Attacking SMS
Total Page:16
File Type:pdf, Size:1020Kb
Load more
Recommended publications
-

SOP 202 Iridium Satellite Phone Provisioning
Standard Operating Procedure Updated: Apr 27, 2017 DOCUMENT NUMBER: SOP202 TITLE: Iridium Satellite Phone Provisioning PURPOSE: This document describes the provisioning and testing of Iridium Satellite phones. It is intended for all Greenland and Alaska field site personnel. BACKGROUND: A satellite telephone, satellite phone, or satphone is a type of mobile phone that connects to orbiting satellites instead of terrestrial cell sites. They provide similar functionality to terrestrial mobile telephones; voice, short messaging service and low-bandwidth internet access are supported through most systems. Depending on the architecture of a particular system, coverage may include the entire Earth or only specific regions. DETAILS: Components Required for Testing • Activated sim chips with phone number labels from IT&C staff • Preconditioned and charged batteries • External iridium egg antenna deployed outside in order to receive satellite signal inside the building • Updated Iridium phone number cheat sheet and Quick use guide Iridium Satellite Phone Testing Procedures • Insert activated SIM chip into satphone • Insert a preconditioned and charged battery into the satphone.. • Place battery cover on the satphone • Connect the satphone being tested to the external iridium egg antenna using a stubby antenna connector • Turn on the satphone and allow the registration process to complete Page 1 of 3 Standard Operating Procedure Updated: Apr 27, 2017 • Make a phone call using the satphone to a known number (ie your cellphone number, land line or a known working Iridium phone) • Make a phone call using your cellphone number, land line or a known working Iridium phone to the satphone being tested. • Adjust the iridium phone audio speaker to highest volume • Set the iridium phone to Ringer only and adjust the ringer to the highest volume • Turn call Forwarding off • Per each phone, adhere the phone number label to the front of the Iridium phone • If above test passed, continue onto next section. -

Ten Steps to Smartphone Security
Ten Steps to Smartphone Security Smartphones continue to grow in popularity and are now as powerful and functional as many computers. It is important to protect your smartphone just like you protect your computer as mobile cybersecurity threats are growing. These mobile security tips can help you reduce the risk of exposure to mobile security threats: 1. Set PINs and passwords. To prevent unauthorized access to your phone, set a password or Personal Identification Number (PIN) on your phone’s home screen as a first line of defense in case your phone is lost or stolen. When possible, use a different password for each of your important log-ins (email, banking, personal sites, etc.). You should configure your phone to automatically lock after five minutes or less when your phone is idle, as well as use the SIM password capability available on most smartphones. 2. Do not modify your smartphone’s security settings. Do not alter security settings for convenience. Tampering with your phone’s factory settings, jailbreaking, or rooting your phone undermines the built-in security features offered by your wireless service and smartphone, while making it more susceptible to an attack. 3. Backup and secure your data. You should backup all of the data stored on your phone – such as your contacts, documents, and photos. These files can be stored on your computer, on a removal storage card, or in the cloud. This will allow you to conveniently restore the information to your phone should it be lost, stolen, or otherwise erased. 4. Only install apps from trusted sources. -

