Introduction Points
Total Page:16
File Type:pdf, Size:1020Kb
Load more
Recommended publications
-

UC Santa Barbara UC Santa Barbara Electronic Theses and Dissertations
UC Santa Barbara UC Santa Barbara Electronic Theses and Dissertations Title A Web of Extended Metaphors in the Guerilla Open Access Manifesto of Aaron Swartz Permalink https://escholarship.org/uc/item/6w76f8x7 Author Swift, Kathy Publication Date 2017 Peer reviewed|Thesis/dissertation eScholarship.org Powered by the California Digital Library University of California UNIVERSITY OF CALIFORNIA Santa Barbara A Web of Extended Metaphors in the Guerilla Open Access Manifesto of Aaron Swartz A dissertation submitted in partial satisfaction of the requirements for the degree Doctor of Philosophy in Education by Kathleen Anne Swift Committee in charge: Professor Richard Duran, Chair Professor Diana Arya Professor William Robinson September 2017 The dissertation of Kathleen Anne Swift is approved. ................................................................................................................................ Diana Arya ................................................................................................................................ William Robinson ................................................................................................................................ Richard Duran, Committee Chair June 2017 A Web of Extended Metaphors in the Guerilla Open Access Manifesto of Aaron Swartz Copyright © 2017 by Kathleen Anne Swift iii ACKNOWLEDGEMENTS I would like to thank the members of my committee for their advice and patience as I worked on gathering and analyzing the copious amounts of research necessary to -

Hacker Public Radio
hpr0001 :: Introduction to HPR hpr0002 :: Customization the Lost Reason hpr0003 :: Lost Haycon Audio Aired on 2007-12-31 and hosted by StankDawg Aired on 2008-01-01 and hosted by deepgeek Aired on 2008-01-02 and hosted by Morgellon StankDawg and Enigma talk about what HPR is and how someone can contribute deepgeek talks about Customization being the lost reason in switching from Morgellon and others traipse around in the woods geocaching at midnight windows to linux Customization docdroppers article hpr0004 :: Firefox Profiles hpr0005 :: Database 101 Part 1 hpr0006 :: Part 15 Broadcasting Aired on 2008-01-03 and hosted by Peter Aired on 2008-01-06 and hosted by StankDawg as part of the Database 101 series. Aired on 2008-01-08 and hosted by dosman Peter explains how to move firefox profiles from machine to machine 1st part of the Database 101 series with Stankdawg dosman and zach from the packetsniffers talk about Part 15 Broadcasting Part 15 broadcasting resources SSTRAN AMT3000 part 15 transmitter hpr0007 :: Orwell Rolled over in his grave hpr0009 :: This old Hack 4 hpr0008 :: Asus EePC Aired on 2008-01-09 and hosted by deepgeek Aired on 2008-01-10 and hosted by fawkesfyre as part of the This Old Hack series. Aired on 2008-01-10 and hosted by Mubix deepgeek reviews a film Part 4 of the series this old hack Mubix and Redanthrax discuss the EEpc hpr0010 :: The Linux Boot Process Part 1 hpr0011 :: dd_rhelp hpr0012 :: Xen Aired on 2008-01-13 and hosted by Dann as part of the The Linux Boot Process series. -
Luigi Documentation Release 2.8.13
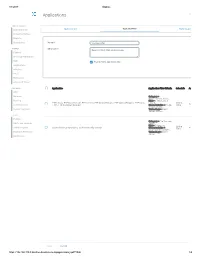
Luigi Documentation Release 2.8.13 The Luigi Authors Apr 29, 2020 Contents 1 Background 3 2 Visualiser page 5 3 Dependency graph example 7 4 Philosophy 9 5 Who uses Luigi? 11 6 External links 15 7 Authors 17 8 Table of Contents 19 8.1 Example – Top Artists.......................................... 19 8.2 Building workflows........................................... 23 8.3 Tasks................................................... 28 8.4 Parameters................................................ 33 8.5 Running Luigi.............................................. 36 8.6 Using the Central Scheduler....................................... 38 8.7 Execution Model............................................. 41 8.8 Luigi Patterns............................................... 43 8.9 Configuration............................................... 