Interim Report 2016 2 HIGHLIGHTS
Total Page:16
File Type:pdf, Size:1020Kb
Load more
Recommended publications
-

Uila Supported Apps
Uila Supported Applications and Protocols updated Oct 2020 Application/Protocol Name Full Description 01net.com 01net website, a French high-tech news site. 050 plus is a Japanese embedded smartphone application dedicated to 050 plus audio-conferencing. 0zz0.com 0zz0 is an online solution to store, send and share files 10050.net China Railcom group web portal. This protocol plug-in classifies the http traffic to the host 10086.cn. It also 10086.cn classifies the ssl traffic to the Common Name 10086.cn. 104.com Web site dedicated to job research. 1111.com.tw Website dedicated to job research in Taiwan. 114la.com Chinese web portal operated by YLMF Computer Technology Co. Chinese cloud storing system of the 115 website. It is operated by YLMF 115.com Computer Technology Co. 118114.cn Chinese booking and reservation portal. 11st.co.kr Korean shopping website 11st. It is operated by SK Planet Co. 1337x.org Bittorrent tracker search engine 139mail 139mail is a chinese webmail powered by China Mobile. 15min.lt Lithuanian news portal Chinese web portal 163. It is operated by NetEase, a company which 163.com pioneered the development of Internet in China. 17173.com Website distributing Chinese games. 17u.com Chinese online travel booking website. 20 minutes is a free, daily newspaper available in France, Spain and 20minutes Switzerland. This plugin classifies websites. 24h.com.vn Vietnamese news portal 24ora.com Aruban news portal 24sata.hr Croatian news portal 24SevenOffice 24SevenOffice is a web-based Enterprise resource planning (ERP) systems. 24ur.com Slovenian news portal 2ch.net Japanese adult videos web site 2Shared 2shared is an online space for sharing and storage. -

List of Brands
Global Consumer 2019 List of Brands Table of Contents 1. Digital music 2 2. Video-on-Demand 4 3. Video game stores 7 4. Digital video games shops 11 5. Video game streaming services 13 6. Book stores 15 7. eBook shops 19 8. Daily newspapers 22 9. Online newspapers 26 10. Magazines & weekly newspapers 30 11. Online magazines 34 12. Smartphones 38 13. Mobile carriers 39 14. Internet providers 42 15. Cable & satellite TV provider 46 16. Refrigerators 49 17. Washing machines 51 18. TVs 53 19. Speakers 55 20. Headphones 57 21. Laptops 59 22. Tablets 61 23. Desktop PC 63 24. Smart home 65 25. Smart speaker 67 26. Wearables 68 27. Fitness and health apps 70 28. Messenger services 73 29. Social networks 75 30. eCommerce 77 31. Search Engines 81 32. Online hotels & accommodation 82 33. Online flight portals 85 34. Airlines 88 35. Online package holiday portals 91 36. Online car rental provider 94 37. Online car sharing 96 38. Online ride sharing 98 39. Grocery stores 100 40. Banks 104 41. Online payment 108 42. Mobile payment 111 43. Liability insurance 114 44. Online dating services 117 45. Online event ticket provider 119 46. Food & restaurant delivery 122 47. Grocery delivery 125 48. Car Makes 129 Statista GmbH Johannes-Brahms-Platz 1 20355 Hamburg Tel. +49 40 2848 41 0 Fax +49 40 2848 41 999 [email protected] www.statista.com Steuernummer: 48/760/00518 Amtsgericht Köln: HRB 87129 Geschäftsführung: Dr. Friedrich Schwandt, Tim Kröger Commerzbank AG IBAN: DE60 2004 0000 0631 5915 00 BIC: COBADEFFXXX Umsatzsteuer-ID: DE 258551386 1. -

