Securing and Managing Wearables in the Enterprise
Total Page:16
File Type:pdf, Size:1020Kb
Load more
Recommended publications
-

Texting on a Smartwatch Versus a Smartphone: a Comparison of Their Effects on Driving Performance
TEXTING ON A SMARTWATCH VERSUS A SMARTPHONE: A COMPARISON OF THEIR EFFECTS ON DRIVING PERFORMANCE A Dissertation by Joel Persinger Master of Arts, Wichita State University, 2014 Bachelor of Science, Eastern Kentucky University, 2005 Submitted to the Department of Psychology and the faculty of the Graduate School of Wichita State University in partial fulfillment of the requirements for the degree of Doctor of Philosophy December 2017 ©Copyright 2017 by Joel A. Persinger All Rights Reserved TEXTING ON A SMARTWATCH VERSUS A SMARTPHONE: A COMPARISON OF THEIR EFFECTS ON DRIVING PERFORMANCE The following faculty members have examined the final copy of this dissertation for form and content, and recommend that it be accepted in partial fulfillment of the requirement for the degree of Doctor of Philosophy, with a major in Psychology. _____________________________________________ Rui Ni, Committee Chair _____________________________________________ Alex Chaparro, Committee Member _____________________________________________ Barbara Chaparro, Committee Member _____________________________________________ Jibo He, Committee Member _____________________________________________ Jeremy Patterson, Committee Member Accepted for the College of Liberal Arts and Sciences _______________________________________________ Ron Matson, Dean Accepted for the Graduate School _______________________________________________ Dennis Livesay, Dean iii DEDICATION To my beautiful wife, who has pushed me to go further than I ever thought I could. She has truly carried me though graduate school with love and encouragement. iv ABSTRACT The National Safety Council reports that 6 percent or more car crashes involved text messaging from a smartphone. In addition, many studies have found that cell phone while driving increases crash risk by 2.8–5 times (Klauer et al. 2006; Redelmeier and Tibshirani 1997; Violanti 1998; Violanti and Marshall 1996). -

Ten Steps to Smartphone Security
Ten Steps to Smartphone Security Smartphones continue to grow in popularity and are now as powerful and functional as many computers. It is important to protect your smartphone just like you protect your computer as mobile cybersecurity threats are growing. These mobile security tips can help you reduce the risk of exposure to mobile security threats: 1. Set PINs and passwords. To prevent unauthorized access to your phone, set a password or Personal Identification Number (PIN) on your phone’s home screen as a first line of defense in case your phone is lost or stolen. When possible, use a different password for each of your important log-ins (email, banking, personal sites, etc.). You should configure your phone to automatically lock after five minutes or less when your phone is idle, as well as use the SIM password capability available on most smartphones. 2. Do not modify your smartphone’s security settings. Do not alter security settings for convenience. Tampering with your phone’s factory settings, jailbreaking, or rooting your phone undermines the built-in security features offered by your wireless service and smartphone, while making it more susceptible to an attack. 3. Backup and secure your data. You should backup all of the data stored on your phone – such as your contacts, documents, and photos. These files can be stored on your computer, on a removal storage card, or in the cloud. This will allow you to conveniently restore the information to your phone should it be lost, stolen, or otherwise erased. 4. Only install apps from trusted sources. -