48 8.10 Configure logging............................................ 60 8.11 Design and limitations.......................................... 61 9 API Reference 63 9.1 luigi package............................................... 63 9.2 Indices and tables............................................ 248 Python Module Index 249 Index 251 i ii Luigi Documentation, Release 2.8.13 Luigi is a Python (2.7, 3.6, 3.7 tested) package that helps you build complex pipelines of batch jobs. It handles dependency resolution, workflow management, visualization, handling failures, command line integration, and much more. Run pip install luigi to install the latest stable version from PyPI. Documentation for the latest release is hosted on readthedocs. Run pip install luigi[toml] to install Luigi with TOML-based configs support. For the bleeding edge code, pip install git+https://github.com/spotify/luigi.git. Bleeding edge documentation is also available. Contents 1 Luigi Documentation, Release 2.8.13 2 Contents CHAPTER 1 Background The purpose of Luigi is to address all the plumbing typically associated with long-running batch processes. You want to chain many tasks, automate them, and failures will happen. -

Webové Diskusní Fórum
MASARYKOVA UNIVERZITA F}w¡¢£¤¥¦§¨ AKULTA INFORMATIKY !"#$%&'()+,-./012345<yA| Webové diskusní fórum BAKALÁRSKÁˇ PRÁCE Martin Bana´s Brno, Jaro 2009 Prohlášení Prohlašuji, že tato bakaláˇrskápráce je mým p ˚uvodnímautorským dílem, které jsem vy- pracoval samostatnˇe.Všechny zdroje, prameny a literaturu, které jsem pˇrivypracování používal nebo z nich ˇcerpal,v práci ˇrádnˇecituji s uvedením úplného odkazu na pˇríslušný zdroj. V Brnˇe,dne . Podpis: . Vedoucí práce: prof. RNDr. JiˇríHˇrebíˇcek,CSc. ii Podˇekování Dˇekujivedoucímu prof. RNDr. JiˇrímuHˇrebíˇckovi,CSc. za správné vedení v pr ˚ubˇehucelé práce a trpˇelivostpˇrikonzutacích. Dále dˇekujicelému kolektivu podílejícímu se na reali- zaci projektu FEED za podnˇetnépˇripomínkya postˇrehy. iii Shrnutí Bakaláˇrskápráce se zabývá analýzou souˇcasnýchdiskusních fór typu open-source a vý- bˇerem nejvhodnˇejšíhodiskusního fóra pro projekt eParticipation FEED. Další ˇcástpráce je zamˇeˇrenána analýzu vybraného fóra, tvorbu ˇceskéhomanuálu, ˇceskélokalizace pro portál a rozšíˇrenípro anotaci pˇríspˇevk˚u. Poslední kapitola je vˇenovánanasazení systému do provozu a testování rozšíˇrení pro anotaci pˇríspˇevk˚u. iv Klíˇcováslova projekt FEED, eParticipation, diskusní fórum, portál, PHP, MySQL, HTML v Obsah 1 Úvod ...........................................3 2 Projekt eParticipation FEED .............................4 2.1 eGovernment ...................................4 2.2 Úˇcastníciprojektu FEED .............................4 2.3 Zamˇeˇreníprojektu FEED .............................5 2.4 Cíl -

Cybercrime: Internet Driven Illicit Activities and Behavior
Land Forces Academy Review Vol. XXV, No. 4(100), 2020 CYBERCRIME: INTERNET DRIVEN ILLICIT ACTIVITIES AND BEHAVIOR Maurice DAWSON Illinois Institute of Technology, Chicago, United States of America [email protected] ABSTRACT Cybercrime affects multiple areas of society with nefarious activities ranging from human trafficking to illegal arms sale. The Internet has allowed some nefarious activities to be revived as others have emerged in this new age. In turn, this has become a national security issue for countries as this requires resources to combat this evolving threat. These activities include undermining legitimate services that provide government services to its citizens, such as passport, national identification, tax services, and more. This paper introduces some of these activities, enabling readers to understand this digital criminal world further. KEYWORDS: cybercrime, human trafficking, dark web, online marketplace, cryptocurrency, disinformation 1. Introduction name a few (Deibert, 2009). Meanwhile, The Internet has allowed for many more countries have been known to use the technological advances that have brought Internet to target political dissidents such as forth positive outcomes. In retrospect, the Cuba, Ethiopia, Eritrea, Gambia, Morocco, Internet has also allowed for criminal North Korea, Russia, and more (Committee activities to flourish. And while both to Protect Journalists, 2020). Even with this positive and negative effects are expected, mentioned censorship and oversight, illicit the use of the Internet by a criminal activities remain on the rise through the organization, nation-states, terrorists, Internet. extremists, and others finds another means In recent years, police and other law to market their illegal activity. As the enforcement organizations have shut down introduction of the technological pages that advocate prostitution. -

