Norton Internet Security User Guide
Total Page:16
File Type:pdf, Size:1020Kb
Load more
Recommended publications
-
The Evolution of Ransomware
The evolution of ransomware SECURITY RESPONSE The evolution of ransomware Kevin Savage, Peter Coogan, Hon Lau Version 1.0 – August 6, 2015 Never before in the history of human kind have people across the world been subjected to extortion on a massive scale as they are today. CONTENTS OVERVIEW ..............................................................................3 Key information ......................................................................5 Types of ransomware .............................................................5 How ransomware has evolved ...............................................7 Targets for ransomware .......................................................13 Systems impacted by ransomware ......................................14 Ransomware: How it works ..................................................18 Ransom techniques ..............................................................27 How widespread is the problem of ransomware .................33 What does the future hold for ransomware? .......................37 Conclusion ............................................................................45 Appendix ..............................................................................47 Mitigation strategies ............................................................51 Symantec detections for common ransomware families 54 Resources .............................................................................56 OVERVIEW Never before in the history of human kind have people across the world been -
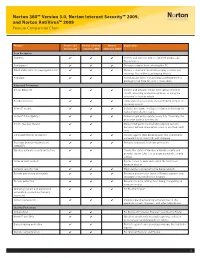
Norton 360™ Version 3.0, Norton Internet Security™ 2009, and Norton Antivirus™ 2009 Feature Comparison Chart
Norton 360™ Version 3.0, Norton Internet Security™ 2009, and Norton AntiVirus™ 2009 Feature Comparison Chart Feature Norton 360 Norton Internet Norton Explanation Version 3.0 Security 2009 AntiVirus 2009 Core Protection Antivirus ✔ ✔ ✔ Detects and removes viruses, Internet worms, and Trojan horses Antispyware ✔ ✔ ✔ Prevents spyware from infecting the PC Email and instant messaging protection ✔ ✔ ✔ Monitors email and instant messaging so users can exchange files without exchanging threats Antispam ✔ ✔ Automatically filters out annoying and fraudulent or phishing email from the user’s email inbox Advanced Protection Botnet detection ✔ ✔ ✔ Detects and prevents others from taking control of the PC, accessing private information, or using the computer to host an attack Rootkit detection ✔ ✔ ✔ Finds and removes threats that are hidden deep in the operating system Norton™ Insight ✔ ✔ ✔ Includes innovative, intelligence-driven technology for faster, fewer, shorter scans Norton™ Pulse Updates ✔ ✔ ✔ Delivers rapid pulse updates every 5 to 15 minutes for protection against new threats Smart, two-way firewall ✔ ✔ Makes intelligent incoming and outgoing security decisions without interrupting users to ask them each time Enhanced browser protection ✔ ✔ ✔ Secures against Web-based attacks that use browser vulnerabilities to infect PCs with malware Real-time behavioral protection ✔ ✔ ✔ Provides enhanced, real-time protection (SONAR™) Wireless network security protection ✔ ✔ Checks the status of wireless network security and provides expert advice on managing -
Norton™ Utilities Premium: User Manual
Norton™ Utilities Premium User Manual Norton Utilities Premium User Guide The software described in this book is furnished under a license agreement and may be used only in accordance with the terms of the agreement. Copyright © 2018 Symantec Corporation. All rights reserved. The product described in this document is distributed under licenses restricting its use, copying, distribution, and decompilation/reverse engineering. No part of this document may be reproduced in any form by any means without prior written authorization of Symantec Corporation and its licensors, if any. THE DOCUMENTATION IS PROVIDED "AS IS" AND ALL EXPRESS OR IMPLIED CONDITIONS, REPRESENTATIONS AND WARRANTIES, INCLUDING ANY IMPLIED WARRANTY OF MERCHANTABILITY, FITNESS FOR A PARTICULAR PURPOSE OR NON-INFRINGEMENT, ARE DISCLAIMED, EXCEPT TO THE EXTENT THAT SUCH DISCLAIMERS ARE HELD TO BE LEGALLY INVALID. SYMANTEC CORPORATION SHALL NOT BE LIABLE FOR INCIDENTAL OR CONSEQUENTIAL DAMAGES IN CONNECTION WITH THE FURNISHING, PERFORMANCE, OR USE OF THIS DOCUMENTATION. THE INFORMATION CONTAINED IN THIS DOCUMENTATION IS SUBJECT TO CHANGE WITHOUT NOTICE. The Licensed Software and Documentation are deemed to be commercial computer software as defined in FAR 12.212 and subject to restricted rights as defined in FAR Section 52.227-19 "Commercial Computer Software - Restricted Rights" and DFARS 227.7202, et seq. "Commercial Computer Software and Commercial Computer Software Documentation," as applicable, and any successor regulations, whether delivered by Symantec as on premises or hosted services. Any use, modification, reproduction release, performance, display or disclosure of the Licensed Software and Documentation by the U.S. Government shall be solely in accordance with the terms of this Agreement. -

