Amazon Buys Encrypted Messaging App Wickr 25 June 2021
Total Page:16
File Type:pdf, Size:1020Kb
Load more
Recommended publications
-

Cisco SCA BB Protocol Reference Guide
Cisco Service Control Application for Broadband Protocol Reference Guide Protocol Pack #60 August 02, 2018 Cisco Systems, Inc. www.cisco.com Cisco has more than 200 offices worldwide. Addresses, phone numbers, and fax numbers are listed on the Cisco website at www.cisco.com/go/offices. THE SPECIFICATIONS AND INFORMATION REGARDING THE PRODUCTS IN THIS MANUAL ARE SUBJECT TO CHANGE WITHOUT NOTICE. ALL STATEMENTS, INFORMATION, AND RECOMMENDATIONS IN THIS MANUAL ARE BELIEVED TO BE ACCURATE BUT ARE PRESENTED WITHOUT WARRANTY OF ANY KIND, EXPRESS OR IMPLIED. USERS MUST TAKE FULL RESPONSIBILITY FOR THEIR APPLICATION OF ANY PRODUCTS. THE SOFTWARE LICENSE AND LIMITED WARRANTY FOR THE ACCOMPANYING PRODUCT ARE SET FORTH IN THE INFORMATION PACKET THAT SHIPPED WITH THE PRODUCT AND ARE INCORPORATED HEREIN BY THIS REFERENCE. IF YOU ARE UNABLE TO LOCATE THE SOFTWARE LICENSE OR LIMITED WARRANTY, CONTACT YOUR CISCO REPRESENTATIVE FOR A COPY. The Cisco implementation of TCP header compression is an adaptation of a program developed by the University of California, Berkeley (UCB) as part of UCB’s public domain version of the UNIX operating system. All rights reserved. Copyright © 1981, Regents of the University of California. NOTWITHSTANDING ANY OTHER WARRANTY HEREIN, ALL DOCUMENT FILES AND SOFTWARE OF THESE SUPPLIERS ARE PROVIDED “AS IS” WITH ALL FAULTS. CISCO AND THE ABOVE-NAMED SUPPLIERS DISCLAIM ALL WARRANTIES, EXPRESSED OR IMPLIED, INCLUDING, WITHOUT LIMITATION, THOSE OF MERCHANTABILITY, FITNESS FOR A PARTICULAR PURPOSE AND NONINFRINGEMENT OR ARISING FROM A COURSE OF DEALING, USAGE, OR TRADE PRACTICE. IN NO EVENT SHALL CISCO OR ITS SUPPLIERS BE LIABLE FOR ANY INDIRECT, SPECIAL, CONSEQUENTIAL, OR INCIDENTAL DAMAGES, INCLUDING, WITHOUT LIMITATION, LOST PROFITS OR LOSS OR DAMAGE TO DATA ARISING OUT OF THE USE OR INABILITY TO USE THIS MANUAL, EVEN IF CISCO OR ITS SUPPLIERS HAVE BEEN ADVISED OF THE POSSIBILITY OF SUCH DAMAGES. -

Security System for Mobile Messaging Applications Pejman Dashtinejad
Security System for Mobile Messaging Applications Pejman Dashtinejad Master of Science Thesis Stockholm, Sweden TRITA–ICT–EX-2015:2 Introduction | 1 Security System for Mobile Messaging Applications Pejman Dashtinejad 8 January 2015 Master of Science Thesis Examiner Professor Sead Muftic Department of ICT KTH University SE-100 44 Stockholm, Sweden TRITA–ICT–EX-2015:2 Abstract | iii Abstract Instant messaging (IM) applications are one of the most popular applications for smartphones. The IMs have the capability of sending messages or initiating voice calls via Internet which makes it almost cost free for the users to communicate with each other. Unfortunately, like any other type of applications, majority of these applications are vulnerable to malicious attacks and have privacy issues. The motivation for this thesis is the need to identifying security services of an IM application and to design a secure system for any mobile messaging application. This research proposes an E2EE (End-to-End Encryption) approach which provides a secure IM application design which protects its users with better integrity, confidentiality and privacy. To achieve this goal a research is conducted to investigate current security features of popular messaging applications in the mobile market. A list of requirements for good security is generated and based on those requirements an architecture is designed. A demo is also implemented and evaluated. Keywords: Mobile, Application, messaging, Chat, Encryption, Security Acknowledgments | v Acknowledgments First and foremost, thank you God to give me another chance to complete my higher education and to learn enormous skills and knowledge through all these years of study at the university. -

