Security Cloud
Total Page:16
File Type:pdf, Size:1020Kb
Load more
Recommended publications
-

Manual Aberto De TIC E Libreoffice Capa: Miguel Vale 3ª Edição Editor: ISCTE – Instituto Universitário De Lisboa, Lisboa 2014 ISBN: 978-989-732-237-2 Suporte: E-Book
Manual de Tecnologias de Informação e Comunicação e LibreOffice [ 3ª edição ] Comunidade LibreOffice Portugal Direitos de autor Este trabalho foi licenciado com uma Licença Creative Commons - Atribuição 3.0 Não Adaptada ou superior em conjunto com GNU General Public License v3+ ou superior. Todas as restantes marcas registadas presentes neste manual pertencem às respectivas entidades. Ficha Técnica Título: Manual Aberto de TIC e LibreOffice Capa: Miguel Vale 3ª Edição Editor: ISCTE – Instituto Universitário de Lisboa, Lisboa 2014 ISBN: 978-989-732-237-2 Suporte: e-book Autor(es) Os autores de cada capítulo estão descritos em cada uma das respectivas fichas técnicas. Feedback Envie os seus comentários ou sugestões sobre este documento para: http://wiki.documentfoundation.org/PT/Main_Page http://wiki.documentfoundation.org/PT/Documentation Acordo Ortográfico Cada capítulo deste documento foi redigido no acordo ortográfico definido pelo(s) seu(s) autor(es) na respectiva ficha técnica. Este capítulo foi redigido ao abrigo do Acordo Ortográfico de 1990. A toda a Comunidade LibreOffice Portugal. A todos os movimentos de Software Livre e Creative Commons em Portugal. A todos os Professores, Formadores e alunos e formandos que fizerem uso deste manual. A todos aqueles que apoiaram e acreditaram neste projecto. Caixa Mágica, Novell Portugal, Associação Ensino Livre, Associação Nacional de Software Livre, Associação de Apoio Social da Portugal Telecom, Ângulo Sólido, OpenLab-ESEV Laboratório de Software Livre da Escola Superior de Educação de Viseu, Instituto Superior de Ciências Educativas, Portal Forma-te e em especial ao ISCTE – Instituto Universitário de Lisboa. Aos nossos pais e família que agora poderão usufruir de mais tempo connosco. -

DVD-Ofimática 2014-02
(continuación 2) CamStudio 2.7.316 - CamStudio Codec 1.5 - CDex 1.70 beta 4 - CDisplayEx 1.9.09 - cdrTools FrontEnd 1.5.1 - Classic Shell 3.6.8 - Clavier+ 10.6.7 - Clementine 1.2.1 - Cobian Backup 8.4.0.202 - Comical 0.8 - ComiX 0.2.1.24 - CoolReader 3.0.56.42 - CubicExplorer 0.95.1 - Daphne 1.55 - Data Crow 3.12.5 - DejaVu Fonts 2.34 - DVD-Ofimática Deluge 1.3.6 - DeSmuME 0.9.10 - Dia 0.97.2.2 - Diashapes 0.2.2 - digiKam 3.4.0 - Disk Imager 1.4 - DiskCryptor 1.0.802.118 - Ditto 3.18.46.0 - DjVuLibre 3.5.25.4 - DocFetcher 1.1.9 - DoISO 2.0.0.6 - DOSBox 0.74 - DosZip Commander 3.21 - Double Commander 0.5.8 2014-02 beta - DrawPile 0.8.0 - DrawPile 0.8.3 actualización - DVD Flick 1.3.0.7 - DVDStyler 2.6.1 - DVDx 4.1.1.0 - Eagle Mode 0.84.0 - EasyTAG 2.1 - Ekiga 4.0.1 2013.08.20 - Electric Sheep 2.7.b35 - eLibrary 2.5.13 - emesene 2.12.9 2012.09.13 - eMule 0.50.a - Eraser 6.0.10 - DVD-Ofimática es una recopilación de programas libres para Windows eSpeak 1.47.11 - Eudora OSE 1.0 - eViacam 1.7.0 - Evince 2.32.0.145 - Exodus 0.10.0.0 - dirigidos a la ofimática en general (ofimática, sonido, gráficos y vídeo, Explore2fs 1.08 beta9 - Ext2Fsd 0.51 - FBReader 0.12.10 - FileBot 3.8 - FileVerifier++ 0.6.3 - Internet y utilidades). -

Spybot - Search & Destroy Can Detect and Remove Spyware of Different Kinds from Your Computer
