Security Policy for FIPS 140-2 Validation
Total Page:16
File Type:pdf, Size:1020Kb
Load more
Recommended publications
-

Volume 2014, No. 1 Law Office Computing Page Puritas Springs Software Law Office Computing
Volume 2014, No. 1 Law Office Computing Page Puritas Springs Software Law Office Computing VOLUME 2014 NO. 1 $ 7 . 9 9 PURITAS SPRINGS SOFTWARE Best Home Pages We think the importance of the through which you accessed INSIDE THIS ISSUE: home page has been greatly the world wide web. Once 1-3 reduced due to the invention of tabbed browsers arrived on the tabbed browsers. Although scene it was possible to create 1,4,5 conceived a group of 4 earlier in 1988, home pages Digital Inklings 6,7 tabbed brows- with each page Child Support 8 ing didn’t go being able to Spousal Support 10 mainstream “specialize” in a Uniform DR Forms 12 until the re- specific area of lease of Micro- your interest. Family Law Documents 13 soft’s Windows Take the Probate Forms 14 Internet Ex- weather for Ohio Estate Tax 16 plorer 7 in example. Every U.S. Income Tax (1041) 18 2006. Until then, your Home good home page should have Ohio Fiduciary Tax 19 page was the sole portal a minimal weather information; (Continued on page 2) Ohio Adoption Forms 20 OH Guardianship Forms 21 OH Wrongful Death 22 Loan Amortizer 23 # More Law Office Tech Tips Advanced Techniques 24 Deed & Document Pro 25 Bankruptcy Forms 26 XX. Quick Launch. The patch the application that you’re Law Office Management 28 of little icons to the right of the working in is maximized. If OH Business Forms 30 Start button is called the Quick you’re interested, take a look Launch toolbar. Sure, you can at the sidebar on page XX of Business Dissolutions 31 put much-used shortcuts on this issue. -
Application of Solid State NMR for the Study of Surface Bound Species and Fossil Fuels Stacey Marie Althaus Iowa State University
Iowa State University Capstones, Theses and Graduate Theses and Dissertations Dissertations 2014 Application of solid state NMR for the study of surface bound species and fossil fuels Stacey Marie Althaus Iowa State University Follow this and additional works at: https://lib.dr.iastate.edu/etd Part of the Analytical Chemistry Commons, Nanoscience and Nanotechnology Commons, Other Chemistry Commons, and the Physical Chemistry Commons Recommended Citation Althaus, Stacey Marie, "Application of solid state NMR for the study of surface bound species and fossil fuels" (2014). Graduate Theses and Dissertations. 14111. https://lib.dr.iastate.edu/etd/14111 This Dissertation is brought to you for free and open access by the Iowa State University Capstones, Theses and Dissertations at Iowa State University Digital Repository. It has been accepted for inclusion in Graduate Theses and Dissertations by an authorized administrator of Iowa State University Digital Repository. For more information, please contact [email protected]. Application of solid state NMR for the study of surface bound species and fossil fuels by Stacey Althaus A dissertation submitted to the graduate faculty in partial fulfillment of the requirements for the degree of DOCTOR OF PHILOSOPHY Major: Physical Chemistry Specialization: Instrumentation Program of Study Committee: Marek Pruski, Co-major Professor Aaron Sadow, Co-major Professor Igor Slowing Theresa Windus Wenyu Huang Iowa State University Ames, Iowa 2014 Copyright © Stacey Althaus, 2014. All rights reserved. ii TABLE -
Surface Pro Et Surface Pro 2 Guide De L'utilisateur
Surface Pro et Surface Pro 2 Guide de l’utilisateur Avec Windows 8.1 Professionnel Date de publication : Octobre 2013 Version 2.0 © 2013 Microsoft. Tous droits réservés. BlueTrack Technology, ClearType, Excel, Hotmail, Internet Explorer, Microsoft, OneNote, Outlook, PowerPoint, SkyDrive, Windows, Xbox et Xbox Live sont des marques déposées de Microsoft Corporation. Surface, Skype et Wedge sont des marques commerciales de Microsoft Corporation. Bluetooth est une marque déposée de Bluetooth SIG, Inc. Dolby et le symbole double-D sont des marques déposées de Dolby Laboratories. Ce document est fourni « en l’état ». Les informations contenues dans ce document, y compris les URL et d’autres références à des sites Web Internet, sont susceptibles d’être modifiées sans préavis. © 2013 Microsoft Page ii Sommaire DECOUVREZ SURFACE PRO ............................................................................................................................................1 À PROPOS DE CE GUIDE ........................................................................................................................................................................................ 1 CARACTERISTIQUES DE SURFACE PRO ................................................................................................................................................................ 2 CONFIGURATION DE VOTRE SURFACE PRO ................................................................................................................5 BRANCHEMENT ET ALLUMAGE ............................................................................................................................................................................ -

