NIST SP 800-72, Guidelines on PDA Forensics
Total Page:16
File Type:pdf, Size:1020Kb
Load more
Recommended publications
-

AMERICAN P VERSIGHT
AMERICAN p VERSIGHT January11,2021 VIA ONLINE PORTAL DouglasHibbard Chief,InitialRequestStaff OfficeofInform ationPolicy DepartmentofJustice 441GStNW,6thFloor Washington,DC20530 ViaOnlinePortal Re: Expedited Freedom of Information Act Request DearFOIAOfficer: PursuanttotheFreedomof InformationAct(FOIA),5U.S.C.§552,andthe implem entingregulationsof youragency,Am ericanOversightmakesthefollowing requestforrecords. OnJanuary6,2021,PresidentTrumpinciteda mtoob attackCongresswhile mbers em werecertifyingtheelectionforPresident-electJoeBiden. 1 Theapparent insurrectionistsattackedtheCapitolBuilding,forcedtheirwaypastreportedly understaffedCapitolPolice,andultim atelydelayedtheCongressionalsessionbyforcing lawmakersandtheirstaffstoflee. 2 Fourpeoplediedduringthisassaultandafifth person,aCapitolPoliceofficer,diedthefollowingdayfrominjuriesincurredwhile engagingwithrioters. 3 Whilem ilitia mbers em roamedthehallsofCongress,Trum preportedlyfoughtagainst deployingtheD.C.NationalGuard, 4 andtheDefenseDepartm entreportedlyinitially 1 PressRelease,OfficeofSen.MittRom ney,Rom neyCondemInsurrectionatU.S. ns Capitol, Jan.6,2021, https://www.romney.senate.gov/rom ney-condem ns-insurrection- us-capitol. 2 RebeccaTan,etal., TrumpSupportersStormU.S.Capitol,WithOneWomanKilledand TearGasFired, Wash.Post(Jan.7,2021,12:30AM), https://www.washingtonpost.com/local/trum p-supporters-storm -capitol- dc/2021/01/06/58afc0b8-504b-11eb-83e3-322644d82356 story.html. 3 EricLevenson, WhatWeKnowAboutthe5DeathsinthePro-TrumpMobthatStormedthe Capitol, CNN(Jan.8,2021,5:29PM), -

Warrantless Workplace Searches of Government
WARRANTLESS WORKPLACE within which the principles outlined in SEARCHES OF GOVERNMENT O’Connor for “workplace” searches by EMPLOYEES government supervisors can be understood and applied. In sum, when a government supervisor is considering the search of a Bryan R. Lemons government employee’s workspace, a two- Branch Chief part analysis can be utilized to simplify the process. First, determine whether the There are a variety of reasons why employee has a reasonable expectation of a government supervisor might wish to privacy in the area to be searched. If a search a government employee’s reasonable expectation of privacy does workplace. For example, a supervisor exist, then consider how that expectation might wish to conduct a search to locate a can be defeated.2 Before turning to those needed file or document; the supervisor issues, however, it is necessary to first might wish to search an employee’s define exactly what is meant by the term workplace to discover whether the “workplace.” employee is misusing government property, such as a government-owned DEFINING THE “WORKPLACE” computer; or, a supervisor might seek to search an employee’s workplace because “Workplace,” as used in this he has information that the employee is article, “includes those areas and items committing a crime, such as using the that are related to work and are generally Internet to download child pornography. within the employer’s control.”3 This would include such areas as offices, desks, In situations where a public filing cabinets, and computers. However, employer -