Parental Control – Whatsapp
Parental controls guide WhatsApp privacy guide Parental Controls information Type of guide Social media privacy guides Features and Benefits WhatsApp privacy settings allow you to restrict who can see your child’s messages and location. There are also ways to block delete or report users on the platform. Please note, WhatsApp new privacy policy has come into effect starting May 15. What specific content can I restrict? Chatting Downloading file sharing Location sharing Privacy Privacy and identity theft What do I need? A WhatsApp account WhatsApp privacy guide Step by step guide 1 Control who sees your information You can set your last seen, profile photo and/or status to the following options: Everyone, My Contacts and Nobody: 1. Open WhatsApp and go to your Settings, tap Account, then tap Privacy. 2. Next, tap your selected option, then choose from either option: ‘Everyone’, ‘My Contacts’ or ‘Nobody’. 3. The changes will be applied automatically. 1 WhatsApp privacy guide 2 3 WhatsApp privacy guide Step by step guide 2 How to block contacts You can stop receiving messages, calls and status updates from certain contacts by blocking them. Open WhatsApp, choose the person you want to block either by searching or scrolling through your chat list. 2. Tap on their name, then scroll down and tap Block Contact. 1 2 WhatsApp privacy guide WhatsApp privacy guide Step by step guide 3 How to report contacts 1. Open WhatsApp, choose the person you want to report either by searching or scrolling through your chat list. 2. Tap on their name, then scroll down and tap Report or Report and Block Contact. -

Enterprise Edition
Secure Communication. Simplified. SAFECHATS Problem Most companies use popular insecure email and ⛔ messaging services to communicate confidential information P The information flow within the Company is ⛔ disorganized Metadata is exposed and available to third-party ⛔ services SAFECHATS Introducing SAFECHATS Ultra-secure communication solution P Designed with security in mind SAFECHATS Why SAFECHATS? ✔ Information is always end-to-end encrypted by default P ✔ All-in-one communication suite: • Text messaging (one-on-one and group chats) • Voice calls • File transfers (no size and file type limits) SAFECHATS How does SAFECHATS solve the problem? ✔ Customizable white label solution ✔ Integrates with existing softwareP infrastructure ✔ Enterprise-wide account and contact list management, supervised audited chats for compliance SAFECHATS What makes SAFECHATS different? ✔ Your own isolated cloud environment or on-premise deployment P ✔ Customizable solution allows to be compliant with internal corporate security policies ✔ No access to your phone number and contact list SAFECHATS Screenshot Protection ✔ Notifications on iOS P ✔ DRM protection on Android SAFECHATS Identity Verification ✔ Protection from man-in-the-middle attacksP ✔ SMP Protocol SAFECHATS Privacy Features ✔ Show / hide messages and files P ✔ Recall messages and files ✔ Self-destructing messages and files SAFECHATS Additional Protection ✔ History retention control P ✔ Application lock: • PIN-code • Pattern-lock on Android devices • Touch ID on iOS devices SAFECHATS How does SAFECHATS -
Digital Communications Protocols
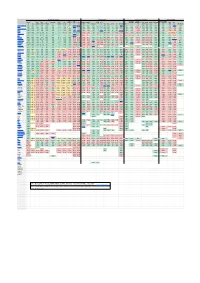
Security & Privacy Compatibility Features & Usability Sustainability E2E E2E Offline Local Decentralized Active Open Open On Anonymous E2E E2E Default Audit FIDO1 Desktop Mobile Apple AOSP Messages messaging File Audio Video Phoneless or Federated Open IETF [1] TLS Client Server Premise [2] Private Group [3] [4] / U2F Web Web Android iOS [5] Win macOS Linux *BSD Terminal MDM [6] [7] [8] Share Call Call [9] [10] Spec [11] Introduced Element/Matrix TRUE TRUE TRUE TRUE TRUE TRUE TRUE TRUE TRUE TRUE PARTIAL TRUE TRUE TRUE TRUE TRUE TRUE TRUE TRUE TRUE TRUE TRUE TRUE TRUE TRUE TRUE TRUE TRUE TRUE TRUE FALSE 2014 XMPP TRUE TRUE TRUE TRUE TRUE TRUE TRUE TRUE PARTIAL [12]TRUE FALSE TRUE TRUE TRUE TRUE TRUE TRUE TRUE TRUE TRUE TRUE TRUE TRUE FALSE [13] TRUE TRUE TRUE TRUE TRUE TRUE TRUE 1999 NextCloud Talk TRUE TRUE TRUE TRUE TRUE TRUE TRUE TRUE TRUE FALSE TRUE TRUE TRUE TRUE TRUE TRUE TRUE TRUE TRUE TRUE FALSE TRUE TRUE FALSE TRUE TRUE TRUE TRUE TRUE FALSE FALSE 2018 Wire TRUE TRUE TRUE TRUE TRUE TRUE TRUE TRUE TRUE TRUE FALSE TRUE FALSE TRUE TRUE FALSE TRUE TRUE TRUE TRUE PARTIAL TRUE TRUE FALSE TRUE TRUE TRUE TRUE FALSE FALSE FALSE 2014 Jami TRUE TRUE TRUE N/A [14] N/A TRUE TRUE FALSE [15] TRUE FALSE N/A [16] FALSE FALSE TRUE TRUE TRUE TRUE TRUE TRUE TRUE FALSE TRUE FALSE FALSE TRUE TRUE TRUE TRUE TRUE PARTIAL PARTIAL[17] [18] 2016 Briar [19] TRUE TRUE TRUE N/A [20] N/A TRUE TRUE TRUE TRUE TRUE N/A [21] FALSE FALSE TRUE FALSE TRUE FALSE FALSE FALSE FALSE FALSE FALSE TRUE TRUE FALSE FALSE FALSE FALSE TRUE FALSE FALSE 2016 Tox TRUE TRUE TRUE -