70-347.Microsoft
70-347.microsoft Number : 70-347 Passing Score : 800 Time Limit : 120 min https://www.gratisexam.com/ Sections 1. Manage clients and end-user devices 2. Provision SharePoint Online site collections 3. Configure Exchange Online and Lync Online for end users 4. Plan for Exchange Online and Lync Online https://www.gratisexam.com/ Exam A QUESTION 1 DRAG DROP You are the Office 365 administrator for a company. Employees are allowed to purchase a desktop computer of their choosing. The company’s owner has one desktop computer, two laptop computers, one Surface RT device, and 2 Surface Pro 2 devices. You plan to deploy Office ProPlus. You provide each user with an Office 365 ProPlus license. You need to deploy Office 365 ProPlus to the unlicensed devices using the fewest number of licenses possible. https://www.gratisexam.com/ What should you do? To answer, move the appropriate license to the correct device. Each license may be used once, more than once, or not at all. You may need to drag the split bar between panes or scroll to view content. Select and Place: https://www.gratisexam.com/ Correct Answer: https://www.gratisexam.com/ Section: Manage clients and end-user devices Explanation Explanation/Reference: Explanation: Each Office 365 ProPlus license allows a user to install Office on up to five computers. If the user decides to install Office 365 ProPlus on a sixth computer, she will need to deactivate one of the first five. References: https://technet.microsoft.com/en-us/library/gg982959.aspx QUESTION 2 HOTSPOT https://www.gratisexam.com/ Contoso, Ltd., has an Office 365 tenant. -

2013 Oct 18 Surface 2 GA
Surface Reviewers Guide September 2013 Say hello to Surface 2 and Surface Pro 2. Do. More. For more information, press only: Jordan Guthmann Waggener Edstrom Worldwide (512) 527-7032 [email protected] The next generation of Surface Meet Surface 2: Thinner, lighter and faster. Surface 2 is always-on, and ready to go. Surface features Surface 2 features Dimensions: 10.81 x 6.77 x 0.37 in Dimensions: 10.81 x 6.79 x 0.35 in Weight: 1.5 lbs Weight: Less than 1.49 lbs Color: Dark Titanium Color: Magnesium (Silver) ClearType HD 10.6” touchscreen (720p resolution, ClearType Full HD 10.6” touchscreen (1080p, 1366x768 pixels). 5-point multi-touch. 1920x1080 pixels). 5-point multi-touch. NVIDIA Tegra 3 Processor with 2GB RAM Super-fast NVIDIA Tegra 4 Processor (1.7 GHz Quad Core) with 2GB RAM Office Home & Student 2013 RT (Word, Excel, Be truly productive with Office Home & Student PowerPoint, and OneNote) 2013 RT. Now with Outlook 2013 RT, manage your email, calendar, and to-do list. Up to 8 hours of battery life Longer battery. Up to 10 hours of active-use battery life on a single charge. (Ten hours of battery life tested using video playback feature.) Full-size USB 2.0 port Transfer files up to 4X faster and charge accessories with the full-size USB 3.0 port. Two 720p HD cameras Improved cameras. The front and rear-facing cameras are perfect for making calls with Skype, recording 1080p HD video, and snapping pictures. The 3.5MP front-facing camera and the 5MP rear- facing camera both feature improved low-light performance. -

Windows® 8 and RT
Getting started with Windows® 8 and RT You can use the OverDrive app to get eBooks, audiobooks, streaming videos, and periodicals from your library on your Windows 8 or RT device. Windows 8 comes on tablets and computers, and Windows RT comes on tablets like the Microsoft Surface RT and Surface 2. Note: Some digital formats may not be available from all libraries. Step 1 Install the OverDrive app from the Windows Store. Step 2 Open the OverDrive app and follow the prompts to create an OverDrive account and log in. If you’re under 13, select I am under 13 years old instead. Step 3 In the OverDrive app, select the Add a library button, then follow the prompts to find your library’s OverDrive website. • Once you find it, swipe down (or right click) on your library to save it to your “My libraries” list. • Click or tap your library’s name to start browsing. Step 4 Log into your library’s OverDrive website with your library card and borrow a title. Note: Magazines and newspapers work a little differently than other digital titles. They have a Send to NOOK app button instead of a Borrow button, and to read them, you’ll need to install the NOOK reading app from the Windows Store. See our “getting started with periodicals” guide for more help. Step 5 Find borrowed titles under your account on your library’s OverDrive website. You can: • Download EPUB eBooks* and MP3 audiobooks directly to the OverDrive app. • Select Play to play streaming videos right in your browser. -
2-In-1 Accessory Kit for Surface and Surface Pro
