Objective Information Theory: a Sextuple Model and 9 Kinds of Metrics
Total Page:16
File Type:pdf, Size:1020Kb
Load more
Recommended publications
-

Information Technology Management 14
Information Technology Management 14 Valerie Bryan Practitioner Consultants Florida Atlantic University Layne Young Business Relationship Manager Indianapolis, IN Donna Goldstein GIS Coordinator Palm Beach County School District Information Technology is a fundamental force in • IT as a management tool; reshaping organizations by applying investment in • understanding IT infrastructure; and computing and communications to promote competi- • ȱǯ tive advantage, customer service, and other strategic ęǯȱǻȱǯȱǰȱŗşşŚǼ ȱȱ ȱ¢ȱȱȱ¢ǰȱȱ¢Ȃȱ not part of the steamroller, you’re part of the road. ǻ ȱǼ ȱ ¢ȱ ȱ ȱ ęȱ ȱ ȱ ¢ǯȱȱȱȱȱ ȱȱ ȱ- ¢ȱȱȱȱȱǯȱ ǰȱ What is IT? because technology changes so rapidly, park and recre- ation managers must stay updated on both technological A goal of management is to provide the right tools for ȱȱȱȱǯ ěȱ ȱ ě¢ȱ ȱ ȱ ȱ ȱ ȱ ȱȱȱȱ ȱȱȱǰȱȱǰȱ ȱȱȱȱȱȱǯȱȱȱȱ ǰȱȱȱȱ ȱȱ¡ȱȱȱȱ recreation organization may be comprised of many of terms crucial for understanding the impact of tech- ȱȱȱȱǯȱȱ ¢ȱ ȱ ȱ ȱ ȱ ǯȱ ȱ ȱ ȱ ȱ ȱ ǯȱ ȱ - ȱȱęȱȱȱ¢ȱȱȱȱ ¢ȱǻ Ǽȱȱȱȱ¢ȱ ȱȱȱȱ ǰȱ ȱ ȱ ȬȬ ȱ ȱ ȱ ȱȱǯȱȱȱȱȱ ¢ȱȱǯȱȱ ȱȱȱȱ ȱȱ¡ȱȱȱȱȱǻǰȱŗşŞśǼǯȱ ȱȱȱȱȱȱĞȱȱȱȱ ǻȱ¡ȱŗŚǯŗȱ Ǽǯ ě¢ȱȱȱȱǯ Information technology is an umbrella term Details concerning the technical terms used in this that covers a vast array of computer disciplines that ȱȱȱȱȱȱȬȬęȱ ȱȱ permit organizations to manage their information ǰȱ ȱ ȱ ȱ Ȭȱ ¢ȱ ǯȱ¢ǰȱȱ¢ȱȱȱ ȱȱ ǯȱȱȱȱȱȬȱ¢ȱ a fundamental force in reshaping organizations by applying ȱȱ ȱȱ ȱ¢ȱȱȱȱ investment in computing and communications to promote ȱȱ¢ǯȱ ȱȱȱȱ ȱȱ competitive advantage, customer service, and other strategic ȱ ǻȱ ȱ ŗŚȬŗȱ ęȱ ȱ DZȱ ęȱǻǰȱŗşşŚǰȱǯȱřǼǯ ȱ Ǽǯ ȱ¢ȱǻ Ǽȱȱȱȱȱ ȱȱȱęȱȱȱ¢ȱȱ ȱ¢ǯȱȱȱȱȱ ȱȱ ȱȱ ȱȱȱȱ ȱ¢ȱ ȱȱǯȱ ȱ¢ǰȱ ȱȱ ȱDZ ȱȱȱȱǯȱ ȱȱȱȱǯȱ It lets people learn things they didn’t think they could • ȱȱȱ¢ǵ ȱǰȱȱǰȱȱȱǰȱȱȱȱȱǯȱ • the manager’s responsibilities; ǻȱǰȱȱ¡ȱĜȱȱĞǰȱȱ • information resources; ǷȱǯȱȱȱřŗǰȱŘŖŖŞǰȱ • disaster recovery and business continuity; ȱĴDZȦȦ ǯ ǯǼ Information Technology Management 305 Exhibit 14. -

