Virus V Kontextu Nových Médií
Total Page:16
File Type:pdf, Size:1020Kb
Load more
Recommended publications
-

Jeffrey Heim, Marcel Hernandez, Maria Nunez,& Matthias Katerna Morris Worm on November 2, 1988, Robert Tappan Morris Releas
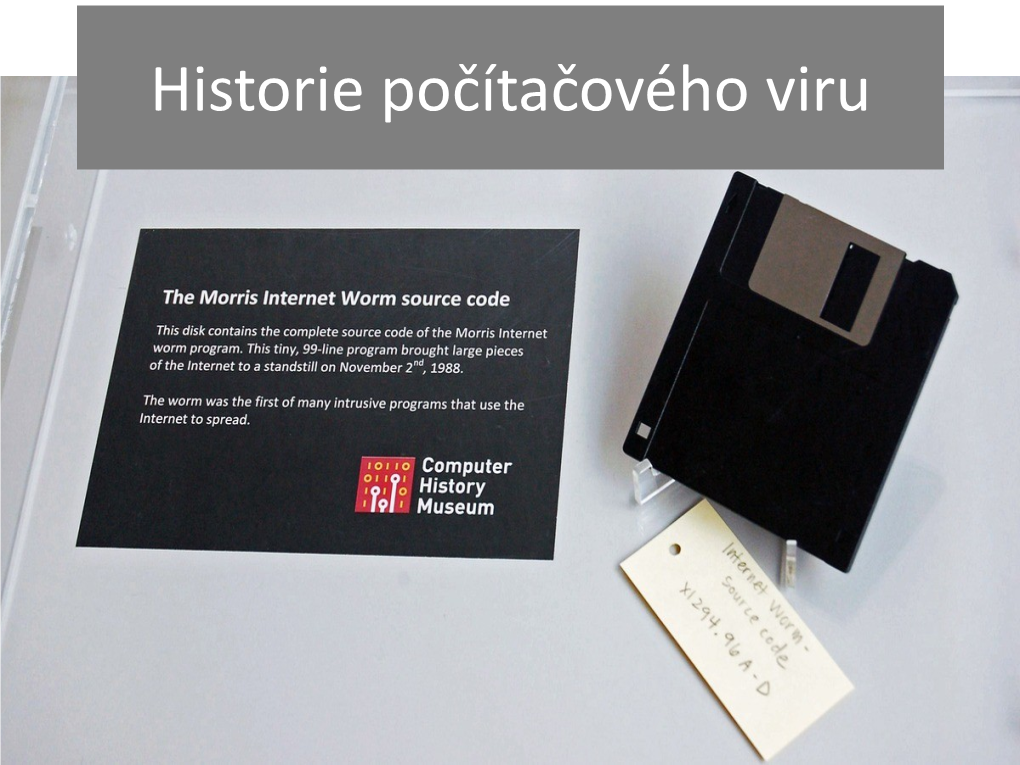
Jeffrey Heim, Marcel Hernandez, Maria Nunez,& Matthias Katerna Morris Worm On November 2, 1988, Robert Tappan Morris released a worm into the internet. The experimental worm was the first of its kind. It replicated itself and programmed itself, so it ended up spreading much faster than Morris expected. It self-programmed and self-replicated at an exponential rate in a manner that had never been seen before. Morris knew this worm was not necessarily ethical, for he released it out of MIT instead of his own Cornell University. In due course, many computers across the United States had crashed because of Morris. Once he discovered how much damage the worm had been causing, he reached out to a friend at Harvard looking for a solution to stop it. They attempted in sending an anonymous message to the network with directions that could kill the worm, but the message came through too late since they system was clogged. Many significant computers at colleges, businesses and the military became infected. The cost to fix each computer ranged from $200 to over $53,000. The worm exploited vulnerabilities in computer systems and in the UNIX email software. Within 24 hours of releasing the worm, thousands of people were aware something was unusual. Eventually, it would infect ten percent of all computers using the internet. The Morris Worm was the largest malware case ever to reach this percentage. However, the percentage was so high due to the fact that the number of computers was much less than today. The computers it impacted included significant systems, such as Stanford’s, Berkley’s and NASA’s. -
Chapter 3: Viruses, Worms, and Blended Threats
Chapter 3 Chapter 3: Viruses, Worms, and Blended Threats.........................................................................46 Evolution of Viruses and Countermeasures...................................................................................46 The Early Days of Viruses.................................................................................................47 Beyond Annoyance: The Proliferation of Destructive Viruses .........................................48 Wiping Out Hard Drives—CIH Virus ...................................................................48 Virus Programming for the Masses 1: Macro Viruses...........................................48 Virus Programming for the Masses 2: Virus Generators.......................................50 Evolving Threats, Evolving Countermeasures ..................................................................51 Detecting Viruses...................................................................................................51 Radical Evolution—Polymorphic and Metamorphic Viruses ...............................53 Detecting Complex Viruses ...................................................................................55 State of Virus Detection.........................................................................................55 Trends in Virus Evolution..................................................................................................56 Worms and Vulnerabilities ............................................................................................................57 -
Lesson 6: Hacking Malware
LESSON 6 HACKING MALWARE Lesson 6: Malware WARNING The Hacker Highschool Project is a learning tool and as with any learning tool there are dangers. Some lessons if abused may result in physical injury. Some additional dangers may also exist where there is not enough research on possible effects of emanations from particular technologies. Students using these lessons should be supervised yet encouraged to learn, try, and do. However ISECOM cannot accept responsibility for how any information herein is abused. The following lessons and workbooks are open and publicly available under the following terms and conditions of ISECOM: All works in the Hacker Highschool Project are provided for non-commercial use with elementary school students, junior high school students, and high school students whether in a public institution, private institution, or a part of home-schooling. These materials may not be reproduced for sale in any form. The provision of any class, course, training, or camp with these materials for which a fee is charged is expressly forbidden without a license including college classes, university classes, trade-school classes, summer or computer camps, and similar. To purchase a license, visit the LICENSE section of the HHS web page at http://www.hackerhighschool.org/licensing.html. The HHS Project is an open community effort and if you find value in this project we ask that you support us through the purchase of a license, a donation, or sponsorship. 2 Lesson 6: Malware Table of Contents WARNING....................................................................................................................................................2 -