How Secure Is Textsecure?
How Secure is TextSecure? Tilman Frosch∗y, Christian Mainkay, Christoph Badery, Florian Bergsmay,Jorg¨ Schwenky, Thorsten Holzy ∗G DATA Advanced Analytics GmbH firstname.lastname @gdata.de f g yHorst Gortz¨ Institute for IT-Security Ruhr University Bochum firstname.lastname @rub.de f g Abstract—Instant Messaging has gained popularity by users without providing any kind of authentication. Today, many for both private and business communication as low-cost clients implement only client-to-server encryption via TLS, short message replacement on mobile devices. However, until although security mechanisms like Off the Record (OTR) recently, most mobile messaging apps did not protect confi- communication [3] or SCIMP [4] providing end-to-end con- dentiality or integrity of the messages. fidentiality and integrity are available. Press releases about mass surveillance performed by intelli- With the advent of smartphones, low-cost short-message gence services such as NSA and GCHQ motivated many people alternatives that use the data channel to communicate, to use alternative messaging solutions to preserve the security gained popularity. However, in the context of mobile ap- and privacy of their communication on the Internet. Initially plications, the assumption of classical instant messaging, fueled by Facebook’s acquisition of the hugely popular mobile for instance, that both parties are online at the time the messaging app WHATSAPP, alternatives claiming to provide conversation takes place, is no longer necessarily valid. secure communication experienced a significant increase of new Instead, the mobile context requires solutions that allow for users. asynchronous communication, where a party may be offline A messaging app that claims to provide secure instant for a prolonged time. -

