Understanding Integer Overflow in C/C++
Total Page:16
File Type:pdf, Size:1020Kb
Load more
Recommended publications
-
Bit Shifts Bit Operations, Logical Shifts, Arithmetic Shifts, Rotate Shifts
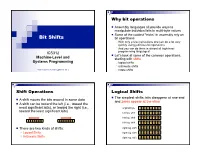
Why bit operations Assembly languages all provide ways to manipulate individual bits in multi-byte values Some of the coolest “tricks” in assembly rely on Bit Shifts bit operations With only a few instructions one can do a lot very quickly using judicious bit operations And you can do them in almost all high-level ICS312 programming languages! Let’s look at some of the common operations, Machine-Level and starting with shifts Systems Programming logical shifts arithmetic shifts Henri Casanova ([email protected]) rotate shifts Shift Operations Logical Shifts The simplest shifts: bits disappear at one end A shift moves the bits around in some data and zeros appear at the other A shift can be toward the left (i.e., toward the most significant bits), or toward the right (i.e., original byte 1 0 1 1 0 1 0 1 toward the least significant bits) left log. shift 0 1 1 0 1 0 1 0 left log. shift 1 1 0 1 0 1 0 0 left log. shift 1 0 1 0 1 0 0 0 There are two kinds of shifts: right log. shift 0 1 0 1 0 1 0 0 Logical Shifts right log. shift 0 0 1 0 1 0 1 0 Arithmetic Shifts right log. shift 0 0 0 1 0 1 0 1 Logical Shift Instructions Shifts and Numbers Two instructions: shl and shr The common use for shifts: quickly multiply and divide by powers of 2 One specifies by how many bits the data is shifted In decimal, for instance: multiplying 0013 by 10 amounts to doing one left shift to obtain 0130 Either by just passing a constant to the instruction multiplying by 100=102 amounts to doing two left shifts to obtain 1300 Or by using whatever -

Effects and Opportunities of Native Code Extensions For
Effects and Opportunities of Native Code Extensions for Computationally Demanding Web Applications DISSERTATION zur Erlangung des akademischen Grades Dr. Phil. im Fach Bibliotheks- und Informationswissenschaft eingereicht an der Philosophischen Fakultät I Humboldt-Universität zu Berlin von Dipl. Inform. Dennis Jarosch Präsident der Humboldt-Universität zu Berlin: Prof. Dr. Jan-Hendrik Olbertz Dekan der Philosophischen Fakultät I: Prof. Michael Seadle, Ph.D. Gutachter: 1. Prof. Dr. Robert Funk 2. Prof. Michael Seadle, Ph.D. eingereicht am: 28.10.2011 Tag der mündlichen Prüfung: 16.12.2011 Abstract The World Wide Web is amidst a transition from interactive websites to web applications. An increasing number of users perform their daily computing tasks entirely within the web browser — turning the Web into an important platform for application development. The Web as a platform, however, lacks the computational performance of native applications. This problem has motivated the inception of Microsoft Xax and Google Native Client (NaCl), two independent projects that fa- cilitate the development of native web applications. Native web applications allow the extension of conventional web applications with compiled native code, while maintaining operating system portability. This dissertation determines the bene- fits and drawbacks of native web applications. It also addresses the question how the performance of JavaScript web applications compares to that of native appli- cations and native web applications. Four application benchmarks are introduced that focus on different performance aspects: number crunching (serial and parallel), 3D graphics performance, and data processing. A performance analysis is under- taken in order to determine and compare the performance characteristics of native C applications, JavaScript web applications, and NaCl native web applications. -