Handover Parameters Optimisation Techniques in 5G Networks
sensors Article Handover Parameters Optimisation Techniques in 5G Networks Wasan Kadhim Saad 1,2,*, Ibraheem Shayea 2, Bashar J. Hamza 1, Hafizal Mohamad 3, Yousef Ibrahim Daradkeh 4 and Waheb A. Jabbar 5,6 1 Engineering Technical College-Najaf, Al-Furat Al-Awsat Technical University (ATU), Najaf 31001, Iraq; [email protected] 2 Electronics and Communication Engineering Department, Faculty of Electrical and Electronics Engineering, Istanbul Technical University (ITU), Istanbul 34467, Turkey; [email protected] 3 Faculty of Engineering and Built Environment, Universiti Sains Islam Malaysia, Bandar Baru Nilai, Nilai 71800, Malaysia; hafi[email protected] 4 Department of Computer Engineering and Networks, College of Engineering at Wadi Addawasir, Prince Sattam Bin Abdulaziz University, Al Kharj 11991, Saudi Arabia; [email protected] 5 Faculty of Electrical & Electronics Engineering Technology, Universiti Malaysia Pahang, Pekan 26600, Malaysia; [email protected] 6 Center for Software Development & Integrated Computing, Universiti Malaysia Pahang, Gambang 26300, Malaysia * Correspondence: [email protected] Abstract: The massive growth of mobile users will spread to significant numbers of small cells for the Fifth Generation (5G) mobile network, which will overlap the fourth generation (4G) network. A tremendous increase in handover (HO) scenarios and HO rates will occur. Ensuring stable and reliable connection through the mobility of user equipment (UE) will become a major problem in future mobile networks. This problem will be magnified with the use of suboptimal handover control parameter (HCP) settings, which can be configured manually or automatically. Therefore, Citation: Saad, W.K.; Shayea, I.; the aim of this study is to investigate the impact of different HCP settings on the performance Hamza, B.J.; Mohamad, H.; of 5G network. -
Sophos Mobile Security
Sophos Mobile Security Protect your Android devices against malware and other threats The market dominance of Android devices and the inherent openness of Android led to the proliferation of malware and Potentially Unwanted Applications (PUA). SophosLabs detected over a million new pieces of malware in 2014 alone, and the growth rate is accelerating. Malware can lead to data loss, reputation loss, additional costs, and reduced performance. Highlights Protection and performance The Sophos Mobile Security antivirus app protects your Android devices without compromising Ì Privacy Advisor warns performance or battery life. The app uses up-to-the-minute intelligence from SophosLabs and the Sophos of potential privacy core antivirus engine. This means your apps are automatically scanned for malware as you install them. breaches Sophos Mobile Security’s consistent performance has earned recognition from independent testing agencies including AV-Test. Ì Security Advisor gives tips to improve device Malware protection security Our Sophos Mobile Security antivirus app protects your Android devices with proactive identification of malware. Your apps are automatically scanned for malware as you install them. Sophos includes protection Ì Loss and Theft for PUAs and low-reputation apps—new apps that have no known history and may pose a threat. PUAs Protection include adware, rootkits, diallers, and any association the app may have to previous malicious behaviour such as a certificate that has been compromised. Ì App Protection with additional passwords for Web protection sensitive apps Surf securely on the internet from your Android device. Sophos Mobile Security checks all websites against a Ì Spam Filter SophosLabs database for known malicious sites and prevents users from accessing them. -

What Is the Impact of Mobile Telephony on Economic Growth?
What is the impact of mobile telephony on economic growth? A Report for the GSM Association November 2012 Contents Foreword 1 The impact of mobile telephony on economic growth: key findings 2 What is the impact of mobile telephony on economic growth? 3 Appendix A 3G penetration and economic growth 11 Appendix B Mobile data usage and economic growth 16 Appendix C Mobile telephony and productivity in developing markets 20 Important Notice from Deloitte This report (the “Report”) has been prepared by Deloitte LLP (“Deloitte”) for the GSM Association (‘GSMA’) in accordance with the contract with them dated July 1st 2011 plus two change orders dated October 3rd 2011 and March 26th 2012 (“the Contract”) and on the basis of the scope and limitations set out below. The Report has been prepared solely for the purposes of assessing the impact of mobile services on GDP growth and productivity, as set out in the Contract. It should not be used for any other purpose or in any other context, and Deloitte accepts no responsibility for its use in either regard. The Report is provided exclusively for the GSMA’s use under the terms of the Contract. No party other than the GSMA is entitled to rely on the Report for any purpose whatsoever and Deloitte accepts no responsibility or liability or duty of care to any party other than the GSMA in respect of the Report or any of its contents. As set out in the Contract, the scope of our work has been limited by the time, information and explanations made available to us. -

