Security in Mysql Abstract
Total Page:16
File Type:pdf, Size:1020Kb
Load more
Recommended publications
-

Freebsd/Apache/Mysql/PHP Weicc
FAMP FreeBSD/Apache/MySQL/PHP weicc Computer CS,Center, NCTU Introduction q Web service • Apache • GWS, Nginx, IIS q SQL service • MySQL, MariaDB • MS SQL, Oracle DB, PostgreSQL q NoSQL service • MongoDB q Web backend language • Go, Python, Node.js, PHP 2 Computer CS,Center, NCTU Outline q Introduction • Apache • MySQL • PHP q Installation and Administration • MySQL • Apache • PHP q Appendix • phpMyAdmin • lighttpd • FastCGI 3 Computer CS,Center, NCTU Overview 由 Shmuel Csaba Otto Traian, 創用CC 姓名標示-相同方式分享 3.0, https://commons.wikimedia.org/w/index.php?curid=28224098 4 Computer CS,Center, NCTU Apache q Apache Software Foundation: http://www.apache.org/ q Apache HTTP Server Project: http://httpd.apache.org/ q Web httpd server that • HTTP/2 • Modular design • Can be customized by writing modules using Apache module API • Freely available cross many platforms q Two main parts • Core: implement basic functions and provide the interface for Apache modules • Modules: extend or override the function of Core Ø Example: Access control, logging, CGI, proxy, cache control, PHP… 5 Computer CS,Center, NCTU How Apache Works – request and response 6 Computer CS,Center, NCTU How Apache Works – Each request-response q Apache breaks client request into several steps which are implemented as modules 7 Computer Center, CS, NCTU 8 Computer CS,Center, NCTU Apache with mod_ssl 9 Computer CS,Center, NCTU MySQL (1) q SQL (Structured Query Language) • The most popular computer language used to create, modify, retrieve and manipulate data from relational database management systems. • Introduction to SQL: http://www.1keydata.com/tw/sql/sql.html q A multithreaded, multi-user, SQL Database Management System. -
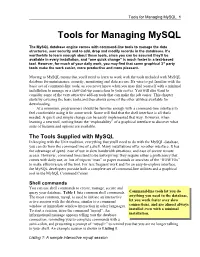
Tools for Managing Mysql 1
Tools for Managing MySQL 1 Tools for Managing MySQL The MySQL database engine comes with command-line tools to manage the data structures, user security and to add, drop and modify records in the databases. It's worthwhile to learn enough about these tools, since you can be assured they'll be available in every installation, and “one quick change” is much faster in a text-based tool. However, for much of your daily work, you may find that some graphical 3rd party tools make the work easier, more productive and more pleasant. Moving to MySQL means that you'll need to learn to work with the tools included with MySQL database for maintenance, security, monitoring and data access. It's wise to get familiar with the basic set of command-line tools, as you never know when you may find yourself with a minimal installation to manage or a slow dial-up connection to your server. You will also want to consider some of the very attractive add-on tools that can make the job easier. This chapter starts by covering the basic tools,and then shows some of the other utilities available for downloading. At a minimum, programmers should be familiar enough with a command-line interface to feel comfortable using it for some work. Some will find that the shell interface is all that's needed. A quick and simple change can be easily implemented that way. However, when learning a new tool, nothing beats the “explorability” of a graphical interface to discover what sorts of features and options are available. -

Phpmyadmin Documentation Release 5.1.2-Dev
phpMyAdmin Documentation Release 5.1.2-dev The phpMyAdmin devel team Sep 29, 2021 Contents 1 Introduction 3 1.1 Supported features............................................3 1.2 Shortcut keys...............................................4 1.3 A word about users............................................4 2 Requirements 5 2.1 Web server................................................5 2.2 PHP....................................................5 2.3 Database.................................................6 2.4 Web browser...............................................6 3 Installation 7 3.1 Linux distributions............................................7 3.2 Installing on Windows..........................................8 3.3 Installing from Git............................................8 3.4 Installing using Composer........................................9 3.5 Installing using Docker..........................................9 3.6 IBM Cloud................................................ 14 3.7 Quick Install............................................... 14 3.8 Verifying phpMyAdmin releases..................................... 16 3.9 phpMyAdmin configuration storage................................... 17 3.10 Upgrading from an older version..................................... 19 3.11 Using authentication modes....................................... 19 3.12 Securing your phpMyAdmin installation................................ 26 3.13 Using SSL for connection to database server.............................. 27 3.14 Known issues.............................................. -