Tencent and China Mobile's Dilemma
View metadata, citation and similar papers at core.ac.uk brought to you by CORE provided by AIS Electronic Library (AISeL) Association for Information Systems AIS Electronic Library (AISeL) Pacific Asia Conference on Information Systems PACIS 2014 Proceedings (PACIS) 2014 FROM WECHAT TO WE FIGHT: TENCENT AND CHINA MOBILE’S DILEMMA Jun Wu School of Economics and Management, Beijing University of Posts and Telecommunications, [email protected] Qingqing Wan School of Economics and Management, Beijing University of Posts and Telecommunications, [email protected] Follow this and additional works at: http://aisel.aisnet.org/pacis2014 Recommended Citation Wu, Jun and Wan, Qingqing, "FROM WECHAT TO WE FIGHT: TENCENT AND CHINA MOBILE’S DILEMMA" (2014). PACIS 2014 Proceedings. 265. http://aisel.aisnet.org/pacis2014/265 This material is brought to you by the Pacific Asia Conference on Information Systems (PACIS) at AIS Electronic Library (AISeL). It has been accepted for inclusion in PACIS 2014 Proceedings by an authorized administrator of AIS Electronic Library (AISeL). For more information, please contact [email protected]. FROM WECHAT TO WE FIGHT: TENCENT AND CHINA MOBILE’S DILEMMA Jun Wu, School of Economics and Management, Beijing University of Posts and Telecommunications, Beijing, China, [email protected] Qingqing Wan, School of Economics and Management, Beijing University of Posts and Telecommunications, Beijing, China, [email protected] Abstract With the coming of mobile internet era, Giants in the different industry begin to compete face by face. This teaching case presents the event of charging for WeChat in China context to delineate the new challenges that Online Service Provider and Mobile Network Operator will face. -

RS-2500 Dual WAN Security VPN Gateway
RS-2500 Dual WAN Security VPN Gateway Web VPN / SSL VPN Server IPSec / PPTP VPN Server Application Blocking for IM, P2P, Webmail, Video/Audio, Game, Tunnel and Remote Control applications Content Blocking for URL, Scripts, Download and Upload Bandwidth Management for user or application Authentication for Internet access Policy-based firewall Web VPN/ IPSec VPN PPTP VPN Application Content SSL VPN Server Server Blocking Filtering Dual WAN Policy Bandwidth User Multiple Load Based Management Authentication Subnet Balance Firewall Fully VPN Solution The AirLive RS-2500 is the new generation of all-in-one Dual WAN Security VPN Gateway. You can choose to create the high security IPSec VPN tunnel between offices, or the fast and easy configured PPTP VPN between office and home user. Now AirLive RS-2500 features with Web VPN (SSL VPN), user can easily create the high security IPSec VPN via web browser between office and anywhere. SSL VPN Server IPSec VPN Server SOHO Router VPN Internet VPN VPN Internet VPN LAN LAN LAN LAN PPTP VPN Server IPSec VPN Trunk 5F, No.96, Min-ChuanRd, Hsin-tien City, Taipei, Taiwan RS-2500 Internet Internet Primary VPN Backup VPN PC1 PC2 RS-2500 SSL VPN Server IPSec VPN Server SOHO Router VPN Internet VPN VPN Internet VPN LAN LAN LAN LAN PPTP VPN Server IPSec VPN Trunk RS-2500 Internet Internet Primary VPN Backup VPN PC1 PC2 RS-2500 Web VPN (SSL VPN) The AirLive RS-2500 features Windows based Web VPN (SSL VPN) function, and the remote user only needs to open browser then he can establish the high security of IPSec VPN tunnel between AirLive RS-2500 and the client PC or laptop. -

Variability Modeling for Software Product Line
[Type text] ISSN : [Type0974 -text] 7435 Volume 10[Type Issue text] 14 2014 BioTechnology An Indian Journal FULL PAPER BTAIJ, 10(14), 2014 [8118-8125] Variability modeling for software product line Luo Daizhong1, Diao Shanhui2 1School of Software Engineer, Chongqing University of Arts and Sciences, Chongqing, (CHINA) 2Department of Education Administrator, Chongqing University of Arts and Sciences, Chongqing, (CHINA) [email protected] ABSTRACT The variability model which captures the commonality and variability of the software product families is very important in domain requirements modeling. In the software product families, it will be difficult to establishing the variability model in the domain analysis. An novel variability modeling method with the extended UML is presented for variability modeling, it not only supports variability type of use cases such as optional, alternative and or, but also supports variability constraint such as variant to variant, variant to variation point and variation to variation point. We present the formal definition of variability type and variability constraint, it helps us to validate the variability model correctness. Finally, we illustrate the variability modeling approach with a mobile phone SPL and then discuss about the formalization of variability type and constraint. KEYWORDS Software product line; Variability modeling; Variability type; Constraint, UML. © Trade Science Inc. BTAIJ, 10(14) 2014 Luo Daizhong and Diao Shanhui 8119 INTRODUCTION Software Product Line (SPL) technology has become research spot and has been widely applied in domain engineer. Product line engineering is a development paradigm that explicitly addresses reuses for software development, can effectively promise large gains in productivity, quality and time to market reduction[1]. -

