Course Name : BCA / MCA
Total Page:16
File Type:pdf, Size:1020Kb
Load more
Recommended publications
-
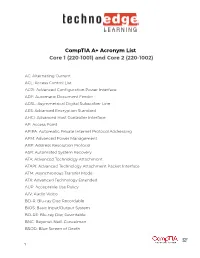
Comptia A+ Acronym List Core 1 (220-1001) and Core 2 (220-1002)
CompTIA A+ Acronym List Core 1 (220-1001) and Core 2 (220-1002) AC: Alternating Current ACL: Access Control List ACPI: Advanced Configuration Power Interface ADF: Automatic Document Feeder ADSL: Asymmetrical Digital Subscriber Line AES: Advanced Encryption Standard AHCI: Advanced Host Controller Interface AP: Access Point APIPA: Automatic Private Internet Protocol Addressing APM: Advanced Power Management ARP: Address Resolution Protocol ASR: Automated System Recovery ATA: Advanced Technology Attachment ATAPI: Advanced Technology Attachment Packet Interface ATM: Asynchronous Transfer Mode ATX: Advanced Technology Extended AUP: Acceptable Use Policy A/V: Audio Video BD-R: Blu-ray Disc Recordable BIOS: Basic Input/Output System BD-RE: Blu-ray Disc Rewritable BNC: Bayonet-Neill-Concelman BSOD: Blue Screen of Death 1 BYOD: Bring Your Own Device CAD: Computer-Aided Design CAPTCHA: Completely Automated Public Turing test to tell Computers and Humans Apart CD: Compact Disc CD-ROM: Compact Disc-Read-Only Memory CD-RW: Compact Disc-Rewritable CDFS: Compact Disc File System CERT: Computer Emergency Response Team CFS: Central File System, Common File System, or Command File System CGA: Computer Graphics and Applications CIDR: Classless Inter-Domain Routing CIFS: Common Internet File System CMOS: Complementary Metal-Oxide Semiconductor CNR: Communications and Networking Riser COMx: Communication port (x = port number) CPU: Central Processing Unit CRT: Cathode-Ray Tube DaaS: Data as a Service DAC: Discretionary Access Control DB-25: Serial Communications -

Planning for Internet Explorer and the IEAK
02_Inst.fm Page 15 Monday, October 16, 2000 9:40 AM TWO 2Chapter 2 Planning for Internet Explorer and the IEAK LChapter Syllabus In this chapter, we will look at material covered in the Planning section of Microsoft’s Implementing MCSE 2.1 Addressing Technical Needs, Rules, and Policies and Supporting Microsoft Internet Explorer 5 by using the Internet Explorer Administration Kit exam MCSE 2.2 Planning for Custom (70-080). After reading this chapter, you should be Installations and Settings able to: MCSE 2.3 Providing Multiple • Identify and evaluate the technical needs of business Language Support units, such as Internet Service Providers (ISPs), con- tent providers, and corporate administrators. MCSE 2.4 Providing Multiple Platform Support • Design solutions based on organizational rules and policies for ISPs, content providers, and corporate MCSE 2.5 Developing Security Strategies administrators. • Evaluate which components to include in a custom- MCSE 2.6 Configuring for Offline ized Internet Explorer installation package for a given Viewing deployment scenario. MCSE 2.7 Replacing Other Browsers • Develop appropriate security strategies for using Internet Explorer at various sites, including public MCSE 2.8 Developing CMAK kiosks, general business sites, single-task-based sites, Strategies and intranet-only sites. 15 02_Inst.fm Page 16 Monday, October 16, 2000 9:40 AM 16 Chapter 2 • Planning for Internet Explorer and the IEAK • Configure offline viewing for various types of users, including gen- eral business users, single-task users, and mobile users. • Develop strategies for replacing other Internet browsers, such as Netscape Navigator and previous versions of Internet Explorer. • Decide which custom settings to configure for Microsoft Outlook Express for a given scenario. -