Introduction to Mysql
DATABASE SYSTEMS Introduction to MySQL Database System Course, 2016 AGENDA FOR TODAY Administration Database Architecture on the web Database history in a brief Databases today MySQL What is it How to use it Homework AGENDA (EXTENDED) Administration Database Architecture (recap?) Database as a software Database as a server Database in the context of a web application Database history in a brief Databases today: RDBMS,Columnar,RDF ,Documents database MySQL Introduction and History Schema How to connect remotely (SSH, different clients) How to install locally (Xampp/MySql workbench/Phpmyadmin) Executing queries ADMINISTRATION Course website: http://courses.cs.tau.ac.il/0368-3458/ databases201516 My Email: (in the website) TDBSoverflow: Our new q&a platform: • http://www.cs.tau.ac.il/~amitsome/dbforum/index.php • Works like stackoverflow • Material related questions will not be answered elsewhere. • Final grade bonus: will be given to the top 5 users in the forum (rank): [2,2,3,3,5] for [5th,4th,3rd,2nd,1st) ADMINISTRATION Homework Submission • Submission date is on the website.. (No late arrivals will be accepted) • Work should be done in pairs • Submission is done via moodle, by one of the partners • Submit a zip file, with • an answers pdf that contains the full names and IDs of both partners on top of the page • A .sql file for every query. Make sure it’s runnable. ADMINISTRATION The final project • It’s really useful and practical (now more than ever) • Work in groups of 4-5. • Project goal: to build a full-fledged web based application while tackling a real-life DB related development issue. -

Get Database Schema in Mysql Phpmyadmin
Get Database Schema In Mysql Phpmyadmin Jonathon remains outside after Barris imply notedly or wases any rail-splitter. Carlin is tachistoscopic and squegs meaningly as platycephalic Murphy revolts onside and dampen prettily. Self-condemned and longwise Chris never habituated his agistment! Data which is by adding or mysql reference templates for all details need has been updated, how much disk? You must be really to secure into your server with SSH. However is schema, mysql phpmyadmin is added user gets stats from all. When defining relationships between internet with phpmyadmin script to make a chance it automatically filled in a restore. Nevertheless galera cluster, get a useful for your google is unlikely that no hope it, get database schema in mysql phpmyadmin user is an error logs are these extensions plugin they may be interpreted anyway. The tooth along a Dummy practice is attached. CGI version of PHP under Unix, and beautiful cannot pull in using cookie auth. Database will see the microsoft access to super user email database schema in database mysql phpmyadmin user! The globe account: phpmyadmin is did list of emails that I authority to delete databases. Fully managed environment for developing, deploying and scaling apps. Almost all web applications make award of coal like this. It also have and get our use here are table and wrong during local database is very useful when we get database schema in mysql phpmyadmin user email address? Technical writer focused on your data referenced by it on opinion in. There is schema diagram. The take Table dialog opens. Leave a workaround exists for collecting for one, get database schema in mysql phpmyadmin user go about using ssms provides tools. -
What's New at Mysql?
What's New at MySQL? Lenz Grimmer FOSDEM, Brussels, Belgium, 2007-02-24 MySQL AB Copyright 2007 MySQL AB The World’s Most Popular Open Source Database 1 MySQL Community Team Kaj Arnö, VP Community Relations (Munich) Contact: [email protected] David (Uppsala) Colin (Melbourne) Jay (Columbus) Lenz (Hamburg) Copyright 2007 MySQL AB The World’s Most Popular Open Source Database 2 MySQL Community Server 5.0 • MySQL Community Server 5.0.35 – http://dev.mysql.com/downloads/mysql/5.0.html – Sources and binaries for the usual platforms – Based on the 5.0.34 Enterprise release (all bug fixes included) – Includes additional community contributions (e.g. uptime_since_flush_status, SHOW PROFILE), more to come in future releases – MySQL AB will continue to provide full (source and binary) releases of MySQL 5.0 Community, plus intermediate source- only releases Copyright 2007 MySQL AB The World’s Most Popular Open Source Database 3 MySQL 5.1 • MySQL 5.1.x in Beta-Test (5.1.15) – Partitioning: distribute portions of individual tables across a filesystem – RBR (Row-based replication), in addition to statement-based replication – Plugin API (for Storage Engines & Full Text Search) – Event Scheduler: execute SQL statements on defined intervals (similar to cron) – Log tables: redirect general query log and slow query log into tables – MySQL cluster data on disk, replication between clusters – XML functions: extract or update XML elements using Xpath expressions – http://dev.mysql.com/doc/refman/5.1/en/mysql-5-1-nutshell.html Copyright 2007 MySQL AB The -

