Comptia Security+ SY0-501
Total Page:16
File Type:pdf, Size:1020Kb
Load more
Recommended publications
-

Bibliography
Bibliography [1] M Aamir Ali, B Arief, M Emms, A van Moorsel, “Does the Online Card Payment Landscape Unwittingly Facilitate Fraud?” IEEE Security & Pri- vacy Magazine (2017) [2] M Abadi, RM Needham, “Prudent Engineering Practice for Cryptographic Protocols”, IEEE Transactions on Software Engineering v 22 no 1 (Jan 96) pp 6–15; also as DEC SRC Research Report no 125 (June 1 1994) [3] A Abbasi, HC Chen, “Visualizing Authorship for Identification”, in ISI 2006, LNCS 3975 pp 60–71 [4] H Abelson, RJ Anderson, SM Bellovin, J Benaloh, M Blaze, W Diffie, J Gilmore, PG Neumann, RL Rivest, JI Schiller, B Schneier, “The Risks of Key Recovery, Key Escrow, and Trusted Third-Party Encryption”, in World Wide Web Journal v 2 no 3 (Summer 1997) pp 241–257 [5] H Abelson, RJ Anderson, SM Bellovin, J Benaloh, M Blaze, W Diffie, J Gilmore, M Green, PG Neumann, RL Rivest, JI Schiller, B Schneier, M Specter, D Weizmann, “Keys Under Doormats: Mandating insecurity by requiring government access to all data and communications”, MIT CSAIL Tech Report 2015-026 (July 6, 2015); abridged version in Communications of the ACM v 58 no 10 (Oct 2015) [6] M Abrahms, “What Terrorists Really Want”,International Security v 32 no 4 (2008) pp 78–105 [7] M Abrahms, J Weiss, “Malicious Control System Cyber Security Attack Case Study – Maroochy Water Services, Australia”, ACSAC 2008 [8] A Abulafia, S Brown, S Abramovich-Bar, “A Fraudulent Case Involving Novel Ink Eradication Methods”, in Journal of Forensic Sciences v41(1996) pp 300-302 [9] DG Abraham, GM Dolan, GP Double, JV Stevens, -

Bots and Botnets: Risks, Issues and Prevention
EMEA MSSD The Journey, So Far: Trends, Graphs and Statistics Martin Overton, IBM UK 20th September 2007 | Author: Martin Overton © 2007 IBM Corporation EMEA MSSD Agenda . The ‘First’ IBM PC Virus . Statistics, 80’s . Statistics, 90’s . Statistics, 00’s . Malware Myth-busting . Putting it all Together . Conclusions . Questions The Journey, So Far: Trends, Graphs and Statistics | Martin Overton © 2007 IBM Corporation EMEA MSSD Disclaimer . Products or services mentioned in this presentation are included for information only. Products and/or services listed, mentioned or referenced in any way do not constitute any form of recommendation or endorsement by IBM or the presenter. All trademarks and copyrights are acknowledged. The Journey, So Far: Trends, Graphs and Statistics | Martin Overton © 2007 IBM Corporation EMEA MSSD Brain . The very first malware written for the IBM PC [and clones] used ‘stealth’ to hide its presence[1]: . Here is a short extract from the description of Brain from F-Secure explaining how the stealth function it used works: . “The Brain virus tries to hide from detection by hooking into INT 13. When an attempt is made to read an infected boot sector, Brain will just show you the original boot sector instead. This means that if you look at the boot sector using DEBUG or any similar program, everything will look normal, if the virus is active in memory. This means the virus is the first "stealth" virus as well.” [1] Source : http://www.research.ibm.com/antivirus/timeline.htm [2] More data can be found here : http://www.f-secure.com/v-descs/brain.shtml -