Description Spybot - Search & Destroy can detect and remove spyware of different kinds from your computer. Spyware is a relatively new kind of threat that common anti-virus applications do not cover yet. If you see new toolbars in your Internet Explorer that you didn't intentionally install, if your browser crashes, or if you browser start page has changed without your knowing, you most probably have spyware. But even if you don't see anything, you may be infected, because more and more spyware is emerging that is silently tracking your surfing behaviour to create a marketing profile of you that will be sold to advertisement companies. Spybot-S&D; is free, so there's no harm in trying to see if something snooped into your computer, too :) Spybot-S&D; can also clean usage tracks, an interesting function if you share your computer with other users and don't want them to see what you worked on. And for professional users, it allows to fix some registry inconsistencies and offers some extended reporting features. License Spybot-S&D; comes under the Dedication Public License. Requirements Microsoft Windows 95, 98, ME, NT, 2000 or XP (32 and 64 bit), 2003, Vista. Compatible with bootable PE disks (e.g. BartPE) and Wine. Minimum of 10 MB free hard disk space, more recommended for updates and backups. Usage We recommend that you continue by reading the tutorial next. © 2000-2008 Safer Networking Ltd. All rights reserved. I. Freeware First of all, the reasons why Spybot-S&D; is free: I.a. Dedication Spybot-S&D; is dedicated to the most wonderful girl on earth :) I.b. -

Mozillamessaging.Com Site Redesign Site Map — Version 3.0 — September 22, 2008
Mozillamessaging.com Site Redesign Site Map — Version 3.0 — September 22, 2008 While this document can be printed at 8.5” x 11” it may be hard to read and is intended to be printed at 11” x 17”. Mozillamessaging.com Site Redesign Version 3.0 Other Systems and Features 03 05 Mozilla Messaging Languages http://www.mozillamessaging.com/en-US/features.html http://www.mozillamessaging.com/en-US/all.html Thunderbird 02 Release Notes 04 Download Page 18 (Overview) http://www.mozillamessaging.com/ http://www.mozillamessaging.com/en-US/releasenotes/ http://www.mozillamessaging.com/en-US/download.html ?? URL TBD en-US/thunderbird Secure Email TBD http://www.mozillamessaging.com/en-US/email.html All Add-Ons https://addons.mozilla.org/en-US/thunderbird/ Supported Servers TBD http://www.mozillamessaging.com/en-US/servers Recommended https://addons.mozilla.org/en-US/thunderbird/recommended Add-Ons Popular https://addons.mozilla.org/en-US/ https://addons.mozilla.org/en-US/thunderbird/browse/type:1/cat:all?sort=popular thunderbird/ FAQ Themes http://www.mozilla.org/support/thunderbird/faq https://addons.mozilla.org/en-US/thunderbird/browse/type:2 Tips & Tricks Dictionaries http://www.mozilla.org/support/thunderbird/tips https://addons.mozilla.org/en-US/thunderbird/browse/type:3 Keyboard Shortcuts http://www.mozilla.org/support/thunderbird/keyboard Mouse Shortcuts Add-Ons Support 06 http://www.mozilla.org/support/thunderbird/mouse https://addons.mozilla.org/en-US/thunderbird/ (Overview) http://www.mozillamessaging.com/ Menu References Bugzilla en-US/support http://www.mozilla.org/support/thunderbird/menu https://bugzilla.mozilla.org/ Editing Config. -
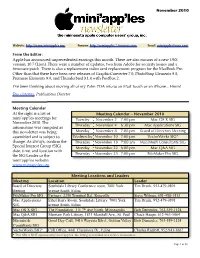
