Internet Toolkit User Manual
Total Page:16
File Type:pdf, Size:1020Kb
Load more
Recommended publications
-

Federal Implementation Guideline for Electronic Data Interchange
NIST RESEARCH LIBRARY NIST Special Publication 881-38 APR 6 " 1998 Federal Implementation Guideline for Electronic Data Interchange ASC X12 Version/Release 003070 FEDERAL CONVENTIONS FOR USING ASC XI 2 TRANSACTION SETS Implementation Convention Nisr U.S. DEPARTMENT OF COMMERCE Technology Administration National Institute of Standards and Technology rhe National Institute of Standards and Technology was established in 1988 by Congress to "assist industry in the development of technology . , . needed to improve product quality, to modernize manufacturing processes, to ensure product reliability . and to facilitate rapid commercialization ... of products based on new scientific discoveries." NIST, originally founded as the National Bureau of Standards in 1901, works to strengthen U.S. industry's competitiveness; advance science and engineering; and improve public health, safety, and the environment. One of the agency's basic functions is to develop, maintain, and retain custody of the national standards of measurement, and provide the means and methods for comparing standards used in science, engineering, manufacturing, commerce, industry, and education with the standards adopted or recognized by the Federal Government. As an agency of the U.S. Commerce Department's Technology Administration, NIST conducts basic and applied research in the physical sciences and engineering, and develops measurement techniques, test methods, standards, and related services. The Institute does generic and precompetitive work on new and advanced technologies. -
Spectrum Reference Manual
Apple® IIGS Spectrum™ 2.5.6 Reference Manual Notes on Freeware Edition From an initial inception as a IIgs communications program called Impala, Spectrum was developed and released under the guidance of Dave Hecker of Seven Hills International. Originally released back in 1991, it was sold by Seven Hills until their eventual closure. Seven Hills agreed I could continue to sell Spectrum, so I asked Eric Shepherd of Syndicomm to sell Spectrum on my behalf. In 2011 Tony Diaz took over Syndicomm and continued to sell it for me. With the declining sales over the years, I finally decided that the time had come in 2012 to make Spectrum Freeware. To coincide with its reclassification, this PDF manual has been compiled from the original Seven Hills manuals. I have changed a few words and links here and there, and added new screen shots and illustrations. Ewen Wannop - 2012 2 Spectrum About Seven Hills Software No Copy Protection We don’t believe in copy protection—all it does is impair the honest user’s ability to use software to its fullest. We strive to provide high quality products at reasonable prices. We hope you will support our efforts by not allowing your family or friends to copy this software. Questions and Comments We always welcome feedback—if you have any questions, or suggestions for improving this product, please let us know. In addition, we would like to hear your ideas for new programs. Copyrights and Trademarks This manual and the software (computer program) described in it are copyrighted with all rights reserved. -
Python Essential Reference (3Rd Edition)
Python ESSENTIAL REFERENCE Third Edition David Beazley DEVELOPER’S LIBRARY Sams Publishing, 800 East 96th Street, Indianapolis, Indiana 46240 USA Python Essential Reference, Acquisitions Editor Third Edition Jenny Watson Copyright 2006 by Sams Publishing Development Editor All rights reserved. No part of this book shall be reproduced, stored in Scott Meyers a retrieval system, or transmitted by any means, electronic, mechanical, photocopying, recording, or otherwise, without written permission Managing Editor from the publisher. No patent liability is assumed with respect to the Charlotte Clapp use of the information contained herein.Although every precaution has been taken in the preparation of this book, the publisher and Project Editor author assume no responsibility for errors or