Validation Report
Total Page:16
File Type:pdf, Size:1020Kb
Load more
Recommended publications
-

Microsoft'sevolving App Strategy
CAN MICROSOFT MAP THE FUTURE OF IT? Microsoft’s Evolving App Strategy Microsoft is trying to better align its applications through a new interface and improved cloud connectivity. Is this the right strategy? BY BRIEN M. POSEY THE NEW INTERFACE WHERE RT AND OFFICE FIT CLOUD CONNECTIVITY CAN MICROSOFT MAP THE FUTURE OF IT? VER THE PAST two decades, Microsoft’s strategy for desktop and mobile ap- plications has remained relatively static. Microsoft devoted much of its energy to creating operating systems and allowed applications to develop almost as an afterthought. THE NEW Even today the company adheres to this haphazard approach to applications. INTERFACE O At the same time, the company’s most recent product-release cycle demonstrates that Microsoft’s support for desktop and mobile apps is evolving. WHERE RT AND OFFICE FIT When it comes to application support in the company’s latest releases, two major themes have emerged: the new tile-based user interface (UI) and cloud con- nectivity. While both of these technologies benefit a segment of Microsoft’s cus- CLOUD CONNECTIVITY tomer base, they have also created numerous challenges for IT professionals. In particular, the new Windows 8 interface has been an impediment to adop- tion among business users, but it is part of a concerted effort on Microsoft’s part to build consistency throughout its application set. Despite this imperfect strat- egy, there are signs that the approach is pointing Microsoft in a direction that al- lows business users to productively use Windows, Office and other applications on PCs, tablets and smartphones. 2 MICROSOFT’S EVOLVING APP STRATEGY THE NEW INTERFACE WINDOWS’ NEW INTERFACE The most well-known element of the Windows 8 operating system is the new user interface (which at one time was called the Metro interface and is now known as the Windows 8-style UI). -

Tablets in the Enterprise: Comparing the Total Cost of Ownership
TABLETS IN THE ENTERPRISE: COMPARING THE TOTAL COST OF OWNERSHIP EXECUTIVE SUMMARY Windows 8 tablets provide a PC experience, which for many workers is essential to maintaining productivity. With Windows 8, users can run familiar desktop applications, maintaining productivity without having to find new ways to carry out their tasks. They can read, edit, and print their emails and Office documents—tasks that can be a challenge on other tablets. In addition to these productivity advantages, Intel Core i5 processor and Windows 8 tablets can provide enterprises with total cost of ownership (TCO) savings of up to 18 percent compared to other tablets. We expect additional TCO savings with Intel Core vPro™ processor-based tablets due to their additional manageability capabilities. We estimate tablets with Intel Architecture and Windows 8 will have lower TCO than other tablets, primarily due to the following: reduced software costs lower management costs improved end-user productivity JANUARY 2013 A PRINCIPLED TECHNOLOGIES WHITE PAPER Commissioned by Intel Corp. TOTAL COST OF OWNERSHIP OF TABLETS IN THE ENTERPRISE In this paper, we first present a TCO analysis for a hypothetical enterprise considering four major categories of tablets for their employees: Microsoft Windows 8 tablets, Windows RT tablets, Android tablets, and Apple iPads. Because the ranges of prices and capabilities differ among models within each category, we selected a single representative model for each. Following this analysis, we discuss the dominant issues in enterprise tablet computing as of this writing. We base our TCO analysis on the primary assumptions in Figure 1. Tablets must be nine inches or larger with 64 GB of storage and Wi-Fi support. -

Microsoft Surface for Education Limited Time Offer
Microsoft Surface for education limited time offer Surface RT (32GB) - AU $219 incl. GST (RRP is $389) Surface RT (32GB) with Touch Keyboard Cover - AU $279 incl. GST (RRP is $449) Surface RT (32GB) with Type Keyboard Cover - AU $319 incl. GST (RRP is $539) For a limited time only, Microsoft is offering education institution customers special pricing on the Surface RT tablet. This offer is available for order now through to 30 September 2013. Our mission in education is to help schools and universities, students and educators realise their full potential. One way we do this is by offering software, hardware and services at affordable prices to education institutions. Surface RT is a terrific tool for teaching and learning and we want students and educators to have the best technology