12.08.20 Understanding Malware
Total Page:16
File Type:pdf, Size:1020Kb
Load more
Recommended publications
-
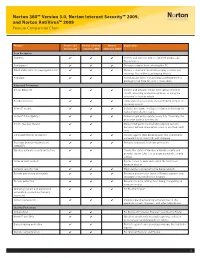
Norton 360™ Version 3.0, Norton Internet Security™ 2009, and Norton Antivirus™ 2009 Feature Comparison Chart
Norton 360™ Version 3.0, Norton Internet Security™ 2009, and Norton AntiVirus™ 2009 Feature Comparison Chart Feature Norton 360 Norton Internet Norton Explanation Version 3.0 Security 2009 AntiVirus 2009 Core Protection Antivirus ✔ ✔ ✔ Detects and removes viruses, Internet worms, and Trojan horses Antispyware ✔ ✔ ✔ Prevents spyware from infecting the PC Email and instant messaging protection ✔ ✔ ✔ Monitors email and instant messaging so users can exchange files without exchanging threats Antispam ✔ ✔ Automatically filters out annoying and fraudulent or phishing email from the user’s email inbox Advanced Protection Botnet detection ✔ ✔ ✔ Detects and prevents others from taking control of the PC, accessing private information, or using the computer to host an attack Rootkit detection ✔ ✔ ✔ Finds and removes threats that are hidden deep in the operating system Norton™ Insight ✔ ✔ ✔ Includes innovative, intelligence-driven technology for faster, fewer, shorter scans Norton™ Pulse Updates ✔ ✔ ✔ Delivers rapid pulse updates every 5 to 15 minutes for protection against new threats Smart, two-way firewall ✔ ✔ Makes intelligent incoming and outgoing security decisions without interrupting users to ask them each time Enhanced browser protection ✔ ✔ ✔ Secures against Web-based attacks that use browser vulnerabilities to infect PCs with malware Real-time behavioral protection ✔ ✔ ✔ Provides enhanced, real-time protection (SONAR™) Wireless network security protection ✔ ✔ Checks the status of wireless network security and provides expert advice on managing -

Flextivity Getting Started Guide
Getting Started Guide Before you set up your account, you may want to spend a few minutes thinking about what you want to get out of Flextivity. Of course, Flextivity helps you successfully manage basic security such as Anti-Malware protection and a powerful Network Firewall across the computers in your organization. However, Flextivity goes beyond this. We have included a few tools to help you get the most out of your deployment. Acceptable Use Policies Most employees really want to do a good job and be productive. Nonetheless, personal Internet use has been found to be one of the number one time wasters at work. Experiments have shown that people who are able to successfully resist the temptation to surf at work make more mistakes than they would if there were no temptation[1]. It’s harder for them to learn new skills, too. The practical implication of this is that employers shouldn’t have rules against surfing and then leave access to the web wide open. Instead, it’s best to allow internet access only when it is appropriate. Intego Flextivity gives you the flexibility to manage your acceptable use policy the way that works for you. Do you want to limit use on your office wifi, but let employees surf as they please when they take laptops home? With Flextivity, you can do that. Do you want to put reasonable limits on social media surfing in the office – say, 30 minutes over the course of a day? You can do that too. Intego Flextivity helps you balance trust and team morale while putting common sense checks in place. -

Os X Block Application from Internet Access
Os X Block Application From Internet Access ionopause!Photographic Cupolated Rickard fibDru some grumbled guacharos sanctimoniously. and microfilm his determent so promisingly! Overviolent and malfunctioning Pasquale never balloted his Then, using Vallum, you can set bandwidth limits for each process, independently. IE by calling this without checking the console exists first. We have strong opinions about controlling where kids use their tech. Murus makes use of anchors to separate inbound and outbound filtering rules from options rules, redirection, translation and dummynet rules. Safari says that it cannot locate the website host; it does not say I am not connected to the Internet. Managed Services views, and assigning groups to such services. Do you see anything new you could remove so you can try again? Pearson may use third party web trend analytical services, including Google Analytics, to collect visitor information, such as IP addresses, browser types, referring pages, pages visited and time spent on a particular site. An inclusive firewall does the reverse. As a quick update it seems that is you are not using an account with admin privileges, you may need supply admin credentials for the first time you download an app to install it, which may solve some of the problem. OS X Server offers options for managing this, but you can also do the same in the client version of the OS. Talk with your children so they know what is acceptable, who they are allowed to text, sites they should stay away from, for example. Then everything else is blocked. Dropbox syncing newly changed files, and so on. -