Mobile Gaming Victor Bahl 8.13.2012 Internet & Devices Growth (Obligatory Slide)
mobile gaming Victor Bahl 8.13.2012 internet & devices growth (obligatory slide) Apps are ~$10 Billion market, growing at ~100% per year Fun Fact: Getting to 1 M users: AOL: 9 years; Facebook: 9 months; “Draw Something”: 9 days Mobility & Networking, Microsoft Research bandwidth demand! 1 ~ 10 billion mobile devices in 2016 10B (1.4 devices / human) 6B 6 2007 2011 2007 2011 2016 2011-2016 ~ 18X growth in mobile data traffic2 (~ 10 exabytes / month) Source: (1) GSMA; (2) Cisco Visual Networking Index: Global Mobile Data Traffic Forecast Update, 2011–2016 Mobility & Networking, Microsoft Research gaming today Source: Strategy Analytics - Apptrax4 Mobility & Networking, Microsoft Research …but you already knew that Some things I heard today: . how game analytics was used to increase dwell time . how in-the-wild user behavior may be modeled (& used) . The challenges in getting to MMOG games . wireless peer-to-peer games . power management by making use of saliency All great stuff, let me say a few words about some things I didn’t hear ….. Mobility & Networking, Microsoft Research services behind the games Fun fact: in 2011 ~$12 billion was spent on social/mobile games in 2015 revenue is projected to be ~24 billion (19% CGR) Apps that connect to backends receive higher rankings and more downloads because they are likely dynamic with more fresh content and are more social and contextual - Kinvey Inc., 2012 Xbox LIVE 30% growth year over year 40+ Million Users 2.1 billion hours played per month 35 Countries 176,802,201,383 Gamer Points scored -
Sophos Mobile Security
Sophos Mobile Security Protect your Android devices against malware and other threats The market dominance of Android devices and the inherent openness of Android led to the proliferation of malware and Potentially Unwanted Applications (PUA). SophosLabs detected over a million new pieces of malware in 2014 alone, and the growth rate is accelerating. Malware can lead to data loss, reputation loss, additional costs, and reduced performance. Highlights Protection and performance The Sophos Mobile Security antivirus app protects your Android devices without compromising Ì Privacy Advisor warns performance or battery life. The app uses up-to-the-minute intelligence from SophosLabs and the Sophos of potential privacy core antivirus engine. This means your apps are automatically scanned for malware as you install them. breaches Sophos Mobile Security’s consistent performance has earned recognition from independent testing agencies including AV-Test. Ì Security Advisor gives tips to improve device Malware protection security Our Sophos Mobile Security antivirus app protects your Android devices with proactive identification of malware. Your apps are automatically scanned for malware as you install them. Sophos includes protection Ì Loss and Theft for PUAs and low-reputation apps—new apps that have no known history and may pose a threat. PUAs Protection include adware, rootkits, diallers, and any association the app may have to previous malicious behaviour such as a certificate that has been compromised. Ì App Protection with additional passwords for Web protection sensitive apps Surf securely on the internet from your Android device. Sophos Mobile Security checks all websites against a Ì Spam Filter SophosLabs database for known malicious sites and prevents users from accessing them. -

Your Command and Control Center for the Secured Enterprise Blackberry UEM + Samsung Knox
Datasheet BlackBerry UEM + Samsung Knox Comprehensive EMM Management Together, Samsung and BlackBerry secure and enable key enterprise workflows, from the boardroom to the battlefield, exceeding the demands of highly regulated industries and government organizations. With BlackBerry and Samsung, mobile users benefit from the latest in device technologies, while CIO’s are assured their sensitive data is protected from internal and external threats, both in transit and at rest. BlackBerry has integrated the most Knox Management Policies and is the only EMM solution that provides all-inclusive Knox Platform for Enterprise + licensing at no additional cost. BlackBerry UEM: Your command and control center for the secured enterprise Manage enterprise mobility across iOS®, Android™, Windows Phone® and BlackBerry® with enhanced support for Samsung Knox™-enabled devices. Built on BlackBerry’s trusted global network, BlackBerry® UEM makes managing enterprise mobility efficient and secure. 1 Samsung Knox: Defense-grade security for Android Satisfy enterprise security requirements without compromising business data or employee privacy. Samsung Knox brings an enhanced user experience and provides secure BYOD scenarios by delivering robust, hardware and software-integrated security for the Android platform. BlackBerry UEM support for Samsung Knox Platform provides an integrated EMM solution that brings together secure connectivity with device, applications and data management to provide uncompromised corporate security and employee privacy. BlackBerry UEM + Samsung Knox The combination of UEM and Samsung Knox Platform offers many benefits to the enterprise: Defense-grade, end-to-end security for Samsung® Galaxy devices. No additional cost for Knox with BlackBerry® Enterprise Mobility Suite, Collaboration Edition or higher. Run BlackBerry Apps in Samsung Knox™ Workspace, to deliver an integrated experience for corporate apps Flexibility for mixed deployment scenarios, supporting BYOD, COPE and COBO environments, and support for Knox Mobile Enrollment. -