From the Editor: Apple Has Announced Unprecedented Earnings This Month
November 2010 Website: http://www.miniapples.org Forums: http://miniapples.7.forumer.com Email: [email protected] From the Editor: Apple has announced unprecedented earnings this month. There are also rumors of a new OSX version, 10.7 (Lion). There were a number of updates, two from Adobe for security issues and a firmware patch. There is also a replacement video card replacement program for the MacBook Pro. Other than that there have been new releases of GraphicConverter 7.0, PhotoShop Elements 9.0, Premiere Elements 9.0, and Thunderbird 3.1.4 with PostBox 2. I’ve been thinking about moving all of my Palm PDA info to an iPod Touch or an iPhone... Hmm! Tom Ostertag, Publications Director Meeting Calendar At the right is a list of Meeting Calendar – November 2010 mini’app’les meetings for Tuesday November 2 7:00 pm Mac OS X SIG November 2010. The Thursday November 4 6:30 pm Mac Applications SIG information was compiled as this newsletter was being Monday November 8 7:00 pm Board of Directors Meeting assembled and is subject to Wednesday November 10 7:00 pm VectorWorks SIG* change. As always, confirm the Thursday November 18 7:00 am Macintosh Consultants SIG Special Interest Group (SIG) Monday November 22 6:00 pm Mac Q&A SIG date, time, and location with Thursday November 25 7:00 pm FileMaker Pro SIG the SIG Leader or the mini’app’les website: www.miniapples.org. Meeting Locations and Leaders Meeting Location Leader Board of Directors Southdale Library Conference room, 7001 York Tim Drenk, 952-479-0891 Meeting Avenue South, Edina FileMaker Pro SIG Partners, 2250 Terminal Rd., Roseville Steve Wilmes, 651-458-1513 Mac Applications Ethel Barry Room, Southdale Library, 7001 York Tim Drenk, 952-479-0891 SIG Avenue South, Edina Mac OS X SIG The Foundation, 311 7th Ave North, Minneapolis Bob Demeules, 763-559-1124 Mac Q&A SIG Merriam Park Library, 1831 Marshall Ave., St. -

Firefox Hacks Is Ideal for Power Users Who Want to Maximize The
Firefox Hacks By Nigel McFarlane Publisher: O'Reilly Pub Date: March 2005 ISBN: 0-596-00928-3 Pages: 398 Table of • Contents • Index • Reviews Reader Firefox Hacks is ideal for power users who want to maximize the • Reviews effectiveness of Firefox, the next-generation web browser that is quickly • Errata gaining in popularity. This highly-focused book offers all the valuable tips • Academic and tools you need to enjoy a superior and safer browsing experience. Learn how to customize its deployment, appearance, features, and functionality. Firefox Hacks By Nigel McFarlane Publisher: O'Reilly Pub Date: March 2005 ISBN: 0-596-00928-3 Pages: 398 Table of • Contents • Index • Reviews Reader • Reviews • Errata • Academic Copyright Credits About the Author Contributors Acknowledgments Preface Why Firefox Hacks? How to Use This Book How This Book Is Organized Conventions Used in This Book Using Code Examples Safari® Enabled How to Contact Us Got a Hack? Chapter 1. Firefox Basics Section 1.1. Hacks 1-10 Section 1.2. Get Oriented Hack 1. Ten Ways to Display a Web Page Hack 2. Ten Ways to Navigate to a Web Page Hack 3. Find Stuff Hack 4. Identify and Use Toolbar Icons Hack 5. Use Keyboard Shortcuts Hack 6. Make Firefox Look Different Hack 7. Stop Once-Only Dialogs Safely Hack 8. Flush and Clear Absolutely Everything Hack 9. Make Firefox Go Fast Hack 10. Start Up from the Command Line Chapter 2. Security Section 2.1. Hacks 11-21 Hack 11. Drop Miscellaneous Security Blocks Hack 12. Raise Security to Protect Dummies Hack 13. Stop All Secret Network Activity Hack 14. -