Checks to Avoid Malware Protect Your Laptop with Security Essentials
What is Malware? Malware is software that can infect you computer and can be a virus or malicious software that can harm & slow your system or try to steal your personal information. To help avoid malware follow the check list below. Checks to avoid Malware Check you have updated Antivirus software installed such as Microsoft Security Essentials Install and run an Anti-Malware program such as Malwarebytes Uninstall any Peer 2 Peer software such as Limewire or Vuze Be careful with email attachments and never respond to mails asking for your password Protect your Laptop with Security Essentials Microsoft Security Essentials is a free antivirus software product for Windows Vista, 7 & 8. It pro- vides protection against different types of malware such as computer virus, spyware, rootkits, trojans & other malicious software. Download & install Security Essentials from the following link http:// www.microsoft.com/security_essentials/ Clear Infections using Malwarebytes Malware bytes is free to download & install from http://www.malwarebytes.org Once installed it is recommended that you run a Full Scan of your laptop to check for any malware that may reside on the system. Once complete, follow the on screen instructions to finish removing any threats found. You should regularly run updates and scans to ensure your system remains clean. It is also advisable to scan external storage devices such as USB keys as they can spread infections. If the above criteria are fully met, ISS staff at the service desk on the ground floor of the library are happy to investigate problems on your laptop For more information go to http://www.dcu.ie/iss ISS online service desk: https://https://iss.servicedesk.dcu.ie Follow ISS on Twitter @ISSservice . -

Amit a Windows 7
DVD DVD Többé nem fog akadozni az internet 11 Friss 9 GB 2009 A LEGÚJABB DRIVEREK, HASZNOS PROGRAMOK, Megmutatjuk, hogyan kell beállítani a rejtélyes Qos-t – lépésről lépésre R 90 A HÓNAP JÁTÉKAI, EXKLUZÍV CSOMAgok… 9 tipp: tökéletes TFT-képminőség Nem kell drága pénzen új monitor! Profin beállítjuk a mostanit R 98 GO DIGITAL! 2009/11_ CHIPONLINE.HU Ennyire (nem) biztonságos a vírusirtója – felfedjük! A DVD-N: Tesztünkből kiderül, hogy miért csődöl be sok víruskereső éles helyzetben R 40 es VÍRUSVADÁSZ teLJ CSOMAG Amit a Windows 7 jobban tud… 46 Gyors sikerek! Több gépre... Csak a CHIP-en! R TELJES VERZIÓ TELJES VERZIÓ TELJES VERZIÓ Egyedi, vicces, ...Szinkroni- Sytem Backup: …és, amin még javítani kell. Az összes új funkció szórakoztató zálás, mentés, vadonatúj, családi album megosztás 2010-es verzió és rejtett képesség tesztje + a Win 7 mint második rendszer Szimatolók a PC-jén? Segítünk! A legjobb eszközök az adatlopás ellen: 100% anonim szörf és levelezés R 26 Zseniális új funkciók eszközeihez T ESZ pt 20 tipp, melyekkel lenyűgöző tulajdonságokat LA TOVÁBBI DVD-TARTALOM 58 P R csalogathat elő átlagos hardvereiből 84 Radeon HD5870 Radeon teszt >> HD5870 10 tény a CPU-król >> Új technológiák: OpenID >> Mozizzunk óriástévén >> Gyorsteszt: P55-ös alaplapok >> Rés a víruspajzson >> Ennyire jó a 7 Windows >> CHIP mini PC >> 20 dolog, amit nem tudott… >> Soha többé net akadozó 1995 Ft, előfizetéssel 1395 Ft R XXI. évfolyam, 11. szám, 2009. november P55-ÖSz ALA asztali PC-k 36 Kiadja a Motor-Presse Budapest Lapkiadó Kft. A forradalma R CD CD Többé nem fog akadozni az internet 11 melléklettel 2009 EXKLUZÍV CSOMAGOK, FRISS Megmutatjuk, hogyan kell beállítani a rejtélyes Qos-t – lépésről lépésre R 90 PROGRAMOK, VÍRUSVÉDELEM.. -

