Openssl Cookbook.Pdf
Total Page:16
File Type:pdf, Size:1020Kb
Load more
Recommended publications
-
SSL/TLS Implementation CIO-IT Security-14-69
DocuSign Envelope ID: BE043513-5C38-4412-A2D5-93679CF7A69A IT Security Procedural Guide: SSL/TLS Implementation CIO-IT Security-14-69 Revision 6 April 6, 2021 Office of the Chief Information Security Officer DocuSign Envelope ID: BE043513-5C38-4412-A2D5-93679CF7A69A CIO-IT Security-14-69, Revision 6 SSL/TLS Implementation VERSION HISTORY/CHANGE RECORD Person Page Change Posting Change Reason for Change Number of Number Change Change Initial Version – December 24, 2014 N/A ISE New guide created Revision 1 – March 15, 2016 1 Salamon Administrative updates to Clarify relationship between this 2-4 align/reference to the current guide and CIO-IT Security-09-43 version of the GSA IT Security Policy and to CIO-IT Security-09-43, IT Security Procedural Guide: Key Management 2 Berlas / Updated recommendation for Clarification of requirements 7 Salamon obtaining and using certificates 3 Salamon Integrated with OMB M-15-13 and New OMB Policy 9 related TLS implementation guidance 4 Berlas / Updates to clarify TLS protocol Clarification of guidance 11-12 Salamon recommendations 5 Berlas / Updated based on stakeholder Stakeholder review / input Throughout Salamon review / input 6 Klemens/ Formatting, editing, review revisions Update to current format and Throughout Cozart- style Ramos Revision 2 – October 11, 2016 1 Berlas / Allow use of TLS 1.0 for certain Clarification of guidance Throughout Salamon server through June 2018 Revision 3 – April 30, 2018 1 Berlas / Remove RSA ciphers from approved ROBOT vulnerability affected 4-6 Salamon cipher stack -

Technical Report RHUL–ISG–2019–1 27 March 2019
20 years of Bleichenbacher attacks Gage Boyle Technical Report RHUL–ISG–2019–1 27 March 2019 Information Security Group Royal Holloway University of London Egham, Surrey, TW20 0EX United Kingdom Student Number: 100866673 Gage, Boyle 20 Years of Bleichenbacher Attacks Supervisor: Kenny Paterson Submitted as part of the requirements for the award of the MSc in Information Security at Royal Holloway, University of London. I declare that this assignment is all my own work and that I have acknowledged all quotations from published or unpublished work of other people. I also declare that I have read the statements on plagiarism in Section 1 of the Regulations Governing Examination and Assessment Offences, and in accordance with these regulations I submit this project report as my own work. Signature: Date: Acknowledgements I would first like to thank my project supervisor, Kenny Paterson. This project would not have been possible without his continuous encouragement to push the boundaries of my knowledge, and I am grateful for the commitment and expertise that he has provided throughout. Secondly, I would like to thank Nimrod Aviram for his invaluable advice, particularly with respect to algorithm implementation and understanding the finer details of this project. Further thanks should go to Raja Naeem Akram, Oliver Kunz and David Morrison for taking the time to teach me Python and how to run my source code on an Ubuntu server. I am grateful for the time that David Stranack, Thomas Bingham and James Boyle have spent proof reading this project, and for the continuous support from my part- ner, Lisa Moxham. -
TLS Deep Dive
12/9/17 TLS Deep Dive Website Security & More Joe Pranevich December 5, 2017 Today’s Session – Overview of TLS – Connection Establishment – Testing Tools – Recent Security Issues 1 12/9/17 What is SSL/TLS? – Core internet protocols (IP, TCP, HTTP) were designed without default security – SSL was invented in 1995 by Netscape to support encryption of web traffic for ecommerce and other uses. – SSL/TLS sits above TCP. It can be used to encrypt many protocols, but mostly used for HTTP. – Over two decades, SSL has been improved (with vulnerabilities discovered in older versions). The name was changed to TLS in 1999. SSL & TLS Timeline Protocol Released Notes SSLv2 1995 Vulnerable, depreciated in 2011 SSLv3 1996 Vulnerable, depreciated in 2015 TLS 1.0 1999 At risk, no longer permitted by PCI TLS 1.1 2006 TLS 1.2 2008 TLS 1.3 TBD Internet Draft 2 12/9/17 But Wait, There’s More! – TLS supports dozens of different encryption methods, compression methods, hashing functions, and other details. – Clients and servers