Winter 2004 ISSN 1741-4229
IIRRMMAA INFORMATION RISK MANAGEMENT & AUDIT JOURNAL ◆ SPECIALIST ROUP OF THE ◆ JOURNAL A G BCS volume 14 number 5 winter 2004 ISSN 1741-4229 Programme for members’ meetings 2004 – 2005 Tuesday 7 September 2004 Computer Audit Basics 2: Auditing 16:00 for 16:30 Late afternoon the Infrastructure and Operations KPMG Thursday 7 October 2004 Regulatory issues affecting IT in the 10:00 to 16:00 Full day Financial Industry Old Sessions House Tuesday 16 November 2004 Networks Attacks – quantifying and 10:00 to 16:00 Full day dealing with future threats Chartered Accountants Hall Tuesday 18 January 2005 Database Security 16:00 for 16:30 Late afternoon KPMG Tuesday 15 March 2005 IT Governance 10:00 to 16:00 Full day BCS – The Davidson Building, 5 Southampton Street, London WC2 7HA Tuesday 17 May 2005 Computer Audit Basics 3: CAATS 16:00 for 16:30 Late afternoon Preceded by IRMA AGM KPMG AGM precedes the meeting Please note that these are provisional details and are subject to change. The late afternoon meetings are free of charge to members. For full day briefings a modest, very competitive charge is made to cover both lunch and a full printed delegate’s pack. For venue maps see back cover. Contents of the Journal Technical Briefings Front Cover Editorial John Mitchell 3 The Down Under Column Bob Ashton 4 Members’ Benefits 5 Creating and Using Issue Analysis Memos Greg Krehel 6 Computer Forensics Science – Part II Celeste Rush 11 Membership Application 25 Management Committee 27 Advertising in the Journal 28 IRMA Venues Map 28 GUIDELINES FOR POTENTIAL AUTHORS The Journal publishes various types of article. -

Disk Management (4 Min) When We Want to Install a Hard Drive in Our System We're Going to Need to Make That Hard Drive Either a Basic Disk Or a Dynamic Disk
Video – Disk Management (4 min) When we want to install a hard drive in our system we're going to need to make that hard drive either a basic disk or a dynamic disk. A basic disk, which is the default, contains primary and extended partitions as well as logical drives. A basic disk is limited to four partitions. The Windows operating system needs to be installed onto a basic disk. After it's installed the basic disk can then be converted to a dynamic disk. Primary partition. The primary partition contains the operating system. There can be up to four primary partitions per hard drive and a primary partition cannot be subdivided into smaller sections. A primary partition can also be marked as the active partition. The operating system uses the active partition to boot the computer. Only one primary partition per disk can be marked as active. In most cases, the C: drive is the active partition and contains the boot and system files. Meaning the MBR or Master Boot Record Partition Table. Newer systems that use EFI instead of BIOS are using the GPT or GUID partition table. If you're using the GPT instead of the MBR partition table you can have more than four primary partitions on a disk. An extended partition. There can only be one extended partition per hard drive. Once again, primary partitions, active partitions and extended partitions are all part of a basic disk. An extended partition cannot hold the operating system, but it can be subdivided into smaller sections called logical drives. -
An Introduction to Windows Operating System
EINAR KROGH AN INTRODUCTION TO WINDOWS OPERATING SYSTEM Download free eBooks at bookboon.com 2 An Introduction to Windows Operating System 2nd edition © 2017 Einar Krogh & bookboon.com ISBN 978-87-403-1935-4 Peer review by Høgskolelektor Lars Vidar Magnusson, Høgskolen i Østfold Download free eBooks at bookboon.com 3 AN INTRODUCTION TO WINDOWS OPERATING SYSTEM CONTENTS CONTENTS Introduction 9 1 About Windows history 10 1.1 MS-DOS 10 1.2 The first versions of Windows 11 1.3 Windows NT 12 1.4 Windows versions based on Windows NT 13 1.5 Windows Server 15 1.6 Control Questions 17 2 The tasks of an operating system 18 2.1 About the construction of computers 19 2.2 Central tasks for an operating system 20 2.3 Control Questions 22 �e Graduate Programme I joined MITAS because for Engineers and Geoscientists I wanted real responsibili� www.discovermitas.comMaersk.com/Mitas �e Graduate Programme I joined MITAS because for Engineers and Geoscientists I wanted real responsibili� Maersk.com/Mitas Month 16 I wwasas a construction Month 16 supervisorI wwasas in a construction the North Sea supervisor in advising and the North Sea Real work helpinghe foremen advising and IInternationalnternationaal opportunities ��reeree wworkoro placements solves Real work problems helpinghe foremen IInternationalnternationaal opportunities ��reeree wworkoro placements solves problems Download free eBooks at bookboon.com Click on the ad to read more 4 AN INTRODUCTION TO WINDOWS OPERATING SYSTEM CONTENTS 3 Some concepts and terms of the Windows operating system 23 3.1 -

