Tracking Computer Use with the Windows® Registry Dataset Doug
Total Page:16
File Type:pdf, Size:1020Kb
Load more
Recommended publications
-

Why Is C. Diff So Hard to Culture and Kill?
Why is C. diff so hard to culture and kill? Clostridium difficile, commonly referred to as C. diff, is the #1 nosocomial infection in hospitals (it actually kicked staph infections out of the top spot). At Assurance, we test for this organism as part of our Gastrointestinal (GI) panel. C. diff is a gram-positive anaerobe, meaning it does not like oxygen. Its defensive mechanism is sporulation – where it essentially surrounds itself with a tough outer layer of keratin and can live in water, soil, etc. for over a decade. For reference, anthrax is another organism that sporulates. Once C. diff sporulates, it is very hard to kill and in fact, bleach is one of the only disinfectants that work. Unfortunately, it can spread quickly throughout hospitals. Spores of C. diff are found all over hospital surfaces and even in some hospital water systems. It’s the most threatening for those who are immunocompromised or the elderly, who are the most likely to end up with C. diff infections. With our PCR testing, we’re looking for the C. diff organism itself but we’re also looking at the production of toxin. Unless it produces toxins A AND B together OR toxin B, C. diff doesn’t cause severe disease. Many babies are exposed to it during birth or in the hospitals and may test positive on our GI panel. Unless they are expressing those toxins (both toxin A&B or just toxin B) it is not considered a clinical infection. Studies show that toxins A&B together causes infection, as well as toxin B. -

Powershell Delete Registry Key Remote Computer
Powershell delete registry key remote computer In Use PowerShell to Edit the Registry on Remote Computers, I talked cmdlet to find and delete the registry key on all remote servers that are. There is a pre powershell registry tool called reg. It will perform registry operations on remote computers. REG DELETE /? REG DELETE. I am trying to create a PowerShell script that deletes two keys on a remote computer. (One key in the code below) I have successfully created a. The Remove-RegistryKey cmdlet is used to delete registry keys and values on the local or a remote computer. I'm working on remotely modifying an autologin key value on batches of {Remove-ItemProperty -Path "HKLM:\Software\Microsoft\Windows Solution: $Computers = Get-Content "C:\"$Path me with a powershell script that can modify registry key on a list of remote computers Basically, I need to modify a product name in add/remove programs list. Then I need to find out whether I got the admin permission on the remote machines. Lastly, remove the specified reg keys. #Read the machine. Deleting Specific Remote Registry Entry - Powershell playing about with trying to write a script to delete a specific software GPO deployed to a remote computer. $Items = $Keys | Foreach-Object {Get-ItemProperty $_. $RegistryKeyValue = $ue($RegistryKeyName) Write-output "Attempting to delete $RegistryKeyName on $Computer `r ". Powershell: Delete Registry Key On Remote Server To run a script on one or many remote computers, use the FilePath parameter of the. I am having trouble changing registry keys. I know the trouble is Set-ItemProperty does not support connections to remote computers. -
Operational and Administrative Guidance
Operational and Administrative Guidance Microsoft Windows Server, Microsoft Windows 10 version 1909 (November 2019 Update), Microsoft Windows Server 2019 version 1809 Hyper-V Common Criteria Evaluation under the Protection Profile for Virtualization, including the Extended Package for Server Virtualization Revision date: January 15, 2021 © 2021 Microsoft. All rights reserved. Microsoft Windows Server and Windows 10 Hyper-V Administrative Guidance Copyright and disclaimer The information contained in this document represents the current view of Microsoft Corporation on the issues discussed as of the date of publication. Because Microsoft must respond to changing market conditions, it should not be interpreted to be a commitment on the part of Microsoft, and Microsoft cannot guarantee the accuracy of any information presented after