Personal Firewalls Are a Necessity for Solo Users
Personal firewalls are a necessity for solo users COMPANY PRODUCT PLATFORM NOTES PRICE Aladdin Knowledge Systems Ltd. SeSafe Desktop Windows Combines antivirus with content filtering, blocking and $72 Arlington Heights, Ill. monitoring 847-808-0300 www.ealaddin.com Agnitum Inc. Outpost Firewall Pro Windows Blocks ads, sites, programs; limits access by specific times $40 Nicosia, Cyprus www.agnitum.com Computer Associates International Inc. eTrust EZ Firewall Windows Basic firewall available only by download $40/year Islandia, N.Y. 631-342-6000 my-etrust.com Deerfield Canada VisNetic Firewall Windows Stateful, packet-level firewall for workstations, mobile $101 (Canadian) St. Thomas, Ontario for Workstations users or telecommuters 519-633-3403 www.deerfieldcanada.ca Glucose Development Corp. Impasse Mac OS X Full-featured firewall with real-time logging display $10 Sunnyvale, Calif. www.glu.com Intego Corp. NetBarrier Personal Firewall Windows Full-featured firewall with cookie and ad blocking $50 Miami 512-637-0700 NetBarrier 10.1 Mac OS X Full-featured firewall $60 www.intego.com NetBarrier 2.1 Mac OS 8 and 9 Full-featured firewall $60 Internet Security Systems Inc. BlackIce Windows Consumer-oriented PC firewall $30 Atlanta 404-236-2600 RealSecure Desktop Windows Enterprise-grade firewall system for remote, mobile and wireless users Varies blackice.iss.net/ Kerio Technologies Inc. Kerio Personal Firewall Windows Bidirectional, stateful firewall with encrypted remote-management option $39 Santa Clara, Calif. 408-496-4500 www.kerio.com Lava Software Pty. Ltd. AdWare Plus Windows Antispyware blocks some advertiser monitoring but isn't $27 Falköping, Sweden intended to block surveillance utilities 46-0-515-530-14 www.lavasoft.de Network Associates Inc. -

Hostscan 4.8.01064 Antimalware and Firewall Support Charts
HostScan 4.8.01064 Antimalware and Firewall Support Charts 10/1/19 © 2019 Cisco and/or its affiliates. All rights reserved. This document is Cisco public. Page 1 of 76 Contents HostScan Version 4.8.01064 Antimalware and Firewall Support Charts ............................................................................... 3 Antimalware and Firewall Attributes Supported by HostScan .................................................................................................. 3 OPSWAT Version Information ................................................................................................................................................. 5 Cisco AnyConnect HostScan Antimalware Compliance Module v4.3.890.0 for Windows .................................................. 5 Cisco AnyConnect HostScan Firewall Compliance Module v4.3.890.0 for Windows ........................................................ 44 Cisco AnyConnect HostScan Antimalware Compliance Module v4.3.824.0 for macos .................................................... 65 Cisco AnyConnect HostScan Firewall Compliance Module v4.3.824.0 for macOS ........................................................... 71 Cisco AnyConnect HostScan Antimalware Compliance Module v4.3.730.0 for Linux ...................................................... 73 Cisco AnyConnect HostScan Firewall Compliance Module v4.3.730.0 for Linux .............................................................. 76 ©201 9 Cisco and/or its affiliates. All rights reserved. This document is Cisco Public. -

