Open Source a Free Software
Total Page:16
File Type:pdf, Size:1020Kb
Load more
Recommended publications
-

Nurturing the Proliferation of Open Source Software
White Paper opensource vision Nurturing the proliferation of Open Source Software 1 Table of Contents Executive Summary ......................................................................................................................................................................ii 1 Introduction.................................................................................................................................................................1 1.1 Challenges and opportunities....................................................................................................................................2 1.2 The wider context ......................................................................................................................................................3 1.3 Potential impact, issues and mitigating them ........................................................................................................4 2 Core strategic principles ........................................................................................................................................................6 3 Current landscape ........ .............................................................................................................................................................7 3.1 Government context..................................................................................................................................................7 3.2 EU context .....................................................................................................................................................................9 -

La Sécurité Informatique Edition Livres Pour Tous (
La sécurité informatique Edition Livres pour tous (www.livrespourtous.com) PDF générés en utilisant l’atelier en source ouvert « mwlib ». Voir http://code.pediapress.com/ pour plus d’informations. PDF generated at: Sat, 13 Jul 2013 18:26:11 UTC Contenus Articles 1-Principes généraux 1 Sécurité de l'information 1 Sécurité des systèmes d'information 2 Insécurité du système d'information 12 Politique de sécurité du système d'information 17 Vulnérabilité (informatique) 21 Identité numérique (Internet) 24 2-Attaque, fraude, analyse et cryptanalyse 31 2.1-Application 32 Exploit (informatique) 32 Dépassement de tampon 34 Rétroingénierie 40 Shellcode 44 2.2-Réseau 47 Attaque de l'homme du milieu 47 Attaque de Mitnick 50 Attaque par rebond 54 Balayage de port 55 Attaque par déni de service 57 Empoisonnement du cache DNS 66 Pharming 69 Prise d'empreinte de la pile TCP/IP 70 Usurpation d'adresse IP 71 Wardriving 73 2.3-Système 74 Écran bleu de la mort 74 Fork bomb 82 2.4-Mot de passe 85 Attaque par dictionnaire 85 Attaque par force brute 87 2.5-Site web 90 Cross-site scripting 90 Défacement 93 2.6-Spam/Fishing 95 Bombardement Google 95 Fraude 4-1-9 99 Hameçonnage 102 2.7-Cloud Computing 106 Sécurité du cloud 106 3-Logiciel malveillant 114 Logiciel malveillant 114 Virus informatique 120 Ver informatique 125 Cheval de Troie (informatique) 129 Hacktool 131 Logiciel espion 132 Rootkit 134 Porte dérobée 145 Composeur (logiciel) 149 Charge utile 150 Fichier de test Eicar 151 Virus de boot 152 4-Concepts et mécanismes de sécurité 153 Authentification forte -
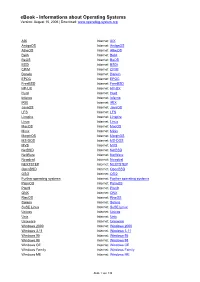
Ebook - Informations About Operating Systems Version: August 15, 2006 | Download