select from a menu of these options to negotiate the best security (more on that later) – Most of these options have their own security histories, some have been deprecated, etc. Key Concepts – Shared Key Cryptography (Symmertric) – Public/Private Key Cryptography (Asymmetric) – Hashing 3 12/9/17 Connection Establishment – TLS Handshake – Cipher negotiation – Certificate Validation – Device Compatibility TLS Handshake – Part One – Client sends a “hello” message saying that they want TLS. – It includes TLS version, ciphers it supports, and other details – Server sends a “hello” message back. – It selects the most secure matching TLS version and ciphers – Connection will fail if client and server cannot agree on protocols and ciphers 4 12/9/17 Client Devices Have Different Capabilities As Do Servers & Load Balancers 5 12/9/17 We Care About The Intersection Backwards Compatibility Warning! – Web browsers and operating systems get updated frequently; you can usually rely on web users having a recent TLS stack when they connect to you. -
Configuring SSL for Services and Servers
Barracuda Web Application Firewall Configuring SSL for Services and Servers https://campus.barracuda.com/doc/4259877/ Configuring SSL for SSL Enabled Services You can configure SSL encryption for data transmitted between the client and the service. In the BASIC > Services page, click Edit next to a listed service and configure the following fields: Status – Set to On to enable SSL on your service. Status defaults to On for a newly created SSL enabled service. Certificate – Select a certificate presented to the browser when accessing the service. Note that only RSA certificates are listed here. If you have not created the certificate, select Generate Certificate from the drop-down list to generate a self-signed certificate. For more information on how to create self- signed certificates, see Creating a Client Certificate. If you want to upload a self-signed certificate, select Upload Certificate from the drop- down list. Provide the details about the certificate in the Upload Certificate dialog box. For information on how to upload a certificate, see Adding an SSL Certificate. Select ECDSA Certificate – Select an ECDSA certificate presented to the browser when accessing the service. SSL/TLS Quick Settings - Select an option to automatically configure the SSL/TLS protocols and ciphers. Use Configured Values - This option allows you to use the previously saved values. If the values are not saved, the Factory Preset option can be used. Factory Preset - This option allows you to enable TLS 1.1, TLS 1.2 and TLS 1.3 protocols without configuring override ciphers. Mozilla Intermediate Compatibility (Default, Recommended) - This configuration is a recommended configuration when you want to enable TLS 1.2 and TLS 1.3 and configure override ciphers for the same. -

TLS Attacks & DNS Security
IAIK TLS Attacks & DNS Security Information Security 2019 Johannes Feichtner [email protected] IAIK Outline TCP / IP Model ● Browser Issues Application SSLStrip Transport MITM Attack revisited Network Link layer ● PKI Attacks (Ethernet, WLAN, LTE…) Weaknesses HTTP TLS / SSL FLAME FTP DNS Telnet SSH ● Implementation Attacks ... ● Protocol Attacks ● DNS Security IAIK Review: TLS Services All applications running TLS are provided with three essential services Authentication HTTPS FTPS Verify identity of client and server SMTPS ... Data Integrity Detect message tampering and forgery, TLS e.g. malicious Man-in-the-middle TCP IP Encryption Ensure privacy of exchanged communication Note: Technically, not all services are required to be used Can raise risk for security issues! IAIK Review: TLS Handshake RFC 5246 = Establish parameters for cryptographically secure data channel Full handshake Client Server scenario! Optional: ClientHello 1 Only with ServerHello Client TLS! Certificate 2 ServerKeyExchange Certificate CertificateRequest ClientKeyExchange ServerHelloDone CertificateVerify 3 ChangeCipherSpec Finished ChangeCipherSpec 4 Finished Application Data Application Data IAIK Review: Certificates Source: http://goo.gl/4qYsPz ● Certificate Authority (CA) = Third party, trusted by both the subject (owner) of the certificate and the party (site) relying upon the certificate ● Browsers ship with set of > 130 trust stores (root CAs) IAIK Browser Issues Overview Focus: Relationship between TLS and HTTP Problem? ● Attacker wants to access encrypted data ● Browsers also have to deal with legacy websites Enforcing max. security level would „break“ connectivity to many sites Attack Vectors ● SSLStrip ● MITM Attack …and somehow related: Cookie Stealing due to absent „Secure“ flag… IAIK Review: ARP Poisoning How? Attacker a) Join WLAN, ● Sniff data start ARP Poisoning ● Manipulate data b) Create own AP ● Attack HTTPS connections E.g. -

