INF 5XX:Application of Modern Cryptography and Cryptanalysis To
Total Page:16
File Type:pdf, Size:1020Kb
Load more
Recommended publications
-

Trusted System Concepts
Trusted System Concepts Trusted System Concepts Marshall D. Abrams, Ph.D. Michael V. Joyce The MITRE Corporation 7525 Colshire Drive McLean, VA 22102 703-883-6938 [email protected] This is the first of three related papers exploring how contemporary computer architecture affects security. Key issues in this changing environment, such as distributed systems and the need to support multiple access control policies, necessitates a generalization of the Trusted Computing Base paradigm. This paper develops a conceptual framework with which to address the implications of the growing reliance on Policy-Enforcing Applications in distributed environments. 1 INTRODUCTION A significant evolution in computer software architecture has taken place over the last quarter century. The centralized time-sharing systems of the 1970s and early 1980s are rapidly being superseded by the distributed architectures of the 1990s. As an integral part of the architecture evolution, the composition of the system access control policy has changed. Instead of a single policy, the system access control policy is more likely to be a composite of several constituent policies implemented in applications that create objects and enforce their own unique access control policies. This paper first provides a survey that explains how the security community developed the accepted concepts and criteria that addressed the time-shared architectures. Second, the paper focuses on the changes currently ongoing, providing insight into the driving forces and probable directions. This paper presents contemporary thinking; it summarizes and generalizes vertical and horizontal extensions to the Trusted Computing Base (TCB) concept. While attempting to be logical and rigorous, formalism is avoided. This paper was first published in Computers & Security, Vol. -
Trusted Computer System Evaluation Criteria
DoD 5200.28-STD Supersedes CSC-STD-00l-83, dtd l5 Aug 83 Library No. S225,7ll DEPARTMENT OF DEFENSE STANDARD DEPARTMENT OF DEFENSE TRUSTED COMPUTER SYSTEM EVALUATION CRITERIA DECEMBER l985 December 26, l985 Page 1 FOREWORD This publication, DoD 5200.28-STD, "Department of Defense Trusted Computer System Evaluation Criteria," is issued under the authority of an in accordance with DoD Directive 5200.28, "Security Requirements for Automatic Data Processing (ADP) Systems," and in furtherance of responsibilities assigned by DoD Directive 52l5.l, "Computer Security Evaluation Center." Its purpose is to provide technical hardware/firmware/software security criteria and associated technical evaluation methodologies in support of the overall ADP system security policy, evaluation and approval/accreditation responsibilities promulgated by DoD Directive 5200.28. The provisions of this document apply to the Office of the Secretary of Defense (ASD), the Military Departments, the Organization of the Joint Chiefs of Staff, the Unified and Specified Commands, the Defense Agencies and activities administratively supported by OSD (hereafter called "DoD Components"). This publication is effective immediately and is mandatory for use by all DoD Components in carrying out ADP system technical security evaluation activities applicable to the processing and storage of classified and other sensitive DoD information and applications as set forth herein. Recommendations for revisions to this publication are encouraged and will be reviewed biannually by the National Computer Security Center through a formal review process. Address all proposals for revision through appropriate channels to: National Computer Security Center, Attention: Chief, Computer Security Standards. DoD Components may obtain copies of this publication through their own publications channels. -
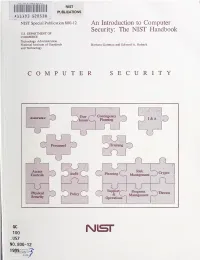
An Introduction to Computer Security: the NIST Handbook U.S