eBook - Informations about Operating Systems Version: August 15, 2006 | Download: www.operating-system.org AIX Internet: AIX AmigaOS Internet: AmigaOS AtheOS Internet: AtheOS BeIA Internet: BeIA BeOS Internet: BeOS BSDi Internet: BSDi CP/M Internet: CP/M Darwin Internet: Darwin EPOC Internet: EPOC FreeBSD Internet: FreeBSD HP-UX Internet: HP-UX Hurd Internet: Hurd Inferno Internet: Inferno IRIX Internet: IRIX JavaOS Internet: JavaOS LFS Internet: LFS Linspire Internet: Linspire Linux Internet: Linux MacOS Internet: MacOS Minix Internet: Minix MorphOS Internet: MorphOS MS-DOS Internet: MS-DOS MVS Internet: MVS NetBSD Internet: NetBSD NetWare Internet: NetWare Newdeal Internet: Newdeal NEXTSTEP Internet: NEXTSTEP OpenBSD Internet: OpenBSD OS/2 Internet: OS/2 Further operating systems Internet: Further operating systems PalmOS Internet: PalmOS Plan9 Internet: Plan9 QNX Internet: QNX RiscOS Internet: RiscOS Solaris Internet: Solaris SuSE Linux Internet: SuSE Linux Unicos Internet: Unicos Unix Internet: Unix Unixware Internet: Unixware Windows 2000 Internet: Windows 2000 Windows 3.11 Internet: Windows 3.11 Windows 95 Internet: Windows 95 Windows 98 Internet: Windows 98 Windows CE Internet: Windows CE Windows Family Internet: Windows Family Windows ME Internet: Windows ME Seite 1 von 138 eBook - Informations about Operating Systems Version: August 15, 2006 | Download: www.operating-system.org Windows NT 3.1 Internet: Windows NT 3.1 Windows NT 4.0 Internet: Windows NT 4.0 Windows Server 2003 Internet: Windows Server 2003 Windows Vista Internet: Windows Vista Windows XP Internet: Windows XP Apple - Company Internet: Apple - Company AT&T - Company Internet: AT&T - Company Be Inc. - Company Internet: Be Inc. - Company BSD Family Internet: BSD Family Cray Inc. -

An Introduction to the X Window System Introduction to X's Anatomy
An Introduction to the X Window System Robert Lupton This is a limited and partisan introduction to ‘The X Window System’, which is widely but improperly known as X-windows, specifically to version 11 (‘X11’). The intention of the X-project has been to provide ‘tools not rules’, which allows their basic system to appear in a very large number of confusing guises. This document assumes that you are using the configuration that I set up at Peyton Hall † There are helpful manual entries under X and Xserver, as well as for individual utilities such as xterm. You may need to add /usr/princeton/X11/man to your MANPATH to read the X manpages. This is the first draft of this document, so I’d be very grateful for any comments or criticisms. Introduction to X’s Anatomy X consists of three parts: The server The part that knows about the hardware and how to draw lines and write characters. The Clients Such things as terminal emulators, dvi previewers, and clocks and The Window Manager A programme which handles negotiations between the different clients as they fight for screen space, colours, and sunlight. Another fundamental X-concept is that of resources, which is how X describes any- thing that a client might want to specify; common examples would be fonts, colours (both foreground and background), and position on the screen. Keys X can, and usually does, use a number of special keys. You are familiar with the way that <shift>a and <ctrl>a are different from a; in X this sensitivity extends to things like mouse buttons that you might not normally think of as case-sensitive. -
Modelsim SE Tutorial T-3
ModelSim® SE Tutorial Version 5.6d Published: 6/Aug/02 The world’s most popular HDL simulator T-2 ModelSim /VHDL, ModelSim /VLOG, ModelSim /LNL, and ModelSim /PLUS are produced by Model Technology™ Incorporated. Unauthorized copying, duplication, or other reproduction is prohibited without the written consent of Model Technology. The information in this manual is subject to change without notice and does not represent a commitment on the part of Model Technology. The program described in this manual is furnished under a license agreement and may not be used or copied except in accordance with the terms of the agreement. The online documentation provided with this product may be printed by the end-user. The number of copies that may be printed is limited to the number of licenses purchased. ModelSim is a registered trademark and ChaseX and TraceX are trademarks of Model Technology Incorporated. Model Technology is a trademark of Mentor Graphics Corporation. PostScript is a registered trademark of Adobe Systems Incorporated. UNIX is a registered trademark of AT&T in the USA and other countries. FLEXlm is a trademark of Globetrotter Software, Inc. IBM, AT, and PC are registered trademarks, AIX and RISC System/6000 are trademarks of International Business Machines Corporation. Windows, Microsoft, and MS-DOS are registered trademarks of Microsoft Corporation. OSF/Motif is a trademark of the Open Software Foundation, Inc. in the USA and other countries. SPARC is a registered trademark and SPARCstation is a trademark of SPARC International, Inc. Sun Microsystems is a registered trademark, and Sun, SunOS and OpenWindows are trademarks of Sun Microsystems, Inc. -