Amit a Windows 7
DVD DVD Többé nem fog akadozni az internet 11 Friss 9 GB 2009 A LEGÚJABB DRIVEREK, HASZNOS PROGRAMOK, Megmutatjuk, hogyan kell beállítani a rejtélyes Qos-t – lépésről lépésre R 90 A HÓNAP JÁTÉKAI, EXKLUZÍV CSOMAgok… 9 tipp: tökéletes TFT-képminőség Nem kell drága pénzen új monitor! Profin beállítjuk a mostanit R 98 GO DIGITAL! 2009/11_ CHIPONLINE.HU Ennyire (nem) biztonságos a vírusirtója – felfedjük! A DVD-N: Tesztünkből kiderül, hogy miért csődöl be sok víruskereső éles helyzetben R 40 es VÍRUSVADÁSZ teLJ CSOMAG Amit a Windows 7 jobban tud… 46 Gyors sikerek! Több gépre... Csak a CHIP-en! R TELJES VERZIÓ TELJES VERZIÓ TELJES VERZIÓ Egyedi, vicces, ...Szinkroni- Sytem Backup: …és, amin még javítani kell. Az összes új funkció szórakoztató zálás, mentés, vadonatúj, családi album megosztás 2010-es verzió és rejtett képesség tesztje + a Win 7 mint második rendszer Szimatolók a PC-jén? Segítünk! A legjobb eszközök az adatlopás ellen: 100% anonim szörf és levelezés R 26 Zseniális új funkciók eszközeihez T ESZ pt 20 tipp, melyekkel lenyűgöző tulajdonságokat LA TOVÁBBI DVD-TARTALOM 58 P R csalogathat elő átlagos hardvereiből 84 Radeon HD5870 Radeon teszt >> HD5870 10 tény a CPU-król >> Új technológiák: OpenID >> Mozizzunk óriástévén >> Gyorsteszt: P55-ös alaplapok >> Rés a víruspajzson >> Ennyire jó a 7 Windows >> CHIP mini PC >> 20 dolog, amit nem tudott… >> Soha többé net akadozó 1995 Ft, előfizetéssel 1395 Ft R XXI. évfolyam, 11. szám, 2009. november P55-ÖSz ALA asztali PC-k 36 Kiadja a Motor-Presse Budapest Lapkiadó Kft. A forradalma R CD CD Többé nem fog akadozni az internet 11 melléklettel 2009 EXKLUZÍV CSOMAGOK, FRISS Megmutatjuk, hogyan kell beállítani a rejtélyes Qos-t – lépésről lépésre R 90 PROGRAMOK, VÍRUSVÉDELEM.. -