An Evolving Threat the Deep Web
8 An Evolving Threat The Deep Web Learning Objectives distribute 1. Explain the differences between the deep web and darknets.or 2. Understand how the darknets are accessed. 3. Discuss the hidden wiki and how it is useful to criminals. 4. Understand the anonymity offered by the deep web. 5. Discuss the legal issues associated withpost, use of the deep web and the darknets. The action aimed to stop the sale, distribution and promotion of illegal and harmful items, including weapons and drugs, which were being sold on online ‘dark’ marketplaces. Operation Onymous, coordinated by Europol’s Europeancopy, Cybercrime Centre (EC3), the FBI, the U.S. Immigration and Customs Enforcement (ICE), Homeland Security Investigations (HSI) and Eurojust, resulted in 17 arrests of vendors andnot administrators running these online marketplaces and more than 410 hidden services being taken down. In addition, bitcoins worth approximately USD 1 million, EUR 180,000 Do in cash, drugs, gold and silver were seized. —Europol, 20141 143 Copyright ©2018 by SAGE Publications, Inc. This work may not be reproduced or distributed in any form or by any means without express written permission of the publisher. 144 Cyberspace, Cybersecurity, and Cybercrime THINK ABOUT IT 8.1 Surface Web and Deep Web Google, Facebook, and any website you can What Would You Do? find via traditional search engines (Internet Explorer, Chrome, Firefox, etc.) are all located 1. The deep web offers users an anonym- on the surface web. It is likely that when you ity that the surface web cannot provide. use the Internet for research and/or social What would you do if you knew that purposes you are using the surface web. -

Tutorial Blogspot Plus Blogger Templates
Tutorial Blogspot Plus Blogger Templates To Bloggers Everywhere 1 2 Contents Contact Us 25 Cara daftar Gmail 25 Cara daftar Blogger pertama kali 27 Cara login ke blogger pertama kali 28 Kontrol panel blogger (dashboard) 29 Cara posting di blogger 30 Halaman Pengaturan (menu dasar) 31 Banyak malware yang ditemukan google 32 Google ! Mesin pembobol yang menakutkan 32 Web Proxy (Anonymous) 33 Daftar alamat google lengkap 34 Google: tampil berdasarkan Link 37 Oom - Pemenang kontes programming VB6 source code 38 (www.planet-sourc... Oom - Keyboard Diagnostic 2002 (VB6 - Open Source) 39 Oom - Access Siemens GSM CellPhone With Full 40 AT+Command (VB6 - Ope... Oom - How to know speed form access (VB6) 40 Para blogger haus akan link blog 41 Nama blog cantik yang disia-siakan dan apakah pantas nama 41 blog dipe... Otomatisasi firewalling IP dan MAC Address dengan bash script 43 Firewalling IP Address dan MAC Address dengan iptables 44 Meminimalis serangan Denial of Service Attacks di Win Y2K/XP 47 Capek banget hari ini.. 48 3 daftar blog ke search engine 48 Etika dan cara promosi blog 49 Tool posting dan edit text blogger 52 Setting Blog : Tab Publikasi 53 Wordpress plugins untuk google adsense 54 Google meluncurkan pemanggilan META tag terbaru 54 “unavailable after” Setting Blog : Tab Format 55 Melacak posisi keyword di Yahoo 56 Mengetahui page ranking dan posisi keyword (kata kunci) anda 56 pada S... Percantik halaman blog programmer dengan "New Code 57 Scrolling Ticke... 20 Terbaik Situs Visual Basic 58 BEST BUY : 11 CD Full Source Code Untuk Programmer 60 Tips memulai blog untuk pemula 62 Lijit: Alternatif search untuk blogger 62 Berpartisipasi dalam Blog "17 Agustus Indonesia MERDEKA" 63 Trafik di blog lumayan, tapi kenapa masih aja minim komentar? 64 Editor posting compose blogger ternyata tidak "wysiwyg" 65 Google anti jual beli link 65 Tips blogger css validator menggunakan "JavaScript Console" 65 pada Fl.. -