omissions. Nor is any lia- Andy Beaster bility assumed for damages resulting from the use of the information contained herein. Copy Editor International Standard Book Number: 0-672-32862-3 Bart Reed Library of Congress Catalog Card Number: 200593277 Printed in the United States of America Proofreader First Printing: February 2006 Paula Lowell 09080706 4321 Indexer David Beazley Trademarks Technical Editor All terms mentioned in this book that are known to be trademarks or Timothy Boronczyk service marks have been appropriately capitalized. Sams Publishing cannot attest to the accuracy of this information. Use of a term in this Publishing Coordinator book should not be regarded as affecting the validity of any trademark or service mark. Vanessa Evans Book Designer Warning and Disclaimer Gary Adair Every effort has been made to make this book as complete and as Page Layout accurate as possible, but no warranty or fitness is implied.The infor- mation provided is on an “as is” basis.The author and the publisher Michelle Mitchell shall have neither liability nor responsibility to any person or entity with respect to any loss or damages arising from the information con- tained in this book. -

DICOM Structured Reporting
DICOM Structured Reporting DICOM Structured Reporting David A. Clunie PixelMed Publishing Bangor, Pennsylvania The author and publisher have taken care in the preparation of this book, but make no expressed or implied warranty of any kind, and assume no responsibility for errors or omissions. No liability is assumed for incidental or consequential damages in connection with or arising out of the use of the information contained herein. Copyright © 2000 by PixelMed Publishing. All rights reserved. No part of this publication may be reproduced, stored in a retrieval system, or trans- mitted, in any form, or by any means, electronic, mechanical, photocopying, recording, or otherwise, with- out the prior written consent of the publisher. Library of Congress Card Number: 00-191700 ISBN 0-9701369-0-0 For Eleanor … Who This Book is For 21 Outline of This Book 22 Versions of the Standard 24 Conventions Used in this Book 24 Acknowledgements 26 Feedback 27 CHAPTER 1 Structured Reporting Concepts 29 Not Just Reports ... 30 Semantics not presentation 30 Constraints, IODs and Templates 31 Content 32 Trees and Relationships 33 Coded Concepts and Values 34 Living Without Codes 35 Report Management 36 Summary 38 CHAPTER 2 Codes and Controlled Terminology 39 Basic Concepts of Coded Entries 39 DICOM Encoding 40 Coding Scheme Designator and Version 42 Pros and Cons of Codes 43 Coding Schemes to Choose From 44 Codes for Structured Reporting 49 What does a Code Represent? 51 Code Meaning Revisited 53 Not Otherwise Specified 54 Context Groups and Mapping Resources -
The Okteta Handbook
The Okteta Handbook Friedrich W. H. Kossebau Alex Richardson The Okteta Handbook 2 Contents 1 Introduction 5 2 Basics 6 2.1 Starting Okteta . .6 2.2 Usage . .6 3 Tools 7 3.1 Overview . .7 3.1.1 Analyzers and Manipulators . .7 3.1.2 General tools . .8 3.2 Structures Tool . .8 3.2.1 General . .8 3.2.2 Installing structure definitions . .9 3.2.2.1 Installing using KNewStuff . .9 3.2.2.2 Installing structure definitions manually . .9 3.2.2.3 Using the newly installed structures . .9 3.2.3 Sharing structure definitions . .9 3.2.4 Creating structure definitions . .9 3.2.5 Structure definition XML file format . 10 3.2.6 An example structure definition in both XML and JavaScript . 12 3.2.6.1 The common step shared by both approaches . 12 3.2.6.2 A simple XML structure definition . 12 3.2.6.3 The simple structure in JavaScript . 13 3.2.6.4 More complex structures . 14 3.2.6.5 Further information . 14 4 Interface Overview 15 4.1 Menu Items . 15 4.1.1 File Menu . 15 4.1.2 Edit Menu . 16 4.1.3 View Menu . 16 4.1.4 Windows Menu . 17 4.1.5 Bookmarks Menu . 18 4.1.6 Tools Menu . 18 4.1.7 Settings Menu . 18 5 Credits and License 19 Abstract Okteta is a simple editor for the raw data of files. This type of program is also called hex editor or binary editor. The Okteta Handbook Chapter 1 Introduction Okteta is a simple editor for the raw data of files. -