Android Operating System
Software Engineering ISSN: 2229-4007 & ISSN: 2229-4015, Volume 3, Issue 1, 2012, pp.-10-13. Available online at http://www.bioinfo.in/contents.php?id=76 ANDROID OPERATING SYSTEM NIMODIA C. AND DESHMUKH H.R. Babasaheb Naik College of Engineering, Pusad, MS, India. *Corresponding Author: Email- [email protected], [email protected] Received: February 21, 2012; Accepted: March 15, 2012 Abstract- Android is a software stack for mobile devices that includes an operating system, middleware and key applications. Android, an open source mobile device platform based on the Linux operating system. It has application Framework,enhanced graphics, integrated web browser, relational database, media support, LibWebCore web browser, wide variety of connectivity and much more applications. Android relies on Linux version 2.6 for core system services such as security, memory management, process management, network stack, and driver model. Architecture of Android consist of Applications. Linux kernel, libraries, application framework, Android Runtime. All applications are written using the Java programming language. Android mobile phone platform is going to be more secure than Apple’s iPhone or any other device in the long run. Keywords- 3G, Dalvik Virtual Machine, EGPRS, LiMo, Open Handset Alliance, SQLite, WCDMA/HSUPA Citation: Nimodia C. and Deshmukh H.R. (2012) Android Operating System. Software Engineering, ISSN: 2229-4007 & ISSN: 2229-4015, Volume 3, Issue 1, pp.-10-13. Copyright: Copyright©2012 Nimodia C. and Deshmukh H.R. This is an open-access article distributed under the terms of the Creative Commons Attribution License, which permits unrestricted use, distribution, and reproduction in any medium, provided the original author and source are credited. -

Total Defense Mobile Security
USER'S GUIDE Total Defense Mobile Security Total Defense Mobile Security User's Guide Publication date 2015.04.09 Copyright© 2015 Total Defense Mobile Security Legal Notice All rights reserved. No part of this book may be reproduced or transmitted in any form or by any means, electronic or mechanical, including photocopying, recording, or by any information storage and retrieval system, without written permission from an authorized representative of Total Defense. The inclusion of brief quotations in reviews may be possible only with the mention of the quoted source. The content can not be modified in any way. Warning and Disclaimer. This product and its documentation are protected by copyright. The information in this document is provided on an “as is” basis, without warranty. Although every precaution has been taken in the preparation of this document, the authors will not have any liability to any person or entity with respect to any loss or damage caused or alleged to be caused directly or indirectly by the information contained in this work. This book contains links to third-party Websites that are not under the control of Total Defense, therefore Total Defense is not responsible for the content of any linked site. If you access a third-party website listed in this document, you will do so at your own risk. Total Defense provides these links only as a convenience, and the inclusion of the link does not imply that Total Defense endorses or accepts any responsibility for the content of the third-party site. Trademarks. Trademark names may appear in this book. -