Tms320c3x Workstation Emulator Installation Guide
TMS320C3x Workstation Emulator Installation Guide 1994 Microprocessor Development Systems Printed in U.S.A., December 1994 2617676-9741 revision A TMS320C3x Workstation Emulator Installation Guide SPRU130 December 1994 Printed on Recycled Paper IMPORTANT NOTICE Texas Instruments (TI) reserves the right to make changes to its products or to discontinue any semiconductor product or service without notice, and advises its customers to obtain the latest version of relevant information to verify, before placing orders, that the information being relied on is current. TI warrants performance of its semiconductor products and related software to the specifications applicable at the time of sale in accordance with TI’s standard warranty. Testing and other quality control techniques are utilized to the extent TI deems necessary to support this warranty. Specific testing of all parameters of each device is not necessarily performed, except those mandated by government requirements. Certain applications using semiconductor products may involve potential risks of death, personal injury, or severe property or environmental damage (“Critical Applications”). TI SEMICONDUCTOR PRODUCTS ARE NOT DESIGNED, INTENDED, AUTHORIZED, OR WARRANTED TO BE SUITABLE FOR USE IN LIFE-SUPPORT APPLICATIONS, DEVICES OR SYSTEMS OR OTHER CRITICAL APPLICATIONS. Inclusion of TI products in such applications is understood to be fully at the risk of the customer. Use of TI products in such applications requires the written approval of an appropriate TI officer. Questions concerning potential risk applications should be directed to TI through a local SC sales offices. In order to minimize risks associated with the customer’s applications, adequate design and operating safeguards should be provided by the customer to minimize inherent or procedural hazards. -

Installation Guide Meeting Maker
Enterprise Scheduling & Calendaring Meeting Maker Installation Guide 010-MAN-0560 Copyright © 1999 by ON Technology Corporation. All rights reserved worldwide. Second Printing: June 1999 Information in this document is subject to change without notice and does not represent a commitment on the part of ON Technology. The software described in this document is furnished under a license agreement and may be used only in accordance with that agreement. This document has been provided pursuant to an agreement containing restrictions on its use. This document is also protected by federal copyright law. No part of this document may be reproduced or distributed, transcribed, stored in a retrieval system, translated into any spoken or computer language or transmitted in any form or by any means whatsoever without the prior written consent of: ON Technology Corporation One Cambridge Center Cambridge, MA 02142 USA Telephone: (617) 374 1400 Fax: (617) 374 1433 ON Technology makes no warranty, representation or promise not expressly set forth in this agreement. ON Technology disclaims and excludes any and all implied warranties of merchantability, title, or fitness for a particular purpose. ON Technology does not warrant that the software or documentation will satisfy your requirements or that the software and documentation are without defect or error or that the operation of the software will be uninterrupted. LIMITATION OF LIABILITY: ON Technology's aggregate liability, as well as that of the authors of programs sold by ON Technology, arising from or relating to this agreement or the software or documentation is limited to the total of all payments made by or for you for the license. -