Bibliography
Bibliography [1] M Aamir Ali, B Arief, M Emms, A van Moorsel, “Does the Online Card Payment Landscape Unwittingly Facilitate Fraud?” IEEE Security & Pri- vacy Magazine (2017) [2] M Abadi, RM Needham, “Prudent Engineering Practice for Cryptographic Protocols”, IEEE Transactions on Software Engineering v 22 no 1 (Jan 96) pp 6–15; also as DEC SRC Research Report no 125 (June 1 1994) [3] A Abbasi, HC Chen, “Visualizing Authorship for Identification”, in ISI 2006, LNCS 3975 pp 60–71 [4] H Abelson, RJ Anderson, SM Bellovin, J Benaloh, M Blaze, W Diffie, J Gilmore, PG Neumann, RL Rivest, JI Schiller, B Schneier, “The Risks of Key Recovery, Key Escrow, and Trusted Third-Party Encryption”, in World Wide Web Journal v 2 no 3 (Summer 1997) pp 241–257 [5] H Abelson, RJ Anderson, SM Bellovin, J Benaloh, M Blaze, W Diffie, J Gilmore, M Green, PG Neumann, RL Rivest, JI Schiller, B Schneier, M Specter, D Weizmann, “Keys Under Doormats: Mandating insecurity by requiring government access to all data and communications”, MIT CSAIL Tech Report 2015-026 (July 6, 2015); abridged version in Communications of the ACM v 58 no 10 (Oct 2015) [6] M Abrahms, “What Terrorists Really Want”,International Security v 32 no 4 (2008) pp 78–105 [7] M Abrahms, J Weiss, “Malicious Control System Cyber Security Attack Case Study – Maroochy Water Services, Australia”, ACSAC 2008 [8] A Abulafia, S Brown, S Abramovich-Bar, “A Fraudulent Case Involving Novel Ink Eradication Methods”, in Journal of Forensic Sciences v41(1996) pp 300-302 [9] DG Abraham, GM Dolan, GP Double, JV Stevens, -
The Advanced Persistent Threat (Or Informa�Onized Force Opera�Ons)
The Advanced Persistent Threat (or Informaonized Force Operaons) Michael K. Daly November 4, 2009 What is meant by Advanced, Persistent Threat? . Increasingly sophiscated cyber aacks by hosle organizaons with the goal of: Gaining access to defense, financial and other targeted informaon from governments, corporaons and individuals. Maintaining a foothold in these environments to enable future use and control. Modifying data to disrupt performance in their targets. APT: People With Money Who Discovered That Computers Are Connected APT in the News A Broad Problem Affecng Many Naons and Industries Is this a big deal? Is it new? . Yes, this is a very big deal. If “it” is the broad noon of the, spying, social engineering and bad stuff, then No, it is definitely not new. However, it is new (~2003) that naon states are widely leveraging the Internet to operate agents across all crical infrastructures. APT acvity is leveraging the expansion of the greater system of systems I’m not in the military. Why do I care? “[APT] possess the targeting competence to identify specific users in a unit or organization based on job function or presumed access to information. [APT] can use this access for passive monitoring of network traffic for intelligence collection purposes. Instrumenting these machines in peacetime may enable attackers to prepare a reserve of compromised machines that can be used during a crisis. [APT] … possess the technical sophistication to craft and upload rootkit and covert remote access software, creating deep persistent access to the -

An Encrypted Payload Protocol and Target-Side Scripting Engine
An Encrypted Payload Protocol and Target-Side Scripting Engine Dino A. Dai Zovi [email protected] Abstract into the remote process and then triggering the vulnera- Modern exploit payloads in commercial and open-source bility (the injection vector) in order to cause the remote penetration testing frameworks have grown much more process to execute the injected code (the payload). Tra- advanced than the traditional shellcode they replaced. ditionally, these payloads have been written in processor- These payloads permit interactive access without launch- specific assembly language, assembled, and extracted by ing a shell, network proxying, and many other rich fea- hand into reusable machine code components. These tures. Available payload frameworks have several lim- payloads were typically small and executed an operating itations, however. They make little use of encryption to system shell, causing them to be commonly referred to secure delivery and communications, especially in earlier as shellcode. Common shellcode variants included func- stage payloads. In addition, their richer features require tionality such as restoring dropped privileges, breaking a constant network connection to the penetration tester, out of chroot environments, and attaching the shell to making them unsuitable against mobile clients, such as an inbound or outbound network connection. This style laptops, PDAs, and smart phones. of payload construction was both labor and skill inten- This work introduces a first-stage exploit payload that sive. is able to securely establish an encrypted channel using With the growth of commercial penetration testing ElGamal key agreement and the RC4 stream cipher. The services and especially commercial penetration test- key agreement implementation requires only modular ing products, exploit payloads have gotten considerably exponentiation and RC4 also lends itself to an implemen- more capable and complex. -