Copyrighted Material
Index Note to the Reader: Throughout this index boldfaced page numbers indicate primary discus- sions of a topic. Italicized page numbers indicate illustrations. Add Keyword List dialog box, 363–364, 364 A Add Local Device dialog box, 156–157, 158 , About the Examiner report, 672 166, 166 Accelerated Graphics Port (AGP) standard Add Note Bookmark dialog box, 386–387, 387 expansion slots, 9 Add Partition dialog box, 577, 578 video cards, 10 Add Partition feature in NTFS, 76 access control lists (ACLs), 26 Add Partition menu, 583–585, 584 – 585 access times in link files, 507 – 509 , 508 Add To Hash Library dialog box, 458, 459 Acquire option in LinEn, 174, 174 Advanced Encryption Standard (AES) acquiring digital evidence, 120 – 121 encryption, 178 boot disks Advanced tab in FastBloc, 161, 161 , 163 booting from, 124 – 127 advanced topics, 572 – 573 creating, 121 – 124 , 121 – 124 Base64 encoding, 619 – 622 , 620 – 621 drive-to-drive DOS acquisition, 128 email, 614 – 619 , 614 – 617 steps, 128 – 132 , 129 – 130 EnCase Decryption Suite, 622 – 629 , 623 – 627 supplemental information, 132 – 135 exam essentials, 648 EnCase Portable, 180 – 188 , 181 – 188 mounting files, 588 – 593 , 589 – 590 , 593 Enterprise and FIM, 176 – 180 , 177 , 179 partitions, 573 – 588 , 573 – 586 exam essentials, 192 – 193 Physical Disk Emulator, 636 – 641 , 637 – 639 FastBloc SE, 163 – 168 , 165 – 168 registry. See registry FastBloc/Tableau, 151 restoration, 633 – 636 , 634 – 636 FastBloc 2 features, 152 – 154 , 153 – 154 review questions, 649 – 652 models, 151 – 152 summary, 645 – 647 steps, 154 – 162 , 156 – 161 Virtual File System, 629 – 632 , 629 , 631 – 632 hints, 188 – 189 Aegis Padlock Pro tool, 668 LinEn, 168 AES (Advanced Encryption Standard) mounting file systems as read-only, encryption, 178 168 – 169 agency seals, 674 overview, 171 – 173 AGP (Accelerated Graphics Port) standard steps, 173 – 176 , 174 – 175 expansion slots, 9 updates, 169 – 171 , 170 – 171 video cards, 10 network. -

Performance of Size-Changing Algorithms in Stackable File Systems
Performance of Size-Changing Algorithms in Stackable File Systems Erez Zadok, Johan M. Andersen, Ion Badulescu, and Jason Nieh Computer Science Department, Columbia University g fezk,johan,ion,nieh @cs.columbia.edu Abstract and ASCII, and size-changing encryption algorithms which Stackable file systems can provide extensible file system can provide added security. Some ideas have been previously functionality with minimal performance overhead and devel- suggested for supporting SCAs in stackable file systems by opment cost. However, previous approaches are limited in using cache coherency mechanisms[11, 15], but no complete the functionality they provide. In particular, they do not sup- solution has ever been developed or implemented, much less port size-changing algorithms, which are important and use- demonstrated. ful for many applications, such as compression and security. The challenge with supporting SCAs in stackable file sys- We propose fast index files, a technique for efficient support tems is that the file data layout and page offsets can change of size-changing algorithms in stackable file systems. Fast from layer to layer. Consider the case of an upper-level com- index files provide a page mapping between file system lay- pression file system stacked on top of a lower-level native file ers in a way that can be used with any size-changing algo- system. When an application writes a file through the com- rithm. Index files are designed to be recoverable if lost and pression file system, the file system will compress the file add less than 0.1% disk space overhead. We have imple- data, then pass the compressed data to the native file system, mented fast indexing using portable stackable templates, and which will then store it on disk. -
Automated Metadata Extraction