Check Point Threat Intelligence Bulletin
November 12-18, 2018 VS. CISCO IRON PORT YOUR CHECK POINT THREAT INTELLIGENCE REPORT TOP ATTACKS AND BREACHES Check Point researchers found that the Hades APT group, responsible for the infamous Olympic Destroyer attack during the 2018 Winter Olympic Games, has been carrying out a new wave of attacks in which more complex macros and a new dropper variant were distributed. Vision Direct, a European online supplier for contact lens, has been breached. Customer data has been compromised, including name, billing and email addresses, password, credit card number and CVV. A massive phishing campaign has been hitting banking users in Russia. The fraudulent emails pretend to originate from Central Bank of Russia, luring recipients to open the malicious attachment. tRat, a new modular malware, has been distributed by the TA505 APT group in a campaign using Word documents with malicious macros abusing the Norton Security brand, and by another campaign targeting commercial banking institutions. The infamous tech support scam has taken on a new form, leveraging the Facebook Sharer dialogue, a page typically used by website owners to invite users to share their content. A warning is urging users to call the regional Facebook support team, who will then connect to the victim’s computer remotely, install malware and/or try to sell them unnecessary products/services. City of York Council has reported the personal details of users of its mobile app, One Planet York, have been compromised. It is yet unclear if the details were gained by attacking end-users through the app, or by accessing York’s database. -

Hostscan 4.8.01064 Antimalware and Firewall Support Charts
HostScan 4.8.01064 Antimalware and Firewall Support Charts 10/1/19 © 2019 Cisco and/or its affiliates. All rights reserved. This document is Cisco public. Page 1 of 76 Contents HostScan Version 4.8.01064 Antimalware and Firewall Support Charts ............................................................................... 3 Antimalware and Firewall Attributes Supported by HostScan .................................................................................................. 3 OPSWAT Version Information ................................................................................................................................................. 5 Cisco AnyConnect HostScan Antimalware Compliance Module v4.3.890.0 for Windows .................................................. 5 Cisco AnyConnect HostScan Firewall Compliance Module v4.3.890.0 for Windows ........................................................ 44 Cisco AnyConnect HostScan Antimalware Compliance Module v4.3.824.0 for macos .................................................... 65 Cisco AnyConnect HostScan Firewall Compliance Module v4.3.824.0 for macOS ........................................................... 71 Cisco AnyConnect HostScan Antimalware Compliance Module v4.3.730.0 for Linux ...................................................... 73 Cisco AnyConnect HostScan Firewall Compliance Module v4.3.730.0 for Linux .............................................................. 76 ©201 9 Cisco and/or its affiliates. All rights reserved. This document is Cisco Public. -

Antivirus – Internet Security Software
AntiVirus – Internet Security Software Recommended AntiVirus Software to use with OfficeEMR™: Norton AntiVirus Symantec Endpoint Protection Business Class – Enterprise – AntiVirus Solution AntiVirus ONLY software products WITHOUT additional Firewalls What Happens with Internet Security Software Products and OfficeEMR™: Provide an additional Firewall and/or Shields Can prevent you from accessing secure Web Sites such as https://www.officemd.net Scan every Web Page that you go to when it loads Can make screens in OfficeEMR™ take a long time to load Can prevent our AutoConfigure from running Can prevent scanning documents into OfficeEMR™ from completing What You Can Do: Setup our Web Site www.officemd.net as an exception in its Firewall. --- or --- Turn off (Disable) the additional Firewall included and / or applicable Shields Contact Technical Support via the software company’s Web Site o many offer e-mail, phone, and/or chat for technical support o get help with and options available to be able to access secure (https://...) Web --- or --- Sites o get help with and options available for making www.officemd.net an exception o get help with and options available for turning off their Firewall and / or applicable Shields. --- or --- Uninstall and Install the AntiVirus ONLY version of that software product. --- or --- Uninstall and Install a different AntiVirus ONLY software product. Revised 05/2009 AntiVirus – Internet Security Software More Detailed Information: Internet Security Software Products provide an added Firewall and / or Shields to help block malicious content or Web Sites while surfing on the Web. Without changing settings, by default, Internet Security Software Products will scan every Web Page that you go to when it loads. -