Using the GNU Compiler Collection (GCC)
Using the GNU Compiler Collection (GCC) Using the GNU Compiler Collection by Richard M. Stallman and the GCC Developer Community Last updated 23 May 2004 for GCC 3.4.6 For GCC Version 3.4.6 Published by: GNU Press Website: www.gnupress.org a division of the General: [email protected] Free Software Foundation Orders: [email protected] 59 Temple Place Suite 330 Tel 617-542-5942 Boston, MA 02111-1307 USA Fax 617-542-2652 Last printed October 2003 for GCC 3.3.1. Printed copies are available for $45 each. Copyright c 1988, 1989, 1992, 1993, 1994, 1995, 1996, 1997, 1998, 1999, 2000, 2001, 2002, 2003, 2004 Free Software Foundation, Inc. Permission is granted to copy, distribute and/or modify this document under the terms of the GNU Free Documentation License, Version 1.2 or any later version published by the Free Software Foundation; with the Invariant Sections being \GNU General Public License" and \Funding Free Software", the Front-Cover texts being (a) (see below), and with the Back-Cover Texts being (b) (see below). A copy of the license is included in the section entitled \GNU Free Documentation License". (a) The FSF's Front-Cover Text is: A GNU Manual (b) The FSF's Back-Cover Text is: You have freedom to copy and modify this GNU Manual, like GNU software. Copies published by the Free Software Foundation raise funds for GNU development. i Short Contents Introduction ...................................... 1 1 Programming Languages Supported by GCC ............ 3 2 Language Standards Supported by GCC ............... 5 3 GCC Command Options ......................... -

Bash Shell Scripts
Bash Shell Scripts Writing Bash shell scripts Bash shell scripts are text files Text files most efficiently built with programming editors (emacs or vi) File must be executable and in search path chmod 700 my_script PATH environment variable may not include .! An example shell script: #!/bin/bash #My first script echo "Hello World!" Bash Shell Scripts Writing Bash shell scripts Compile a Verilog file with vlog #!/bin/bash if [ ! d work ] ; then echo work does not exist, making it vlib work fi if [ ! s adder.v ] ; then vlog adder.v fi work directory must exist before compilation Get scripts via wget, eg: wget http://web.engr.oregonstate.edu/~traylor/ece474/script --- Bash Shell Scripts Writing Bash shell scripts File attribute checking #!/bin/bash if [ ! s junk_dir ] ; then mkdir junk_dir fi Spaces around brackets are needed! File attribute checking d exists and is a directory e, a file exists f exists and is a regular file s file exists and is not empty --- Bash Shell Scripts Writing Bash shell scripts Compile Verilog then run a simultion #!/bin/bash if [ ! -d "work" ] ; then vlib work fi if [ -s "adder.v" ] ; then vlog adder.v #runs simulation with a do file and no GUI vsim adder -do do.do quiet c else echo verilog file missing fi --- Bash Shell Scripts Writing Bash shell scripts vsim command and arguments vsim entity_name do dofile.do quiet -c -quiet (do not report loading file messages) -c (console mode, no GUI) -do (run vsim from a TCL do file) +nowarnTFMPC (don’t warn about mismatched ports, scary) +nowarnTSCALE (don’t warn about timing mismatches) Try vsim help for command line arguements --- Bash Shell Scripts Writing Bash Shell Scripts (TCL Script) In another text file, we create a TCL script with commands for the simulator. -

Introduction to Linux by Lars Eklund Based on Work by Marcus Lundberg
Introduction to Linux By Lars Eklund Based on work by Marcus Lundberg ● What is Linux ● Logging in to UPPMAX ● Navigate the file system ● “Basic toolkit” What is Linux ● The Linux Operating system is a UNIX like UNIX compatible Operating system. ● Linux is a Kernel on which many different programs can run. The shell(bash, sh, ksh, csh, tcsh and many more) is one such program ● Linux has a multiuser platform at its base which means permissions and security comes easy. Many Flavours Connect to UPPMAX ● (Download XQuartz or other X11 server for Mac OS ) ● Linux and MacOS: – start Terminal – $ ssh -X [email protected] Connect to UPPMAX for windows users ● Download a X-server such as GWSL or X-ming or VcXsrv or an other of your choosing ● Install WSL and a Distribution such as ubuntu or a ssh program such as MobaXTerm ● Connect to $ ssh -X [email protected] Windows links ● https://sourceforge.net/projects/vcxsrv/ ● https://mobaxterm.mobatek.net/ ● https://opticos.github.io/gwsl/ ● https://sourceforge.net/projects/xming/ ● https://docs.microsoft.com/en-us/windows/wsl/install-wi n10 ● Don’t forget to update to wsl2 X11-forwarding graphics from the command line ● Graphics can be sent through the SSH connection you’re using to connect - Use ssh -Y or ssh -X ● MacOS users will need to install XQuartz. ● When starting a graphical program, a new window will open, but your terminal will be “locked”. - Run using & at the end to run it as a background proccess e.g. “gedit &” - Alternatively, use ctrl-z to put gedit to sleep and -