the date of publication. This document is for informational purposes only. MICROSOFT MAKES NO WARRANTIES, EXPRESS OR IMPLIED, AS TO THE INFORMATION IN THIS DOCUMENT. Complying with all applicable copyright laws is the responsibility of the user. This work is licensed under the Creative Commons Attribution-NoDerivs-NonCommercial VLicense (which allows redistribution of the work). To view a copy of this license, visithttp://creativecommons.org/licenses/by-nd-nc/1.0/ or send a letter to Creative Commons, 559 Nathan Abbott Way, Stanford, California 94305, USA. Microsoft may have patents, patent applications, trademarks, copyrights, or other intellectual property rights covering subject matter in this document. Except as expressly provided in any written license agreement from Microsoft, the furnishing of this document does not give you any license to these patents, trademarks, copyrights, or other intellectual property. The example companies, organizations, products, people and events depicted herein are fictitious. -

Oracle Database Platform Guide for Windows
Oracle® Database Platform Guide 10g Release 1 (10.1) for Windows Part No. B10113-01 December 2003 Oracle Database Platform Guide, 10g Release 1 (10.1) for Windows Part No. B10113-01 Copyright © 1996, 2003 Oracle Corporation. All rights reserved. Primary Author: Craig B. Foch Contributing Author: Mark Kennedy and Helen Slattery Contributor: David Collelo The Programs (which include both the software and documentation) contain proprietary information of Oracle Corporation; they are provided under a license agreement containing restrictions on use and disclosure and are also protected by copyright, patent and other intellectual and industrial property laws. Reverse engineering, disassembly or decompilation of the Programs, except to the extent required to obtain interoperability with other independently created software or as specified by law, is prohibited. The information contained in this document is subject to change without notice. If you find any problems in the documentation, please report them to us in writing. This document is not warranted to be error-free. Except as may be expressly permitted in your license agreement for these Programs, no part of these Programs may be reproduced or transmitted in any form or by any means, electronic or mechanical, for any purpose. If the Programs are delivered to the U.S. Government or anyone licensing or using the programs on behalf of the U.S. Government, the following notice is applicable: Restricted Rights Notice Programs delivered subject to the DOD FAR Supplement are "commercial computer software" and use, duplication, and disclosure of the Programs, including documentation, shall be subject to the licensing restrictions set forth in the applicable Oracle license agreement. -
Compressed Modes User's Guide
Drivers for Windows Compressed Modes User’s Guide Version 2.0 NVIDIA Corporation August 27, 2002 NVIDIA Drivers Compressed Modes User’s Guide Version 2.0 Published by NVIDIA Corporation 2701 San Tomas Expressway Santa Clara, CA 95050 Copyright © 2002 NVIDIA Corporation. All rights reserved. This software may not, in whole or in part, be copied through any means, mechanical, electromechanical, or otherwise, without the express permission of NVIDIA Corporation. Information furnished is believed to be accurate and reliable. However, NVIDIA assumes no responsibility for the consequences of use of such information nor for any infringement of patents or other rights of third parties, which may result from its use. No License is granted by implication or otherwise under any patent or patent rights of NVIDIA Corporation. Specifications mentioned in the software are subject to change without notice. NVIDIA Corporation products are not authorized for use as critical components in life support devices or systems without express written approval of NVIDIA Corporation. NVIDIA, the NVIDIA logo, GeForce, GeForce2 Ultra, GeForce2 MX, GeForce2 GTS, GeForce 256, GeForce3, Quadro2, NVIDIA Quadro2, Quadro2 Pro, Quadro2 MXR, Quadro, NVIDIA Quadro, Vanta, NVIDIA Vanta, TNT2, NVIDIA TNT2, TNT, NVIDIA TNT, RIVA, NVIDIA RIVA, NVIDIA RIVA 128ZX, and NVIDIA RIVA 128 are registered trademarks or trademarks of NVIDIA Corporation in the United States and/or other countries. Intel and Pentium are registered trademarks of Intel. Microsoft, Windows, Windows NT, Direct3D, DirectDraw, and DirectX are registered trademarks of Microsoft Corporation. CDRS is a trademark and Pro/ENGINEER is a registered trademark of Parametric Technology Corporation. OpenGL is a registered trademark of Silicon Graphics Inc. -