Hosting Multiple Certs on One IP
Hosting multiple SSL Certicates on a single IP S Solving the IPv4 shortage dilemma FULL COMPATIBILITY When it comes to SSL security, hosting companies are increasingly facing In public environments, using SNI alone would mean cutting access to a issues related to IP addresses scarcity. Today every digital certificate used large number of potential site visitors as around 15% of systems (as of to provide an SSL connection on a webserver needs a dedicated IP January 2013) are incompatible with SNI. address, making it difficult for hosting companies to respond to increas- ing demand for security. The true solution GlobalSign has developed a solution to address hosting companies’ operational limitations and to let them run multiple certificates on a By coupling the Server Name Indication technology with SSL Certificates single IP address, at no detriment to browser and operating system and a CloudSSL Certificate from GlobalSign, multiple certificates can compatibility. now be hosted on a single IP without losing potential visitors that might lack SNI support. Host Headers GlobalSign SSL Certificates can be installed on several name-based virtual hosts as per any SNI-based https website. Each website has its To address the current concern of shortage of IPv4 addresses, most own certificate, allowing for even the highest levels of security (such as websites have been configured as name-based virtual hosts for years. Extended Validation Certificates). When several websites share the same IP number, the server will select the website to display based on the name provided in the Host Header. GlobalSign will then provide a free fall-back CloudSSL certificate for legacy configurations, enabling the 15% of visitors that do not have SNI Unfortunately this doesn’t allow for SSL security as the SSL handshake compatibility to access the secure websites on that IP address. -
Perception Financial Services Cyber Threat Briefing Report
PERCEPTION FINANCIAL SERVICES CYBER THREAT BRIEFING REPORT Q1 2019 1 Notable Cyber Activity within Financial Services Contents January 2019 October 2018 A security researcher discovered that The State Bank of India Between the 4th and 14th October 2018 HSBC reported a number Table of Contents . 1 (SBI), India’s largest bank, had failed to secure a server which of US online bank accounts were accessed by unauthorized users, Welcome . 1 was part of their text-messaging platform. The researcher was with potential access to personal information about the account able to read all messages sent and received by the bank’s ‘SBI holder. HSBC told the BBC this affected fewer than 1% of its 1 Notable Cyber Activity within Financial Services . 2 quick’ enquiry service which contained information on balances, American clients and has not released further information on 2 Threat Actor Profile: The Carbanak Organized Crime Gang . 4 phone numbers and recent transactions. This information could how the unauthorized access occurred. have been used to profile high net worth individuals, or aid social 3 Benefits and challenges of deploying TLS 1.3 . 5 engineering attacks which are one of the most common types of It is likely that this was an example of a credential-stuffing attack, 4 Ethereum Classic (ETC) 51% Attack . 9 financial fraud in India.1 where attackers attempt to authenticate with vast quantities 5 Authoritative DNS Security . 10 of username and password combinations obtained from other December 2018 compromised sites, hoping to find users who have re-used their Kaspersky published a detailed examination of intrusions into credentials elsewhere. -

It-Säkerhet - Examensarbete