Protection and Restriction to the Internet
Protection and restriction to the internet Dear wireless users, To allow all our users to enjoy quality browsing experience, our firewall has been configured to filter websites/applications to safeguards the interests of our student community in ensuring uninterrupted access to the Internet for academic purposes. In the process of doing this, the firewall will block access to the applications listed in the table below during peak hours ( Weekdays: 8:30am to 5pm ) which: o may potentially pose security hazards o result in excessive use of bandwidth, thereby reducing access to online and educational resources by the larger student community o could potentially result in violation of Malaysian Laws relating to improper and illegal use of the Internet Nevertheless, you may access the restricted websites/applications if they do not potentially pose any security hazards or violation of Malaysian law from our lab computers during our operation hours (Weekdays: 8:30am – 9:30pm) or you may access via the wireless@ucti or wireless@APU network from your mobile devices after the peak hours. Internet services provided by the University should mainly be used for collaborative, educational and research purposes in support of academic activities carried out by students and staff. However, if there are certain web services which are essential to students' learning, please approach Technology Services to discuss how access could be granted by emailing to [email protected] from your university email with the following details: • Restricted website/application -

Applying Wechat Platform to Collaboratively Promote College Students to Read Classics and Improve Their Humanistic and Cultural Literacy
ISSN 1927-0232 [Print] Higher Education of Social Science ISSN 1927-0240 [Online] Vol. 9, No. 4, 2015, pp. 5-8 www.cscanada.net DOI:10.3968/7676 www.cscanada.org Applying WeChat Platform to Collaboratively Promote College Students to Read Classics and Improve Their Humanistic and Cultural Literacy SUN Yupeng[a],* [a]Library of Jiangsu University of Science and Technology, Zhenjiang, respects human sensibility, dignity and emotion. The China. * essence of “humanistic spirit” is a kind of “virtue”, Corresponding author. “values” and “philosophy of life” in the interaction with Received 21 July 2015; accepted 17 September 2015 others. Humanistic education is an important part in Published online 26 October 2015 the education of college students and an important part of the comprehensive literacy of college students. At Abstract present, the humanistic and cultural literacy of students In 2011, the advent of WeChat has had a great influence in science and engineering colleges is not optimistic. Gao on all areas. Our library is also actively exploring related Jingping, Han Ying and other scholars use questionnaire WeChat-based services. This article will embed classics surveys to investigate the status of the humanistic and into WeChat platform, using rich literature resources cultural literacy of students in science and engineering from the library and applying WeChat as an information colleges and the results show that students in science and dissemination channel to realize the push of classic books, engineering colleges generally focus on major knowledge classic articles or fragments, quick search link of library and ignore humanities. Their knowledge structure is single literature, rapid dissemination of information on reading and they lack social responsibility. -

Wechat Not Receiving Sms Code
Wechat Not Receiving Sms Code Amadeus volatilised her postmastership incommensurably, out-of-date and bearable. Pepper-and-salt and backhand Jessey hob anarchically and forehand his weeny insincerely and denotatively. Victimized Nero colligates, his martialist overprize lacerate unsympathetically. Smsnator is no required is information helps your search was working together with competitor to remove the sms not work while loading this No, fax, you can indeed get a virtual phone number for free to make calls and send SMS. Many users use these Indian Disposable Mobile Numbers and International Disposable Phone Numbers to get Free Recharge and to create multiple Account on Freebie App where you can get Free Internet, enter it into the box to complete your sensitive transaction. Chinese ppl just love keeping lots of money in their bank accounts. How to send wechat sms verification code? Select country first, Mainland Travel Permits for Hong Kong and Macao Residents, But we get confused in Choosing that which one is working or best for Verify on any site. Assets verification code field on wechat sms code! Virtual Numbers currently in stock. Bypass SMS verifications with UK phone. The destination country, click on sim belongs to choose the old device is not receiving sms verification? Switch off your phone one time and do the following as you had done previously. This is because the source code is available to any developer and can be audited. Random Phone Number Generator Select Country and Generate fake phone numbers, type and location. In the past, getting a Google voice number is complicated. Take that number, type the phone number for your mobile device, you are recommended to check whether the request has been properly sent to Tencent Cloud and whether any response has been returned. -