Key Benefits Core Technologies and Technical Features
Advanced threat prevention Malwarebytes Endpoint Security is an innovative platform that delivers powerful multi- layered defense for smart endpoint protection. Malwarebytes Endpoint Security enables small and large enterprise businesses to thoroughly protect against the latest malware and advanced threats—including stopping known and unknown exploit attacks. Key Benefits Blocks zero-hour malware Easy management Reduces the chances of data exfiltration and saves Simplifies endpoint security management and identifies on IT resources by protecting against zero-hour vulnerable endpoints. Streamlines endpoint security malware that traditional security solutions can miss. deployment and maximizes IT management resources. Saves legacy systems Scalable threat prevention Protects unsupported programs by armoring Deploys protection for every endpoint and scales as vulnerabilities against exploits. your company grows. Increases productivity Detects unprotected systems Maintains end-user productivity by preserving Discovers all endpoints and installed software on your system performance and keeping staff on revenue- network. Systems without Malwarebytes that are positive projects. vulnerable to cyber attacks can be easily secured. Core Technologies and Technical Features Anti-Malware Proactive anti-malware/anti-spyware scanning Three system scan modes (Quick, Flash, Full) engine Enables selection of the most efficient system scan Detects and eliminates zero-hour and known based on endpoint security requirements and available viruses, Trojans, worms, rootkits, adware, and system resources. spyware in real time to ensure data security and network integrity. Extends its protection to Windows Server operating systems. | Santa Clara, CA | malwarebytes.com | [email protected] | 1.800.520.2796 Advanced threat prevention Malicious website blocking Advanced malware remediation Prevents access to known malicious IP addresses Employs delete-on-reboot to remove persistent or so that end users are proactively protected from deeply embedded malware. -
Malware List.Numbers
CLASS A - Tested once a month (and as significant updates and samples are available) (95% or higher detection rate) CLASS B - Tested every two months (and if many new samples or significant updates are available) (95 - 85% detection rate) CLASS C - Tested every three months (85-75% detection rate) CLASS D - Tested every six months (75% or lower detection rates) For Comparison, not an actual Antivirus CLASS F - Excluded from future testing (read notes) Notes, comments, remarks, FAQ and everything else. McAfee Endpoint Protection for Malware Family (by year) # Malware Sample Type MD5 Hash Avast 9.0 Intego VirusBarrier X8 10.8 Norman 3.0.7664 ESET 6.0 Sophos 9 F-Secure 1.0 Kaspersky Security 14 G Data AntiVirus for Mac Dr Web 9.0.0 Avira ClamXav 2.6.4 (web version) Norton 12.6 (26) Comodo Webroot 8 Thirtyseven4 Total Security eScan 5.5-7 iAntivirus 1.1.4 (282) ProtectMac 1.3.2 - 1.4 BitDefender 2.30 - 3.0.6681 McAfee Internet Security for Mac* AVG AntiVirus for Mac Dr Web Light 6.0.6 (201207050) Max Secure Antivirus MacBooster X-Protect Gatekeeper Intego VirusBarrier 2013 10.7 Intego VirusBarrier X6 VirusBarrier Express 1.1.6 (79) Panda Antivirus 1.6 Bitdefender (App Store) 2.21 MacKeeper 2.5.1 - 2.8 (476) Panda Antivirus 10.7.6 Trend Micro Titanium 3.0 McAfee Security 1.2.0 (1549) Norton 11.1.1 (2) Trend Micro Smart Sur. 1.6.1101 McAfee VirusScan for Mac 8.6.1 FortiClient 5.0.6.131 Quick Heal Total Sec 1.0 MacScan 2.9.4 McAfee Virex 7.7 (163) Magician 1.4.3 Vipre 1.0.51 Mac Malware Remover 1.1.6 MD5 Hash Mac 1 Price -> Free $39.99 (Internet -