Bioinformatics 1
Bioinformatics 1 Bioinformatics School School of Science, Engineering and Technology (http://www.stmarytx.edu/set/) School Dean Ian P. Martines, Ph.D. ([email protected]) Department Biological Science (https://www.stmarytx.edu/academics/set/undergraduate/biological-sciences/) Bioinformatics is an interdisciplinary and growing field in science for solving biological, biomedical and biochemical problems with the help of computer science, mathematics and information technology. Bioinformaticians are in high demand not only in research, but also in academia because few people have the education and skills to fill available positions. The Bioinformatics program at St. Mary’s University prepares students for graduate school, medical school or entry into the field. Bioinformatics is highly applicable to all branches of life sciences and also to fields like personalized medicine and pharmacogenomics — the study of how genes affect a person’s response to drugs. The Bachelor of Science in Bioinformatics offers three tracks that students can choose. • Bachelor of Science in Bioinformatics with a minor in Biology: 120 credit hours • Bachelor of Science in Bioinformatics with a minor in Computer Science: 120 credit hours • Bachelor of Science in Bioinformatics with a minor in Applied Mathematics: 120 credit hours Students will take 23 credit hours of core Bioinformatics classes, which included three credit hours of internship or research and three credit hours of a Bioinformatics Capstone course. BS Bioinformatics Tracks • Bachelor of Science -
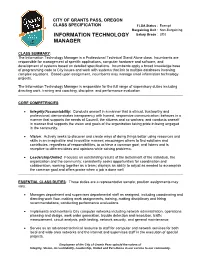
Information Technology Manager Is a Professional Technical Stand Alone Class
CITY OF GRANTS PASS, OREGON CLASS SPECIFICATION FLSA Status : Exempt Bargaining Unit : Non-Bargaining INFORMATION TECHNOLOGY Salary Grade : UD2 MANAGER CLASS SUMMARY: The Information Technology Manager is a Professional Technical Stand Alone class. Incumbents are responsible for management of specific applications, computer hardware and software, and development of systems based on detailed specifications. Incumbents apply a broad knowledge base of programming code to City issues and work with systems that link to multiple databases involving complex equations. Based upon assignment, incumbents may manage small information technology projects. The Information Technology Manager is responsible for the full range of supervisory duties including directing work, training and coaching, discipline, and performance evaluation. CORE COMPETENCIES: Integrity/Accountability: Conducts oneself in a manner that is ethical, trustworthy and professional; demonstrates transparency with honest, responsive communication; behaves in a manner that supports the needs of Council, the citizens and co-workers; and conducts oneself in manner that supports the vision and goals of the organization taking pride in being engaged in the community. Vision: Actively seeks to discover and create ways of doing things better using resources and skills in an imaginative and innovative manner; encourages others to find solutions and contributes, regardless of responsibilities, to achieve a common goal; and listens and is receptive to different ideas and opinions while solving problems. Leadership/United: Focuses on outstanding results of the betterment of the individual, the organization and the community; consistently seeks opportunities for coordination and collaboration, working together as a team; displays an ability to adjust as needed to accomplish the common goal and offers praise when a job is done well. -

Use of Bioinformatics Resources and Tools by Users of Bioinformatics Centers in India Meera Yadav University of Delhi, [email protected]
University of Nebraska - Lincoln DigitalCommons@University of Nebraska - Lincoln Library Philosophy and Practice (e-journal) Libraries at University of Nebraska-Lincoln 2015 Use of Bioinformatics Resources and Tools by Users of Bioinformatics Centers in India meera yadav University of Delhi, [email protected] Manlunching Tawmbing Saha Institute of Nuclear Physisc, [email protected] Follow this and additional works at: http://digitalcommons.unl.edu/libphilprac Part of the Library and Information Science Commons yadav, meera and Tawmbing, Manlunching, "Use of Bioinformatics Resources and Tools by Users of Bioinformatics Centers in India" (2015). Library Philosophy and Practice (e-journal). 1254. http://digitalcommons.unl.edu/libphilprac/1254 Use of Bioinformatics Resources and Tools by Users of Bioinformatics Centers in India Dr Meera, Manlunching Department of Library and Information Science, University of Delhi, India [email protected], [email protected] Abstract Information plays a vital role in Bioinformatics to achieve the existing Bioinformatics information technologies. Librarians have to identify the information needs, uses and problems faced to meet the needs and requirements of the Bioinformatics users. The paper analyses the response of 315 Bioinformatics users of 15 Bioinformatics centers in India. The papers analyze the data with respect to use of different Bioinformatics databases and tools used by scholars and scientists, areas of major research in Bioinformatics, Major research project, thrust areas of research and use of different resources by the user. The study identifies the various Bioinformatics services and resources used by the Bioinformatics researchers. Keywords: Informaion services, Users, Inforamtion needs, Bioinformatics resources 1. Introduction ‘Needs’ refer to lack of self-sufficiency and also represent gaps in the present knowledge of the users. -