Understanding Integer Overflow in C/C++
Appeared in Proceedings of the 34th International Conference on Software Engineering (ICSE), Zurich, Switzerland, June 2012. Understanding Integer Overflow in C/C++ Will Dietz,∗ Peng Li,y John Regehr,y and Vikram Adve∗ ∗Department of Computer Science University of Illinois at Urbana-Champaign fwdietz2,[email protected] ySchool of Computing University of Utah fpeterlee,[email protected] Abstract—Integer overflow bugs in C and C++ programs Detecting integer overflows is relatively straightforward are difficult to track down and may lead to fatal errors or by using a modified compiler to insert runtime checks. exploitable vulnerabilities. Although a number of tools for However, reliable detection of overflow errors is surprisingly finding these bugs exist, the situation is complicated because not all overflows are bugs. Better tools need to be constructed— difficult because overflow behaviors are not always bugs. but a thorough understanding of the issues behind these errors The low-level nature of C and C++ means that bit- and does not yet exist. We developed IOC, a dynamic checking tool byte-level manipulation of objects is commonplace; the line for integer overflows, and used it to conduct the first detailed between mathematical and bit-level operations can often be empirical study of the prevalence and patterns of occurrence quite blurry. Wraparound behavior using unsigned integers of integer overflows in C and C++ code. Our results show that intentional uses of wraparound behaviors are more common is legal and well-defined, and there are code idioms that than is widely believed; for example, there are over 200 deliberately use it. -

Collecting Vulnerable Source Code from Open-Source Repositories for Dataset Generation
applied sciences Article Collecting Vulnerable Source Code from Open-Source Repositories for Dataset Generation Razvan Raducu * , Gonzalo Esteban , Francisco J. Rodríguez Lera and Camino Fernández Grupo de Robótica, Universidad de León. Avenida Jesuitas, s/n, 24007 León, Spain; [email protected] (G.E.); [email protected] (F.J.R.L.); [email protected] (C.F.) * Correspondence: [email protected] Received:29 December 2019; Accepted: 7 February 2020; Published: 13 February 2020 Abstract: Different Machine Learning techniques to detect software vulnerabilities have emerged in scientific and industrial scenarios. Different actors in these scenarios aim to develop algorithms for predicting security threats without requiring human intervention. However, these algorithms require data-driven engines based on the processing of huge amounts of data, known as datasets. This paper introduces the SonarCloud Vulnerable Code Prospector for C (SVCP4C). This tool aims to collect vulnerable source code from open source repositories linked to SonarCloud, an online tool that performs static analysis and tags the potentially vulnerable code. The tool provides a set of tagged files suitable for extracting features and creating training datasets for Machine Learning algorithms. This study presents a descriptive analysis of these files and overviews current status of C vulnerabilities, specifically buffer overflow, in the reviewed public repositories. Keywords: vulnerability; sonarcloud; bot; source code; repository; buffer overflow 1. Introduction In November 1988 the Internet suffered what is publicly known as “the first successful buffer overflow exploitation”. The exploit took advantage of the absence of buffer range-checking in one of the functions implemented in the fingerd daemon [1,2]. Even though it is considered to be the first exploited buffer overflow, different researchers had been working on buffer overflow for years. -