Programming with Windows Forms
A P P E N D I X A ■ ■ ■ Programming with Windows Forms Since the release of the .NET platform (circa 2001), the base class libraries have included a particular API named Windows Forms, represented primarily by the System.Windows.Forms.dll assembly. The Windows Forms toolkit provides the types necessary to build desktop graphical user interfaces (GUIs), create custom controls, manage resources (e.g., string tables and icons), and perform other desktop- centric programming tasks. In addition, a separate API named GDI+ (represented by the System.Drawing.dll assembly) provides additional types that allow programmers to generate 2D graphics, interact with networked printers, and manipulate image data. The Windows Forms (and GDI+) APIs remain alive and well within the .NET 4.0 platform, and they will exist within the base class library for quite some time (arguably forever). However, Microsoft has shipped a brand new GUI toolkit called Windows Presentation Foundation (WPF) since the release of .NET 3.0. As you saw in Chapters 27-31, WPF provides a massive amount of horsepower that you can use to build bleeding-edge user interfaces, and it has become the preferred desktop API for today’s .NET graphical user interfaces. The point of this appendix, however, is to provide a tour of the traditional Windows Forms API. One reason it is helpful to understand the original programming model: you can find many existing Windows Forms applications out there that will need to be maintained for some time to come. Also, many desktop GUIs simply might not require the horsepower offered by WPF. -

GOTOHELL.DLL: Software Dependencies and The
GOTOHELL.DLL Software Dependencies and the Maintenance of Microsoft Windows Stephanie Dick Daniel Volmar Harvard University Presented at “The Maintainers: A Conference” Stephens Institute of Technology, Hoboken, NJ April 9, 2016 Abstract Software never stands alone, but exists always in relation to the other soft- ware that enables it, the hardware that runs it, and the communities who make, own, and maintain it. Here we consider a phenomenon called “DLL hell,” a case in which those relationships broke down, endemic the to Mi- crosoft Windows platform in the mid-to-late 1990s. Software applications often failed because they required specific dynamic-link libraries (DLLs), which other applications may have overwritten with their own preferred ver- sions. We will excavate “DLL hell” for insight into the experience of modern computing, which emerged from the complex ecosystem of manufacturers, developers, and users who collectively held the Windows platform together. Furthermore, we propose that in producing Windows, Microsoft had to balance a unique and formidable tension between customer expectations and investor demands. Every day, millions of people rely on software that assumes Windows will behave a certain way, even if that behavior happens to be outdated, inconvenient, or just plain broken, leaving Microsoft “on the hook” for the uses or abuses that others make of its platform. Bound so tightly to its legacy, Windows had to maintain the old in order to pro- mote the new, and DLL hell highlights just how difficult this could be. We proceed in two phases: first, exploring the history of software componenti- zation in order to explain its implementation on the Windows architecture; and second, defining the problem and surveying the official and informal means with which IT professionals managed their unruly Windows systems, with special attention paid to the contested distinction between a flaw on the designer’s part and a lack of discipline within the using community. -