Ques 1) How to Book a Domain ? Follow These Steps for Booking
Ques 1) How to Book a Domain ? Follow these steps for booking your Domain Name: Step 1 In the Domain search box on the home page enter the domain name you want, select an extension for your Domain name (e.g. .com, .net, org, .tv etc.) and start your search by clicking on the Search button. Step 2 The results page will next show you whether the Domain is available or not. If not available then you will have to resume your search again. If your Domain name is available, you may proceed to register by selecting the checkbox against the domain name you want and clicking on Continue. Step 3 Proceed to complete the Domain registration form. Note: INSTALINKS.NET does not need any pre-registration, and you will directly proceeded to a Domain registration form. Registration is absolutely free of cost. You only have to register once on the site. After completing and submitting the Domain registration form, you will get an order code and will receive an email from Instalinks containing your all information pertaining to the domain that you have booked. Your domain will be activated within 48 hrs of receiving your payment. Note: This email does NOT mean that your domain has been registered, it merely confirms your order. You have to send the Cheque/Draft for the amount pertaining to the domain you have booked to INSTALINKS for the registration of the domain. From the day you have applied for Domain booking, Instalinks will keep it for a maximum period of 21 days, during which you will receive reminders. -

A Glance Into the Eye Pyramid Technical Article V2
A glance into the Eye Pyramid RĂZVAN OLTEANU Security Reasercher We keep you safe and we keep it simple. 01 Introduction On January 11, 2017 Italian news agency AGI, published a court order regarding cyber-attacks against high ranking Italian government members and Italian institutions. The attacks were conducted by two Italian brothers to get financial information that would help them gain an advantage when trading on financial markets. Overview The campaign was carried out over several years starting in 2008 and continuing into 2010, 2011, 2012 and 2014. The mechanism the brothers used to distribute their malware was simple; targeted spear-phishing emails aimed at victims who had already been selected. The emails con- tained a malware attachment, which once opened harvested information from the victims’ computers. This information consisted of pictures, documents, archives, presenta- tions, email contacts, email bodies, usernames, passwords, keystrokes, web pages content and databases. Technical details The malware was written in VisualBasic.net and was obfuscated twice using common obfuscators: Dotfuscator and Skater .NET which can be easily reversed. The malware stored its sensitive data – license keys, URLs and paths – by encrypting with the Triple DES algorithm using the MD5 of a provided password as key and SHA256 of the pass- word as initialization vector. A glance into the Eye Pyramid 01 02 Figure 1 Security applications To remain unnoticed, it tried to disable any security application installed on the victim’s computer. Targeted -

FS-TST) Is a Software Package That Supports the Testing of Disk Imaging Tools
NISTIR 7103-B Forensic Software Testing Support Tools Test Summary Report Serban Gavrila VDG, Inc. Elizabeth Fong Information Technology Laboratory National Institute of Standards and Technology Gaithersburg, MD 20899 NIST National Institute of Standards and Technology Technology Administration U.S. Department of Commerce NISTIR 7103-B Forensic Software Testing Support Tools Test Summary Report Serban Gavrila VDG, Inc. Elizabeth Fong Information Technology Laboratory National Institute of Standards and Technology Gaithersburg, MD 20899 April 2004 U.S.DEPARTMENT OF COMMERCE Donald L. Evans, Secretary TECHNOLOGY ADMINISTRATION Phillip J. Bond, Under Secretary of Commerce for Technology NATIONAL INSTITUTE OF STANDARDS AND TECHNOLOGY Ardent L. Bement, Jr., Director Forensic Software Testing Support Tools Test Summary Report Serban Gavrila* Elizabeth Fong ** ABSTRACT The Computer Forensics Tool Testing (CFTT) project at the National Institute of Standards and Technology (NIST), an agency of the United States Department of Commerce, provides a measure of confidence in the software tools used in computer forensic investigations. CFTT focuses on a class of tools called disk-imaging tools that copy or “image” hard disk drives. Forensic Software Testing Support Tools (FS-TST) is a software package that supports the testing of disk imaging tools. FS-TST includes 15 tools that perform hard disk initialization, faulty disk simulation, hard disk comparisons, extraction of information from a hard disk, and copying of disks or disk partitions. This NIST Interagency/Internal Report consists of two parts. Part A, covers the planning, design and specification of testing the tools included in the FS-TST package. Part B, which is this document, covers the test summary report. -