RICH: Automatically Protecting Against Integer-Based Vulnerabilities
RICH: Automatically Protecting Against Integer-Based Vulnerabilities David Brumley, Tzi-cker Chiueh, Robert Johnson [email protected], [email protected], [email protected] Huijia Lin, Dawn Song [email protected], [email protected] Abstract against integer-based attacks. Integer bugs appear because programmers do not antici- We present the design and implementation of RICH pate the semantics of C operations. The C99 standard [16] (Run-time Integer CHecking), a tool for efficiently detecting defines about a dozen rules governinghow integer types can integer-based attacks against C programs at run time. C be cast or promoted. The standard allows several common integer bugs, a popular avenue of attack and frequent pro- cases, such as many types of down-casting, to be compiler- gramming error [1–15], occur when a variable value goes implementation specific. In addition, the written rules are out of the range of the machine word used to materialize it, not accompanied by an unambiguous set of formal rules, e.g. when assigning a large 32-bit int to a 16-bit short. making it difficult for a programmer to verify that he un- We show that safe and unsafe integer operations in C can derstands C99 correctly. Integer bugs are not exclusive to be captured by well-known sub-typing theory. The RICH C. Similar languages such as C++, and even type-safe lan- compiler extension compiles C programs to object code that guages such as Java and OCaml, do not raise exceptions on monitors its own execution to detect integer-based attacks. -
Lock-In-Pop: Securing Privileged Operating System Kernels By
Lock-in-Pop: Securing Privileged Operating System Kernels by Keeping on the Beaten Path Yiwen Li, Brendan Dolan-Gavitt, Sam Weber, and Justin Cappos, New York University https://www.usenix.org/conference/atc17/technical-sessions/presentation/li-yiwen This paper is included in the Proceedings of the 2017 USENIX Annual Technical Conference (USENIX ATC ’17). July 12–14, 2017 • Santa Clara, CA, USA ISBN 978-1-931971-38-6 Open access to the Proceedings of the 2017 USENIX Annual Technical Conference is sponsored by USENIX. Lock-in-Pop: Securing Privileged Operating System Kernels by Keeping on the Beaten Path Yiwen Li Brendan Dolan-Gavitt Sam Weber Justin Cappos New York University Abstract code needed to run such a system increases the odds that Virtual machines (VMs) that try to isolate untrusted flaws will be present, and, in turn, that tens of millions code are widely used in practice. However, it is often of user machines could be at risk [25]. Furthermore, iso- possible to trigger zero-day flaws in the host Operating lation will not work if a malicious program can access System (OS) from inside of such virtualized systems. In even a small portion of the host OS’s kernel that contains this paper, we propose a new security metric showing a zero-day flaw [12]. Both of these drawbacks reveal the strong correlation between “popular paths” and kernel key underlying weakness in designing OSVM systems – vulnerabilities. We verify that the OS kernel paths ac- a lack of information as to which parts of the host kernel cessed by popular applications in everyday use contain can be safely exported to user programs. -

Open Benchmark Alignment
Benchmark Selection Guide, Vol. 1 Doing it Right Art Morgan Performance Engineer, Intel Corporation Spring 2015 Legal Disclaimers Software and workloads used in performance tests may have been optimized for performance only on Intel microprocessors. Performance tests, such as SYSmark* and MobileMark*, are measured using specific computer systems, components, software, operations and functions. Any change to any of those factors may cause the results to vary. You should consult other information and performance tests to assist you in fully evaluating your contemplated purchases, including the performance of that product when combined with other products. For more information go to http://www.intel.com/performance. Intel is a sponsor and member of the BenchmarkXPRT* Development Community, and was the major developer of the XPRT* family of benchmarks. Principled Technologies* is the publisher of the XPRT family of benchmarks. You should consult other information and performance tests to assist you in fully evaluating your contemplated purchases. © 2015 Intel Corporation. Intel, Intel Inside and other logos are trademarks or registered trademarks of Intel Corporation, or its subsidiaries in the United States and other countries. * Other names and brands may be claimed as the property of others. 2 About this Guide This guide uses benchmark comparison tables to help you select the right set of tools for Windows*, Android* and Chrome* platform evaluations. Benchmarks covered in this guide: . General Guidance on Platform Evaluations 3DMark* 1.2.0 ANDEBench* PRO AnTuTu* v5.6.1 . Benchmark Selection for Windows BaseMark* CL BatteryXPRT* 2014 CompuBench* CL 1.5 for OpenCL* . Benchmark Selection for Android CompuBench* RS 2.0 for RenderScript* CrXPRT* 2015 Geekbench* 3.3.1 . -