on the market today. Surface RT for Schools and Universities Communicate with Skype and Lync Microsoft Surface RT is a great choice for schools and universities who Today schools are using Skype and Lync to host virtual classes, invite want powerful, affordable touch-enabled tablets for students, educators prominent speakers into classrooms, and connect with other schools and staff. In addition to cutting edge hardware specs, Surface RT comes from around the world. Lync when combined with Office 365 for Educa- with many software and cloud features that will have educators and tion is an enterprise-grade web meeting and collaboration solution that students teaching and learning in no time. provides HD video conferencing, instant messaging and presenting content. Many students and schools choose Skype for its simplicity, high Microsoft Office Built-In quality video and voice conference calls and very large user base. -
Bluetooth Setting Utility for Mcollection
Software Manual - Star Bluetooth Utility for mCollection- Supported Models MCP31LB MCP21LB POP10 Rev. 1.0 Introduction l This utility enables you to configure your mCollection printer. l This manual is made for the Star Bluetooth Utility Ver.2.0.0. l The Bluetooth Utility supports the following Windows OS versions: aWindows 7 32-bit and 64-bit aWindows 8 32-bit and 64-bit (except Windows RT) aWindows 8.1 32-bit and 64-bit (except Windows RT 8.1) aWindows 10 32-bit and 64-bit (except Windows 10 Mobile and Windows 10 IoT) * Limitation for Windows 8 / 8.1 / 10 - Desktop UI only. l Administrator privilege is required to execute this utility. Notice • All rights reserved. Reproduction of any part of this manual in any form whatsoever, without STAR’s express permission is forbidden. • The contents of this manual are subject to change without notice. • All efforts have been made to ensure the accuracy of the contents of this manual at the time of going to press. However, should any errors be detected, STAR would greatly appreciate being informed of them. • The above notwithstanding, STAR can assume no responsibility for any errors in this manual. © 2018 Star Micronics Co., Ltd. Bluetooth Utility 1. Getting Started With the Bluetooth Utility Make the following preparations before using this utility. 1. Complete Bluetooth pairing between the PC and the printer, and check the COM port access point. See the "Online Manual" for more information on pairing. 2. Executing the Bluetooth Utility To execute the Bluetooth utility, proceed as follows. 1. On the Windows taskbar, click 'Start', and then click 'All Programs' > 'Star Micronics' > 'Printer Software for mCollection'> 'Star Bluetooth for mCollection' . -
6.2.9200 for Windows 8, Windows RT, Windows Server 2012, Windows Storage Server 2012, and Windows Phone 8
Boot Manager Security Policy for FIPS 140‐2 Validation Microsoft Windows 8 Microsoft Windows Server 2012 Microsoft Windows RT Microsoft Surface Windows RT Microsoft Surface Windows 8 Pro Microsoft Windows Phone 8 Microsoft Windows Storage Server 2012 Boot Manager DOCUMENT INFORMATION Version Number 1.3 Updated On December 17, 2014 © 2014 Microsoft. All Rights Reserved Page 1 of 19 This Security Policy is non‐proprietary and may be reproduced only in its original entirety (without revision). Boot Manager The information contained in this document represents the current view of Microsoft Corporation on the issues discussed as of the date of publication. Because Microsoft must respond to changing market conditions, it should not be interpreted to be a commitment on the part of Microsoft, and Microsoft cannot guarantee the accuracy of any information presented after the date of publication. This document is for informational purposes only. MICROSOFT MAKES NO WARRANTIES, EXPRESS OR IMPLIED, AS TO THE INFORMATION IN THIS DOCUMENT. Complying with all applicable copyright laws is the responsibility of the user. This work is licensed under the Creative Commons Attribution-NoDerivs- NonCommercial License (which allows redistribution of the work). To view a copy of this license, visit http://creativecommons.org/licenses/by-nd-nc/1.0/ or send a letter to Creative Commons, 559 Nathan Abbott Way, Stanford, California 94305, USA. Microsoft may have patents, patent applications, trademarks, copyrights, or other intellectual property rights covering subject matter in this document. Except as expressly provided in any written license agreement from Microsoft, the furnishing of this document does not give you any license to these patents, trademarks, copyrights, or other intellectual property. -

All About Tablets What Is a Tablet?