IBM X-Force Threat Insight Quarterly 2 X-Force Threat Insight Quarterly IBM Security Solutions
IBM Security Solutions May 2011 IBM X-Force Threat Insight Quarterly 2 X-Force Threat Insight Quarterly IBM Security Solutions Contents About the report 2 About the Report The IBM X-Force® Threat Insight Quarterly is designed to highlight some of the most significant threats and challenges 3 Evolution: From Nuisance to Weapon facing security professionals today. This report is a product of IBM Managed Security Services and the IBM X-Force 8 Prolific and Impacting Issues of Q1 2011 research and development team. Each issue focuses on specific challenges and provides a recap of the most significant recent 16 References online threats. IBM Managed Security Services are designed to help an organization improve its information security, by outsourcing security operations or supplementing your existing security teams. The IBM protection on-demand platform helps deliver Managed Security Services and the expertise, knowledge and infrastructure an organization needs to secure its information assets from Internet attacks. The X-Force team provides the foundation for a preemptive approach to Internet security. The X-Force team is one of the best-known commercial security research groups in the world. This group of security experts researches and evaluates vulnerabilities and security issues, develops assessment and countermeasure technology for IBM security products, and educates the public about emerging Internet threats. We welcome your feedback. Questions or comments regarding the content of this report should be addressed to [email protected]. 3 X-Force Threat Insight Quarterly IBM Security Solutions Evolution: From Nuisance to Weapon One of the more notable examples here is Brain3, a boot sector infector which originated in Pakistan and released in 1986, was Creeper, Wabbit, Animal, Elk Cloner, Brain, Vienna, Lehigh, one of the first examples of malware that infected PC’s running Stoned, Jerusalem. -
![Reversing Malware [Based on Material from the Textbook]](https://docslib.b-cdn.net/cover/8924/reversing-malware-based-on-material-from-the-textbook-1438924.webp)
Reversing Malware [Based on Material from the Textbook]
SoftWindows 11/23/05 Reversing Malware [based on material from the textbook] Reverse Engineering (Reversing Malware) © SERG What is Malware? • Malware (malicious software) is any program that works against the interest of the system’s user or owner. • Question: Is a program that spies on the web browsing habits of the employees of a company considered malware? • What if the CEO authorized the installation of the spying program? Reverse Engineering (Reversing Malware) © SERG Reversing Malware • Revering is the strongest weapon we have against the creators of malware. • Antivirus researchers engage in reversing in order to: – analyze the latest malware, – determine how dangerous the malware is, – learn the weaknesses of malware so that effective antivirus programs can be developed. Reverse Engineering (Reversing Malware) © SERG Distributed Objects 1 SoftWindows 11/23/05 Uses of Malware • Why do people develop and deploy malware? – Financial gain – Psychological urges and childish desires to “beat the system”. – Access private data – … Reverse Engineering (Reversing Malware) © SERG Typical Purposes of Malware • Backdoor access: – Attacker gains unlimited access to the machine. • Denial-of-service (DoS) attacks: – Infect a huge number of machines to try simultaneously to connect to a target server in hope of overwhelming it and making it crash. • Vandalism: – E.g., defacing a web site. • Resource Theft: – E.g., stealing other user’s computing and network resources, such as using your neighbors’ Wireless Network. • Information Theft: – E.g., stealing other user’s credit card numbers. Reverse Engineering (Reversing Malware) © SERG Types of Malware • Viruses • Worms • Trojan Horses • Backdoors • Mobile code • Adware • Sticky software Reverse Engineering (Reversing Malware) © SERG Distributed Objects 2 SoftWindows 11/23/05 Viruses • Viruses are self-replicating programs that usually have a malicious intent. -

Topics in Malware What Is Malware?