Unix Programmer's Manual
There is no warranty of merchantability nor any warranty of fitness for a particu!ar purpose nor any other warranty, either expressed or imp!ied, a’s to the accuracy of the enclosed m~=:crials or a~ Io ~helr ,~.ui~::~::.j!it’/ for ~ny p~rficu~ar pur~.~o~e. ~".-~--, ....-.re: " n~ I T~ ~hone Laaorator es 8ssumg$ no rO, p::::nS,-,,.:~:y ~or their use by the recipient. Furln=,, [: ’ La:::.c:,:e?o:,os ~:’urnes no ob~ja~tjon ~o furnish 6ny a~o,~,,..n~e at ~ny k:nd v,,hetsoever, or to furnish any additional jnformstjcn or documenta’tjon. UNIX PROGRAMMER’S MANUAL F~ifth ~ K. Thompson D. M. Ritchie June, 1974 Copyright:.©d972, 1973, 1974 Bell Telephone:Laboratories, Incorporated Copyright © 1972, 1973, 1974 Bell Telephone Laboratories, Incorporated This manual was set by a Graphic Systems photo- typesetter driven by the troff formatting program operating under the UNIX system. The text of the manual was prepared using the ed text editor. PREFACE to the Fifth Edition . The number of UNIX installations is now above 50, and many more are expected. None of these has exactly the same complement of hardware or software. Therefore, at any particular installa- tion, it is quite possible that this manual will give inappropriate information. The authors are grateful to L. L. Cherry, L. A. Dimino, R. C. Haight, S. C. Johnson, B. W. Ker- nighan, M. E. Lesk, and E. N. Pinson for their contributions to the system software, and to L. E. McMahon for software and for his contributions to this manual. -

Windows Registry,Some Basic Understanding
WINDOWS REGISTRY,SOME BASIC UNDERSTANDING For the peoples who use Windows, „Windows Registry‟ is not a new word at all. The registry is a central database of all configuration settings for most of the applications installed on the computer. Windows stores all its settings in this „Registry‟ itself. The „Windows Registry Editor‟ allows us to configure many hidden settings for windows and other applications installed, which are not accessible by the interface of the particular software itself. You can easily manipulate and modify the values of registry and improve the PC‟s performance. However, do it carefully, because modify the right setting and your computer gets a boost, modify the wrong one and you end up with a non-booting system. In my previous post I wrote about „Autoruns‟, it can also manipulate registry. (Read here) To edit registry, we can use „Windows Registry Editor‟, which is preinstalled in Windows itself. It can be launched by using the command „regedit‟ in the „RUN‟ dialog box, which can be launched by pressing “Windows key+R”. On start-up, „Windows Registry‟ will show up the following five root entries. HKEY_CLASSES_ROOT HKEY_CURRENT_USER HKEY_LOCAL_MACHINE HKEY_USERS HKEY_CURRENT_CONFIG All the settings given above are not stored in a single file. They are spread across multiple files in logical groups called „hives‟. The combination of hives makes „Windows Registry‟. The values are stored here in binary format. That means only “1” and “0” is used here. “1” means “yes”, whereas the value “0” represents “no”. Let us look into the details of these settings. 1. HKEY_CLASSES_ROOT: It is abbreviated as HKCR. -

Fine-Grained and Accurate Source Code Differencing Jean-Rémy Falleri, Floréal Morandat, Xavier Blanc, Matias Martinez, Martin Monperrus