Total Defense Mobile Security
USER'S GUIDE Total Defense Mobile Security Total Defense Mobile Security User's Guide Publication date 2015.04.09 Copyright© 2015 Total Defense Mobile Security Legal Notice All rights reserved. No part of this book may be reproduced or transmitted in any form or by any means, electronic or mechanical, including photocopying, recording, or by any information storage and retrieval system, without written permission from an authorized representative of Total Defense. The inclusion of brief quotations in reviews may be possible only with the mention of the quoted source. The content can not be modified in any way. Warning and Disclaimer. This product and its documentation are protected by copyright. The information in this document is provided on an “as is” basis, without warranty. Although every precaution has been taken in the preparation of this document, the authors will not have any liability to any person or entity with respect to any loss or damage caused or alleged to be caused directly or indirectly by the information contained in this work. This book contains links to third-party Websites that are not under the control of Total Defense, therefore Total Defense is not responsible for the content of any linked site. If you access a third-party website listed in this document, you will do so at your own risk. Total Defense provides these links only as a convenience, and the inclusion of the link does not imply that Total Defense endorses or accepts any responsibility for the content of the third-party site. Trademarks. Trademark names may appear in this book. -
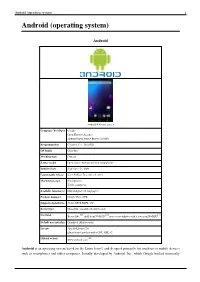
Android (Operating System) 1 Android (Operating System)
Android (operating system) 1 Android (operating system) Android Android 4.4 home screen Company / developer Google Open Handset Alliance Android Open Source Project (AOSP) Programmed in C (core), C++, Java (UI) OS family Unix-like Working state Current Source model Open source with proprietary components Initial release September 23, 2008 Latest stable release 4.4.2 KitKat / December 9, 2013 Marketing target Smartphones Tablet computers Available language(s) Multi-lingual (46 languages) Package manager Google Play, APK Supported platforms 32-bit ARM, MIPS, x86 Kernel type Monolithic (modified Linux kernel) [1] [2] [3] Userland Bionic libc, shell from NetBSD, native core utilities with a few from NetBSD Default user interface Graphical (Multi-touch) License Apache License 2.0 Linux kernel patches under GNU GPL v2 [4] Official website www.android.com Android is an operating system based on the Linux kernel, and designed primarily for touchscreen mobile devices such as smartphones and tablet computers. Initially developed by Android, Inc., which Google backed financially Android (operating system) 2 and later bought in 2005, Android was unveiled in 2007 along with the founding of the Open Handset Alliance: a consortium of hardware, software, and telecommunication companies devoted to advancing open standards for mobile devices. The first publicly available smartphone running Android, the HTC Dream, was released on October 22, 2008. The user interface of Android is based on direct manipulation, using touch inputs that loosely correspond to real-world actions, like swiping, tapping, pinching and reverse pinching to manipulate on-screen objects. Internal hardware such as accelerometers, gyroscopes and proximity sensors are used by some applications to respond to additional user actions, for example adjusting the screen from portrait to landscape depending on how the device is oriented. -
Mobile Security Companion to the CIS Critical Security Controls (Version 6)
Mobile Security Companion to the CIS Critical Security Controls (Version 6) 1 Mobile Security Companion to the CIS Critical Security Controls (Version 6) Introduction ................................................................................................................................................................................................................................................................. 3 Description ................................................................................................................................................................................................................................................................... 5 CIS Critical Security Controls (Version 6): Mobile Security .................................................................................................................................................................... 5 2 Introduction Mobile devices are starting to replace laptops for regular business use. Organizations are building or porting their applications to mobile platforms, so users are increasingly accessing the same data with mobile as with their laptops. Also, organizations have increasingly implemented Bring Your Own Device (BYOD) policies to manage this trend. However, many organizations have been struggling with the increase of personal mobile devices, and don’t fully understand the security risks they may bring. There are concerns that their compact size makes them easy to lose, that they run newer operating systems that don’t -
Securing and Managing Wearables in the Enterprise
White Paper: Securing and Managing Wearables in the Enterprise Streamline deployment and protect smartwatch data with Samsung Knox Configure White Paper: Securing and Managing Wearables in the Enterprise 2 Introduction: Smartwatches in the Enterprise As the wearable device market heats up, wrist-worn devices Industries as varied as healthcare, such as smartwatches are leading the pack. According to CCS Insight, forecasts for global sales of smart wearable devices finance, energy, transportation, will grow strongly over the next five years, with the global public safety, retail and hospitality market reaching nearly $30 billion by 2023.1 are deploying smartwatches for While smartwatches for fitness and activity tracking are popular, consumer demand is only part of the equation. added business value. Enterprises are also seeing business value in wearable devices. In a report by Robert Half Technology, 81 percent of CIOs surveyed expect wearable devices like smartwatches to Samsung has been working to address these concerns and become common tools in the workplace.2 has developed the tools to make its Galaxy and Galaxy Active smartwatches customizable, easily manageable and highly secure for enterprise users. This white paper will look at how these tools address key wearable security and manageability challenges, as well as considerations for smartwatch 81% deployments. of CIOs surveyed expect wearable devices like smartwatches to become common tools in the workplace. Industries as varied as healthcare, finance, energy, transportation, public safety, retail and hospitality are deploying smartwatches for added business value, such as hands-free communication for maintenance workers, task management, as well as physical monitoring of field workers in dangerous or remote locations. -