Ethics of Facebook: Analyzing the Social Network and Global Leader
Ethics of Facebook: Analyzing the Social Network and Global Leader A Thesis Submitted to the Faculty of the School of Engineering and Applied Science University of Virginia • Charlottesville, Virginia In Partial Fulfillment of the Requirements of the Degree Bachelor of Science, School of Engineering Selwyn Hector Spring 2020 On my honor as a University Student, I have neither given nor received unauthorized aid on this assignment as defined by the Honor Guidelines for Thesis-Related Assignments Signature __________________________________________ Date __________ Selwyn Hector Approved __________________________________________ Date __________ Michael Gorman, Department of Engineering and Society Ethics of Facebook: Analyzing the Social Network and Global Leader Introduction As computing technology has grown, the internet and computers have become an essential part of people’s daily lives. According to data from the US Census, 81% of United States homes had a computer with internet access in 2016 and 76% of households had at least 1 one smartphone. Facebook is one of the internet’s largest services with 1.59 billion daily active 2 users and 2.41 billion monthly active users as of June 2019. Facebook’s massive user base gives it a platform to influence many parts of the world. Facebook began as a platform for connecting college students but now is a behemoth in entertainment, news, advertising, and more. Small decisions in how content is prioritized and what content is allowed to be posted have consequences across many cultures. This enormous power makes Facebook not only a social network that connects friends but a global leader that shapes the future. Unfortunately, the platform has been at the center of many controversies related to user 3,4 privacy, misinformation, and hate speech. -

What Is Whatsapp? Whatsapp Is a Mobile Phone Application That Allows Users to Send Messages to Individuals and Groups, As Well As Share Images and Documents
What is WhatsApp? WhatsApp is a mobile phone application that allows users to send messages to individuals and groups, as well as share images and documents. WhatsApp is a useful tool when you want to communicate with a group—such as all the nurses on your unit. It is less cumbersome than starting a texting group using everyone’s personal mobile phone. How to set up WhatsApp on your mobile phone Go to the App Store for your iPhone or Open Google Play on your Android Install “WhatsApp” Once you have the App on your phone: Go to “Settings” and add a photo and a status message (optional) The App will draw from directly your contacts in your phone and identified people who have WhatsApp How to set up a group chat Open WhatsApp On the bottom of the screen there are options to make calls, send texts etc. Click on the Chat Bubble which will take you to the screen where you message with your contacts From here there are two ways of creating a new group: Click on NEW GROUP on the top right of your screen This will take you to your contact list. Type a name in the search bar at top, or go down the list and tap everyone you would like in the group (a little blue check will show up next to their name). Click NEXT The next page is where you can give your group a name, and add a picture that represents the group (optional) SECOND WAY TO CREATE A GROUP CHAT: Back on the main chat page, you can click on the icon of a note being written all the way at the top right of the page Which will take to the next page offering you the option of creating a new group. -

Is Bob Sending Mixed Signals?
Is Bob Sending Mixed Signals? Michael Schliep Ian Kariniemi Nicholas Hopper University of Minnesota University of Minnesota University of Minnesota [email protected] [email protected] [email protected] ABSTRACT Demand for end-to-end secure messaging has been growing rapidly and companies have responded by releasing applications that imple- ment end-to-end secure messaging protocols. Signal and protocols based on Signal dominate the secure messaging applications. In this work we analyze conversational security properties provided by the Signal Android application against a variety of real world ad- versaries. We identify vulnerabilities that allow the Signal server to learn the contents of attachments, undetectably re-order and drop messages, and add and drop participants from group conversations. We then perform proof-of-concept attacks against the application to demonstrate the practicality of these vulnerabilities, and suggest mitigations that can detect our attacks. The main conclusion of our work is that we need to consider more than confidentiality and integrity of messages when designing future protocols. We also stress that protocols must protect against compromised servers and at a minimum implement a trust but verify model. 1 INTRODUCTION (a) Alice’s view of the conversa-(b) Bob’s view of the conversa- Recently many software developers and companies have been inte- tion. tion. grating end-to-end encrypted messaging protocols into their chat applications. Some applications implement a proprietary protocol, Figure 1: Speaker inconsistency in a conversation. such as Apple iMessage [1]; others, such as Cryptocat [7], imple- ment XMPP OMEMO [17]; but most implement the Signal protocol or a protocol based on Signal, including Open Whisper Systems’ caching. -