Fine-grained and Accurate Source Code Differencing Jean-Rémy Falleri, Floréal Morandat, Xavier Blanc, Matias Martinez, Martin Monperrus To cite this version: Jean-Rémy Falleri, Floréal Morandat, Xavier Blanc, Matias Martinez, Martin Monperrus. Fine- grained and Accurate Source Code Differencing. Proceedings of the International Conference on Automated Software Engineering, 2014, Västeras, Sweden. pp.313-324, 10.1145/2642937.2642982. hal-01054552 HAL Id: hal-01054552 https://hal.archives-ouvertes.fr/hal-01054552 Submitted on 12 Sep 2014 HAL is a multi-disciplinary open access L’archive ouverte pluridisciplinaire HAL, est archive for the deposit and dissemination of sci- destinée au dépôt et à la diffusion de documents entific research documents, whether they are pub- scientifiques de niveau recherche, publiés ou non, lished or not. The documents may come from émanant des établissements d’enseignement et de teaching and research institutions in France or recherche français ou étrangers, des laboratoires abroad, or from public or private research centers. publics ou privés. Fine-grained and Accurate Source Code Differencing Jean-Rémy Falleri Floréal Morandat Xavier Blanc Univ. Bordeaux, Univ. Bordeaux, Univ. Bordeaux, LaBRI, UMR 5800 LaBRI, UMR 5800 LaBRI, UMR 5800 F-33400, Talence, France F-33400, Talence, France F-33400, Talence, France [email protected] [email protected] [email protected] Matias Martinez Martin Monperrus INRIA and University of Lille, INRIA and University of Lille, France France [email protected] [email protected] ABSTRACT are computed between two versions of a same file. The goal At the heart of software evolution is a sequence of edit actions, of an edit script is to accurately reflect the actual change called an edit script, made to a source code file. -

Older Operating Systems
Older Operating Systems Class Notes # 18 Windows 9X Registry January 6, 2004 The windows 9x registry contains the operating system database. The data stored in the registry includes the following: system configuration, user settings, device manager information, application software settings, hardware settings, etc. The database has a hierarchical tree structure. See below: Figure 1: Registry editor Note that the right of the window are value name (e.g. ScreenSaveTime) and to the right of each value of each name is the value data assigned (e.g. 900). The registry is contained in two files which are hidden: System.dat and User.dat. The registry is organized in six major keys or branches of the registry tree and are described on table one: 1 Table one: Six major keys of the Windows 9x registry Key Description HKEY_CLASSES_ROOT Contains information about file associations and OLE data (This branch of the tree is a copy of HKEY_LOCAL_MACHINE\Software\Classes HKEY_USER Includes user preferences, including desktop configuration and network connections HKEY_CURRENT_USER If there is only one user of the system, this is a duplicate of HKEY_USERS, but for a multi-user system, this key contains information about the current user preferences. HKEY_LOCAL_MACHINE Contains information about hardware and installed software HKEY_CURRENT_CONFIG Contains the same information in HKEY_LOCAL_MACHINE\Config and has information about printers and display fonts HKEY_DYN_DATA Keeps information about Windows performance and Plug and Play information You can think of the six major keys in table one as root keys. Each root keys contains a number of subkeys as shown in figure one. A registry key can contain other keys. -
AN4421 – Using Codewarrior Diff Tool
Freescale Semiconductor Document Number: AN4421 Application Note Using the CodeWarrior Diff Tool 1. Introduction CodeWarrior for Microcontrollers v10.x leverages the features of the Eclipse framework and thereby provides Contents a sophisticated and visually clear, graphical "diff" tool 1. Introduction .............................................................. 1 for comparing differences between revisions of source 2. Comparing Files....................................................... 1 code files. This document explores the use of the diff 3. Comparing File Edits ............................................... 3 tool available in CodeWarrior. 4. Comparison within Version Control Systems ....... 4 5. Merge ........................................................................ 