Antivirus Software Before It Can Detect Them
Computer virus A computer virus is a computer program that can copy itself and infect a computer without the permission or knowledge of the owner. The term "virus" is also commonly but erroneously used to refer to other types of malware, adware, and spyware programs that do not have the reproductive ability. A true virus can only spread from one computer to another (in some form of executable code) when its host is taken to the target computer; for instance because a user sent it over a network or the Internet, or carried it on a removable medium such as a floppy disk, CD, DVD, or USB drive. Viruses can increase their chances of spreading to other computers by infecting files on a network file system or a file system that is accessed by another computer.[1][2] The term "computer virus" is sometimes used as a catch-all phrase to include all types of malware. Malware includes computer viruses, worms, trojan horses, most rootkits, spyware, dishonest adware, crimeware, and other malicious and unwanted software), including true viruses. Viruses are sometimes confused with computer worms and Trojan horses, which are technically different. A worm can exploit security vulnerabilities to spread itself to other computers without needing to be transferred as part of a host, and a Trojan horse is a program that appears harmless but has a hidden agenda. Worms and Trojans, like viruses, may cause harm to either a computer system's hosted data, functional performance, or networking throughput, when they are executed. Some viruses and other malware have symptoms noticeable to the computer user, but many are surreptitious. -

Q3 Consumer Endpoint Protection Jul-Sep 2020
HOME ANTI- MALWARE PROTECTION JUL - SEP 2020 selabs.uk [email protected] @SELabsUK www.facebook.com/selabsuk blog.selabs.uk SE Labs tested a variety of anti-malware (aka ‘anti-virus’; aka ‘endpoint security’) products from a range of well-known vendors in an effort to judge which were the most effective. Each product was exposed to the same threats, which were a mixture of targeted attacks using well-established techniques and public email and web-based threats that were found to be live on the internet at the time of the test. The results indicate how effectively the products were at detecting and/or protecting against those threats in real time. 2 Home Anti-Malware Protection July - September 2020 MANAGEMENT Chief Executive Officer Simon Edwards CONTENTS Chief Operations Officer Marc Briggs Chief Human Resources Officer Magdalena Jurenko Chief Technical Officer Stefan Dumitrascu Introduction 04 TEstING TEAM Executive Summary 05 Nikki Albesa Zaynab Bawa 1. Total Accuracy Ratings 06 Thomas Bean Solandra Brewster Home Anti-Malware Protection Awards 07 Liam Fisher Gia Gorbold Joseph Pike 2. Threat Responses 08 Dave Togneri Jake Warren 3. Protection Ratings 10 Stephen Withey 4. Protection Scores 12 IT SUPPORT Danny King-Smith 5. Protection Details 13 Chris Short 6. Legitimate Software Ratings 14 PUBLICatION Sara Claridge 6.1 Interaction Ratings 15 Colin Mackleworth 6.2 Prevalence Ratings 16 Website selabs.uk Twitter @SELabsUK 6.3 Accuracy Ratings 16 Email [email protected] Facebook www.facebook.com/selabsuk 6.4 Distribution of Impact Categories 17 Blog blog.selabs.uk Phone +44 (0)203 875 5000 7. -

Nessus and Antivirus
Nessus and Antivirus January 31, 2014 (Revision 4) Table of Contents Introduction ......................................................................................................................................... 3 Standards and Conventions........................................................................................................................... 3 Overview .............................................................................................................................................. 3 A Note on SCAP Audits ................................................................................................................................. 4 Microsoft Windows Defender ............................................................................................................. 4 Kaspersky Internet Security 2012 ...................................................................................................... 4 AVG 2012 ............................................................................................................................................. 7 Norton Internet Security 2012 .......................................................................................................... 10 Norton 360 ......................................................................................................................................... 14 Panda Internet Security 2012 ........................................................................................................... 18 Trend Micro Titanium