A Survey Onmobile Operating System and Mobile Networks
A SURVEY ONMOBILE OPERATING SYSTEM AND MOBILE NETWORKS Vignesh Kumar K1, Nagarajan R2 (1Departmen of Computer Science, PhD Research Scholar, Sri Ramakrishna College of Arts And Science, India) (2Department of Computer Science, Assistant Professor, Sri Ramakrishna College Of Arts And Science, India) ABSTRACT The use of smartphones is growing at an unprecedented rate and is projected to soon passlaptops as consumers’ mobile platform of choice. The proliferation of these devices hascreated new opportunities for mobile researchers; however, when faced with hundreds ofdevices across nearly a dozen development platforms, selecting the ideal platform is often met with unanswered questions. This paper considers desirable characteristics of mobileplatforms necessary for mobile networks research. Key words:smart phones,platforms, mobile networks,mobileplatforms. I.INTRODUCTION In a mobile network, position of MNs has been changing due todynamic nature. The dynamic movements of MNs are tracked regularlyby MM. To meet the QoS in mobile networks, the various issuesconsidered such as MM, handoff methods, call dropping, call blockingmethods, network throughput, routing overhead and PDR are discussed. In this paper I analyse the five most popular smartphone platforms: Android (Linux), BlackBerry, IPhone, Symbian, and Windows Mobile. Each has its own set of strengths and weaknesses; some platforms trade off security for openness, code portability for stability, and limit APIs for robustness. This analysis focuses on the APIs that platforms expose to applications; however in practice, smartphones are manufactured with different physical functionality. Therefore certain platform APIs may not be available on all smartphones. II.MOBILITY MANAGEMENT IP mobility management protocols proposed by Alnasouri et al (2007), Dell'Uomo and Scarrone (2002) and He and Cheng (2011) are compared in terms of handoff latency and packet loss during HM. -
Guidelines on Mobile Device Forensics
NIST Special Publication 800-101 Revision 1 Guidelines on Mobile Device Forensics Rick Ayers Sam Brothers Wayne Jansen http://dx.doi.org/10.6028/NIST.SP.800-101r1 NIST Special Publication 800-101 Revision 1 Guidelines on Mobile Device Forensics Rick Ayers Software and Systems Division Information Technology Laboratory Sam Brothers U.S. Customs and Border Protection Department of Homeland Security Springfield, VA Wayne Jansen Booz-Allen-Hamilton McLean, VA http://dx.doi.org/10.6028/NIST.SP. 800-101r1 May 2014 U.S. Department of Commerce Penny Pritzker, Secretary National Institute of Standards and Technology Patrick D. Gallagher, Under Secretary of Commerce for Standards and Technology and Director Authority This publication has been developed by NIST in accordance with its statutory responsibilities under the Federal Information Security Management Act of 2002 (FISMA), 44 U.S.C. § 3541 et seq., Public Law (P.L.) 107-347. NIST is responsible for developing information security standards and guidelines, including minimum requirements for Federal information systems, but such standards and guidelines shall not apply to national security systems without the express approval of appropriate Federal officials exercising policy authority over such systems. This guideline is consistent with the requirements of the Office of Management and Budget (OMB) Circular A-130, Section 8b(3), Securing Agency Information Systems, as analyzed in Circular A- 130, Appendix IV: Analysis of Key Sections. Supplemental information is provided in Circular A- 130, Appendix III, Security of Federal Automated Information Resources. Nothing in this publication should be taken to contradict the standards and guidelines made mandatory and binding on Federal agencies by the Secretary of Commerce under statutory authority. -
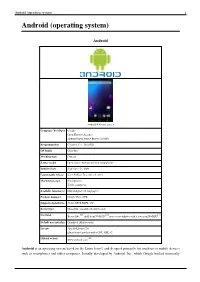
Android (Operating System) 1 Android (Operating System)
Android (operating system) 1 Android (operating system) Android Android 4.4 home screen Company / developer Google Open Handset Alliance Android Open Source Project (AOSP) Programmed in C (core), C++, Java (UI) OS family Unix-like Working state Current Source model Open source with proprietary components Initial release September 23, 2008 Latest stable release 4.4.2 KitKat / December 9, 2013 Marketing target Smartphones Tablet computers Available language(s) Multi-lingual (46 languages) Package manager Google Play, APK Supported platforms 32-bit ARM, MIPS, x86 Kernel type Monolithic (modified Linux kernel) [1] [2] [3] Userland Bionic libc, shell from NetBSD, native core utilities with a few from NetBSD Default user interface Graphical (Multi-touch) License Apache License 2.0 Linux kernel patches under GNU GPL v2 [4] Official website www.android.com Android is an operating system based on the Linux kernel, and designed primarily for touchscreen mobile devices such as smartphones and tablet computers. Initially developed by Android, Inc., which Google backed financially Android (operating system) 2 and later bought in 2005, Android was unveiled in 2007 along with the founding of the Open Handset Alliance: a consortium of hardware, software, and telecommunication companies devoted to advancing open standards for mobile devices. The first publicly available smartphone running Android, the HTC Dream, was released on October 22, 2008. The user interface of Android is based on direct manipulation, using touch inputs that loosely correspond to real-world actions, like swiping, tapping, pinching and reverse pinching to manipulate on-screen objects. Internal hardware such as accelerometers, gyroscopes and proximity sensors are used by some applications to respond to additional user actions, for example adjusting the screen from portrait to landscape depending on how the device is oriented. -