DVD-Ofimática 2014-07
(continuación 2) Calizo 0.2.5 - CamStudio 2.7.316 - CamStudio Codec 1.5 - CDex 1.70 - CDisplayEx 1.9.09 - cdrTools FrontEnd 1.5.2 - Classic Shell 3.6.8 - Clavier+ 10.6.7 - Clementine 1.2.1 - Cobian Backup 8.4.0.202 - Comical 0.8 - ComiX 0.2.1.24 - CoolReader 3.0.56.42 - CubicExplorer 0.95.1 - Daphne 2.03 - Data Crow 3.12.5 - DejaVu Fonts 2.34 - DeltaCopy 1.4 - DVD-Ofimática Deluge 1.3.6 - DeSmuME 0.9.10 - Dia 0.97.2.2 - Diashapes 0.2.2 - digiKam 4.1.0 - Disk Imager 1.4 - DiskCryptor 1.1.836 - Ditto 3.19.24.0 - DjVuLibre 3.5.25.4 - DocFetcher 1.1.11 - DoISO 2.0.0.6 - DOSBox 0.74 - DosZip Commander 3.21 - Double Commander 0.5.10 beta - DrawPile 2014-07 0.9.1 - DVD Flick 1.3.0.7 - DVDStyler 2.7.2 - Eagle Mode 0.85.0 - EasyTAG 2.2.3 - Ekiga 4.0.1 2013.08.20 - Electric Sheep 2.7.b35 - eLibrary 2.5.13 - emesene 2.12.9 2012.09.13 - eMule 0.50.a - Eraser 6.0.10 - eSpeak 1.48.04 - Eudora OSE 1.0 - eViacam 1.7.2 - Exodus 0.10.0.0 - Explore2fs 1.08 beta9 - Ext2Fsd 0.52 - FBReader 0.12.10 - ffDiaporama 2.1 - FileBot 4.1 - FileVerifier++ 0.6.3 DVD-Ofimática es una recopilación de programas libres para Windows - FileZilla 3.8.1 - Firefox 30.0 - FLAC 1.2.1.b - FocusWriter 1.5.1 - Folder Size 2.6 - fre:ac 1.0.21.a dirigidos a la ofimática en general (ofimática, sonido, gráficos y vídeo, - Free Download Manager 3.9.4.1472 - Free Manga Downloader 0.8.2.325 - Free1x2 0.70.2 - Internet y utilidades). -

Download the Index
41_067232945x_index.qxd 10/5/07 1:09 PM Page 667 Index NUMBERS 3D video, 100-101 10BaseT Ethernet NIC (Network Interface Cards), 512 64-bit processors, 14 100BaseT Ethernet NIC (Network Interface Cards), 512 A A (Address) resource record, 555 AbiWord, 171-172 ac command, 414 ac patches, 498 access control, Apache web server file systems, 536 access times, disabling, 648 Accessibility module (GNOME), 116 ACPI (Advanced Configuration and Power Interface), 61-62 active content modules, dynamic website creation, 544 Add a New Local User screen, 44 add command (CVS), 583 address books, KAddressBook, 278 Administrator Mode button (KDE Control Center), 113 Adobe Reader, 133 AFPL Ghostscript, 123 41_067232945x_index.qxd 10/5/07 1:09 PM Page 668 668 aggregators aggregators, 309 antispam tools, 325 aKregator (Kontact), 336-337 KMail, 330-331 Blam!, 337 Procmail, 326, 329-330 Bloglines, 338 action line special characters, 328 Firefox web browser, 335 recipe flags, 326 Liferea, 337 special conditions, 327 Opera web browser, 335 antivirus tools, 331-332 RSSOwl, 338 AP (Access Points), wireless networks, 260, 514 aKregator webfeeder (Kontact), 278, 336-337 Apache web server, 529 album art, downloading to multimedia dynamic websites, creating players, 192 active content modules, 544 aliases, 79 CGI programming, 542-543 bash shell, 80 SSI, 543 CNAME (Canonical Name) resource file systems record, 555 access control, 536 local aliases, email server configuration, 325 authentication, 536-538 allow directive (Apache2/httpd.conf), 536 installing Almquist shells -
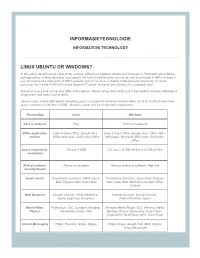
Informasietegnologie Linux Ubuntu Or Windows?