Nacldroid: Native Code Isolation for Android Applications
NaClDroid: Native Code Isolation for Android Applications Elias Athanasopoulos1, Vasileios P. Kemerlis2, Georgios Portokalidis3, and Angelos D. Keromytis4 1 Vrije Universiteit Amsterdam, The Netherlands [email protected] 2 Brown University, Providence, RI, USA [email protected] 3 Stevens Institute of Technology, Hoboken, NJ, USA [email protected] 4 Columbia University, New York, NY, USA [email protected] Abstract. Android apps frequently incorporate third-party libraries that contain native code; this not only facilitates rapid application develop- ment and distribution, but also provides new ways to generate revenue. As a matter of fact, one in two apps in Google Play are linked with a library providing ad network services. However, linking applications with third-party code can have severe security implications: malicious libraries written in native code can exfiltrate sensitive information from a running app, or completely modify the execution runtime, since all native code is mapped inside the same address space with the execution environment, namely the Dalvik/ART VM. We propose NaClDroid, a framework that addresses these problems, while still allowing apps to include third-party code. NaClDroid prevents malicious native-code libraries from hijacking Android applications using Software Fault Isolation. More specifically, we place all native code in a Native Client sandbox that prevents uncon- strained reads, or writes, inside the process address space. NaClDroid has little overhead; for native code running inside the NaCl sandbox the slowdown is less than 10% on average. Keywords: SFI, NaCl, Android 1 Introduction Android is undoubtedly the most rapidly growing platform for mobile devices, with estimates predicting one billion Android-based smartphones shipping in 2017 [12]. -
Conda-Build Documentation Release 3.21.5+15.G174ed200.Dirty
conda-build Documentation Release 3.21.5+15.g174ed200.dirty Anaconda, Inc. Sep 27, 2021 CONTENTS 1 Installing and updating conda-build3 2 Concepts 5 3 User guide 17 4 Resources 49 5 Release notes 115 Index 127 i ii conda-build Documentation, Release 3.21.5+15.g174ed200.dirty Conda-build contains commands and tools to use conda to build your own packages. It also provides helpful tools to constrain or pin versions in recipes. Building a conda package requires installing conda-build and creating a conda recipe. You then use the conda build command to build the conda package from the conda recipe. You can build conda packages from a variety of source code projects, most notably Python. For help packing a Python project, see the Setuptools documentation. OPTIONAL: If you are planning to upload your packages to Anaconda Cloud, you will need an Anaconda Cloud account and client. CONTENTS 1 conda-build Documentation, Release 3.21.5+15.g174ed200.dirty 2 CONTENTS CHAPTER ONE INSTALLING AND UPDATING CONDA-BUILD To enable building conda packages: • install conda • install conda-build • update conda and conda-build 1.1 Installing conda-build To install conda-build, in your terminal window or an Anaconda Prompt, run: conda install conda-build 1.2 Updating conda and conda-build Keep your versions of conda and conda-build up to date to take advantage of bug fixes and new features. To update conda and conda-build, in your terminal window or an Anaconda Prompt, run: conda update conda conda update conda-build For release notes, see the conda-build GitHub page.