IT-SÄKERHET - EXAMENSARBETE Största IT-säkerhetshoten mot svenska företag och organisationer idag, samt kontemporära metoder och verktyg för bekämpning av dessa IT-säkerhetshot. DEN 29 MARS 2016 BENJAMIN LUNDSTRÖM Examensarbete i Nät- & kommunikationsteknik, Umeå universitet. Löpnummer EL1609. BENJAMIN LUNDSTRÖM 16-03-29 IT-SÄKERHET - EXAMENSARBETE Sammanfattning Olika former av IT-relaterade hot har förekommit sedan internets födelse. Inledningsvis var de harmlösa humoristiska program som över tiden utvecklades till kriminella verktyg med ekonomiska syften. Elakartad programkod benämns under samlingsnamnet Malware. En angripare besitter idag ett stort antal metoder för otillåten tillgång till system, neka legitima användare tillgång till system eller på ett stort antal sätt bedriva kriminell verksamhet av ekonomisk karaktär. Skydds- och bekämpningsmetoderna innefattar brandväggar, olika analys-, detektions- och preventionssystem (IDS/IPS) och kryptering. Men för att komma tillrätta med IT-hoten fullt ut krävs också säkerhetsutbildning och incidenthantering som sker via incidentplanering, rapporter, dokumentation, backup och informationsklassning. Kontemporära IT-säkerhetshot av betydande art belyses i rapporten. Stuxnet (2009), som angrep Irans kärnvapenforskning. Flamer (2011), ett cybervapen vars syfte är spårlös informationsinhämtning. BlackEnergy (2015) och angreppet mot elförsörjningen i Ukraina. DDoS- attacken mot Svenska medier behandlas liksom Petya (2016) som är nya generationens Ransomeware. Det är vitalt för företag och organisationer att skydda sin viktigaste tillgång, informationen. Både mot cyberkriminella element i rent finansiellt syfte men i tilltagande grad också mot olika cybervapen och möjligtvis också mot cyberterrorism. Abstract A number of IT-related threats have emerged since the birth of internet. In the beginning they were harmless but over time they developed into fearsome criminal tools for economic purposes. -

The Trip to TLS Land Using the WSA Tobias Mayer, Consulting Systems Engineer BRKSEC-3006 Me…
The Trip to TLS Land using the WSA Tobias Mayer, Consulting Systems Engineer BRKSEC-3006 Me… CCIE Security #14390, CISSP & Motorboat driving license… Working in Content Security & IPv6 Security tmayer{at}cisco.com Writing stuff at “blogs.cisco.com” Agenda • Introduction • Understanding TLS • Configuring Decryption on the WSA • Troubleshooting TLS • Thoughts about the Future • Conclusion For Your Reference • There are (many...) slides in your print-outs that will not be presented. • They are there “For your Reference” For Your Reference Microsoft and Google pushing encryption • Microsoft pushing TLS with PFS • Google, FB, Twitter encrypting all traffic • HTTPS usage influencing page ranking on google • Deprecate SHA1, only SHA2+ • Browser Vendors aggressively pushing https • Problems with older TLS versions leading to upgrade of servers to newer protocols and ciphers • Poodle, Freak, Beast, …. Google Search Engine • Google ranking influenced by using HTTPS • http://blog.searchmetrics.com/us/2015 /03/03/https-vs-http-website-ssl-tls- encryption-ranking-seo-secure- connection/ Understanding TLS TLS Versions • SSLv3, 1996 • TLS 1.0, 1999, RFC2246 • TLS 1.1, 2006, RFC4346 • Improved security • TLS 1.2, 2008, RFC5246 • Removed IDEA and DES ciphers • Stronger hashes • Supports authenticated encryption ciphers (AES-GCM) • TLS 1.3, currently Internet Draft Attacks… • POODLE • SSLv3 Problems with Padding, turn of SSLv3 • BEAST • Know issues in CBC mode, use TLS 1.1/1.2 with non-CBC mode ciphers (GCM) • CRIME/BREACH • Compression Data Leak, disable -
How Organisations Can Properly Configure SSL Services to Ensure the Integrity and Confidentiality of Data in Transit”
An NCC Group Publication “SS-Hell: the Devil is in the details” Or “How organisations can properly configure SSL services to ensure the integrity and confidentiality of data in transit” Prepared by: Will Alexander Jerome Smith © Copyright 2014 NCC Group Contents 1 Introduction .................................................................................................................................................... 3 2 Protocols ........................................................................................................................................................ 3 3 Cipher Suites ................................................................................................................................................. 4 4 Certificates ..................................................................................................................................................... 