Lifecycle of the Advanced Persistent Threat
Lifecycle of the Advanced Persistent Threat Counter Threat Unit research Table of Contents Summary .............................................................. 2 Background: Who, not what ......................................... 3 Organized .................................................................... 3 Efficient ...................................................................... 3 Tenacious .................................................................... 4 APT Lifecycle ......................................................... 5 Preparation .................................................................. 6 Initial intrusion .............................................................. 6 Primary Objective .................................................... 9 Expansion .................................................................... 9 Persistence ................................................................. 11 Search and Exfiltration .................................................... 12 Cleanup ...................................................................... 14 Conclusion .......................................................... 15 Copyright © 2012 Dell SecureWorks Page 1 Summary Advanced Persistent Threats (APT) are a serious concern in the today’s threat landscape. They represent a threat to an organization’s intellectual property, financial assets and reputation. In some cases, these threats target critical infrastructure and government suppliers, thereby threatening the victim country’s national -
Characteristics of a Computer Virus
We Are The Devils Of Your Computer System A Computer Virus is a program that may disturb the normal working of a computer. CHARACTERISTICS OF A COMPUTER VIRUS: ● the ability to replicate itself. ● the ability to attach itself to another computer file. For fun Release anger Take revenge For fame Antivirus market Disrupt enemy’s information and network The term "computer virus" is often used incorrectly as a catch-all phrase to include all types of Malware such as Computer Worms, Spyware, Adware, and Root kits - all of which are slightly different than Computer Viruses. What is Malware? ● Malware is a general name for all programs that are harmful: ● Virus ● Trojan Horse ● Spyware ● Adware ● Rootkits VIRUS: A computer virus is a small program written to alter the way a computer operates, without the permission or knowledge of the user. With an ability to replicate itself, thus continuing to spread. Also, known as Malicious Software, a program that can cause damage to a computer. •Boot sector virus •Master Boot Record (MBR) virus •File infector virus •Multipartite virus •Macro virus BOOT SECTOR VIRUS: Boot sector viruses generally hide in the boot sector, either in the bootable disk or the hard drive. It attaches itself to the primary active partition of the hard disk that is read by the computer upon boot up. MASTER BOOT RECORD VIRUS: MBR viruses are memory-resident viruses that infect disks in the same manner as boot sector viruses. However it, infects the MBR of the system, gets activated when the BIOS activates the Master boot code. MBR infectors normally save a legitimate copy of the master boot record in an different location. -
T-AIMD-99-146 Information Security: the Melissa Computer Virus
United States General Accounting Office Testimony GAO Before the Subcommittee on Technology, Committee on Science, House of Representatives For Release on Delivery Expected at 10 a.m. INFORMATION SECURITY Thursday, April 15, 1999 The Melissa Computer Virus Demonstrates Urgent Need for Stronger Protection Over Systems and Sensitive Data Statement of Keith A. Rhodes Technical Director for Computers and Telecommunications Accounting and Information Management Division GAO/T-AIMD-99-146 Madam Chairwoman and Members of the Subcommittee: Thank you for inviting me to participate in todays hearing on the Melissa computer virus. Although it did disrupt the operations of thousands of companies and some government agencies, this virus did not reportedly permanently damage systems and did not compromise sensitive government data. Nevertheless, it has shown us just how quickly computer viruses can spread and just how vulnerable federal information systems are to computer attacks. Moreover, Melissa has clearly highlighted the urgent and serious need for stronger agency and governmentwide protection over sensitive data. Today, I will discuss the immediate effects of the Melissa virus and variations of it as well as its broader implications. I will also discuss some critical measures that should be taken to help ensure that federal departments and agencies are better prepared for future viruses and other forms of attack. Melissa is a macro virus that can affect users of Microsofts Word 1 97 or The Melissa Virus and Word 2000. Macro viruses are computer viruses that use an applications Its Immediate Impact own macro programming language2 to reproduce themselves. Macro viruses can inflict damage to the document or to other computer software. -

Data Thieves: the Motivations of Cyber Threat Actors and Their Use
Testimony Data Thieves The Motivations of Cyber Threat Actors and Their Use and Monetization of Stolen Data Lillian Ablon CT-490 Testimony presented before the House Financial Services Committee, Subcommittee on Terrorism and Illicit Finance, on March 15, 2018. For more information on this publication, visit www.rand.org/pubs/testimonies/CT490.html Testimonies RAND testimonies record testimony presented or submitted by RAND associates to federal, state, or local legislative committees; government-appointed commissions and panels; and private review and oversight bodies. Published by the RAND Corporation, Santa Monica, Calif. © Copyright 2018 RAND Corporation is a registered trademark. Limited Print and Electronic Distribution Rights This document and trademark(s) contained herein are protected by law. This representation of RAND intellectual property is provided for noncommercial use only. Unauthorized posting of this publication online is prohibited. Permission is given to duplicate this document for personal use only, as long as it is unaltered and complete. Permission is required from RAND to reproduce, or reuse in another form, any of its research documents for commercial use. For information on reprint and linking permissions, please visit www.rand.org/pubs/permissions.html. www.rand.org Data Thieves: The Motivations of Cyber Threat Actors and Their Use and Monetization of Stolen Data Testimony of Lillian Ablon1 The RAND Corporation2 Before the Committee on Financial Services Subcommittee on Terrorism and Illicit Finance United States House of Representatives March 15, 2018 ood afternoon, Chairman Pearce, Ranking Member Perlmutter, and distinguished members of the subcommittee. Thank you for the invitation to testify at this important G hearing, “After the Breach: the Monetization and Illicit Use of Stolen Data.” Cybersecurity is a constant and growing challenge. -