Topics in Malware What is Malware? • Malware (malicious software) is any program that works against the interest of the system’s user or owner. • Question: Is a program that spies on the web browsing habits of the employees of a company considered malware? • What if the CEO authorized the installation of the spying program? Uses of Malware • Why do people develop and deploy malware? – Financial gain – Psychological urges and childish desires to “beat the system”. – Access private data – … Typical purposes of Malware • Backdoor access: – Attacker gains unlimited access to the machine. • Denial-of-service (DoS) attacks: – Infect a huge number of machines to try simultaneously to connect to a target server in hope of overwhelming it and making it crash. • Vandalism: – E.g., defacing a web site. • Resource Theft: – E.g., stealing other user’s computing and network resources, such as using your neighbors’ Wireless Network. • Information Theft: – E.g., stealing other user’s credit card numbers. Types of Malware • Viruses • Worms • Trojan Horses • Backdoors • Mobile code • Adware • Sticky software Metamorphic viruses • Instead of encrypting the program’s body and making slight alterations in the decryption engine, alter the entire program each time it is replicated. • This makes it extremely difficult for antivirus writers to use signature-matching techniques to identify malware. • Metamorphism requires a powerful code analysis engine that needs to be embedded into the malware. Metamorphic viruses: Operation • Metamorphic engine scans the code and generates a different version of it every time the program is duplicated. • The metamorphic engine performs a wide variety of transformations on the malware and on the engine itself. -
TCP SYN-ACK) to Spoofed IP Addresses
Joint Japan-India Workshop on Cyber Security and Services/Applications for M2M and Fourteenth GISFI Standardization Series Meeting How to secure the network - Darknet based cyber-security technologies for global monitoring and analysis Koji NAKAO Research Executive Director, Distinguished Researcher, NICT Information Security Fellow, KDDI Outline of NICT Mission As the sole national research institute in the information and communications field, we as NICT will strive to advance national technologies and contribute to national policies in the field, by promoting our own research and development and by cooperating with and supporting outside parties. Collaboration between Industry, Academic Institutions and Government R&D carried out by NICT’s researchers Budget (FY 2012): approx. 31.45 Billion Yen (420 Million US$) Personnel: 849 Researchers: 517 PhDs: 410 R&D assistance (as of April 2012) to industry and life convenient Japan Standard Time and academia Space Weather Forecast services Forecast Weather Space of the global community community global the of Growth of Economy of Japanese Growth Promotion of ICT a more for Security and Safety businesses Interaction with National ICT Policy problems major solve to Contribution 2 Internet Security Days 2012 Network Security Research Institute Collabor • Cyber attack monitoring, tracking, • Dynamic and optimal deployment of ation security functions analysis, response and prevention New GenerationNetwork Security • Prompt promotion of outcomes • Secure new generation network design Security Cybersecurity Architecture Laboratory Security Organizations Laboratory Daisuke Inoue Shin’ichiro Matsuo Kazumasa Taira Koji Nakao (Director General) (Distinguished Researcher) Security • Security evaluation of cryptography Fundamentals • Practical security • Post quantum cryptography Laboratory • Quantum security Shiho Moriai Recommendations for Cryptographic Algorithms and Key Lengths to Japan e-Government and SDOs 3 Internet Security Days 2012 Content for Today • Current Security Threats (e.g. -

Hacking Techniques in Wired Networks