Establishing the Basis for a CIS (Computer Information Systems) Undergraduate Program: on Seeking the Body of Knowledge
Information Systems Education Journal (ISEDJ) 13 (5) ISSN: 1545-679X September 2015 Establishing the Basis for a CIS (Computer Information Systems) Undergraduate Program: On Seeking the Body of Knowledge Herbert E. Longenecker, Jr. [email protected] University of South Alabama Mobile, AL 36688, USA Jeffry Babb [email protected] West Texas A&M University Canyon, TX 79016, USA Leslie J. Waguespack [email protected] Bentley University Waltham, Massachusetts 02452, USA Thomas N. Janicki [email protected] University of North Carolina Wilmington Wilmington, NC 28403, USA David Feinstein [email protected] University of South Alabama Mobile, AL 36688, USA Abstract The evolution of computing education spans a spectrum from computer science (CS) grounded in the theory of computing, to information systems (IS), grounded in the organizational application of data processing. This paper reports on a project focusing on a particular slice of that spectrum commonly labeled as computer information systems (CIS) and reflected in undergraduate academic programs designed to prepare graduates for professions as software developers building systems in government, commercial and not-for-profit enterprises. These programs with varying titles number in the hundreds. This project is an effort to determine if a common knowledge footprint characterizes CIS. If so, an eventual goal would be to describe the proportions of those essential knowledge components and propose guidelines specifically for effective undergraduate CIS curricula. Professional computing societies (ACM, IEEE, AITP (formerly DPMA), etc.) over the past fifty years have sponsored curriculum guidelines for various slices of education that in aggregate offer a compendium of knowledge areas in ©2015 EDSIG (Education Special Interest Group of the AITP) Page 37 www.aitp-edsig.org /www.isedj.org Information Systems Education Journal (ISEDJ) 13 (5) ISSN: 1545-679X September 2015 computing. -

An Academic Discipline
Information Technology – An Academic Discipline This document represents a summary of the following two publications defining Information Technology (IT) as an academic discipline. IT 2008: Curriculum Guidelines for Undergraduate Degree Programs in Information Technology. (Nov. 2008). Association for Computing Machinery (ACM) and IEEE Computer Society. Computing Curricula 2005 Overview Report. (Sep. 2005). Association for Computing Machinery (ACM), Association for Information Systems (AIS), Computer Society (IEEE- CS). The full text of these reports with details on the model IT curriculum and further explanation of the computing disciplines and their commonalities/differences can be found online: http://www.acm.org/education/education/curricula-recommendations) From IT 2008: Curriculum Guidelines for Undergraduate Degree Programs in Information Technology IT programs aim to provide IT graduates with the skills and knowledge to take on appropriate professional positions in Information Technology upon graduation and grow into leadership positions or pursue research or graduate studies in the field. Specifically, within five years of graduation a student should be able to: 1. Explain and apply appropriate information technologies and employ appropriate methodologies to help an individual or organization achieve its goals and objectives; 2. Function as a user advocate; 3. Manage the information technology resources of an individual or organization; 4. Anticipate the changing direction of information technology and evaluate and communicate the likely utility of new technologies to an individual or organization; 5. Understand and, in some cases, contribute to the scientific, mathematical and theoretical foundations on which information technologies are built; 6. Live and work as a contributing, well-rounded member of society. In item #2 above, it should be recognized that in many situations, "a user" is not a homogeneous entity. -

Applications of Social Media in Hydroinformatics: a Survey
Applications of Social Media in Hydroinformatics: A Survey Yufeng Yu, Yuelong Zhu, Dingsheng Wan,Qun Zhao [email protected] College of Computer and Information Hohai University Nanjing, Jiangsu, China Kai Shu, Huan Liu [email protected] School of Computing, Informatics, and Decision Systems Engineering Arizona State University Tempe, Arizona, U.S.A Abstract Floods of research and practical applications employ social media data for a wide range of public applications, including environmental monitoring, water resource managing, disaster and emergency response, etc. Hydroinformatics can benefit from the social media technologies with newly emerged data, techniques and analytical tools to handle large datasets, from which creative ideas and new values could be mined. This paper first proposes a 4W (What, Why, When, hoW) model and a methodological structure to better understand and represent the application of social media to hydroinformatics, then provides an overview of academic research of applying social media to hydroinformatics such as water environment, water resources, flood, drought and water Scarcity management. At last,some advanced topics and suggestions of water-related social media applications from data collection, data quality management, fake news detection, privacy issues , algorithms and platforms was present to hydroinformatics managers and researchers based on previous discussion. Keywords: Social Media, Big Data, Hydroinformatics, Social Media Mining, Water Resource, Data Quality, Fake News 1 Introduction In the past two -