All About Tablets What is a tablet? A tablet is any portable device with a touch screen that allows for mobile computing. It differs from a Smart Phone in that it does not have phone functionality. Otherwise, it can be nearly identical. An eReader is a type of tablet designed primarily for reading eBooks, and may or may not have the same advanced functionalities as a tablet. Things you can do with a tablet Most tablets have: Internet web browsing Calendar/Clock Email mp3/Music Playing Camera (Picture/Video) Some Androids and iPads allow for a keyboard/mouse to be connected, for easier use. Some also have a 3g (or 4g) antenna built-in, which allows for cell phone data access to the internet in areas where there is no WiFi available (this requires a subscription to use). Things you CAN’T do with a tablet Tablets cannot run or install traditional programs, like what a computer uses. Tablets only run “apps”. You cannot install a program or game unless it is available as an app. Not all tablets have apps. Some third-party tablets (that are neither Androids nor iPads) do not have an “App Store”, and only run the apps they come with. Tablets cannot connect to a printer. Some advanced printers allow for printing from Android or iPads, but not many do. Even if it has a USB port, you cannot just plug a USB device into a tablet unless the tablet supports it. Types of Tablets/Operating Systems Apple iOS: Used by all Apple devices, including iPhone, iPad, and even iPod Android OS: The most commonly used OS. -

Microsoft Iso Download Tool Windows 8
microsoft iso download tool windows 8 How to Download Windows 8/8.1 ISO Files? Here Is the Guide [Partition Manager] If you have a Windows ISO file, you can make a bootable USB media and use it to reinstall your operating system. In this post, MiniTool Partition Wizard introduces some methods to download a Windows 8.1 ISO file and you can have a try if you need. Quick Navigation : Windows 8 is an operating system produced by Microsoft. It received a mixed critical reception. In October 2013, Windows 8.1 was released to address complaints of Windows 8 users and reviewers, and it is better than Windows 8. Nowadays, Microsoft has stopped providing support and updates for Windows 8 RTM. Since Windows 8 devices no longer receive important security updates, Microsoft recommends users to upgrade Windows 8 to Windows 8.1, and they can make it by downloading a Windows 8.1 ISO file, create a bootable USB flash drive with the ISO file, and install Windows 8.1. It also works when users need to reinstall Windows 8.1. You might wonder how to download Windows 8.1 ISO file. Don’t worry. Here are some methods for you. Method 1: Get Windows 8.1 ISO Download from Microsoft. Microsoft supports Windows 8.1 ISO download free. Therefore, an easy way to download Windows 8.1 ISO is to visit the support page of Microsoft. Here are the detailed steps. Step 1 : Open your browser and search for Windows 8.1 ISO download. Click the first result which comes from the official website of Microsoft. -

Microsoft Windows (Phone)
Laat ons weten wat u vindt van deze sessie! Vul de evaluatie in via www.techdaysapp.nl en maak kans op een van de 20 prijzen*. Prijswinnaars worden bekend gemaakt via Twitter (#TechDaysNL). Gebruik hiervoor de code op uw badge. Let us know how you feel about this session! Give your feedback via www.techdaysapp.nl and possibly win one of the 20 prizes*. Winners will be announced via Twitter (#TechDaysNL). Use your personal code on your badge. * Over de uitslag kan niet worden gecorrespondeerd, prijzen zijn voorbeelden – All results are final, prices are examples Application deployment across several devices with ConfigMgr 2012 R2 Kenneth van Surksum & Peter Daalmans Agenda •Introduction •Microsoft’s Cross Plaform Architecture •Enrollment •Deployment Types for Mobile Applications •Settings Management Introduction Who we are Kenneth van Surksum Consultant at itgration Microsoft MVP for 3 yrs, vExpert for 2 yrs Authoring: • Contributor System Center 2012 Configuration Manager Unleashed • Contributor System Center 2012 R2 Configuration Manager Unleashed • Contributor System Center 2012 R2 Service Manager Unleashed • Co-Author Mastering Windows 7 Deployment Communities: • Co-founder WMUG NL (http://wmug.nl) • Founder and Blogger www.vansurksum.com • Chief Editor at virtualization.info en cloudcomputing.info Speaker: • Microsoft Techdays • Microsoft Management Summit Follow me: @kennethvs / www.vansurksum.com Who we are Peter Daalmans Senior Technical Consultant at IT-Concern 3 year Microsoft MVP: Enterprise Client Management (ConfigMgr and Windows Intune) Author: • Mastering System Center 2012 Configuration Manager • Mastering System Center 2012 R2 Configuration Manager Communities: • Co-founder WMUG NL (http://wmug.nl) • Founder and Blogger ConfigMgrBlog.com Speaker: • Spoke on several events like TechDays Netherlands, ExpertsLive, User Group meetings, TechEd New Zealand and TechEd Australia. -
End User Devices Security Guidance: Windows 8 RT Updated 14 October 2013
GOV.UK Guidance End User Devices Security Guidance: Windows 8 RT Updated 14 October 2013 Contents 1. Usage Scenario 2. Summary of Platform Security 3. How the Platform Can Best Satisfy the Security Recommendations 4. Network Architecture 5. Deployment Process 6. Provisioning Steps 7. Policy Recommendations 8. Enterprise Considerations This guidance is applicable to devices running Windows 8 RT. Windows RT implements a different set of features to the Enterprise edition of Windows 8 and so is considered separately. This guidance was developed following testing performed on Microsoft Surface tablets. 1. Usage Scenario Windows RT devices will be used remotely over Wi-Fi and 3G to connect back to the enterprise over a VPN. This enables a variety of remote working approaches such as accessing OFFICIAL email; creating, editing, reviewing and commenting on OFFICIAL documents; accessing the OFFICIAL intranet resources, the Internet and other web-resources. To support these scenarios, the following architectural choices are recommended: All data should be routed over a secure enterprise VPN to ensure the confidentiality and integrity of the traffic, and to benefit from enterprise protective monitoring solutions. Arbitrary third-party application installation by users is not permitted on the device. Procedural measures are in place to enable users to install trusted applications as approved and monitored by the enterprise. 2. Summary of Platform Security This platform has been assessed against each of the twelve security recommendations, and that assessment is shown in the table below. Explanatory text indicates that there is something related to that recommendation that the risk owners should be aware of. -