Hacking Techniques in Wired Networks Qijun Gu, Pennsylvania State University, University Park Peng Liu, Pennsylvania State University, University Park Chao-Hsien Chu, Pennsylvania State University, University Park Introduction Principles of Hacking Seven Steps of Hacking Overview of Hacking Toolkits Classifications of Hacking Toolkits Attacks against the Internet Infrastructure Attacks against DNS Attacks against TCP/IP Attacks against BGP Attacks against End Systems of the Internet Morris Worm Melissa Sadmind Code Red I and Code Red II Nimda SQL Slammer W32/Blaster Attacks against Enterprise Network Systems Attacks against Private Networks Attacks against Private Networks with Web Service Attacks against Firewalls and Virtual Private Networks Conclusion Keywords: Wired network, Security, Cyber attack, Vulnerability, Hack, Worm, Virus, Internet infrastructure, End system, Enterprise network Wired networks, especially the Internet, have already been indispensable in our daily activities. However, in the last 10 years, security “disasters” have challenged the design and development of networks and systems. Vulnerabilities in current systems are frequently exploited by hackers and attackers. Cyber attacks have become a more and more serious threat to our society. In order to better protect networks, this article gives an overview on a variety of hacking techniques. This article focuses on the objectives, principles, functionalities and characteristics of different types of hacking techniques in wired networks, and provides in-depth discussions on the common characteristics of cyber attacks, the structure and components of cyber attacks, and the relationships among cyber attacks. These discussions can help security professionals grasp the “soul” of a “new” cyber attack in an easier and quicker way. INTRODUCTION Nowadays, wired networks, especially the Internet, have already become a platform to support not only high-speed data communication, but also powerful distributed computing for a variety of personal and business processes every day. -
Computer Viruses--A Form of Artificial Life?
View metadata, citation and similar papers at core.ac.uk brought to you by CORE provided by Purdue E-Pubs Purdue University Purdue e-Pubs Department of Computer Science Technical Reports Department of Computer Science 1990 Computer Viruses--A Form of Artificial Life? Eugene H. Spafford Purdue University, [email protected] Report Number: 90-985 Spafford, Eugene H., "Computer Viruses--A Form of Artificial Life?" (1990). Department of Computer Science Technical Reports. Paper 837. https://docs.lib.purdue.edu/cstech/837 This document has been made available through Purdue e-Pubs, a service of the Purdue University Libraries. Please contact [email protected] for additional information. COMPUTER YmUSES-A FORM OF ARTIFICIAL LIFE? Eugene H. Spalford CSD·TR·985 June 1990 Computer Viruses-A Form of Artificial Life? * Technical Repor~ CSD-TR-985 Eugene H. SpaJford Software Engineering Research Center Department of Computer Science Purdue University West Lafayette, Indiana 47907-2004 (317) 494-7825 [email protected] June 8, 1990 1 Introduction There has been con5id~rable interest of late in computer viruses. One aspect of this interest has been to ask if computer viruses are a form of artificial life, and what that might imply. This paper is a condensed, high-Ievell' description ofcomputer viruses their history, structure, and how they relate to some properties that might derme artificial life. It provides a general introduction to the topic without requiring an extensive background in computer science. The interested reader might pursue [9, I, 2] and [5] for more detail about computer viruses and their properties. The description in this paper of the origins of computer viruses and their structure is taken from [9]. -
Automating Cyber Attacks
Automating Cyber Attacks HYPE AND REALITY AUTHORS Ben Buchanan John Bansemer Dakota Cary Jack Lucas Micah Musser NOVEMBER 2020 Established in January 2019, the Center for Security and Emerging Technology (CSET) at Georgetown’s Walsh School of Foreign Service is a research organization fo- cused on studying the security impacts of emerging tech- nologies, supporting academic work in security and tech- nology studies, and delivering nonpartisan analysis to the policy community. CSET aims to prepare a generation of policymakers, analysts, and diplomats to address the chal- lenges and opportunities of emerging technologies. During its first two years, CSET will focus on the effects of progress in artificial intelligence and advanced computing. CSET.GEORGETOWN.EDU | [email protected] 2 Center for Security and Emerging Technology NOVEMBER 2020 Automating Cyber Attacks HYPE AND REALITY AUTHORS Ben Buchanan John Bansemer Dakota Cary Jack Lucas Micah Musser ACKNOWLEDGMENTS The authors would like to thank Perri Adams, Max Guise, Drew Lohn, Igor Mikolic-Torreira, Chris Rohlf, Lynne Weil, and Alexandra Vreeman for their comments on earlier versions of this manuscript. PRINT AND ELECTRONIC DISTRIBUTION RIGHTS © 2020 by the Center for Security and Emerging Technology. This work is licensed under a Creative Commons Attribution- NonCommercial 4.0 International License. To view a copy of this license, visit: https://creativecommons.org/licenses/by-nc/4.0/. Document Identifier: doi: 10.51593/2020CA002 Cover photo: KsanaGraphica/ShutterStock. Contents EXECUTIVE SUMMARY III INTRODUCTION V 1 | THE CYBER KILL CHAIN 1 2 | HOW MACHINE LEARNING CAN (AND CAN’T) 11 CHANGE OFFENSIVE OPERATIONS 3 | CONCLUSION: KEY JUDGMENTS 21 ENDNOTES 29 Center for Security and Emerging Technology i iv Center for Security and Emerging Technology Executive Summary acking is a well-established part of statecraft. -