POST LIST INFORMASIETEGNOLOGIE INFORMATION TECHNOLOGY LINUX UBUNTU OR WINDOWS? In this article we will look at a few of the common differences between Ubuntu and windows 8. Firstly with any software package before making decisions most people will look at what it would cost me as user to purchase it. With windows 8 you are looking at a retail price of R800 upwards, but of course as a student of Stellenbosch University, it can be purchased for a mere R180-00 from the Student IT Centre. However with Ubuntu, it’s completely free! Now let’s have a look at how they differ at first glance, Ubuntu brings their Unity look to the platform whereas Windows 8 brings there new metro look to theirs. Ubuntu is also a fairly light weight operating system compared to Windows 8 which takes up 16 to 20 GB of hard drive space compared to Ubuntu’s 4.5GB. Below is a table of a list of relevant comparisons. Feature/App Linux Windows Cost to end-user Free R800 and upwards Office application Libre & Open Office, Google docs, Libre & Open Office, Google docs, Office 365 + choices Office Web Apps, Soft maker Office Web Apps, Microsoft Office suite, Soft maker Office Space required for OS size 4.5GB OS size is 16 GB (32-bit) or 20 GB (64-bit) installation Risk of software Almost non existent Various malicious software, High risk security threats Email clients Thunderbird, Evolution, KMail, Opera Thunderbird, Evolution, Opera Mail, Pegasus Mail, Pegasus Mail, Claws Mail Mail, Claws Mail, Windows Live Mail, Office Outlook Web Browsers Google Chrome, Firefox/Waterfox, -

Instalación Y Administración De Servicios De Correo Electrónico
Servicios de red e internet Instalación y administración de servicios de correo electrónico Raquel Castellanos Crespo Instalación y administración de servicios de correo electrónico Servicios de red e internet Raquel Castellanos Crespo INDICE Características del servicio de correo electrónico Elementos del servicio de correo electrónico -Agentes de correo electrónico. - Servidores de correo electrónico. Open relay y Smart host - Clientes de correo electrónico: entorno-DOS, gráficos y navegadores. - Direcciones, cuentas de correo y servidores DNS - Protocolos y servicios de descarga de correo: SMPT, ESMTP, POP, IMAP. Funcionamiento del servicio de correo electrónico Cuentas de correo, alias y buzones de correo Estructura de mensajes de correo electrónico - Cabecera, cuerpo, MIME Monitorización y registros del servicio de correo electrónico Servicio de correo electrónico vía web Correo seguro - Firma digital y cifrado de mensajes Veracidad del correo - Correo basura ("SPAM”) fraude, engaño, cadenas y virus informáticos 2 Servicios de red e internet | Instalación y administración de servicios de correo electrónico Servicios de red e internet Raquel Castellanos Crespo Características del servicio de correo electrónico Correo electrónico (correo-e, conocido también como e-mail ), es un servicio de red que permite a los usuarios enviar y recibir mensajes y archivos rápidamente (también denominados mensajes electrónicos o cartas electrónicas) mediante sistemas de comunicación electrónicos. Principalmente se usa este nombre para denominar al sistema que provee este servicio en Internet, mediante el protocolo SMTP, aunque por extensión también puede verse aplicado a sistemas análogos que usen otras tecnologías. Por medio de mensajes de correo electrónico se puede enviar, no solamente texto, sino todo tipo de documentos digitales. -