HATl INST. OF STAND & TECH R.I.C. NIST PUBLICATIONS AlllOB SEDS3fl NIST Special Publication 800-12 An Introduction to Computer Security: The NIST Handbook U.S. DEPARTMENT OF COMMERCE Technology Administration National Institute of Standards Barbara Guttman and Edward A. Roback and Technology COMPUTER SECURITY Contingency Assurance User 1) Issues Planniii^ I&A Personnel Trairang f Access Risk Audit Planning ) Crypto \ Controls O Managen»nt U ^ J Support/-"^ Program Kiysfcal ~^Tiireats Policy & v_ Management Security Operations i QC 100 Nisr .U57 NO. 800-12 1995 The National Institute of Standards and Technology was established in 1988 by Congress to "assist industry in the development of technology . needed to improve product quality, to modernize manufacturing processes, to ensure product reliability . and to facilitate rapid commercialization ... of products based on new scientific discoveries." NIST, originally founded as the National Bureau of Standards in 1901, works to strengthen U.S. industry's competitiveness; advance science and engineering; and improve public health, safety, and the environment. One of the agency's basic functions is to develop, maintain, and retain custody of the national standards of measurement, and provide the means and methods for comparing standards used in science, engineering, manufacturing, commerce, industry, and education with the standards adopted or recognized by the Federal Government. As an agency of the U.S. Commerce Department's Technology Administration, NIST conducts basic and applied research in the physical sciences and engineering, and develops measurement techniques, test methods, standards, and related services. The Institute does generic and precompetitive work on new and advanced technologies. NIST's research facilities are located at Gaithersburg, MD 20899, and at Boulder, CO 80303. -

Expanding Malware Defense by Securing Software Installations*
Expanding Malware Defense by Securing Software Installations? Weiqing Sun1, R. Sekar1, Zhenkai Liang2 and V.N. Venkatakrishnan3 1 Department of Computer Science, Stony Brook University 2 Department of Computer Science, Carnegie Mellon University 3 Department of Computer Science, University of Illinois, Chicago. Abstract. Software installation provides an attractive entry vector for malware: since installations are performed with administrator privileges, malware can easily get the en- hanced level of access needed to install backdoors, spyware, rootkits, or “bot” software, and to hide these installations from users. Previous research has been focused mainly on securing the execution phase of untrusted software, while largely ignoring the safety of installations. Even security-enhanced operating systems such as SELinux and Vista don't usually impose restrictions during software installs, expecting the system administrator to “know what she is doing.” This paper addresses this “gap in armor” by securing software installations. Our technique can support a diversity of package managers and software installers. It is based on a framework that simplifies the development and enforcement of policies that govern safety of installations. We present a simple policy that can be used to prevent untrusted software from modifying any of the files used by benign software packages, thus blocking the most common mechanism used by malware to ensure that it is run automatically after each system reboot. While the scope of our technique is limited to the installation phase, it can be easily combined with approaches for secure execution, e.g., by ensuring that all future runs of an untrusted package will take place within an administrator-specified sandbox. -

Cybersecurity and Domestic Surveillance Or Why Trusted Computing Shouldn’T Be: Agency, Trust and the Future of Computing
Cybersecurity and Domestic Surveillance or Why Trusted Computing Shouldn’t Be: Agency, Trust and the Future of Computing. Douglas Thomas Annenberg School for Communication University of Southern California As you begin playing the latest MP3 file downloaded from the Internet your computer flashes an ominous warning. A few second later your computer shuts down and you are unable to turn it back on. The work of malicious hackers? The result of the latest virus? The work of cyber-terrorists disrupting the Internet? The answer becomes apparent a few days later when you receive a summons to appear in court for federal copyright infringement. Before it stopped working, your now defunct computer forwarded a list of suspicious files to the record companies. Legislation currently under consideration by Congress would make such scenario not only likely, but also perfectly legal. At the same time, computer chip manufactures, software producers and record company executives are hard at work, bringing products to market to make it a reality. While many of our worst fears about the future of the Internet circulate around notions of hackers, viruses and cyber-terrorists, the real threat to our individual freedoms and liberties are grounded in