Bus Driver Fatigue and Stress Issues Study
Bus Driver Fatigue and Stress Issues Study DTGH61-99-Z-00027 Final Report December 8, 1999 Prepared for Mr. Phil Hanley, HMCE-10 Federal Highway Administration Office of Motor Carriers 400 Seventh Street, SW, Room 4432A Washington, DC 20590 Prepared by Arrowhead Space & Telecommunications, Inc. 803 W. Broad Street, Suite 400 Falls Church, VA 22046 (703) 241-2801 voice (703) 241-2802 fax www.arrowheadsat.com Bus Driver Fatigue and Stress Issues Study Table of Contents I. Introduction 1 II. Approach 3 III. Literature Search 6 IV. Video Search 10 V. World Wide Web Search 11 VI. Industry Advisory Panel 32 VII. Federal and State Officials 35 VIII. Focus Group Sessions 36 IX. Identification of Issues from Focus Group Sessions and Phone Survey 39 X. Countermeasures 49 Appendix A: Focus Group and Phone Survey Participants Appendix B:Issues Identified at Focus Group Sessions Appendix C:Travel Industry Focus Group Report Appendix D:Safety Study Performed by Greyhound Lines, Inc. Bus Driver Fatigue and Stress Issues Study Final Report November 18, 1999 I INTRODUCTION Arrowhead Space and Telecommunications, Inc. conducted a research project to identify unique aspects of operations within the motorcoach industry which may produce bus driver fatigue and stress. Funding for and oversight of the study was provided by the Federal Highway Administration (FHWA), Office of Motor Carriers (OMC). The purpose of this study is to (1) identify from direct interaction with motorcoach owners, safety directors, operations managers, and drivers those fatigue-inducing stresses which they believe are unique to the motorcoach industry; (2) evaluate the relative influence of these stresses on bus driver fatigue; (3) provide relevant feedback to the FHWA/OMC for its use in future decisions which will affect the motorcoach industry; and (4) develop an outreach video to help motorcoach drivers understand the effects of fatigue, the stresses that induce it, and means to reduce it. -

9/11 Report”), July 2, 2004, Pp
Final FM.1pp 7/17/04 5:25 PM Page i THE 9/11 COMMISSION REPORT Final FM.1pp 7/17/04 5:25 PM Page v CONTENTS List of Illustrations and Tables ix Member List xi Staff List xiii–xiv Preface xv 1. “WE HAVE SOME PLANES” 1 1.1 Inside the Four Flights 1 1.2 Improvising a Homeland Defense 14 1.3 National Crisis Management 35 2. THE FOUNDATION OF THE NEW TERRORISM 47 2.1 A Declaration of War 47 2.2 Bin Ladin’s Appeal in the Islamic World 48 2.3 The Rise of Bin Ladin and al Qaeda (1988–1992) 55 2.4 Building an Organization, Declaring War on the United States (1992–1996) 59 2.5 Al Qaeda’s Renewal in Afghanistan (1996–1998) 63 3. COUNTERTERRORISM EVOLVES 71 3.1 From the Old Terrorism to the New: The First World Trade Center Bombing 71 3.2 Adaptation—and Nonadaptation— ...in the Law Enforcement Community 73 3.3 . and in the Federal Aviation Administration 82 3.4 . and in the Intelligence Community 86 v Final FM.1pp 7/17/04 5:25 PM Page vi 3.5 . and in the State Department and the Defense Department 93 3.6 . and in the White House 98 3.7 . and in the Congress 102 4. RESPONSES TO AL QAEDA’S INITIAL ASSAULTS 108 4.1 Before the Bombings in Kenya and Tanzania 108 4.2 Crisis:August 1998 115 4.3 Diplomacy 121 4.4 Covert Action 126 4.5 Searching for Fresh Options 134 5. -