Applications Log Viewer
4/1/2017 Sophos Applications Log Viewer MONITOR & ANALYZE Control Center Application List Application Filter Traffic Shaping Default Current Activities Reports Diagnostics Name * Mike App Filter PROTECT Description Based on Block filter avoidance apps Firewall Intrusion Prevention Web Enable Micro App Discovery Applications Wireless Email Web Server Advanced Threat CONFIGURE Application Application Filter Criteria Schedule Action VPN Network Category = Infrastructure, Netw... Routing Risk = 1-Very Low, 2- FTPS-Data, FTP-DataTransfer, FTP-Control, FTP Delete Request, FTP Upload Request, FTP Base, Low, 4... All the Allow Authentication FTPS, FTP Download Request Characteristics = Prone Time to misuse, Tra... System Services Technology = Client Server, Netwo... SYSTEM Profiles Category = File Transfer, Hosts and Services Confe... Risk = 3-Medium Administration All the TeamViewer Conferencing, TeamViewer FileTransfer Characteristics = Time Allow Excessive Bandwidth,... Backup & Firmware Technology = Client Server Certificates Save Cancel https://192.168.110.3:4444/webconsole/webpages/index.jsp#71826 1/4 4/1/2017 Sophos Application Application Filter Criteria Schedule Action Applications Log Viewer Facebook Applications, Docstoc Website, Facebook Plugin, MySpace Website, MySpace.cn Website, Twitter Website, Facebook Website, Bebo Website, Classmates Website, LinkedIN Compose Webmail, Digg Web Login, Flickr Website, Flickr Web Upload, Friendfeed Web Login, MONITOR & ANALYZE Hootsuite Web Login, Friendster Web Login, Hi5 Website, Facebook Video -

Dark and Deep Webs-Liberty Or Abuse
International Journal of Cyber Warfare and Terrorism Volume 9 • Issue 2 • April-June 2019 Dark and Deep Webs-Liberty or Abuse Lev Topor, Bar Ilan University, Ramat Gan, Israel https://orcid.org/0000-0002-1836-5150 ABSTRACT While the Dark Web is the safest internet platform, it is also the most dangerous platform at the same time. While users can stay secure and almost totally anonymously, they can also be exploited by other users, hackers, cyber-criminals, and even foreign governments. The purpose of this article is to explore and discuss the tremendous benefits of anonymous networks while comparing them to the hazards and risks that are also found on those platforms. In order to open this dark portal and contribute to the discussion of cyber and politics, a comparative analysis of the dark and deep web to the commonly familiar surface web (World Wide Web) is made, aiming to find and describe both the advantages and disadvantages of the platforms. KeyWoRD Cyber, DarkNet, Information, New Politics, Web, World Wide Web INTRoDUCTIoN In June 2018, the United States Department of Justice uncovered its nationwide undercover operation in which it targeted dark web vendors. This operation resulted in 35 arrests and seizure of weapons, drugs, illegal erotica material and much more. In total, the U.S. Department of Justice seized more than 23.6$ Million.1 In that same year, as in past years, the largest dark web platform, TOR (The Onion Router),2 was sponsored almost exclusively by the U.S. government and other Western allies.3 Thus, an important and even philosophical question is derived from this situation- Who is responsible for the illegal goods and cyber-crimes? Was it the criminal[s] that committed them or was it the facilitator and developer, the U.S. -

Measurement and Analysis of Cryptolocker Ransoms in Bitcoin
Behind Closed Doors: Measurement and Analysis of CryptoLocker Ransoms in Bitcoin Kevin Liao, Ziming Zhao, Adam Doupe,´ and Gail-Joon Ahn Arizona State University fkevinliao, zmzhao, doupe, [email protected] Abstract—Bitcoin, a decentralized cryptographic currency that called bitcoins1, to other addresses by issuing transactions, has experienced proliferating popularity over the past few years, which are then broadcast to the public blockchain. is the common denominator in a wide variety of cybercrime. Since all confirmed transactions are visible to the public, the We perform a measurement analysis of CryptoLocker, a family of ransomware that encrypts a victim’s files until a ransom blockchain’s inherent transparency has proven to be ineffective is paid, within