5 4.1 Self-Signed or Untrusted Certificates ................................................................................................... 5 4.2 Mismatched Hostnames ....................................................................................................................... 6 4.3 Wildcard Certificates ............................................................................................................................. 6 4.4 Extended Validation Certificates .......................................................................................................... 7 4.5 Certificate Validity Period .................................................................................................................... -
Ethical Hacking : Methodology and Techniques
Ethical Hacking : Methodology and techniques TEI Heraklion [email protected] November 2017 Prerequisites You should have some knowledge of : 1. Basic network protocols : IP, ICMP, UDP, TCP 2. Network devices : routers, switches, access-points, firewalls, IDS/IPS 3. Basic network security : WiFi security (WPA2), SSL 4. Unsecured protocols VS secured protocols : FTP-SFTP-SCP / HTTP-HTTPS / Telnet- SSH 5. System administration : Basic Linux administration, Windows Active Directory Domains 6. Basic virtualization techniques using Vmware Workstation or Virtualbox Interesting skills if you plan a career in Computer Security : – Programming skills, System administration (Windows, Linux, Vmware, …), Database administration, Networking skills Disclaimer : The methodology, techniques and tools that you will learn must not be used in a production environment… Use these tools only in a protected lab environment 2/34 Hacking phases : RSGMC 1. Reconnaissance 2. Scanning 3. Gain access 4. Maintain access 5. Clear tracks 3/34 1. Reconnaissance Aim : gather info about target Target may be organization, system, employee What kind of info : Employee : linkedin, facebook, … Organization : location, ... Network infrastructure : Network integrator ? Architecture ? IP addresses ? Procedures ? Policies Types of reconnaissance : ACTIVE (= direct contact : social engineering, physical access) PASSIVE (no direct contact, internet queries) Sources of information Internet websites, google hacking, whois database, DNS footprinting, social media job sites -
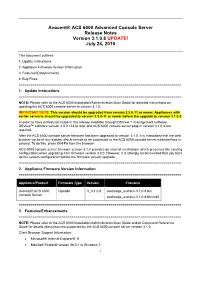
Avocent® ACS 6000 Advanced Console Server Release Notes Version 3.1.0.8 UPDATE! July 24, 2015
Avocent® ACS 6000 Advanced Console Server Release Notes Version 3.1.0.8 UPDATE! July 24, 2015 This document outlines: 1. Update Instructions 2. Appliance Firmware Version Information 3. Features/Enhancements 4. Bug Fixes =================================================================================== 1. Update Instructions =================================================================================== NOTE: Please refer to the ACS 6000 Installation/Administration/User Guide for detailed instructions on updating the ACS 6000 console server to version 3.1.0. IMPORTANT NOTE: This version should be upgraded from version 2.5.0-11 or newer. Appliances with earlier versions should be upgraded to version 2.5.0-11 or newer before the upgrade to version 3.1.0.8. In order to have all features listed in this release available through DSView™ management software, DSView™ software version 4.5.0.123 or later and ACS 6000 console server plug-in version 3.1.0.4 are required. After the ACS 6000 console server firmware has been upgraded to version 3.1.0, it is mandatory that the web browser cache of any system which intends to be connected to the ACS 6000 console server web interface is cleared. To do this, press Ctrl-F5 from the browser. ACS 6000 console server firmware version 3.1.0 provides an internal mechanism which preserves the existing configuration when upgrading from firmware version 3.0.0. However, it is strongly recommended that you back up the system configuration before the firmware version upgrade. =================================================================================== 2. Appliance Firmware Version Information =================================================================================== Appliance/Product Firmware Type Version Filename Avocent® ACS 6000 Opcode V_3.1.0.8 avoImage_avctacs-3.1.0-8.bin Console Server avoImage_avctacs-3.1.0-8.bin.md5 =================================================================================== 3.