a threat much closer to home—Digital Rights Management, information security, and domestic surveillance. As the number of cameras, recording devices, and monitoring apparatuses grows larger each year, the public is offered cataclysmic scenarios of financial ruin and devastating loss of life as the result of a few mouse clicks or carefully written code by cyber-terrorists.1 In reality such threats are nearly non-existent.2 Why then are stories of cyber-terrorists using the Internet to attack American power plants, airlines, hospitals and food services so widespread? The answer has more to do with record companies, Walt Disney, and corporate databases than we might possibly imagine. -
A Rule-Set Approach to Formal Modeling of a Trusted Computer System
A Rule-Set Approach to Formal Modeling of a Trusted Computer System Leonard J. LaPadula The MITRE Corporation ABSTRACT: This article describes a rule-set approach to formal modeling of a trusted computer system. A finite state machine models the access operations of the trusted system while a separate rule set expresses the system's trust policies. A powerful feature of this approach is its ability to fit several widely differing trust policies easily within the same model. The paper shows how this approach to modeling relates to general ideas of access control. Departing from the traditional abstractness of discussions of formal models, the paper also relates this approach to the implementation of real systems by connecting the rule set of the model to the system operations of a UNIX System V system. This gives high confidence that a real system could clearly derive from the elements of the formal model instead of additionally depending on numerous design and policy decisions not addressed in the model. Neither are the trust policies left largely to the imagination of the reader-the rule base has detailed specifications of the mandatory access control policy of UNIX Sys- tem V/IVILS, a version of the Clark-Wilson integrity policy, and two supporting policies that implement roles. A fundamental point established by the work reported in this article is that formal modeling can be moved considerably closer to implementation of real systems, a fact that has great beneficial impact on the possibility of building high assurance trusted systems. @1994 The USENIX Association, Computing Systems, Vol. -

Trends and Directions in Trusted Computing: Models, Architectures and Technologies
CORE Metadata, citation and similar papers at core.ac.uk Provided Proceedingsby Directory of Open of Access the International Journals MultiConference of Engineers and Computer Scientists 2008 Vol I IMECS 2008, 19-21 March, 2008, Hong Kong Trends and Directions in Trusted Computing: Models, Architectures and Technologies Muhammad Amin1, Shabaz Khan2, Tamleek Ali3, Saleem Gul4 Abstract—Until recently, all the security measures have Mail Extensions), SSL, SET (Secure Electronic Transaction), addressed servers or networks while clients or network endpoints IEEE 802.11 WEP, IEEE 802.1x, etc [2]. have missed the required security concerns relatively. Most of the mechanisms safeguarding endpoints (clients) are software TCG’s primary work is the development of an inexpensive based. Making endpoints survive in open and reasonably exposed chip, known as the Trusted Platform Module (TPM) [3] or environments-like internet-demand that client security should stand by a tried and true dependence and merely software the secure hardware, that can help users protect information based mechanisms are inadequate in providing the desired assets from compromise due to external software attack security level. Trusted Computing (TC) initiatives solve these through integrating security standards mentioned above, at the security problems through operating environments, applications hardware level. A software based TPM [4] for testing and and secure hardware changes to the personal computer. Using research is also available. secure hardware as a basis for trusted computing provides a level of relevance since hardware-based security is mooted difficult TPM verifies the system integrity in network environment, to compromise than conventional approaches. Therefore, TC provides a powerful set of features to implement applications and turns a system into a trusted one through Core Root of such as secure auctions, integrity measurement, and biometric Trust Measurement (CRTM) including trusted boot, strong identifcation. -
2Bsecure [email protected] 301-922-3884