Masaryk University Faculty of Informatics Automated Metadata Extraction Master’s Thesis Bc. Martin Šmíd Brno, Spring 2021 Masaryk University Faculty of Informatics Automated Metadata Extraction Master’s Thesis Bc. Martin Šmíd Brno, Spring 2021 Declaration Hereby I declare that this paper is my original authorial work, which I have worked out on my own. All sources, references, and literature used or excerpted during elaboration of this work are properly cited and listed in complete reference to the due source. Bc. Martin Šmíd Advisor: RNDr. Lukáš Němec i Acknowledgements I would like to thank my advisor, RNDr. Lukáš Němec, for his friendly approach, helpful advice, and guidance of my work. I would like to express my gratitude to my family for their support. iii Abstract This thesis aims to create a modular tool that can extract important pat- terns of interest from binary data of generally unknown origin. Binary data can come in many different forms. Therefore, several standard encodings used to represent binary data are introduced in the first part. A section introducing selected interesting data patterns whose detection allows for more detailed identification of certain virtual or physical entities follows. The thesis also includes a description of the implemented tool that automates data decoding and data pattern extraction, along with the results of a collected dataset processing. iv Keywords binary-to-text encoding, metadata extraction, Python, data decoding, pattern detection v Contents 1 Introduction 1 2 Binary-to-text Encoding 3 2.1 UUEncoding . .3 2.2 Base encoding . .4 2.2.1 Base16 . .5 2.2.2 Base32 . -

Respectful Type Converters
Resp ectful Type Converters Jeannette M Wing John Ockerbloom May CMUCS School of Computer Science Carnegie Mellon University Pittsburgh PA Submitted to IEEE Transactions on Software Engineering Abstract In converting an ob ject of one type to another we exp ect some of the original ob jects b ehavior to remain the same and some to change How can we state the relationship b etween the original ob ject and converted ob ject to characterize what information is preserved and what is lost after the conversion takes place We answer this question by introducing the new relation respects and say that a type converter function C A B respects a type T We formally dene respects in terms of the Liskov and Wing b ehavioral notion of subtyping types A and B are subtypes of T We explain in detail the applicability of resp ectful type converters in the context of the Typed Ob ject Mo del TOM Conversion Service built at Carnegie Mellon and used on a daily basis throughout the world We also briey discuss how our respects relation addresses a similar question in two other contexts type evolution and interoperability This research is sp onsored in part by the Defense Advanced Research Pro jects Agency and the Wright Lab oratory Aeronautical Systems Center Air Force Materiel Command USAF F and Rome Lab oratory Air Force Materiel Command USAF under agreement number F and in part by the National Science Foundation under Grant No CCR The US Government is authorized to repro duce and distribute reprints for Governmental purp oses notwithstanding any copyright -

Can / Am EMTP News
___________________________________________ Can / Am EMTP News Voice of the Canadian / American EMTP User Group ___________________________________________ Publishers and Mailers : Authorized by Co-chairmen : Drs. Kai - Hwa Ger and Tsu - huei Liu Dr. W. Scott Meyer, Editor 3179 Oak Tree Court Dr. Tsu - huei Liu West Linn, Oregon 97068 E - mail : thliu @ bpa . gov United States of America Vol. 99 – 3 ; July, 1999 Table of Contents Salford Compiler and DOS Extender Salford Compiler and DOS Extender .......................... 1 Ver. 2.66 of FTN77/486, which dates to 1991, finally News from Outside USA and Canada ........................ 2 has met a FORTRAN subroutine that is too big to More about the Internet and E-mail ............................ 2 compile. This was the compiled TACS code associated Foreign Languages and E-mail ..................................... 3 with disk file IMMOD.DAT from Prof. Humberto Henao Watcom ATP for MS Windows ................................. 4 (see mention elsewhere in this issue). The error message News about TACS and MODELS ............................... 