Portable Wi-Fi Calling and Interactive Voice Response System
www.ijemr.net ISSN (ONLINE): 2250-0758, ISSN (PRINT): 2394-6962 Volume-7, Issue-1, January-February 2017 International Journal of Engineering and Management Research Page Number: 384-386 Portable Wi-Fi Calling and Interactive Voice Response System Ruchi W. Kasare1, Pooja K. Muneshwar2, Nikhil D. Tembhekar3, Prof. V. P. Yadav4, Prof. J. V. Shriral5 1,2,3,4,5Department of Computer Science and Engineering, Priyadarshani College of Engineering and Research, Nagpur University, Maharashtra, INDIA ABSTRACT Wireless IP-PBX utilizes WIFI technology for Implementation of a VoIP telephony system using communication, the same wireless infrastructure used for an IP Telephony solution in the organization as IVR. A new your corporate network. Just as we use mobiles and technology VoIP or Internet Telephony means that your laptops within this wireless infrastructure to gain access voice is carried over the IP network, otherwise known as to information, now we can use wireless IP phones the Internet. Voice which is an analog signal, is converted system as this system uses the telephony function to digital data, which is then disassembled and transmitted through the Internet or Internet to be recovered back to an directly into an already existing data network. This analog signal an the other using an IP Telephony solution provides an advantage that voice and data network can which is an Linux base system. be used together using single system. One of the major This service can be properly managed and advantages of the IP-PBX wireless phone is that you can deployed over a network with less stress and expenses. -
Protec3ng Messaging Other Than Email, Plus Network Link Protec3on
Protec'ng Messaging Other Than Email, plus Network Link Protec'on Joe St Sauver, Ph.D. [email protected] or [email protected] M3AAWG Senior Technical Advisor Scien@st, Farsight Security, Inc. Gold Ballroom, 1st Floor M3AAWG 36, San Francisco, California Wednesday Feb 17th, 2016, 15:30-16:30 hPps://www.stsauver.com/joe/crypto-other-than-email/ 1 Introduc'on • Today's session has two parts: – The first part will consider cryptographic privacy protecon for messaging other than email. – The second part will focus on cryptographic protecon of high speed internal links. • The common link between the two topics is that in each case, your op@ons are constrained by what the market offers. Today's goal is to help you understand why you want protec@on for these points of exposure, and how to select a solu@on. • Both of these topics are the subject of pending dra documents in the Pervasive Monitoring SIG. 2 I. Messaging Other Than Email 3 Messaging Other Than Email • M3AAWG has been working hard on protec@ng email against pervasive monitoring. • That's very important work, and protec@ng email privacy is a totally appropriate goal for M3AAWG. • Although M3AAWG has always had a strong focus on email, our charter, as the an@-Pervasive Monitoring SIG of the Messaging, Malware, and Mobile An-Abuse Working Group, includes, or should include, protec@ng mobile voice telephony and mobile applicaons (such as tex@ng/chat), too. • Arguably, for many users, secure mobile voice and secure text/ chat is as important, or even more important than email. -

National Security Agency | Cybersecurity Information Selecting
National Security Agency | Cybersecurity Information Selecting and Safely Using Collaboration Services for Telework - UPDATE Summary During a global pandemic or other crisis contingency scenarios, many United States Government (USG) personnel must operate from home while continuing to perform critical national functions and support continuity of government services. With limited access to government furnished equipment (GFE) such as laptops and secure smartphones, the use of (not typically approved) commercial collaboration services on personal devices for limited government official use becomes necessary and unavoidable. We define collaboration services as those capabilities that allow the workforce to communicate via internet-enabled text, voice, and video, and can include the sharing of files and other mission content. Collaboration can occur between two people or widened to include a large group to support mission needs. This document provides a snapshot of best practices and criteria based on capabilities available at the time of publication and was coordinated with the Department of Homeland Security (DHS), which has released similar guidance: “Cybersecurity Recommendations for Federal Agencies Using Video Conferencing” [1] and “Guidance for Securing Video Conferencing” [2]. This NSA publication is designed to provide simple and actionable considerations for individual government users. The intent of this document is not meant to be exhaustive or based on formal testing, but rather be responsive to a growing demand amongst the federal government to allow its workforce to operate remotely using personal devices when deemed to be in the best interests of the health and welfare of its workforce and the nation. Recommendations in this document are likely to change as collaboration services evolve and also address known vulnerabilities and threats.