2-in-1 Accessory Kit for Surface and Surface Pro Product ID: MSTS3MDPUGBK Get more from your Microsoft Surface™ Pro 4 or Surface Book (backward compatible with Surface Pro 3, Surface 3 and Surface Pro 2) by adding HDMI® and VGA video compatibility as well as wired network connectivity. Connect your Surface to virtually any display You can maximize the versatility of your Microsoft Surface by ensuring that you can connect to virtually any monitor, projector or television. This accessory kit ensures that you're ready to connect to any HDMI or VGA display using the Mini DisplayPort output on your Surface Pro 4, Surface Pro 3 or Surface 3 making it the perfect solution when you're traveling between boardrooms, home and remote offices, trade-shows, hotels and conference centers. Hard-wire your network connection Get the speed and reliability of a hardwired Ethernet connection with your Surface Pro 4. This Surface accessory kit includes a reliable USB 3.0 to Gigabit Ethernet adapter, which adds wired network support that's ideal for BYOD hot-desking, or use as an on-the-go dock solution to enhance your workstation. www.startech.com 1 800 265 1844 The adapter also includes an extra USB 3.0 port built-in, so you can add a USB peripheral device, such as a flash drive for added storage, or a mouse for increased control. Maximize portability Your Microsoft Surface is one of the most versatile and portable computers in the world. Don't be tied down by accessories that require an external power adapter, or a bulky housing. -
Surface Pro User Guide
Surface Pro y Surface Pro 2 Manual del usuario Con el software Windows 8.1 Pro Fecha de publicación: enero de 2014 Versión 2.0 © 2014 Microsoft. Todos los derechos reservados. BlueTrack Technology, ClearType, Excel, Hotmail, Internet Explorer, Microsoft, OneNote, Outlook, PowerPoint, SkyDrive, Windows, Xbox y Xbox Live son marcas registradas de Microsoft Corporation. Surface, Skype y Wedge son marcas comerciales de Microsoft Corporation. Bluetooth es una marca comercial registrada de Bluetooth SIG, Inc. Dolby y el símbolo de doble D son marcas comerciales registradas de Dolby Laboratories. Este documento se proporciona "tal cual". La información que contiene este documento, incluidas las direcciones URL y otras referencias de sitios web de Internet, puede cambiar sin previo aviso. © 2014 Microsoft Página ii Contenido INTRODUCCIÓN A SURFACE PRO .................................................................................................................................1 ACERCA DE ESTE MANUAL .................................................................................................................................................................................... 1 CARACTERÍSTICAS DE SURFACE PRO ................................................................................................................................................................... 2 CONFIGURACIÓN DE SURFACE PRO .............................................................................................................................5 CONEXIÓN Y ENCENDIDO -

Troubleshooting Guide
Troubleshooting guide Troubleshoot Surface Dock and docking stations Note Some products might not be available in your country or region. If you’re having trouble getting your Surface Dock or docking station working with your Surface, here's help. Before you begin troubleshooting First, to make sure your Surface is working properly, get the latest updates. For more info, see Install Surface and Windows updates. Once you have updated your Surface and if you still need help, determine which dock you have and follow the steps for that model. If your dock looks like the one below, follow the steps If your dock looks like the one below, follow the steps in the in the Troubleshoot docking Troubleshoot Surface Dock section. stations for Surface Pro (original), Pro 2, Pro 3 and Surface 3 section. Troubleshoot Surface Dock Surface Dock isn't connecting to your external monitor Update your Surface Dock Surface isn't charging while connected to Surface Dock Audio problems while connected to the Surface dock Surface Dock isn't connecting to your external monitor If your monitor won’t project to a second screen, check your display adapter. Adapters released with Surface Pro 4 and Surface Book are compatible with Surface Dock. Note Legacy adapters released with Surface 3, Surface Pro 3, and previous devices are not compatible with Surface Dock. Adapters released with Surface Pro 4 and Surface Book are compatible with Surface Dock. If your legacy adapter won’t fit in your Surface Dock due to the angle of the connector, replace that adapter if you want to use an external monitor. -
Surface Pro and Surface Pro 2 User Guide with Windows 8.1 Pro Software