Topic Higher Education
1 1 BEFORE THE NEW YORK STATE SENATE FINANCE AND ASSEMBLY WAYS AND MEANS COMMITTEES 2 ---------------------------------------------------- 3 JOINT LEGISLATIVE HEARING 4 In the Matter of the 2020-2021 EXECUTIVE BUDGET ON 5 HIGHER EDUCATION 6 ---------------------------------------------------- 7 Hearing Room B Legislative Office Building 8 Albany, New York 9 February 2, 2020 9:35 a.m. 10 11 PRESIDING: 12 Senator Liz Krueger Chair, Senate Finance Committee 13 Assemblywoman Helene Weinstein 14 Chair, Assembly Ways & Means Committee 15 PRESENT: 16 Senator James L. Seward Senate Finance Committee (RM) 17 Assemblyman Edward P. Ra 18 Assembly Ways & Means Committee (RM) 19 Assemblywoman Deborah J. Glick Chair, Assembly Higher Education Committee 20 Senator Toby Stavisky 21 Chair, Senate Higher Education Committee 22 Senator John C. Liu 23 Assemblywoman Barbara S. Lifton 24 Assemblywoman Karen McMahon 2 1 2020-2021 Executive Budget Higher Education 2 2-4-20 3 PRESENT: (Continued) 4 Assemblywoman Jo Anne Simon 5 Senator Kenneth P. LaValle 6 Assemblywoman Patricia Fahy 7 Assemblywoman Rebecca A. Seawright 8 Senator Anna Kaplan 9 Assemblyman Al Stirpe 10 Assemblywoman Alicia Hyndman 11 Senator Rachel May 12 Assemblyman Harvey Epstein 13 Assemblyman Doug Smith 14 Senator Andrew Gounardes 15 Assemblyman Charles D. Fall 16 Senator James Gaughran 17 Assemblywoman Rodneyse Bichotte 18 Assemblyman John T. McDonald III 19 Assemblywoman Marianne Buttenschon 20 Senator Brad Hoylman 21 Assemblyman Jake Ashby 22 Assemblywoman Judy Griffin 23 Assemblyman Victor M. Pichardo 24 Senator Robert Jackson 3 1 2020-2021 Executive Budget Higher Education 2 2-4-20 3 PRESENT: (Continued) 4 Assemblyman William Colton 5 6 7 LIST OF SPEAKERS 8 STATEMENT QUESTIONS 9 Kristina M. -

PDA Forensic Tools: an Overview and Analysis
NISTIR 7100 PDA Forensic Tools: An Overview and Analysis Rick Ayers Wayne Jansen NISTIR 7100 PDA Forensic Tools: An Overview and Analysis Rick Ayers Wayne Jansen C O M P U T E R S E C U R I T Y Computer Security Division Information Technology Laboratory National Institute of Standards and Technology Gaithersburg, MD 20988-8930 August 2004 U.S. Department of Commerce Donald L. Evans, Secretary Technology Administration Phillip J. Bond, Under Secretary of Commerce for Technology National Institute of Standards and Technology Arden L. Bement, Jr., Director ii Reports on Computer Systems Technology The Information Technology Laboratory (ITL) at the National Institute of Standards and Technology (NIST) promotes the U.S. economy and public welfare by providing technical leadership for the Nation’s measurement and standards infrastructure. ITL develops tests, test methods, reference data, proof of concept implementations, and technical analysis to advance the development and productive use of information technology. ITL’s responsibilities include the development of technical, physical, administrative, and management standards and guidelines for the cost-effective security and privacy of sensitive unclassified information in Federal computer systems. This Interagency Report discusses ITL’s research, guidance, and outreach efforts in computer security, and its collaborative activities with industry, government, and academic organizations. National Institute of Standards and Technology Interagency Report 67 pages (2004) Certain commercial entities, equipment, or materials may be identified in this document in order to describe an experimental procedure or concept adequately. Such identification is not intended to imply recommendation or endorsement by the National Institute of Standards and Techn ology, nor is it intended to imply that the entities, materials, or equipment are necessa rily the best available for the purpose. -