Tahoe-LAFS Documentation Release 1.X
Tahoe-LAFS Documentation Release 1.x The Tahoe-LAFS Developers January 19, 2017 Contents 1 Welcome to Tahoe-LAFS! 3 1.1 What is Tahoe-LAFS?..........................................3 1.2 What is “provider-independent security”?................................3 1.3 Access Control..............................................4 1.4 Get Started................................................4 1.5 License..................................................4 2 Installing Tahoe-LAFS 5 2.1 First: In Case Of Trouble.........................................5 2.2 Pre-Packaged Versions..........................................5 2.3 Preliminaries...............................................5 2.4 Install the Latest Tahoe-LAFS Release.................................6 2.5 Running the tahoe executable.....................................8 2.6 Running the Self-Tests..........................................8 2.7 Common Problems............................................9 2.8 Using Tahoe-LAFS............................................9 3 How To Run Tahoe-LAFS 11 3.1 Introduction............................................... 11 3.2 Do Stuff With It............................................. 12 3.3 Socialize................................................. 13 3.4 Complain................................................. 13 4 Configuring a Tahoe-LAFS node 15 4.1 Node Types................................................ 16 4.2 Overall Node Configuration....................................... 16 4.3 Connection Management........................................ -

GIAC.GCFA.V2018-03-11.Q309
GIAC.GCFA.v2018-03-11.q309 Exam Code: GCFA Exam Name: GIAC Certified Forensics Analyst Certification Provider: GIAC Free Question Number: 309 Version: v2018-03-11 # of views: 403 # of Questions views: 24822 https://www.freecram.com/torrent/GIAC.GCFA.v2018-03-11.q309.html NEW QUESTION: 1 Which of the following statements is NOT true about the file slack spaces in Windows operating system? A. File slack is the space, which exists between the end of the file and the end of the last cluster. B. File slack may contain data from the memory of the system. C. It is possible to find user names, passwords, and other important information in slack. D. Large cluster size will decrease the volume of the file slack. Answer: D (LEAVE A REPLY) NEW QUESTION: 2 In which of the following files does the Linux operating system store passwords? A. Passwd B. SAM C. Shadow D. Password Answer: (SHOW ANSWER) NEW QUESTION: 3 Which of the following password cracking attacks is based on a pre-calculated hash table to retrieve plain text passwords? A. Rainbow attack B. Dictionary attack C. Hybrid attack D. Brute Force attack Answer: A (LEAVE A REPLY) NEW QUESTION: 4 You work as a Network Administrator for NetTech Inc. The company has a network that consists of 200 client computers and ten database servers. One morning, you find that an unauthorized user is accessing data on a database server on the network. Which of the following actions will you take to preserve the evidences? Each correct answer represents a complete solution. -

CHFI: Computer Hacking Forensic Investigator Course Content
CHFI: Computer Hacking Forensic Investigator Course ID #: 1275-200-ZZ-W Hours: 40 Course Content Course Description: CHFI v9 covers a detailed methodological approach to computer forensic and evidence analysis. It provides the necessary skillset for identification of intruder’s footprints and gathering necessary evidence for its prosecution. All major tools and theories used by cyber forensic industry are covered in the curriculum. The certification can fortify the applied knowledge level of law enforcement personnel, system administrators, security officers, defense and military personnel, legal professionals, bankers, computer and network security professionals, and anyone who is concerned about the integrity of the network and digital investigations CHFI provides training in the necessary skills to perform effective digital forensic investigation. It is a comprehensive course covering major forensic investigation scenarios that enables students to acquire necessary hands-on experience on various forensic investigation techniques and standard forensic tools necessary to successfully carryout computer forensic investigation leading to prosecution of perpetrators. CHFI presents a methodological approach to computer forensics including searching and seizing, chain-of-custody, acquisition, preservation, analysis and reporting of digital evidence. Target Student: Anyone interested in cyber forensics/investigations Attorneys, Legal Consultants, and Lawyers Law Enforcement Officers Police Officers Federal/Government Agents Defense and Military Detectives/Investigators Incident Response Team Members Information Security Managers Network Defenders IT Professionals, IT Directors/Managers System/Network Engineers Security Analyst/Architect/Auditors/Consultants www.tcworkshop.com Pages 1 of 17 800.639.3535 CHFI: Computer Hacking Forensic Investigator Course ID #: 1275-200-ZZ-W Hours: 40 Prerequisites: IT/Forensics Professionals with basic knowledge on IT/Cyber Security, Computer Forensics, and Incident response. -

