calculate parity information on it, etc. And, very importantly, its default options are well chosen. Well, that is, except for the preservation of atimes (see atime-preserveration above). -

TO: Charles F. Bolden, Jr. Administrator December 17,2012 FROM: Paul K. Martin (79- Inspector General SUBJECT: NASA's Efforts To
National Aeronautics and Space Administration Office of Inspector General N~~, J. Washington, DC 20546-0001 December 17,2012 TO: Charles F. Bolden, Jr. Administrator FROM: Paul K. Martin (79- Inspector General SUBJECT: NASA's Efforts to Encrypt its Laptop Computers On October 31, 2012, a NASA-issued laptop was stolen from the vehicle ofa NASA Headquarters employee. The laptop contained hundreds of files and e-mails with the Social Security numbers and other forms of personally identifiable information (PH) for more than 10,000 current and former NASA employees and contractors. Although the laptop was password protected, neither the laptop itself nor the individual files were encrypted. l As a result of this loss, NASA contracted with a company to provide credit monitoring services to the affected individuals. NASA estimates that these services will cost between $500,000 and $700,000. This was not the first time NASA experienced a significant loss of PH or other sensitive but unclassified (SBU) data as a result of the theft of an unencrypted Agency laptop. For example, in March 2012 a bag containing a government-issued laptop, NASA access badge, and a token used to enable remote-access to a NASA network was stolen from a car parked in the driveway of a Kennedy Space Center employee. A review by information technology (IT) security officials revealed that the stolen computer contained the names, Social Security numbers, and other PH information for 2,400 NASA civil servants, as well as two files containing sensitive information related to a NASA program. As a result of the theft, NASA incurred credit monitoring expenses of approximately $200,000. -

GNU Sharutils, Version 4.1.9 a Set of Shell Archiver Utilities Edition 4.1.9, 28 October
GNU sharutils, version 4.1.9 A set of shell archiver utilities Edition 4.1.9, 28 October Jan Dj¨arv Francois Pinard Copyright c 1994 Free Software Foundation, Inc. Permission is granted to make and distribute verbatim copies of this manual provided the copy- right notice and this permission notice are preserved on all copies. Permission is granted to copy and distribute modified versions of this manual under the condi- tions for verbatim copying, provided that the entire resulting derived work is distributed under the terms of a permission notice identical to this one. Permission is granted to copy and distribute translations of this manual into another language, under the above conditions for modified versions, except that this permission notice may be stated in a translation approved by the Foundation. i Short Contents 1 Introduction to both programs ................................... 1 2 Invoking the shar program ..................................... 2 3 Invoking the unshar program ................................... 7 4 Miscellaneous considerations .................................... 8 ii Table of Contents 1 Introduction to both programs .......................... 1 2 Invoking the shar program .............................. 2 2.1 Selecting files................................................................ 2 2.2 Splitting output ............................................................. 2 2.3 Controlling the shar headers .................................................. 3 2.4 Selecting how files are stocked ............................................... -

Building and Installing Software Packages for Linux Building and Installing Software Packages for Linux
Building and Installing Software Packages for Linux Building and Installing Software Packages for Linux Table of Contents Building and Installing Software Packages for Linux.....................................................................................1 Mendel Cooper −−− http://personal.riverusers.com/~thegrendel/...........................................................1 1.Introduction...........................................................................................................................................1 2.Unpacking the Files..............................................................................................................................1 3.Using Make...........................................................................................................................................1 4.Prepackaged Binaries............................................................................................................................1 5.Termcap and Terminfo Issues...............................................................................................................1 6.Backward Compatibility With a.out Binaries.......................................................................................1 7.Troubleshooting....................................................................................................................................2 8.Final Steps.............................................................................................................................................2 -

Proceedings of the 17 Large Installation Systems Administration
USENIX Association Proceedings of the 17th Large Installation Systems Administration Conference San Diego, CA, USA October 26–31, 2003 THE ADVANCED COMPUTING SYSTEMS ASSOCIATION © 2003 by The USENIX Association All Rights Reserved For more information about the USENIX Association: Phone: 1 510 528 8649 FAX: 1 510 548 5738 Email: [email protected] WWW: http://www.usenix.org Rights to individual papers remain with the author or the author's employer. Permission is granted for noncommercial reproduction of the work for educational or research purposes. This copyright notice must be included in the reproduced paper. USENIX acknowledges all trademarks herein. Further Torture: More Testing of Backup and Archive Programs Elizabeth D. Zwicky ABSTRACT Every system administrator depends on some set of programs for making secondary copies of data, as backups for disaster recovery or as archives for long term storage. These programs, like all other programs, have bugs. The important thing for system administrators to know is where those bugs are. Some years ago I did testing on backup and archive programs, and found that failures were extremely common and that the documented limitations of programs did not match their actual limitations. Curious to see how the situation had changed, I put together a new set of tests, and found that programs had improved significantly, but that undocumented failures were still common. In the previous tests, almost every program crashed outright at some point, and dump significantly out-performed all other contenders. In addition, many programs other than the backup and archive programs failed catastrophically (most notably fsck on many platforms, and the kernel on one platform).