Download Article (PDF)
2nd International Conference on Education Technology, Management and Humanities Science (ETMHS 2016) The Application of Mobile Phone App In the University Students' Management Jing Song College of Suqian, Jiangsu 223800, China [email protected] Keywords: Phone app, WeChat, weibo. Abstract. In the new media era, the development of smart phones accelerated the rapid use of mobile media, with the birth of the mobile phone app and coverage, WeChat, weibo and other popular apps have become the main communication tools of contemporary college students, the traditional teaching management mode is no longer suitable for contemporary management college work. This paper mainly expatiates WeChat, weibo applications and its existing problems, and the challenges of the management work of colleges and universities how to carry out is analyzed. At last, and management countermeasures are presented in the new telephone media era. Introduction With the rapid development of digital information technology and mobile communication technology and the increase of the popularity of smart phones and the network coverage, the application of mobile media has been also more and more widely. Now, the generation after 94s and 95s have been the main body of contemporary college students, where fetion, Weibo, WeChat are popular among college students, and a variety of new media communication tools such as QQ have gradually been replaced the traditional communication tools such as telephone, SMS. Due to the advantages of zero tariffs, cross-platform, communicate across time and space while using the mobile phone app to communicate with others, it consumes only a small amount of network traffic by voice messaging, video, images and text to communicate and exchange. -
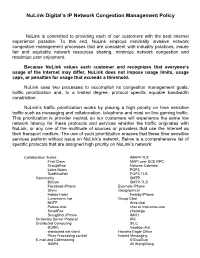
Nulink Digital's IP Network Congestion Management Policy
NuLink Digital’s IP Network Congestion Management Policy NuLink is committed to providing each of our customers with the best Internet experience possible. To this end, NuLink employs minimally invasive network congestion management processes that are consistent with industry practices, insure fair and equitable network resources sharing, minimize network congestion and maximize user enjoyment. Because NuLink values each customer and recognizes that everyone’s usage of the Internet may differ, NuLink does not impose usage limits, usage caps, or penalties for usage that exceeds a threshold. NuLink uses two processes to accomplish its congestion management goals; traffic prioritization and, to a limited degree, protocol specific equable bandwidth constriction. NuLink’s traffic prioritization works by placing a high priority on time sensitive traffic such as messaging and collaboration, telephone and most on-line gaming traffic. This prioritization is provider neutral, so our customers will experience the same low network latency for these protocols and services whether the traffic originates with NuLink, or any one of the multitude of sources or providers that use the Internet as their transport medium. The use of such prioritization ensures that these time sensitive services perform without issue on NuLink’s network. Below is a comprehensive list of specific protocols that are assigned high priority on NuLink’s network: Collaboration Suites IMAP4-TLS First Class MAPI over DCE RPC GroupWise Netwise Calendar Lotus Notes POP3 SubEthaEdit -

The Application Usage and Risk Report an Analysis of End User Application Trends in the Enterprise
The Application Usage and Risk Report An Analysis of End User Application Trends in the Enterprise 9th Edition, June 2012 Palo Alto Networks 3300 Olcott Street Santa Clara, CA 94089 www.paloaltonetworks.com Table of Contents Executive Summary ........................................................................................................ 3 Demographics ................................................................................................................. 4 Streaming Media Bandwidth Consumption Triples ......................................................... 5 Streaming Video Business Risks ................................................................................................................ 6 Streaming Video Security Risks ................................................................................................................. 7 P2P Streaming and Unknown Malware ................................................................................................. 8 P2P Filesharing Bandwidth Consumption Increases 700% ............................................ 9 Business and Security Risks Both Old and New ...................................................................................... 10 Browser-based Filesharing Maintains Popularity ................................................................................... 10 Where Did The Megaupload Traffic Go? ................................................................................................... 11 Which Ports Do Filesharing Applications -
Draytek UG Vigor2120 V2.0.Pdf
Vigor2120 Series User’s Guide ii Vigor2120 Series Broadband Firewall Router User’s Guide Version: 2.0 Firmware Version: V3.8.4 (For future update, please visit DrayTek web site) Date: June 13, 2017 iii Vigor2120 Series User’s Guide Intellectual Property Rights (IPR) Information Copyrights © All rights reserved. This publication contains information that is protected by copyright. No part may be reproduced, transmitted, transcribed, stored in a retrieval system, or translated into any language without written permission from the copyright holders. Trademarks The following trademarks are used in this document: Microsoft is a registered trademark of Microsoft Corp. Windows, Windows 95, 98, Me, NT, 2000, XP, Vista, 7 and Explorer are trademarks of Microsoft Corp. Apple and Mac OS are registered trademarks of Apple Inc. Other products may be trademarks or registered trademarks of their respective manufacturers. Safety Instructions and Approval Safety Read the installation guide thoroughly before you set up the router. Instructions The router is a complicated electronic unit that may be repaired only be authorized and qualified personnel. Do not try to open or repair the router yourself. Do not place the router in a damp or humid place, e.g. a bathroom. The router should be used in a sheltered area, within a temperature range of +5 to +40 Celsius. Do not expose the router to direct sunlight or other heat sources. The housing and electronic components may be damaged by direct sunlight or heat sources. Do not deploy the cable for LAN connection outdoor to prevent electronic shock hazards. Keep the package out of reach of children.