Input to the Commission on Enhancing National Cybersecurity � Building a Trusted Computing Foundation � Introduction: In the early 1980's, the U.S. Government (largely the Department of Defense and the Intelligence Community) recognized that the only way to stop determined/sophisticated (e.g., Nation-State) hacking into computer networks, systems and applications was to establish requirements for raising the level of security and, as important, trust in our computing systems. Considerable time and energy was devoted to establishing principles, rules and, eventually, technical and programmatic requirements for building security and trust into contemporary computing systems. The result of this research and academic deliberations was the publication of the Department of Defense Trusted System Computer Evaluation Criteria (The Orange Book) in 1983. The Orange Book was followed up by an additional series of guides known as the Rainbow Series of trusted computer evaluation criteria for topics including networks, supply chain and application security. While the Rainbow series of trusted computer evaluation guides were written (largely) by inside the beltway people, for use by inside the beltway organizations, many real systems were actually built by industry and at the higher levels of trust (i.e., B3-A1) were indeed “unhackable.” While these systems mostly used proprietary firmware and operating systems (thus, why they failed in the commercial market), they succeeded in demonstrating that computing platforms can be built with high levels of security and trust and can dramatically raise the bar for would-be hackers, including sophisticated hackers. Their legacy lives on today in the implementation of many contemporary high-security products like SE/Linux, Trusted Solaris, the Blackberry phone and even the Apple IOS security architecture. -

Trusted Computing Update
Trusted Computing Update Trusted Computing Update Marshall D. Abrams, Ph.D. Michael V. Joyce The MITRE Corporation 7525 Colshire Drive McLean, VA 22102 703-883-6938 [email protected] This is the second paper of a series of three related papers that examine contemporary information technology concepts. The first paper examined how the security community developed the accepted concepts and criteria, looked at changes currently ongoing, and provided insight into the driving forces and probable directions. This paper presents contemporary thinking about object management and summarizes vertical and horizontal extensions to the Trusted Computing Base (TCB) concept. 1 INTRODUCTION The evolution in computer software architecture has prompted significant changes in the structure of security functions and the composition of trusted information technology systems. Conventionally, most of the security-relevant functions are concentrated within the operating system. Often, these functions, especially those dealing with access control, are commingled with object management functions. This natural inclination to commingle these functions draws attention to the relevance of object management in achieving security goals. Following an introduction of the object manager function, this paper examines the relationships between object management and the vertical and horizontal extensions for structuring the Trusted Computing Base and describes representative examples of access control techniques in contemporary information technology systems. This paper was first published in Computers & Security, Vol. 14 No.1 pp. 57-68, © Elsevier Advanced Technology 1995, Oxford, UK; http://www.elsevier.nl/locate/compsec. This is the second of three related papers. 1 Trusted Computing Update 2 OBJECTS AND OBJECT MANAGEMENT An object manager is a logical function responsible for handling and controlling entities in the logical address space. -
Trustworthy Computing at APL
S. C. Lee Trustworthy Computing at APL Susan C. Lee ABSTRACT As dependence on cyber-enabled, networked systems grows, so does the need to make them more trustworthy, especially in the high-stakes adversarial environment of Johns Hopkins Uni- versity Applied Physics Laboratory (APL) sponsors. This article describes APL’s research over nearly two decades to make computing systems more trustworthy—ensuring that they will do what we expect them to do, and nothing else. The basic elements of a trustworthy com- puting environment—high-assurance systems providing a reference monitor and a separation mechanism—appeared in the literature in the 1970s. When APL began its work, however, few mechanisms