Effect of Payload Virus As Threatening for Internet Security
International Journal of Modern Communication Technologies & Research (IJMCTR) ISSN: 2321-0850, Volume-2, Issue-9, September 2014 Effect of Payload Virus as Threatening For Internet Security Sana Mahmoud Eltayeb Almansour, Dr.Amin Babekir Abd elnabi Mustafa can really bypass security borders , stay in the victim devise or Abstract– Security remains at the top concerns of internet spread in the network without being noticed . usage despite this continuous effort of security engineers to make the Internet as safe as possible, the level of threats II. PAYLOAD:- continues to grow. Hackers are getting better and quicker every day, while In order to define payload it is best explained through the security programming companies do their best to stay the definition of vulnerability and exploit. A particular server, winner of the race. It is an everlasting fight against hacker and website or application is vulnerable when it can be intruders who are trying to breach the safety and privacy of compromised or overtaken by A hacker. their victim whom could be someone using the Internet. Now that we know that a particular application is vulnerable, In this paper one of the current, dangerous most effective we need to find an exploit for that vulnerability, which might method will be discussed, explaining how what is a payload, how be the piece of code, to overtake the victim's application it works, exploits, and the intrusion process, most definitely security precision needs to be taken. without prior authorization. To go further I need a tool, virus or Trojan sent along with the exploit, to be executed on the Index Terms– Payload, Hacking, Internet Security, Victim. -
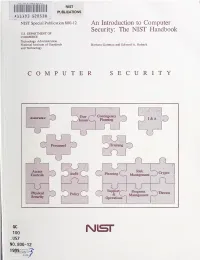
An Introduction to Computer Security: the NIST Handbook U.S
HATl INST. OF STAND & TECH R.I.C. NIST PUBLICATIONS AlllOB SEDS3fl NIST Special Publication 800-12 An Introduction to Computer Security: The NIST Handbook U.S. DEPARTMENT OF COMMERCE Technology Administration National Institute of Standards Barbara Guttman and Edward A. Roback and Technology COMPUTER SECURITY Contingency Assurance User 1) Issues Planniii^ I&A Personnel Trairang f Access Risk Audit Planning ) Crypto \ Controls O Managen»nt U ^ J Support/-"^ Program Kiysfcal ~^Tiireats Policy & v_ Management Security Operations i QC 100 Nisr .U57 NO. 800-12 1995 The National Institute of Standards and Technology was established in 1988 by Congress to "assist industry in the development of technology . needed to improve product quality, to modernize manufacturing processes, to ensure product reliability . and to facilitate rapid commercialization ... of products based on new scientific discoveries." NIST, originally founded as the National Bureau of Standards in 1901, works to strengthen U.S. industry's competitiveness; advance science and engineering; and improve public health, safety, and the environment. One of the agency's basic functions is to develop, maintain, and retain custody of the national standards of measurement, and provide the means and methods for comparing standards used in science, engineering, manufacturing, commerce, industry, and education with the standards adopted or recognized by the Federal Government. As an agency of the U.S. Commerce Department's Technology Administration, NIST conducts basic and applied research in the physical sciences and engineering, and develops measurement techniques, test methods, standards, and related services. The Institute does generic and precompetitive work on new and advanced technologies. NIST's research facilities are located at Gaithersburg, MD 20899, and at Boulder, CO 80303. -

Cyber Risk – Common Threats Part 1 of 2
Cyber Risk – Common Threats Part 1 of 2 Table of Contents Threats to Information Systems ..................................................................................................... 2 Malware .......................................................................................................................................... 4 Viruses ............................................................................................................................................. 5 Virus Examples ................................................................................................................................ 6 Worms ............................................................................................................................................. 8 Brief Virus and Worm History ......................................................................................................... 9 Downloaders ................................................................................................................................. 11 Attack Scripts ................................................................................................................................ 13 Botnet -1 ....................................................................................................................................... 15 Botnet -2 ....................................................................................................................................... 17 IRCBotnet Example ......................................................................................................................