BSD UNIX Toolbox 1000+ Commands for Freebsd, Openbsd
76034ffirs.qxd:Toolbox 4/2/08 12:50 PM Page iii BSD UNIX® TOOLBOX 1000+ Commands for FreeBSD®, OpenBSD, and NetBSD®Power Users Christopher Negus François Caen 76034ffirs.qxd:Toolbox 4/2/08 12:50 PM Page ii 76034ffirs.qxd:Toolbox 4/2/08 12:50 PM Page i BSD UNIX® TOOLBOX 76034ffirs.qxd:Toolbox 4/2/08 12:50 PM Page ii 76034ffirs.qxd:Toolbox 4/2/08 12:50 PM Page iii BSD UNIX® TOOLBOX 1000+ Commands for FreeBSD®, OpenBSD, and NetBSD®Power Users Christopher Negus François Caen 76034ffirs.qxd:Toolbox 4/2/08 12:50 PM Page iv BSD UNIX® Toolbox: 1000+ Commands for FreeBSD®, OpenBSD, and NetBSD® Power Users Published by Wiley Publishing, Inc. 10475 Crosspoint Boulevard Indianapolis, IN 46256 www.wiley.com Copyright © 2008 by Wiley Publishing, Inc., Indianapolis, Indiana Published simultaneously in Canada ISBN: 978-0-470-37603-4 Manufactured in the United States of America 10 9 8 7 6 5 4 3 2 1 Library of Congress Cataloging-in-Publication Data is available from the publisher. No part of this publication may be reproduced, stored in a retrieval system or transmitted in any form or by any means, electronic, mechanical, photocopying, recording, scanning or otherwise, except as permitted under Sections 107 or 108 of the 1976 United States Copyright Act, without either the prior written permission of the Publisher, or authorization through payment of the appropriate per-copy fee to the Copyright Clearance Center, 222 Rosewood Drive, Danvers, MA 01923, (978) 750-8400, fax (978) 646-8600. Requests to the Publisher for permis- sion should be addressed to the Legal Department, Wiley Publishing, Inc., 10475 Crosspoint Blvd., Indianapolis, IN 46256, (317) 572-3447, fax (317) 572-4355, or online at http://www.wiley.com/go/permissions. -
Installing Framemaker for UNIX®
Adobe ® FrameMaker ® 7.0 Installing FrameMaker for UNIX® © 2002 Adobe Systems Incorporated and its licensors. All rights reserved. Installing Adobe FrameMaker for UNIX This manual, as well as the software described in it, is furnished under license and may be used or copied only in accordance with the terms of such license. The content of this manual is furnished for informational use only, is subject to change without notice, and should not be construed as a com- mitment by Adobe Systems Incorporated. Adobe Systems Incorporated assumes no responsibility or liability for any errors or inaccuracies that may appear in this book. Except as permitted by such license, no part of this publication may be reproduced, stored in a retrieval system, or transmitted, in any form or by any means, electronic, mechanical, recording, or otherwise, without the prior written permission of Adobe Systems Incorporated. Please remember that existing artwork or images that you may want to include in your project may be protected under copyright law. The unautho- rized incorporation of such material into your new work could be a violation of the rights of the copyright owner. Please be sure to obtain any per- mission required from the copyright owner. Any references to company names in sample templates are for demonstration purposes only and are not intended to refer to any actual organization. Adobe, the Adobe logo, Acrobat, Acrobat Reader, Adobe Type Manager, ATM, Display PostScript, Distiller, Exchange, FrameMaker, InstantView, Post- Script, and SuperATM are trademarks of Adobe Systems Incorporated. The following are copyrights of their respective companies or organizations: Portions reproduced with the permission of Apple Computer, Inc. -

Administraci´On De Sistemas Unix