the Bitcoin ecosystem from September 5, 2013 in preserving the anonymity of its users (legitimate users through January 31, 2014. Using information collected from and cybercriminals alike). While Bitcoin addresses alone are online fora, such as reddit and BitcoinTalk, as an initial starting not explicitly tied to any real-world entities, a number of point, we generate a cluster of 968 Bitcoin addresses belonging recent research efforts have shown that monetary movements to CryptoLocker. We provide a lower bound for CryptoLocker’s economy in Bitcoin and identify 795 ransom payments totalling and address links can be traced throughout the blockchain 1,128.40 BTC ($310,472.38), but show that the proceeds could data structure [3]–[8]. Even though there have been many have been worth upwards of $1.1 million at peak valuation. By attempts to enhance user privacy with varying degrees of analyzing ransom payment timestamps both longitudinally across success (i.e. -
JW Apostate Reply Supporting Motion to Quash April 6Th
Case 7:20-mc-00119-CS Document 13 Filed 04/06/20 Page 1 of 21 1 JANE / JOHN DOE 2 Email: [email protected] 3 4 Pro se 5 IN THE UNITED STATES DISTRICT COURT FOR THE 6 SOUTHERN DISTRICT OF NEW YORK 7 8 IN RE: DMCA SUBPOENA TO GOOGLE, LLC Case No.: 7:20-mc-00119 9 10 JANE / JOHN DOE’S REPLY IN SUPPORT OF THE OBJECTION AND MOTION TO 11 QUASH DMCA SUBPOENA 12 13 A. INTRODUCTION 14 15 While it is true that Jehovah’s Witnesses are well known for their distribution of 16 Bible based books and publications, they are also a notorious group of criminal 17 pedophiles running a scam “religion” who are guilty of abuse of process and emotional 18 19 extortion through sham litigation in their pathetic efforts at discovering leaks and 20 moles and whistleblowers. Unfortunately for them, this is the year 2020 and things 21 22 like VPNs, anonymous proxies, and TOR exit nodes frustrate them at every turn. 23 Whether one is known as Darkspilver or John Redwood or JW Apostate, or any 24 number of other pseudonyms, it does not really matter as we are all Spartacus in this 25 26 fight! Reporting on and exposing to public comment and ridicule the doctrinal 27 inconsistencies and reversals, failed predictions, mistranslation of the Bible, harsh 28 JANE / JOHN DOE’S REPLY IN SUPPORT OF OBJECTION AND MOTION TO QUASH DMCA SUBPOENA- 1 Case 7:20-mc-00119-CS Document 13 Filed 04/06/20 Page 2 of 21 1 treatment of former members and autocratic and coercive leadership (not to mention 2 the child raping!) is a public duty that Jane / John Doe takes extremely seriously at 3 1 great personal risk. -
LAMP and the REST Architecture Step by Step Analysis of Best Practice
LAMP and the REST Architecture Step by step analysis of best practice Santiago Gala High Sierra Technology S.L.U. Minimalistic design using a Resource Oriented Architecture What is a Software Platform (Ray Ozzie ) ...a relevant and ubiquitous common service abstraction Creates value by leveraging participants (e- cosystem) Hardware developers (for OS level platforms) Software developers Content developers Purchasers Administrators Users Platform Evolution Early stage: not “good enough” solution differentiation, innovation, value flows Later: modular architecture, commoditiza- tion, cloning no premium, just speed to market and cost driven The platform effect - ossification, followed by cloning - is how Chris- tensen-style modularity comes to exist in the software industry. What begins as a value-laden proprietary platform becomes a replaceable component over time, and the most successful of these components finally define the units of exchange that power commodity networks. ( David Stutz ) Platform Evolution (II) Example: PostScript Adobe Apple LaserWriter Aldus Pagemaker Desktop Publishing Linotype imagesetters NeWS (Display PostScript) OS X standards (XSL-FO -> PDF, Scribus, OOo) Software Architecture ...an abstraction of the runtime elements of a software system during some phase of its oper- ation. A system may be composed of many lev- els of abstraction and many phases of opera- tion, each with its own software architecture. Roy Fielding (REST) What is Architecture? Way to partition a system in components