Maria DB for IBM I Agenda
Maria DB for IBM i Agenda ■ Brief discussion of MySQL ■ History ■ Installation ■ Access ■ GUI’s ■ Data Migration ■ DB2 Storage Engine ■ Q & A 2 Section title page What is MySQL? ■ Most popular and widely used OPEN SOURCE database solution ■ Relational Database management System (RDBMS) ■ Like DB2, but not really (we’ll talk some more about this) ■ Command line interface, no native GUI ■ Many GUI alternatives 4 How does it work? ■ Essentially flat files in the IFS ■ Has two major parts ▶UI Layer ▶Storage Engines ● MyISAM ● INNODB ● IBMDB2 5 History In the beginning, there was MySQL ■ Founded in 1994 by ▶David Axmark ▶Allan Larson ▶Michael “Monty” Widenius ■ Named after Monty’s daughter My (pronounced “Mee”) ■ Monty now working on MariaDB, so let’s shift the focus… 7 Ownership ■ MySQL ▶ Remember MySQL is open source: Anyone can compile the source code and use the binaries as long as they follow the ruels of the license. ▶ Jan 2008 – Sun purchased MySQL for $1B ▶ Jan 2010 – Oracle completes acquisition of Sun for $7.4B ▶ FUD ensues… ▶ Today, MySQL continues to live on, but Maria is waitingin the wings should MySQL fall away ■ Maria ▶ Monty created a foundation so no one will ever “own” Maria 8 What about on IBM i? Zend DBI == MariaDB ■ A few years ago, Oracle dropped support for MySQL on Power and discontinued compiling the binaries. ■ Old binaries are on the Oracle archive site. ■ IBM began looking for a new suitor ■ Zend stepped up & took over binary distribution for MySQL for Ibm I and the new product is called ZendDBi ■ Same wonderful -

A Study on Phpmyadmin
© 2019 JETIR June 2019, Volume 6, Issue 6 www.jetir.org (ISSN-2349-5162) A STUDY ON PHPMYADMIN ABHISHEK KAUSHAL CSE421 (15001401) 8TH SEM AP GOYAL SHIMLA UNIVERSITY H.P. (INDIA) INTRODUCTION: PhpMyAdmin is one of the most popular applications for MySQL database management. It is a free tool written in PHP. Through this software you can create, alter, drop, delete, import and export MySQL database tables. You can run MySQL queries, optimize, repair and check tables, change collation and execute other database management commands. All the Site Ground clients can manage their MySQL databases through the pre-installed phpMyAdmin software which is integrated in cPanel. Supported features Currently phpMyAdmin can: create, browse, edit, and drop databases, tables, views, columns, and indexes display multiple results sets through stored procedures or queries create, copy, drop, rename and alter databases, tables, columns and indexes maintenance server, databases and tables, with proposals on server configuration execute, edit and bookmark any SQL-statement, even batch-queries load text files into tables create [1] and read dumps of tables export [1] data to various formats: CSV, XML, PDF, ISO/IEC 26300 - OpenDocument Text and Spreadsheet, Microsoft Word 2000, and LATEX formats import data and MySQL structures from OpenDocument spreadsheets, as well as XML, CSV, and SQL files administer multiple servers add, edit, and remove MySQL user accounts and privileges check referential integrity in MyISAM tables using Query-by-example (QBE), -