Use of Hydroinformatics Technology in Central and Eastern Europe During Last Decade K
Use of Hydroinformatics technology in Central and Eastern Europe during last decade K. Pryl, T. Metelka, M. Suchanek To cite this version: K. Pryl, T. Metelka, M. Suchanek. Use of Hydroinformatics technology in Central and Eastern Europe during last decade. Novatech 2010 - 7ème Conférence internationale sur les techniques et stratégies durables pour la gestion des eaux urbaines par temps de pluie / 7th International Conference on sustainable techniques and strategies for urban water management, Jun 2010, Lyon, France. pp.3. hal-03296498 HAL Id: hal-03296498 https://hal.archives-ouvertes.fr/hal-03296498 Submitted on 22 Jul 2021 HAL is a multi-disciplinary open access L’archive ouverte pluridisciplinaire HAL, est archive for the deposit and dissemination of sci- destinée au dépôt et à la diffusion de documents entific research documents, whether they are pub- scientifiques de niveau recherche, publiés ou non, lished or not. The documents may come from émanant des établissements d’enseignement et de teaching and research institutions in France or recherche français ou étrangers, des laboratoires abroad, or from public or private research centers. publics ou privés. NOVATECH 2010 Use of Hydroinformatics technology in Central and Eastern Europe during last decade L’utilisation de la technologie hydro-informatique en Europe centrale et orientale au cours de la dernière décennie Tomas Metelka, Karel Pryl, Milan Suchanek DHI a.s., Na Vrsich 5, Prague 10, 100 00, Czech Republic ([email protected], [email protected], [email protected]) RÉSUMÉ Au cours de la dernière décennie, l’hydro-informatique s’est progressivement développée dans le secteur de l’ingénierie de l’eau, complétée par des méthodes adéquates et des approches qui diffèrent souvent beaucoup des normes largement acceptées. -

Information Systems Foundations Theory, Representation and Reality
Information Systems Foundations Theory, Representation and Reality Information Systems Foundations Theory, Representation and Reality Dennis N. Hart and Shirley D. Gregor (Editors) Workshop Chair Shirley D. Gregor ANU Program Chairs Dennis N. Hart ANU Shirley D. Gregor ANU Program Committee Bob Colomb University of Queensland Walter Fernandez ANU Steven Fraser ANU Sigi Goode ANU Peter Green University of Queensland Robert Johnston University of Melbourne Sumit Lodhia ANU Mike Metcalfe University of South Australia Graham Pervan Curtin University of Technology Michael Rosemann Queensland University of Technology Graeme Shanks University of Melbourne Tim Turner Australian Defence Force Academy Leoni Warne Defence Science and Technology Organisation David Wilson University of Technology, Sydney Published by ANU E Press The Australian National University Canberra ACT 0200, Australia Email: [email protected] This title is also available online at: http://epress.anu.edu.au/info_systems02_citation.html National Library of Australia Cataloguing-in-Publication entry Information systems foundations : theory, representation and reality Bibliography. ISBN 9781921313134 (pbk.) ISBN 9781921313141 (online) 1. Management information systems–Congresses. 2. Information resources management–Congresses. 658.4038 All rights reserved. No part of this publication may be reproduced, stored in a retrieval system or transmitted in any form or by any means, electronic, mechanical, photocopying or otherwise, without the prior permission of the publisher. Cover design by Brendon McKinley with logo by Michael Gregor Authors’ photographs on back cover: ANU Photography Printed by University Printing Services, ANU This edition © 2007 ANU E Press Table of Contents Preface vii The Papers ix Theory Designing for Mutability in Information Systems Artifacts, Shirley Gregor and Juhani Iivari 3 The Eect of the Application Domain in IS Problem Solving: A Theoretical Analysis, Iris Vessey 25 Towards a Unied Theory of Fit: Task, Technology and Individual, Michael J. -