Antivirus HAX! Presented by Ehab Hussein Synapse Malware Research Team : Sofiane Talmat (Algeria) Ehab Hussein (Egypt) Saadtalaat (Egypt) Amr Thabet (Egypt)
AntiVirus HAX! Presented by Ehab Hussein Synapse Malware research team : Sofiane Talmat (Algeria) Ehab Hussein (Egypt) SaadTalaat (Egypt) Amr Thabet (Egypt) http://www.synapse-labs.com [email protected] Synapse Intro History AV Detection Techniques Bypassing Sophos :) Demo Student Bounty Challenge $$$ http://www.synapse-labs.com [email protected] Security Corporate Services Services Solution Development Trainings http://www.synapse-labs.com [email protected] Viruses don't harm, ignorance does! « The Evolution of malware within the last ten years is described by the evolution of people who develop that » (Eugene kaspersky) http://www.synapse-labs.com [email protected] http://www.synapse-labs.com [email protected] – 1948 – 1966 (First theroical Approach) John von Neumann « Theory of self-reproducing automata » http://www.synapse-labs.com [email protected] – 1971 (First Worm) Robert (Bob) H. Thomas (BBN technologies) "I'm the creeper, catch me if you can!" Machine : PDP-10 System : TENEX Transport : ARPANET was the world's first operational packet switching network and the core network of a set that came to compose the global Internet. Funded by Darpa http://www.synapse-labs.com [email protected] WORM http://www.synapse-labs.com [email protected] TROJAN HORSE http://www.synapse-labs.com [email protected] – 1974/1975 (First Trojan Virus) John Walker « ANIMAL » UNIVAC 1108 http://www.synapse-labs.com [email protected] – 1982/1982 (First microcomputer Virus) Rich Skrenta « Elk Cloner » Apple II Boot Sector http://www.synapse-labs.com [email protected] BOOT SECTOR http://www.synapse-labs.com [email protected] – 1986 (First IBM-PC Virus) Basit & Amjad Farooq Alvi « Brain Boot Sector » « Pakistan Flu » « Lahore » http://www.synapse-labs.com [email protected] – 1986 (First File Infector Virus) VirDem Ver.: 1.06 (Generation #) aktive. -
The Ultimate Cybersecurity Guide for the It Professional
THE ULTIMATE CYBERSECURITY GUIDE FOR THE IT PROFESSIONAL { 01101000 01110100 01110100 01110000 01110011 00111010 00101111 00101111 01110111 01110111 01110111 00101110 01100011 01100001 01110010 01100010 01101111 01101110 01100010 01101100 01100001 01100011 01101011 00101110 01100011 01101111 01101101 } THE ULTIMATE CYBERSECURITY GUIDE FOR THE IT PROFESSIONAL 2019 Welcome to our comprehensive guide on the basics of cybersecurity. Whether you've been in IT for a long time or are just starting out, there is an expectation that everyone in IT should have some degree of expo- sure to InfoSec. A good way to do that is to learn from and get connected in the community. Cybersecurity is a fascinating and rapidly evolving area of IT. And those that are involved are friendly people who care passionately about keeping us all safe. With information from over 150 sourced references, and personal input from The Howler Hub community of security experts, this guide contains the key information to help you: • Understand key concepts that drive the security professional. • Learn a common language to engage with cybersecurity professionals. • Connect with sources to stay up-to-date on this evolving field. • Engage with cybersecurity experts and the threat hunting community at large. CONTENTS 01 02 03 History of Attackers + Common Cybersecurity Their Motives Attacks <pg num="001" /> <pg num="005" /> <pg num="007" /> 04 05 06 Terms to Know Experts to Blogs to Read <pg num="009" /> Follow <pg num="014" /> <pg num="013" /> 07 08 09 Events to Books to Read Movies + Shows Attend <pg num="017" /> to Watch <pg num="015" /> <pg num="019" /> 10 11 12 Communities Become a References to Engage Threat Hunter <pg num="023" /> <pg num="021" /> <pg num="022" /> 13 Appendices <pg num="024" /> <pg num="001" /> SEC.