5 was: "*** Compiler stack overflow - routine is too Line and Cable Constants .............................................. 6 complex ...." Is this believable? Unfortunately, yes. Concurrent Plotting of ATP .......................................... 6 Executable FORTRAN produced by CTM totaled 32863 Higher - Order Pi Circuits ............................................... 6 lines, of which 31366 were non-comment lines. Does any Brain - damaged MS Windows ....................................... 7 Salford FTN77 user know how the stack space might be Mohan Assembles ATP data .......................................... 7 expanded? Your Editor looked in a printed FTN77 GNU ATP for djgpp and Cygnus ................................. 7 Reference Manual dated 1990, but noted nothing obvious. GNU ATP for Mingw32 ................................................ 8 He also carried the code to that shared, 90-MHz Pentium Scrollable MS-DOS Windows ..................................... -

A Encoding Formats
Input Octet 1 Input Bit 7 6 5 4 3 2 1 0 Output Data #1 5 4 3 2 1 0 Output Data #2 5 4 Input Octet 2 Input Bit 7 6 5 4 3 2 1 0 Output Data #2 3 2 1 0 Output Data #3 5 4 3 2 Input Octet 3 Input Bit 7 6 5 4 3 2 1 0 Output Data #3 1 0 Output Data #4 5 4 3 2 1 0 Table 1: Bit mapping for Three-in-Four encoding A Encoding Formats The following sections describe the four most widely used formats for encoding binary data into plain text, uuencoding, xxencoding, Base64 and BinHex. Another section shortly mentions Quoted-Printable encoding. Other formats exist, like btoa and ship, but they are not mentioned here. btoa is much less efficient than the others. ship is slightly more efficient and will probably be supported in future. Uuencoding, xxencoding and Base 64 basically work the same. They are all “three in four” encodings, which means that they take three octets11 from the input file and encode them into four characters. Three bytes are 24 bits, and they are divided into 4 sections of 6 bits each. Table 1 describes in detail how the input bits are copied into the output data bits. 6 bits can have values from 0 to 63; each of the “three in four” encodings now uses a character table with 64 entries, where each possible value is mapped to a specific character. The advantage of three in four encodings is their simplicity, as encoding and decoding can be done by mere bit shifting and two simple tables (one for encoding, mapping values to characters, and one for decoding, with the reverse mapping). -
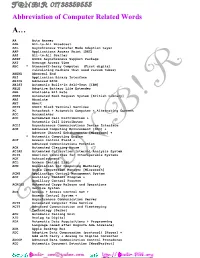
T T Abbreviation of Computer Related Words
Abbreviation of Computer Related Words A… AA Auto Answer AAB All-to-All Broadcast AAL Asynchronous Transfer Mode Adaption Layer AAP Applications Access Point [DEC] AAS All-to-All Scatter AASP ASCII Asynchronous Support Package AAT Average Access Time ABC * Atanasoff-Berry Computer (First digital calculating machine that used vacuum tubes) ABEND Abnormal End ABI Application Binary Interface ABIOS Advanced BIOS ABIST Automatic Built-In Self-Test [IBM] ABLE Adaptive Battery Life Extender ABR Available Bit Rate ABRS Automated Book Request System [British Library] ABS Absolute ABT Abort ABTS ASCII Block Terminal Services AC Autocheck + Automatic Computer + Alternating Current ACC Accumulator ACD Automated Call Distribution + Automatic Call Distributor ACDI Asynchronous Communications Device Interface ACE Advanced Computing Environment [SCO] + Adverse Channel Enhancements [Microcom] + * Automatic Computing Engine ACF Access Control Field + Advanced Communications Function ACH Automated Clearing House ACIAS Automated Calibration Interval Analysis System ACIS American Committee for Interoperable Systems ACK Acknowledgment ACL Access Control List ACM Association for Computing Machinery Audio Compression Manager [Microsoft] ACMS Application Control Management System ACP Ancillary Control Program + Auxillary Control Process ACROSS Automated Cargo Release and Operations Service System ACS Access + Access Control Set + Access Control System + Asynchronous Communication Server ACTS Automated Computer Time Service ACTT Advanced Communication and Timekeeping