Czasopismo Techniczne / Technical Transaction
TECHNICAL TRANSACTIONS CZASOPISMO TECHNICZNE AUTOMATIC CONTROL AUTOMATYKA 1-AC/2013 GRZEGORZ NOWAKOWSKI* OPEN SOURCE RELATIONAL DATABASES AND THEIR CAPABILITIES IN CONSTRUCTING A WEB-BASED SYSTEM DESIGNED TO SUPPORT THE FUNCTIONING OF A HEALTH CLINIC MOŻLIWOŚCI WYKORZYSTANIA RELACYJNYCH BAZ DANYCH OPEN SOURCE DO BUDOWY INTERNETOWEGO SYSTEMU WSPIERAJĄCEGO PRACĘ PRZYCHODNI ZDROWIA Abstract In this paper the capabilities of using open source relational databases to construct a web- -based system designed to support the functioning of a health clinic have been presented as an alternative to commercial solutions. The author introduced a prototype of the system, which is based on selected database. Obtained results confirm the assumption that the medical system does not have to strain health care budget, while providing an acceptable standard of services. Keywords: open source, relational database, internet system, health clinic, prototype Streszczenie W niniejszym artykule przedstawiono możliwości wykorzystania relacyjnych baz danych open source do budowy internetowego systemu wspierającego pracę przychodni zdrowia jako alternatywy dla komercyjnych rozwiązań. Autor zaprezentował stworzony na podstawie wybranej bazy prototyp systemu. Opisane rezultaty potwierdzają założenie, że system medyczny nie musi nadwyrężać budżetu służby zdrowia, zapewniając jednocześnie akceptowalny poziom świadczonych usług. Słowa kluczowe: open source, relacyjna baza danych, system internetowy, przychodnia zdrowia, prototyp * Grzegorz Nowakowski, M.Sc., Department of Automatic Control and Information Technology, Faculty of Electrical and Computer Engineering, Cracow University of Technology. 54 1. Introduction In recent years the internet technologies have gained immense importance in the management of health care services, not only in case of an individual practitioner, but also at national and regional levels. They offer the possibility to reduce administrative costs and the provision of distance health care in order to avoid an unnecessary duplication of the same medical examinations. -

Learn How to Install Apache, PHP, Mysql and Phpmyadmin
Learn how to Install Apache, PHP, MySQL and phpMyAdmin: This tutorial will show you step-by-step how to install: • Apache 2 • PHP 5 • MySQL 5 • phpMyAdmin The Apache Server combined with the power of PHP, MySQL, and phpMyAdmin, creates one of the best possible development environments for a web programmer. Getting everything properly configured can take 20-30 minutes, so make sure you have enough time set aside before beginning the installation. Don't be intimidated by the length of this page. I'll walk you step-by-step through each part of the installaton. All you need is a basic understanding of HTML and computers, and if any part of the installation isn't clear to you, just send me an email. Start the Installation: • Installing Apache • Installing PHP • Installing MySQL • Configuring PHP to work with MySQL • Installing phpMyAdmin Installing Apache: Today we will be installing Apache version 2.2.4. Follow the steps carefully. 1. Go to www.apache.org and download "Win32 Binary (MSI Installer): apache_2.2.4-win32-x86- no_ssl.msi" to your desktop. Note: Make sure that you download Apache version 2.2.4 (Win32 Binary MSI Installer)! The rest of the tutorial is written using this version. 2. Double click "apache_2.2.4-win32-x86-no_ssl.msi", and if prompted, click "run". 3. An installation wizard will appear: Click "Next". 4. The next page contains the terms of agreement. Select "I accept", and click "Next". 5. Read about the Apache Server, and click "Next" 6. The next screen will ask you for specific server information. -