Windows 8.1 Preview Product Guide
Windows 8.1 Preview product guide Microsoft makes no warranties, express or implied, with respect to any information described in this document. Images show pre-released product which may be substantially modified before the product is commercially released. Some apps or features described in this document may not be updated or included in Windows 8.1 Preview and may be modified before the product is commercially released. © 2013 Microsoft Corporation. All rights reserved. Microsoft, Active Directory, Bing, BitLocker, Direct2D, Direct3D, Excel, Internet Explorer, Office, OneNote, Outlook, PowerPoint, SkyDrive, Skype, SmartGlass, SmartScreen, Visual Studio, Windows, Windows Server, Word, Xbox, are trademarks of the Microsoft group of companies. All other trademarks are property of their respective owners. Contents Windows devices and services for the way you live 4 Windows devices and services for business 30 Introducing Windows 8.1 Preview and Windows RT 8.1 Preview 7 Everything you do for work, from anywhere 32 Great business devices 34 8 Great, personal devices Always business-ready 35 The right device for you 10 Make it unique 11 Building Windows Store apps 38 Your personal experience across devices 12 Make money in the Windows Store 40 Devices provide a world of choice 42 14 Bringing together all you do Engaging customers through leading user experiences 44 Connect 16 Modern engineering enables the next wave of app innovation 46 Create 18 Discover 20 Advancing the vision of Windows 8 50 Work 26 Play 28 Windows devices and services for the way you live Windows 8 introduced innovation for a new era of devices designed for mobility and touch. -
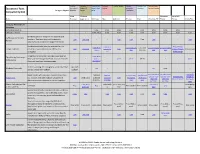
Chart-Of-Educational-Tools.Pdf
Category: Category: Category: Note- Category: Category: Writing Category: Category: Class Category: Study - Educational Tools Reminders & Research & Saving & Note- Reading Information Interaction Learning - Practice Category Legend: Schedules Sources taking Presentation Compatibility Grid Web Chrome Windows Basic Cell Tools About Browser (app; ext.) Windows Mac Android iPhone iPad Windows RT Phone Phone Kindle Fire Category: Reminders & Schedules Reminders: Built-in - - Free Free Free Free Free Free Free Free Calenders: Built-in - - Free; OS 8 Free Free Free Free Free Free Free Free Electronic planner designed for students and myHomework Student teachers. Teachers may push homework Free Free; app - - Free Free Free Free - - Free Planner information to students through Teachers.io. Electronic calendar/planner and task list. It is Free; third Free; limited Free; third sync or third party sync or third sync or third party sync or third party Google Calendar possible to view the calendar offline on a Free Free; app party or iCal Free access through third party apps party apps party apps apps apps computer. sync text message Integration of calendar, reminders and task list. Free; third CalenGoo by Dominique May sync with Google Calendar, but not required. - - party - $5.99 $6.99 $6.99 - - - $5.99 Andre Gunia Does not need internet connection. BlueStacks Includes, among other programs, a Calendar that sync with Windows Essentials - Free - - - - sync sync - - can be synced with Outlook. Outlook sync with Email service with calendar, reminders and task Outlook Outlook sync limited; sync limited; sync with built in sync with built in calendar <OR> calendar <OR> Outlook SMS Google or Outlook.com list. -
Accessibility in Windows 8
Accessibility in Windows 8 Overview of accessibility in Windows 8, tutorials, and keyboard shortcuts Published by Microsoft Corporation, Trustworthy Computing One Microsoft Way Redmond, Washington 98052 Copyright 2012 Microsoft Corporation. All rights reserved. No part of the contents of this document may be reproduced or transmitted in any form or by any means without the written permission of the publisher. For permissions, visit www.microsoft.com. Microsoft and Windows are trademarks of Microsoft Corporation in the United States and/or other countries. Find further information on Microsoft Trademarks (http://www.microsoft.com/about/legal/en/us/IntellectualProperty/Trademarks/EN-US.aspx). Table of Contents Overview of Accessibility in Windows 8 .................................................................................................. 7 What’s new in Windows 8 accessibility ...................................................................................................................................7 Narrator and touch-enabled devices .................................................................................................................................................. 7 Magnifier and touch-enabled devices ............................................................................................................................................... 9 Ease of Access .............................................................................................................................................. 12 Make