Surface Pro and Surface Pro 2 User Guide With Windows 8.1 Pro Software Published: March 2014 Version 2.0 © 2014 Microsoft. All rights reserved. BlueTrack Technology, ClearType, Excel, Hotmail, Internet Explorer, Microsoft, OneNote, Outlook, PowerPoint, OneDrive, Windows, Xbox, and Xbox Live are registered trademarks of Microsoft Corporation. Surface, Skype, and Wedge are trademarks of Microsoft Corporation. Bluetooth is a registered trademark of Bluetooth SIG, Inc. Dolby and the double-D symbol are registered trademarks of Dolby Laboratories. This document is provided “as-is.” Information in this document, including URL and other Internet Web site references, may change without notice. © 2014 Microsoft Page ii Contents MEET SURFACE PRO ........................................................................................................................................................1 ABOUT THIS GUIDE ................................................................................................................................................................................................ 1 SURFACE PRO FEATURES ....................................................................................................................................................................................... 2 SET UP YOUR SURFACE PRO ..........................................................................................................................................5 PLUG IN AND TURN ON ....................................................................................................................................................................................... -
Creating Mobile Apps with Xamarin.Forms
PREVIEW EDITION This excerpt provides early content from a book currently in development and is still in draft format. See additional notice below. PUBLISHED BY Microsoft Press A Division of Microsoft Corporation One Microsoft Way Redmond, Washington 98052-6399 Copyright © 2014 Xamarin, Inc. All rights reserved. No part of the contents of this book may be reproduced or transmitted in any form or by any means without the written permission of the publisher. ISBN: 978-0-7356-9725-6 Microsoft Press books are available through booksellers and distributors worldwide. Please tell us what you think of this book at http://aka.ms/tellpress. This document is provided for informational purposes only and Microsoft makes no warranties, either express or implied, in this document. Information in this document, including URL and other Internet website references, is subject to change without notice. The entire risk of the use or the results from the use of this document remains with the user. This ERRNH[SUHVVHVWKHDXWKRU·s views and opinions. The information contained in this book is provided without any express, statutory, or implied warranties. Neither the authors, Microsoft Corporation, nor its resellers, or distributors will be held liable for any damages caused or alleged to be caused either directly or indirectly by this book. Complying with all applicable copyright laws is the responsibility of the user. Without limiting the rights under copyright, no part of this document may be reproduced, stored in or introduced into a retrieval system, or transmitted in any form or by any means (electronic, mechanical, photocopying, recording, or otherwise), or for any purpose, without the express written permission of Microsoft Corporation. -
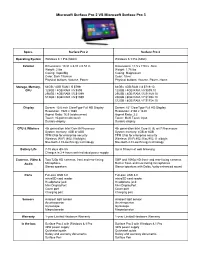
Microsoft Surface Pro 2 VS Microsoft Surface Pro 3
Microsoft Surface Pro 2 VS Microsoft Surface Pro 3 Specs Surface Pro 2 Surface Pro 3 Operating System Windows 8.1 Pro (64bit) Windows 8.1 Pro (64bit) Exterior Dimensions: 10.81 x 6.81 x 0.53 in Dimensions: 11.5 x 7.93 x .36 in Weight: 2 lbs Weight: 1.76 lbs Casing: VaporMg Casing: Magnesium Color: Dark Titanium Color: Silver Physical buttons: Volume, Power Physical buttons: Volume, Power, Home Storage, Memory, 64GB / 4GB RAM / i5 $799 64GB / 4GB RAM / i3 $719.10 CPU 128GB / 4GB RAM / i5 $899 128GB / 4GB RAM / i5 $899.10 256GB / 8GB RAM / i5 $1099 256GB / 8GB RAM / i5 $1169.10 512GB / 8GB RAM / i5 $1599 256GB / 8GB RAM / i7 $1394.10 512GB / 8GB RAM / i7 $1754.10 Display Screen: 10.6 inch ClearType Full HD Display Screen: 12" ClearType Full HD Display Resolution: 1920 x 1080 Resolution: 2160 x 1440 Aspect Ratio: 16:9 (widescreen) Aspect Ratio: 3:2 Touch: 10point multitouch Touch: Multi Touch input Durable display Durable display CPU & Wireless 4th generation Intel Core i5 Processor 4th generation Intel Core i3, i5, or i7 Processors System memory: 4GB or 8GB System memory: 4GB or 8GB TPM Chip for enterprise security TPM Chip for enterprise security Wireless: WiFi (802.11a/b/g/n) Wireless: WiFi 802.11ac/802.11 a/b/g/n Bluetooth 4.0 Low Energy technology Bluetooth 4.0 Low Energy technology Battery Life 715 days idle life Up to 9 hours of web browsing Charges in 24 hours with included power supply Cameras, Video & Two 720p HD cameras, front and rearfacing 5MP and 1080p HD front and rearfacing cameras Audio Microphone Builtin front