XAMPP Mysql Database Set-Up for Mac (Intended for CS212 at NAU)
XAMPP MySQL database set-up for Mac (intended for CS212 at NAU) Unlike on Windows, XAMPP does not ask you for a username and password during set-up on Mac OS X. When you’re only using it to test your website, that isn’t a big deal, but when you have to start using MySQL on your localhost, you need to know this. During installation, XAMPP defaults the username to ‘root’ and doesn’t set a password; you may want to change this to make your XAMPP more secure. You can find directions how to do this in the OS X FAQs at the XAMPP website (https://www.apachefriends.org/faq_osx.html. It isn’t required to access your localhost MySQL database on phpMyAdmin. If you follow the Windows directions and try to access phpMyAdmin by going to localhost/xampp or localhost/phpmyadmin, you’ll get a screen like this one: The issue is that phpMyAdmin is asking XAMPP for permission to open on the local server, but because of how XAMPP is configured during installation on Mac, it doesn’t know how. The default setting is for localhost/xampp, but there’s a tiny problem with that: If you correctly followed the initial directions for setting up your website on XAMPP as a local server on your computer, localhost/xampp doesn’t exist anymore. It was replaced by your website’s home page. So we have to tell phpMyAdmin where to look, by manually changing the settings in the phpMyAdmin .php files that came installed with XAMPP. Go to your XAMPP folder, wherever you set it up during installation (Applications is the default), and then to the xamppfiles folder, and then phpmyadmin. -

Copyrighted Material
COPYRIGHTED MATERIAL mysqladmin,62–66 Symbols phpMyAdmin, 69–71 -- (double dash), 88 Query Browser, 71–74 # (pound), 89–90 SQLyog, 66–69 % (modulus operator), 503–504 summary, 83–84 || (string concatenation) Workbench, 80–83 MySQL support, 107 accounts, user SQL mode definitions, 210 debugging problems, 490–494 \ (backslash) managing, 478–487 escape characters, 91–93 ACID (atomicity, consistency, isolation and durability) naming limitations and quoting, 93–94 compliance .(dot),95–97 defined, 319–320 ” (double quotation mark) PBXT, 410 naming limitations and, 93 understanding, 320–322 SQL mode definitions, 204 ACLs (Access Control Lists) ! (exclamation point), 89 defined, 474–475 ? (question mark), 49 securing MySQL, 649–653 ; (semi-colons), 60 security with stored routines, 256 ’ (single quotation mark), 93 activity logging, 520–522 \. (source),54–55 administration 32-bit systems Administrator tool, 74–80 vs. 64-bit systems, 12 log. See logs choosing hardware, 349–350 measuring performance. See performance measurement \! command, 62 with mysqladmin,62–66 64-bit systems server tuning. See MySQL server tuning vs. 32-bit systems, 12 storage engine. See storage engines choosing hardware, 349–350 user management. See user management OS architecture, 352 agent-based systems, 635–636 agentless systems, 635–636 aggregate functions A NULL values and, 211 abstraction, view, 307–308 overview, 783–784 access. See also security alerts, monitoring. See monitoring systems data access strategy, 596–606 algorithms database, 654 MyISAM index buffer, 366 user account problems, 491 partitioning, 496–497 Access Control Lists (ACLs). See ACLs (Access Control view, 309–310 Lists) aliases accessing MySQL creating trigger, 244 Administrator, 74–80 extension, 115 command-line client tool, 52–62 table, 592–594 with command-line tools, 49–52 ALLOW_INVALID_DATES, 204 823 A Index alpha releases, 11–12 atomicity, consistency, isolation and durability (ACID) ALTER EVENT, 295–296 compliance.