ADMINISTRACION´ DE SISTEMAS UNIX Antonio Villal´onHuerta <[email protected]> Sergio Bayarri Gausi <[email protected]> Mayo, 2005 2 ´Indice General 1 Introducci´on:el superusuario 5 1.1 Conceptos b´asicospara administradores . 5 1.2 El entorno del superusuario . 5 1.3 El papel del administrador . 6 1.4 Comunicaci´oncon los usuarios. 7 2 Arranque y parada de m´aquina 11 2.1 Arranque del sistema . 11 2.2 Parada del sistema . 16 2.3 El int´erpretede ´ordenes . 16 3 Procesos 19 3.1 Conceptos b´asicos . 19 3.2 Actividades de los usuarios . 20 3.3 Control de procesos . 23 4 Sistemas de ficheros 27 4.1 Ficheros . 27 4.2 Sistemas de ficheros . 29 4.3 Creaci´one incorporaci´onde sistemas de ficheros . 30 4.4 Gesti´ondel espacio en disco . 31 4.5 Algunos sistemas de ficheros . 32 5 Tareas. Mantenimiento del sistema 35 5.1 Gesti´onde usuarios . 35 5.2 Automatizaci´onde tareas . 39 5.3 Actualizaci´one instalaci´onde paquetes software . 42 5.4 Copias de seguridad . 44 5.4.1 Consejos a considerar al realizar copias de seguridad . 45 5.4.2 Planificaci´onde un programa de copias de seguridad . 45 5.4.3 Realizaci´onde copias de seguridad y restauraci´onde archivos . 46 5.4.4 Ejemplo pr´actico:copia de seguridad del sistema . 51 5.4.5 Resumen . 52 5.5 Instalaci´onde la red . 52 5.5.1 Conceptos sobre redes . 52 5.5.2 Configuraci´onde la red . 55 5.5.3 Configuraci´onde servicios en Internet . -
Kratka Povijest Unixa Od Unicsa Do Freebsda I Linuxa
Kratka povijest UNIXa Od UNICSa do FreeBSDa i Linuxa 1 Autor: Hrvoje Horvat Naslov: Kratka povijest UNIXa - Od UNICSa do FreeBSDa i Linuxa Licenca i prava korištenja: Svi imaju pravo koristiti, mijenjati, kopirati i štampati (printati) knjigu, prema pravilima GNU GPL licence. Mjesto i godina izdavanja: Osijek, 2017 ISBN: 978-953-59438-0-8 (PDF-online) URL publikacije (PDF): https://www.opensource-osijek.org/knjige/Kratka povijest UNIXa - Od UNICSa do FreeBSDa i Linuxa.pdf ISBN: 978-953- 59438-1- 5 (HTML-online) DokuWiki URL (HTML): https://www.opensource-osijek.org/dokuwiki/wiki:knjige:kratka-povijest- unixa Verzija publikacije : 1.0 Nakalada : Vlastita naklada Uz pravo svakoga na vlastito štampanje (printanje), prema pravilima GNU GPL licence. Ova knjiga je napisana unutar inicijative Open Source Osijek: https://www.opensource-osijek.org Inicijativa Open Source Osijek je član udruge Osijek Software City: http://softwarecity.hr/ UNIX je registrirano i zaštićeno ime od strane tvrtke X/Open (Open Group). FreeBSD i FreeBSD logo su registrirani i zaštićeni od strane FreeBSD Foundation. Imena i logo : Apple, Mac, Macintosh, iOS i Mac OS su registrirani i zaštićeni od strane tvrtke Apple Computer. Ime i logo IBM i AIX su registrirani i zaštićeni od strane tvrtke International Business Machines Corporation. IEEE, POSIX i 802 registrirani i zaštićeni od strane instituta Institute of Electrical and Electronics Engineers. Ime Linux je registrirano i zaštićeno od strane Linusa Torvaldsa u Sjedinjenim Američkim Državama. Ime i logo : Sun, Sun Microsystems, SunOS, Solaris i Java su registrirani i zaštićeni od strane tvrtke Sun Microsystems, sada u vlasništvu tvrtke Oracle. Ime i logo Oracle su u vlasništvu tvrtke Oracle. -

Open Systems December 27, 2019
1969 1970 1971 1972 1973 UNIX Time-Sharing System UNIX Time-Sharing System UNIX Time-Sharing System UNICS First Edition (V1) Second Edition (V2) Third Edition (V3) september 1969 november 3, 1971 june 12, 1972 february 1973 Open Systems December 27, 2019 Éric Lévénez 1998-2019 <http://www.levenez.com/unix/> 1974 1975 1976 1977 SRI Eunice UNSW Mini Unix may 1977 LSX UNIX Time-Sharing System UNIX Time-Sharing System UNIX Time-Sharing System Fourth Edition (V4) Fifth Edition (V5) Sixth Edition (V6) november 1973 june 1974 may 1975 PWB/UNIX PWB 1.0 1974 july 1, 1977 USG 1.0 TS 1.0 1977 MERT 1974 RT 1.0 1977 1978 1979 1980 UNIX Time-Sharing System Seventh Edition Modified (V7M) december 1980 1BSD 2BSD 2.79BSD march 9, 1978 may 10, 1979 april 1980 3BSD 4.0BSD march 1980 october 1980 UCLA Secure Unix 1979 The Wollongong Group Eunice (Edition 7) 1980 UNSW 01 UNSW 04 january 1978 november 1979 BRL Unix V4.1 july 1979 UNIX 32V V7appenda may 1979 february 12, 1980 UNIX Time-Sharing System Seventh Edition (V7) january 1979 PWB 2.0 PWB 1.2 1978 XENIX OS august 25, 1980 CB UNIX 1 CB CB UNIX 3 UNIX 2 USG 2.0 USG 3.0 TS 2.0 TS 3.0 TS 3.0.1 1978 1979 1980 Interactive IS/1 UCLA Locally Cooperating Unix Systems 1980 Note 1 : an arrow indicates an inheritance like a compatibility, it is not only a matter of source code. Note 2 : this diagram shows complete systems and [micro]kernels like Mach, Linux, the Hurd..