to create these environments existed, and even fewer systems incorporated them. True to its legacy, APL did not stop at research into potential mechanisms for trustworthy comput- ing; it also led the way by demonstrating how they could be realized in practical, working systems. This article details APL’s development of reference monitors, including an early reference monitor that today is able to detect the activity of a very stealthy threat in executing code. It describes APL’s innovative use of existing COTS hardware to provide separation and APL’s role in the creation of new hardware in COTS computers specifically intended to provide a high-assurance separation mechanism. Finally, it describes APL’s continuing efforts to make high-assurance system devel- opment tools both available and usable by APL’s engineers, including the application of formal methods, a very potent but nascent software assurance technique, to find life-threatening flaws in real-life critical systems. -
Rule-Set Modeling of a Trusted Computer System
Essay 9 Rule-Set Modeling of a Trusted Computer System Leonard J. LaPadula 7KLV HVVD\ GHVFULEHV D QHZ DSSURDFK WR IRUPDO PRGHOLQJ RI D WUXVWHG FRPSXWHU V\VWHP $ ILQLWHVWDWH PDFKLQH PRGHOV WKH DFFHVV RSHUDWLRQVRIWKHWUXVWHGFRPSXWHUV\VWHPZKLOHDVHSDUDWH UXOH VHW H[SUHVVHV WKH V\VWHP·V WUXVW SROLFLHV $ SRZHUIXO IHDWXUH RI WKLV DS SURDFKLVLWVDELOLW\WRILWVHYHUDOZLGHO\GLIIHULQJWUXVWSROLFLHVHDVLO\ ZLWKLQWKHVDPHPRGHO:HZLOOVKRZKRZWKLVDSSURDFKWRPRGHOLQJ UHODWHVWRJHQHUDOLGHDVRIDFFHVVFRQWURODV\RXPLJKWH[SHFW:HZLOO DOVR UHODWH WKLV DSSURDFK WR WKH LPSOHPHQWDWLRQ RI UHDO V\VWHPV E\ FRQQHFWLQJ WKH UXOH VHW RI WKH PRGHO WR WKH V\VWHP RSHUDWLRQV RI D 8QL[6\VWHP9V\VWHP7KHWUXVWSROLFLHVZHGHPRQVWUDWHLQWKHUXOH VHWRIWKHPRGHOLQFOXGHWKHPDQGDWRU\DFFHVVFRQWUROSROLF\RI81,; 6\VWHP 90/6 D YHUVLRQ RI WKH &ODUN:LOVRQ LQWHJULW\ SROLF\ DQG WZRVXSSRUWLQJSROLFLHVWKDWLPSOHPHQWUROHV 7KHPRGHOLQJDSSURDFKZHZLOOGLVFXVVJUHZRXWRIVHYHUDOLGHDV GHYHORSHG LQ WKH *HQHUDOL]HG )UDPHZRUN IRU $FFHVV &RQWURO *)$& SURMHFWGLUHFWHGE\$EUDPV>$%5$@7KHYLVLRQRIWKDWSURMHFWZDV WR JDLQ JUHDWHU XWLOLW\ LQ RXU trusted computer systems E\ FUHDWLQJ D WHFKQRORJ\IRUSXWWLQJDULFKVHWRIYDULRXVaccess control policiesLQWRD VLQJOHWUXVWHGFRPSXWHUV\VWHP2XUPRGHOLQJDSSURDFKUHVSRQGVWR WKHFKDOOHQJHRIWKDWYLVLRQDVH[SUHVVHGLQWKHVHREMHFWLYHV 0DNHLWHDV\WRVWDWHIRUPDOL]HDQGDQDO\]HDFFHVVFRQWUROSROLFLHV EHVLGHV WUDGLWLRQDO mandatory access control 0$& DQG discretionary access control '$& WRLQFUHDVHWKHDYDLODELOLW\RIGLYHUVHDVVXUHG VHFXULW\SROLFLHV 0DNHLWIHDVLEOHWRFRQILJXUHDV\VWHPZLWKVHFXULW\SROLFLHVFKRVHQ IURPDYHQGRUSURYLGHGVHWRIRSWLRQVZLWKFRQILGHQFHWKDWWKHUH -

Cloaking Malware with the Trusted Platform Module
Cloaking Malware with the Trusted Platform Module Alan M. Dunn Owen S. Hofmann Brent Waters Emmett Witchel The University of Texas at Austin {adunn,osh,bwaters,witchel}@cs.utexas.edu Abstract in Microsoft’s popular BitLocker drive encryption soft- The Trusted Platform Module (TPM) is commonly ware [7] and the United States Department of Defense has thought of as hardware that can increase platform secu- required the TPM as a solution for securing data on lap- rity. However, it can also be used for malicious pur- tops [4]. TPMs are regularly included on desktop, laptop, poses. The TPM, along with other hardware, can imple- and server-class computers from a number of manufac- ment a cloaked computation, whose memory state cannot turers. The wide dissemination of TPM functionality is be observed by any other software, including the operat- potentially a boon for computer security, but this paper ing system and hypervisor. We show that malware can examines the potential of the TPM for malware authors (a use cloaked computations to hide essential secrets (like first to our knowledge). the target of an attack) from a malware analyst. A malware writer can use the TPM for implementing We describe and implement a protocol that establishes cloaked computations which, combined with a protocol an encryption key under control of the TPM that can only described in this paper, impede malware analysis. The be used by a specific infection program. An infected host TPM is used with “late launch” processor mechanisms then proves the legitimacy of this key to a remote mal- (Intel’s Trusted Execution Technology [12, 8], abbrevi- ware distribution platform, and receives and executes an ated TXT, and AMD’s Secure Startup mechanism [10]) encrypted payload in a way that prevents software visibil- that ensure uninterrupted execution of secure binaries.