The Search for the "Manchurian Candidate" the Cia and Mind Control
THE SEARCH FOR THE "MANCHURIAN CANDIDATE" THE CIA AND MIND CONTROL John Marks Allen Lane Allen Lane Penguin Books Ltd 17 Grosvenor Gardens London SW1 OBD First published in the U.S.A. by Times Books, a division of Quadrangle/The New York Times Book Co., Inc., and simultaneously in Canada by Fitzhenry & Whiteside Ltd, 1979 First published in Great Britain by Allen Lane 1979 Copyright <£> John Marks, 1979 All rights reserved. No part of this publication may be reproduced, stored in a retrieval system, or transmitted in any form or by any means, electronic, mechanical, photocopying, recording or otherwise, without the prior permission of the copyright owner ISBN 07139 12790 jj Printed in Great Britain by f Thomson Litho Ltd, East Kilbride, Scotland J For Barbara and Daniel AUTHOR'S NOTE This book has grown out of the 16,000 pages of documents that the CIA released to me under the Freedom of Information Act. Without these documents, the best investigative reporting in the world could not have produced a book, and the secrets of CIA mind-control work would have remained buried forever, as the men who knew them had always intended. From the documentary base, I was able to expand my knowledge through interviews and readings in the behavioral sciences. Neverthe- less, the final result is not the whole story of the CIA's attack on the mind. Only a few insiders could have written that, and they choose to remain silent. I have done the best I can to make the book as accurate as possible, but I have been hampered by the refusal of most of the principal characters to be interviewed and by the CIA's destruction in 1973 of many of the key docu- ments. -

Ela Best Standards
Table of Contents Table of Contents .......................................................................................................................................... 1 Introduction ................................................................................................................................................... 5 Standards Map ............................................................................................................................................ 10 Progression of Foundations Benchmarks .................................................................................................... 11 Spiraled Standards in a Vertical Progression .............................................................................................. 13 Kindergarten ........................................................................................................................................... 26 Foundational Skills ............................................................................................................................. 26 Reading ............................................................................................................................................... 27 Communication ................................................................................................................................... 29 Vocabulary .......................................................................................................................................... 32 Sample texts by -

Yale College Council Student Jobs Handbook
Yale College Council Student Jobs Handbook University Services Team May 2017 STUDENT JOBS HANDBOOK 2 TABLE OF CONTENTS Introduction…………………………………………………………….………….………3 Before the Job Search...….…………………………….………………………………….4 Yale Policies………………………………………….….……….……….4 Important Considerations…………………………………………………5 The Search Process…………….…...…………………………….………………….….7 Finding a Job………………………………………………………….….7 Resumes…………………….……………...……………………...…...….9 Cover Letters…………………………………………………...…...…...12 Interviews…………………….………………………………….………13 Succeeding in Your Employment……………….…………………………………...……15 Payslips…………………….……………...……………………………...15 Direct Deposit…………………….……………...…………………...…...15 Federal I-9 Form………………………………………………………….15 Tax Returns………………………………………………………...……...15 Special Considerations for International Students……………………...…16 Balancing Employment and Academics…………………………………...17 Building a Relationship with Your Employer………………………….…...17 Maintaining a Job and Getting Promoted……………………….……….18 Asking for a Raise………………………………………………………...18 Off-Campus Employment……………………………………………...….19 Conclusion……………………………………………………………...….19 Acknowledgements.…….……………………………………………………………….20 Appendix A…………...…….…………………………………………………….….…22 STUDENT JOBS HANDBOOK 3 INTRODUCTION Welcome to your comprehensive guide for student jobs at Yale! Thanks to support from the Yale College Dean’s Office, the Yale College Council has compiled this document to encompass almost all aspects of the on-campus job search. Many of us have been through the struggle of finding an on-campus job, and we -