Information System Owner
DOE CYBERSECURITY: CORE COMPETENCY TRAINING REQUIREMENTS Key Cybersecurity Role: Information System Owner Role Definition: The Information System Owner (also referred to as System Owner) is the individual responsible for the overall procurement, development, integration, modification, operation, maintenance, and retirement of an information system. The System Owner is a key contributor in developing system design specifications to ensure the security and user operational needs are documented, tested, and implemented. Competency Area: Data Security Functional Requirement: Design Competency Definition: Refers to the application of the principles, policies, and procedures necessary to ensure the confidentiality, integrity, availability, and privacy of data in all forms of media (i.e., electronic and hardcopy) throughout the data life cycle. Behavioral Outcome: The System Owner will understand the policies and procedures required to protect all categories of information as well as have a working knowledge of data access controls required to ensure the confidentiality, integrity, and availability of information. He/she will apply this knowledge during all phases of the System Development Life Cycle (SDLC). Training concepts to be addressed at a minimum: Identify and document the appropriate level of protection for data, including use of encryption. Specify data and information classification, sensitivity, and need-to-know requirements by information type on a system in terms of its confidentiality, integrity, and availability. Utilize DOE M 205.1-5 to determine the information impacts for unclassified information and DOE M 205.1-4 to determine the Consequence of Loss for classified information. Create authentication and authorization system for users to gain access to data based on assigned privileges and permissions. -

Bioinformatics Careers
University of Pittsburgh | School of Arts and Sciences | Department of Biological Sciences BIOINFORMATICS CAREERS General Information • Bioinformatics is an interdisciplinary field that incorporates computer science and biology to research, develop, and apply computational tools and approaches to manage and process large sets of biological data. • The Bioinformatics career focuses on creating software tools to store, manage, interpret, and analyze data at the genome, proteome, transcriptome, and metabalome levels. Primary investigations consist of integrating information from DNA and protein sequences and protein structure and function. • Bioinformatics jobs exist in biomedical, molecular medicine, energy development, biotechnology, environmental restoration, homeland security, forensic investigations, agricultural, and animal science fields. • Most bioinformatics jobs require a Bachelor’s degree. Post-grad programs, University level teaching & research, and administrative positions require a graduate degree. The following list provides a brief sample of responsibilities, employers, jobs, and industries for individuals with a degree in this major. This is by no means an exhaustive listing, but is simply designed to give initial insight into a particular career field that would employ the skills and knowledge gained through this major. Areas Employers Environmental/Government • BLM • Private • Sequence genomes of bacteria useful in energy production, • DOE Contractors environmental cleanup, industrial processing, and toxic waste • EPA • National Parks reduction. • NOAA • State Wildlife • Examination of genomes dependent on carbon sources to address • USDA Agencies climate change concerns. • USFS • Army Corp of • Sequence genomes of plants and animals to produce stronger, • USFWS Engineers resistant crops and healthier livestock. • USGS • Transfer genes into plants to improve nutritional quality. Industrial • DOD • Study the genetic material of microbes and isolate the genes that give • DOE them their unique abilities to survive under extreme conditions. -

Information System Development Using Augmented Reality Tools*
Information system development using augmented reality tools* Grigorev Rostislav Aleksandrovich Valijanov Bahrom Adhamdzon-ugli Kazan Federal University Kazan Federal University Kazan, Russia Kazan, Russia [email protected] [email protected] Medvedeva Olga Anatolievna Mustafina Svetlana Anatol’evna Kazan Federal University Bashkir State University Kazan, Russia Ufa, Russia [email protected] [email protected] Abstract This work is devoted to the issues of visualization and information processing, in particular, to improving the visualization of 3D objects using augmented reality technology. The concept of augmented reality offers a more advanced user interface for visualization due to a combination of natural ways to control the change of angle of an object and visualization in a real context. In the process of performing the work, computer graphics, algorithms, and modeling methods were used. The experimental part of the work was carried out using a set of development tools for tracking Vuforia and Unity development tools. Introduction Augmented reality (AR) is an interactive experience of a real-world environment where the objects that reside in the real world are enhanced by computer-generated perceptual information, sometimes across multiple sensory modalities, including visual, auditory, haptic, somatosensory and olfactory. AR can be defined as a system that fulfills three basic features: a combination of real and virtual worlds, real-time interaction, and accurate 3D registration of virtual and real objects. The overlaid sensory information can be constructive (i.e. additive to the natural environment), or destructive (i.e. masking of the natural environment). This experience is seamlessly interwoven with the physical world such that it is perceived as an immersive aspect of the real environment.