DVD-Ofimática 2014-03
(continuación 2) CamStudio 2.7.316 - CamStudio Codec 1.5 - CDex 1.70 beta 4 - CDisplayEx 1.9.09 - cdrTools FrontEnd 1.5.2 - Classic Shell 3.6.8 - Clavier+ 10.6.7 - Clementine 1.2.1 - Cobian Backup 8.4.0.202 - Comical 0.8 - ComiX 0.2.1.24 - CoolReader 3.0.56.42 - CubicExplorer 0.95.1 - Daphne 1.55 - Data Crow 3.12.5 - DejaVu Fonts 2.34 - DVD-Ofimática Deluge 1.3.6 - DeSmuME 0.9.10 - Dia 0.97.2.2 - Diashapes 0.2.2 - digiKam 3.4.0 - Disk Imager 1.4 - DiskCryptor 1.0.802.118 - Ditto 3.18.46.0 - DjVuLibre 3.5.25.4 - DocFetcher 1.1.10 - DoISO 2.0.0.6 - DOSBox 0.74 - DosZip Commander 3.21 - Double Commander 2014-03 0.5.8 beta - DrawPile 0.8.0 - DrawPile 0.8.5 actualización - DVD Flick 1.3.0.7 - DVDStyler 2.7 - DVDx 4.1.1.1 - Eagle Mode 0.84.0 - EasyTAG 2.1.10 - Ekiga 4.0.1 2013.08.20 - Electric Sheep 2.7.b35 - eLibrary 2.5.13 - emesene 2.12.9 2012.09.13 - eMule 0.50.a - Eraser 6.0.10 DVD-Ofimática es una recopilación de programas libres para Windows - eSpeak 1.48.02 - Eudora OSE 1.0 - eViacam 1.7.0 - Evince 2.32.0.145 - Exodus 0.10.0.0 - dirigidos a la ofimática en general (ofimática, sonido, gráficos y vídeo, Explore2fs 1.08 beta9 - Ext2Fsd 0.51 - FBReader 0.12.10 - FileBot 3.8 - FileVerifier++ 0.6.3 - Internet y utilidades). -

Using Free Software for Your Studies
Using Free Software for your studies. This document is for information, not specific recommendation (although everything here reflects the way I work myself). It is meant to help people who wish to use Free software for part or all of their work with their computer. For an explanation of Free (and the reason I am using a capital letter for the word, because it means a lot more than 'no cost'), see www.fsf.org 1) Operating system: You can use Free software on a proprietary operating system (eg Windows, MacOSX, iOS). If you want to go the whole hog, though, you can replace Windows or OSX with Linux, which is totally Free. There are many different versions ('distros') – Ubuntu is the most friendly to newcomers, being at least a simple to set up as Windows. NB – if you have a laptop, check first that the Linux you choose will work with it – Macbooks, in particular, can have issues with the wireless. Android is a version of Linux optimized for mobile devices, by the way. 2) Web Browser: Firefox is the obvious choice: works on Linux, OSX, Windows and more. Using scroogle instead of Google (www.scroogle.org.scraper.html) respects your privacy and does not track you or bombard you with adverts as Google does. 3) Word processor, spreadsheet, database, slideshow: LibreOffice: works on Linux, OSX, Windows and more. Can read and write Microsoft format files too, if you need to work with people who choose to use those MS Office. OpenOffice is very similar, but not quite 100% Free (though it is costless).