Satellite Phone Store Presentation
SATELLITE PHONE STORE Voice, messaging and internet data anywhere on the globe SATELLITE BROADBAND SOLUTIONS GLOBAL XPRESS SYSTEMS The GX system has been designed to support global coverage and enable global mobility. The system includes the space segment and ground segment to provide complete GEO-visible earth connectivity. GX 5075 Fly-Away VSAT GX 3075 Fly-Away VSAT • Automatic antenna pointing system • Manual pointing Antenna System • High Speed portable satellite internet • High Speed portable satellite internet • Deploy anywhere in the world • Deploy anywhere in the world • Fly-Away Transport in 2 pelican boxes • Fly-Away Transport in 2 pelican boxes • Speed up to 8Mbps up / 4Mbps down • Speed up to 8Mbps up / 4Mbps down Operating in the resilient Ka-band, while integrating seamlessly with our proven L-band network, Global Xpress allows customers across aviation, maritime, enterprise and government sectors to have reliable and assured access to high-throughput communications. GLOBAL XPRESS SYSTEMS GLOBAL XPRESS AND FLEET XPRESS COVERAGE Kymeta KyWay™ Kymeta KyWay™ u7 Ku-band satellite terminals address the need for lightweight, low-profile, and high-throughput communication systems that out perform any mechanical system fixed and on-the-move making connecting nearly any vehicle, vessel, or fixed platform easier and more reliable than ever before. Kymeta KYWAY U7 8W / 16W Kymeta KyWay™ Go • Capable of transmitting • Fastest and easiest to deploy high and receiving data while speed satellite terminal on the on the move market "plug -

Threat Modeling Framework for Mobile Communication Systems
Threat modeling framework for mobile communication systems Siddharth Prakash Rao Silke Holtmanns Tuomas Aura Aalto University Nokia-Bell Labs Aalto University Espoo, Finland Espoo, Finland Espoo, Finland siddharth:rao@aalto: silke:holtmanns@nokia-bell- tuomas:aura@aalto: labs:com ABSTRACT protocols, which evolved in a more open setup, security tools avail- Due to the complex nature of mobile communication systems, most able in the public domain for the laer are now used by hackers to of the security eorts in its domain are isolated and scaered across exploit the mobile networks [9]. underlying technologies. is has resulted in an obscure view of Despite the odds, mobile communication systems have under- the overall security. In this work, we aempt to x this problem gone a fair amount of scrutiny from the security research com- by proposing a domain-specic threat modeling framework. By munity. For example, internal components of a mobile device [71, gleaning from a diverse and large body of security literature, we 74, 101], radio communication between the phone and the cell systematically organize the aacks on mobile communications into towers[37, 162], and mobile core network protocols [55, 80, 122] various tactics and techniques. Our framework is designed to model have been tested for security-critical issues. All these isolated adversarial behavior in terms of its aack phases and to be used as research eorts are scaered across underlying protocols and tech- a common taxonomy matrix. We also provide concrete examples nologies, and, it has resulted in an obscure and complex view of mo- of using the framework for modeling the aacks individually and bile communication security. -

Prospects for Improving Competition in Mobile Roaming
WIK Wissenschaftliches Institut für Kommunikationsdienste GmbH Prospects for improving competition in mobile roaming Ulrich Stumpf Paper prepared for the 29th TPRC 2001, 27 - 29 October 2001, Alexandria, Va. Prospects for improving competition in mobile roaming I Contents Abstract II 1 Introduction 1 2 Basics of international roaming 2 3 Supply-side of wholesale roaming markets 7 3.1 Small number of suppliers and high market concentration 8 3.2 Spectrum scarcity and second-mover disadvantages 9 3.3 Imperfect substitutes to wholesale roaming 12 3.4 Transparency of competitors’ IOTs 13 4 Demand-side of wholesale roaming markets 13 4.1 Lack of competitive pressure in downstream retail roaming markets 14 4.2 Customer ignorance, insufficient control over network selection, and demand externalities 17 5 Conclusions and implications for application of non-discrimination rules 21 References 23 Prospects for improving competition in mobile roaming II Abstract The ability to make international roaming calls is of increasing importance to customers. However, there are various complaints that prices of retail roaming are intransparent, rigid and at levels that are unrelated to the cost of carriage. The focus if the paper is on wholesale roaming, which is the prime determinant of retail roaming prices. The paper analyses the structural conditions of wholesale roaming markets that have impaired incentives to competition, namely (1) high combined market share of the two leading operators combined with second mover disadvantages, and (2) demand externalities associated with customer ignorance and lack of control over network selection. The paper argues that a number of developments are under way that are likely to modify this situation in the future.