7 2. Comparing Files The simplest case to use the CodeWarrior diff tool is to compare any two files in a project. To compare files: 1. Select any two files in the CodeWarrior Project Explorer view. You can use Ctrl-click or Shift- click to select the files, 2. Right-click on one of the files and select Compare With > Each Other from the context menu. © Freescale Semiconductor, Inc., 2012. All rights reserved. Comparing Files Figure 1. Comparison of two files in a project Notice in the trivial example in Figure 1 above hello.c and hello.cpp are (faintly) selected. The differences include: • Code outline view which can also be used to limit the scope of what is displayed in the differences below it. • Compare viewer or the comparison window at the bottom that contains the two files side-by-side with the line-oriented differences highlighted by outline and the specific differences with a background highlight. The icons at the top right of the source comparison are tool buttons are helpful for managing a merge. For more information on managing merge refer to the topic Merge in the document. -

Unix Commands (09/04/2014)
Unix Commands (09/04/2014) • Access control – login <login_name> – exit – passwd <login_name> – yppassswd <loginname> – su – • Login as Super user – su <login> • Login as user <login> • Root Prompt – [root@localhost ~] # • User Prompt – [bms@raxama ~] $ On Line Documentation – man <command/topic> – info <command/topic> • Working with directories – mkdir –p <subdir> ... {-p create all directories in path if not present} mkdir –p /2015/Jan/21/14 will create /2015, Jan, 21 & 14 in case any of these is absent – cd <dir> – rm -r <subdir> ... Man Pages • 1 Executable programs or shell commands • 2 System calls (functions provided by the kernel) • 3 Library calls (functions within program libraries) • 4 Special files (usually found in /dev) • 5 File formats and conventions eg /etc/passwd • 6 Games • 7 Miscellaneous (including macro packages and conventions), e.g. man(7), groff(7) • 8 System administration commands (usually only for root) • 9 Kernel routines [Non standard] – man grep, {awk,sed,find,cut,sort} – man –k mysql, man –k dhcp – man crontab ,man 5 crontab – man printf, man 3 printf – man read, man 2 read – man info Runlevels used by Fedora/RHS Refer /etc/inittab • 0 - halt (Do NOT set initdefault to this) • 1 - Single user mode • 2 - Multiuser, – without NFS (The same as 3, if you do not have networking) • 3 - Full multi user mode w/o X • 4 - unused • 5 - X11 • 6 - reboot (Do NOT set init default to this) – init 6 {Reboot System} – init 0 {Halt the System} – reboot {Requires Super User} – <ctrl> <alt> <del> • in tty[2-7] mode – tty switching • <ctrl> <alt> <F1-7> • In Fedora 10 tty1 is X. -
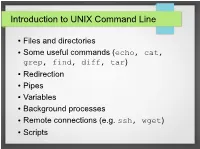
Introduction to UNIX Command Line
Introduction to UNIX Command Line ● Files and directories ● Some useful commands (echo, cat, grep, find, diff, tar) ● Redirection ● Pipes ● Variables ● Background processes ● Remote connections (e.g. ssh, wget) ● Scripts The Command Line ● What is it? ● An interface to UNIX ● You type commands, things happen ● Also referred to as a “shell” ● We'll use the bash shell – check you're using it by typing (you'll see what this means later): ● echo $SHELL ● If it doesn't say “bash”, then type bash to get into the bash shell Files and Directories / home var usr mcuser abenson drmentor science catvideos stuff data code report M51.fits simulate.c analyze.py report.tex Files and Directories ● Get a pre-made set of directories and files to work with ● We'll talk about what these commands do later ● The “$” is the command prompt (yours might differ). Type what's listed after hit, then press enter. $$ wgetwget http://bit.ly/1TXIZSJhttp://bit.ly/1TXIZSJ -O-O playground.tarplayground.tar $$ tartar xvfxvf playground.tarplayground.tar Files and directories $$ pwdpwd /home/abenson/home/abenson $$ cdcd playgroundplayground $$ pwdpwd /home/abenson/playground/home/abenson/playground $$ lsls animalsanimals documentsdocuments sciencescience $$ mkdirmkdir mystuffmystuff $$ lsls animalsanimals documentsdocuments mystuffmystuff sciencescience $$ cdcd animals/mammalsanimals/mammals $$ lsls badger.txtbadger.txt porcupine.txtporcupine.txt $$ lsls -l-l totaltotal 88 -rw-r--r--.-rw-r--r--. 11 abensonabenson abensonabenson 19441944 MayMay 3131 18:0318:03 badger.txtbadger.txt -rw-r--r--.-rw-r--r--. 11 abensonabenson abensonabenson 13471347 MayMay 3131 18:0518:05 porcupine.txtporcupine.txt Files and directories “Present Working Directory” $$ pwdpwd Shows the full path of your current /home/abenson/home/abenson location in the filesystem.