MICROSOFT WINDOWS Early Versions Main Articles: Windows 1.0
MICROSOFT WINDOWS Early versions Main articles: Windows 1.0, Windows 2.0, and Windows 2.1x Windows 1.0, the first version, released in 1985 The history of Windows dates back to September 1981, when Chase Bishop, a computer scientist, designed the first model of an electronic device and project "Interface Manager" was started. It was announced in November 1983 (after the Apple Lisa, but before the Macintosh) under the name "Windows", but Windows 1.0 was not released until November 1985.[5] Windows 1.0 achieved little popularity and was to compete with Apple's own operating system. Windows 1.0 is not a complete operating system; rather, it extends MS-DOS. The shell of Windows 1.0 is a program known as the MS- DOS Executive. Components included Calculator, Calendar, Cardfile, Clipboard viewer, Clock, Control Panel, Notepad, Paint, Reversi, Terminal and Write. Windows 1.0 does not allow overlapping windows. Instead all windows are tiled. Only modal dialog boxes may appear over other windows. Windows 2.0 was released in December 1987 and was more popular than its predecessor. It features several improvements to the user interface and memory management.[citation needed] Windows 2.03 changed the OS from tiled windows to overlapping windows. The result of this change led to Apple Computer filing a suit against Microsoft alleging infringement on Apple's copyrights.[6][7] Windows 2.0 also introduced more sophisticated keyboard shortcuts and could make use of expanded memory. Windows 2.1 was released in two different versions: Windows/286 and Windows/386. Windows/386 uses the virtual 8086 mode of Intel 80386 to multitask several DOS programs and the paged memory model to emulate expanded memory using available extended memory. -

Vista General
SVRRETIRO.ELRETIROCC.LOCAL Remote Computer Audit :: 19/02/2015 10:04:10 Vista General Item Value Computer Name SVRRETIRO Domain Name ELRETIROCC Site Name Default-First-Site-Name Roles Workstation, Server, SQL Server, Primary Domain Controller Description Operating System Microsoft Windows 2008 R2 Server Standard (full installation) 64-bit Manufacturer HP Model ProLiant ML350 G6 Serial Number MXQ2170303 Asset Tag Number Of Processors 1 Processor Description Intel(R) Xeon(R) CPU E5645 @ 2.40GHz Total Memory 6144MB Total Hard Drive 2379GB Display 1600 x 900 pixels, 65536 colours BIOS Version HP - 2 User Account administrador System Uptime 14 Days, 19 Hours, 26 Minutes Local Time 2015-02-19 10:03:48 19/02/2015 10:05:41 1/110 SVRRETIRO.ELRETIROCC.LOCAL Top Software instalado Active Setup Name Version Installed .NET Framework 2,0,50727,0 .NET Framework 2,0,50727,1 .NET Framework 2,0,50727,1 .NET Framework 2,0,50727,1 .NET Framework 2,0,50727,1 .NET Framework 4,0,30319,0 .NET Framework 4,0,30319,0 19/02/2015 10:05:41 2/110 SVRRETIRO.ELRETIROCC.LOCAL Active Directory Service Interface 5,0,00,0 Yes Address Book 7 6,1,7601,17514 Yes Applying Enhanced Security Configuration 8,0,7100,0 Yes Applying Enhanced Security Configuration 8,0,7100,0 Yes Browsing Enhancements 11,0,9600,17501 Yes DirectDrawEx 4,71,1113,0 Yes Dynamic HTML Data Binding 11,0,9600,17501 Yes Google Chrome 24,0,0,0 Yes HTML Help 6,3,9600,17501 Yes Internet Explorer Core Fonts 11,0,9600,0 Yes Internet Explorer Help 11,0,9600,17501 Yes Internet Explorer Setup Tools 11,0,9600,17501