The Second Twenty Years, 1971-1991
Northwestern Michigan College The Second IVvenfy Years 1971 -1991 Al Shumsky Assisted by Carole Marlatt NORTHWESTERN MICHIGAN COLLEGE The Second Twenty Years 1971-1991 A1 Shumsky Assisted by Carole Marlatt February 1994 ACKNOWLEDGMENTS Thanks are due many people who helped with this project. First to the two people without whom it could not have been done: Tim Quinn and Carole Marlatt. Tim initiated the project and supported it with released time, and with no directions whatsoever beyond "Have a good time!" Carole not only prepared the manuscript, assembled the rosters in the appendix, chose the pictures, and both provided her own and edited my memories; she also is the one who recorded the Board minutes for these twenty years and then indexed them and preserved the hard copy so it was available to this amateur historian. (She, in fact, is the one to go to if you want to know what really went on during these years.) Thanks are also due these many others who graciously provided information or corroborated memories: Bob Buttleman, Doug Campbell, Becky Chartier, Jan Gasnik, Kathleen Guy, Chet Janik, Bill King, George Kuhn, Keith MacPhee, Nancy McArthur, Shelley Merrill, Dick Minor, Shirley Okerstrom, Barbara Raehl, Joe Rogers, PatSalathiel, Bill Shaw, Don Shikoski, Chuck Shreve, Robbie Teahen, Bob Warner, and Steve Westphal. Recognition is also due the hundreds of people—Board members, faculty and staff—whose names do not appear in this account, but who in fact constituted the College. Without them, there would be no history to write. I apologize to all whose contributions have not been specifically mentioned. -

The AU and the Search for Peace and Reconciliation in Burundi and Comoros
Th e AU and the search for Peace and Reconciliation in Burundi and Comoros The Centre for Humanitarian Dialogue (HD Centre) is an independent mediation organisation dedicated to helping improve the global response to armed confl ict. It attempts to achieve this by mediating between warring parties and providing support to the broader mediation community. The HD Centre is driven by humanitarian values and its ultimate goal to reduce the consequences of violent confl ict, improve security, and contribute to the peaceful resolution of confl ict. It maintains a neutral stance towards the warring parties that it mediates between and, in order to maintain its impartiality it is funded by a variety of governments, private foundations and philanthropists. © Centre for Humanitarian Dialogue, 2011 Reproduction of all or part of this publication may be authorised only with written consent and acknowledgement of the source. Front cover photography: © African Union, 78th PSC Meeting on Comoros, 9 June 2007 | © Lt. TMN Turyamumanya / Afrian Union, TFG Soldiers in Somalia queue for their fi rst organised payment exercise supervised by AMISOM troops in Mogadishu | © African Union, Water provision to neighbouring villagers in Mogadishu Th e AU and the search for Peace and Reconciliation in Burundi and Comoros Table of contents Part I Foreword 02 Acknowledgements 04 — Burundi case study Introduction 05 Part I: Burundi case study 09 Part II Executive summary 09 1.1 Context 10 case study — Comoros 1.2 OAU/AU intervention in the Burundi crisis 12 Part II: Comoros -
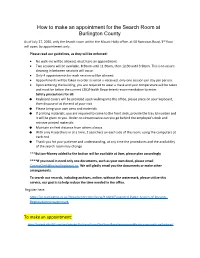
How to Make an Appointment for the Search Room at the County Clerk
How to make an appointment for the Search Room at Burlington County As of July 27, 2020, only the Search room within the Mount Holly office, at 50 Rancocas Road, 3rd floor will open, by appointment only. Please read our guidelines, as they will be enforced: No walk-ins will be allowed, must have an appointment. Two sessions will be available, 8:30am until 11:30am, then 12:30 until 3:30pm. This is to assure cleaning in between sessions will occur. Only 4 appointments for each session will be allowed. Appointments will be taken in order as email is received, only one session per day per person. Upon entering the building, you are required to wear a mask and your temperature will be taken and must be below the current CDC/Health Department recommendation to enter. Safety precautions for all: Keyboard covers will be provided upon walking into the office, please place on your keyboard, then dispose of at the end of your visit Please bring your own pens and materials If printing materials, you are required to come to the front desk, provide the tray Id number and it will be given to you. Under no circumstance can you go behind the employee’s desk and retrieve printed materials Maintain six feet distance from others always With only 4 searchers in at a time, 2 searchers on each side of the room, using the computers at each end Thank you for your patience and understanding, at any time the procedures and the availability of the search room may change ***Button-Money added to the button will be available at 9am, please plan accordingly ****If you need in need only one documents, such as your own deed, please email [email protected] We will gladly email you the documents or make other arrangements.