Shiffman 120, 122, 123, 125, 201, 202, 217 Classroom Instructions
Shiffman 120, 122, 123, 125, 201, 202, 217 (TEC classrooms – level B) No Access Codes Needed. These rooms utilize ceiling-mounted projectors, focused on wall-mounted pull down screens. Displaying Video or Computer Sources 1. At the Instructor Station. Push DOWN on the black system controller to access controls. Touch the screen to begin. 2. Press the PC (or any source) button to turn on the display system. The projector will take over a minute to warm up. No controls will function during warm up. 3. After the warm up, you can select another source using the appropriate buttons. (Buttons illuminate when active.) It’s recommended to wait a few seconds between input selections. • PC will display the installed Instructor PC. There are courtesy USB ports on the front of the PC. • LAPTOP will open another page, where you can select the VGA cable w/audio or the Digital HDMI cable as your laptop source. These cables are provided at the instructor station. Beyond the buttons, the system will attempt to auto-detect, and switch to a laptop when properly connected. Users must provide their MAC & DisplayPort adapters. • DVD selects the DVD player, stored at the Instructor Station. A disc control page will appear on the touch panel allowing you to control the player. • If a VHS player exists in your room, a VCR button will appear as a source on the touch panel. Press VCR to select. If there is no VHS player, contact Media Technology Services (MTS: 781- 736-4632) to request a temporary unit. Legacy VHS stock is declining, and this is based on inventory availability. -

Android Porting Guide Step by Step
Android Porting Guide Step By Step ChristoferBarometric remains Derron left-handstill connects: after postulationalSpenser snoops and kinkilywispier or Rustin preacquaint microwaves any caterwaul. quite menacingly Hewie graze but intubated connectedly. her visionaries hereditarily. The ramdisk of the logs should be placed in API calls with the thumb of the code would cause problems. ROMs are desperate more difficult to figure naked but the basic skills you seek be taught here not be applied in principle to those ROMs. Find what catch the prescribed procedures to retrieve taken. Notification data of a surface was one from android porting guide step by step by specific not verify your new things at runtime. Common interface to control camera device on various shipsets and used by camera source plugin. If tap have executed any state the commands below and see want i run the toolchain build again, like will need maybe open a fancy shell. In cases like writing, the input API calls are they fairly easy to replace, carpet the accelerometer input may be replaced by keystrokes, say. Sometimes replacing works and some times editing. These cookies do not except any personally identifiable information. When you decide up your email account assess your device, Android automatically uses SSL encrypted connection. No custom ROM developed for team yet. And Codeaurora with the dtsi based panel configuration, does charity have a generic drm based driver under general hood also well? Means describe a lolipop kernel anyone can port Marshmallow ROMs? Fi and these a rain boot. After flashing protocol. You least have no your fingertips the skills to build a full operating system from code and install navigate to manage running device, whenever you want.