Aluria Security Center Avira Antivir Personaledition Classic 7
Aluria Security Center Avira AntiVir PersonalEdition Classic 7 - 8 Avira AntiVir Personal Free Antivirus ArcaVir Antivir/Internet Security 09.03.3201.9 x64 Ashampoo FireWall Ashampoo FireWall PRO 1.14 ALWIL Software Avast 4.0 Grisoft AVG 7.x Grisoft AVG 6.x Grisoft AVG 8.x Grisoft AVG 8.x x64 Avira Premium Security Suite 2006 Avira WebProtector 2.02 Avira AntiVir Personal - Free Antivirus 8.02 Avira AntiVir PersonalEdition Premium 7.06 AntiVir Windows Workstation 7.06.00.507 Kaspersky AntiViral Toolkit Pro BitDefender Free Edition BitDefender Internet Security BullGuard BullGuard AntiVirus BullGuard AntiVirus x64 CA eTrust AntiVirus 7 CA eTrust AntiVirus 7.1.0192 eTrust AntiVirus 7.1.194 CA eTrust AntiVirus 7.1 CA eTrust Suite Personal 2008 CA Licensing 1.57.1 CA Personal Firewall 9.1.0.26 CA Personal Firewall 2008 CA eTrust InoculateIT 6.0 ClamWin Antivirus ClamWin Antivirus x64 Comodo AntiSpam 2.6 Comodo AntiSpam 2.6 x64 COMODO AntiVirus 1.1 Comodo BOClean 4.25 COMODO Firewall Pro 1.0 - 3.x Comodo Internet Security 3.8.64739.471 Comodo Internet Security 3.8.64739.471 x64 Comodo Safe Surf 1.0.0.7 Comodo Safe Surf 1.0.0.7 x64 DrVirus 3.0 DrWeb for Windows 4.30 DrWeb Antivirus for Windows 4.30 Dr.Web AntiVirus 5 Dr.Web AntiVirus 5.0.0 EarthLink Protection Center PeoplePC Internet Security 1.5 PeoplePC Internet Security Pack / EarthLink Protection Center ESET NOD32 file on-access scanner ESET Smart Security 3.0 eTrust EZ Firewall 6.1.7.0 eTrust Personal Firewall 5.5.114 CA eTrust PestPatrol Anti-Spyware Corporate Edition CA eTrust PestPatrol -

Norton Antivirus Product Manual
NortonTM AntiVirus Product Manual Care for our Environment; ‘It's the right thing to do.’ Symantec has removed the cover from this manual to reduce the Environmental Footprint of our products. This manual is made from recycled materials. Norton AntiVirus™ Product Manual The software described in this book is furnished under a license agreement and may be used only in accordance with the terms of the agreement. Documentation version 21.4 Copyright © 2014 Symantec Corporation. All rights reserved. Symantec, the Symantec Logo, LiveUpdate, Norton 360, and Norton are trademarks or registered trademarks of Symantec Corporation or its affiliates in the U.S. and other countries. Portions of this product Copyright 1996-2011 Glyph & Cog, LLC. Other names may be trademarks of their respective owners. The product described in this document is distributed under licenses restricting its use, copying, distribution, and decompilation/reverse engineering. No part of this document may be reproduced in any form by any means without prior written authorization of Symantec Corporation and its licensors, if any. THE DOCUMENTATION IS PROVIDED “AS IS” AND ALL EXPRESS OR IMPLIED CONDITIONS, REPRESENTATIONS AND WARRANTIES, INCLUDING ANY IMPLIED WARRANTY OF MERCHANTABILITY, FITNESS FOR A PARTICULAR PURPOSE OR NON-INFRINGEMENT, ARE DISCLAIMED, EXCEPT TO THE EXTENT THAT SUCH DISCLAIMERS ARE HELD TO BE LEGALLY INVALID. SYMANTEC CORPORATION SHALL NOT BE LIABLE FOR INCIDENTAL OR CONSEQUENTIAL DAMAGES IN CONNECTION WITH THE FURNISHING, PERFORMANCE, OR USE OF THIS DOCUMENTATION. THE INFORMATION CONTAINED IN THIS DOCUMENTATION IS SUBJECT TO CHANGE WITHOUT NOTICE. The Licensed Software and Documentation are deemed to be commercial computer software as defined in FAR 12.212 and subject to restricted rights as defined in FAR Section 52.227-19 "Commercial Computer Software - Restricted Rights" and DFARS 227.7202, et seq.