New Strategies for Automated Random Testing
Total Page:16
File Type:pdf, Size:1020Kb
Load more
Recommended publications
-

Microprocessor
MICROPROCESSOR www.MPRonline.com THE REPORTINSIDER’S GUIDE TO MICROPROCESSOR HARDWARE EEMBC’S MULTIBENCH ARRIVES CPU Benchmarks: Not Just For ‘Benchmarketing’ Any More By Tom R. Halfhill {7/28/08-01} Imagine a world without measurements or statistical comparisons. Baseball fans wouldn’t fail to notice that a .300 hitter is better than a .100 hitter. But would they welcome a trade that sends the .300 hitter to Cleveland for three .100 hitters? System designers and software developers face similar quandaries when making trade-offs EEMBC’s role has evolved over the years, and Multi- with multicore processors. Even if a dual-core processor Bench is another step. Originally, EEMBC was conceived as an appears to be better than a single-core processor, how much independent entity that would create benchmark suites and better is it? Twice as good? Would a quad-core processor be certify the scores for accuracy, allowing vendors and customers four times better? Are more cores worth the additional cost, to make valid comparisons among embedded microproces- design complexity, power consumption, and programming sors. (See MPR 5/1/00-02, “EEMBC Releases First Bench- difficulty? marks.”) EEMBC still serves that role. But, as it turns out, most The Embedded Microprocessor Benchmark Consor- EEMBC members don’t openly publish their scores. Instead, tium (EEMBC) wants to help answer those questions. they disclose scores to prospective customers under an NDA or EEMBC’s MultiBench 1.0 is a new benchmark suite for use the benchmarks for internal testing and analysis. measuring the throughput of multiprocessor systems, Partly for this reason, MPR rarely cites EEMBC scores including those built with multicore processors. -

Load Testing, Benchmarking, and Application Performance Management for the Web
Published in the 2002 Computer Measurement Group (CMG) Conference, Reno, NV, Dec. 2002. LOAD TESTING, BENCHMARKING, AND APPLICATION PERFORMANCE MANAGEMENT FOR THE WEB Daniel A. Menascé Department of Computer Science and E-center of E-Business George Mason University Fairfax, VA 22030-4444 [email protected] Web-based applications are becoming mission-critical for many organizations and their performance has to be closely watched. This paper discusses three important activities in this context: load testing, benchmarking, and application performance management. Best practices for each of these activities are identified. The paper also explains how basic performance results can be used to increase the efficiency of load testing procedures. infrastructure depends on the traffic it expects to see 1. Introduction at its site. One needs to spend enough but no more than is required in the IT infrastructure. Besides, Web-based applications are becoming mission- resources need to be spent where they will generate critical to most private and governmental the most benefit. For example, one should not organizations. The ever-increasing number of upgrade the Web servers if most of the delay is in computers connected to the Internet and the fast the database server. So, in order to maximize the growing number of Web-enabled wireless devices ROI, one needs to know when and how to upgrade create incentives for companies to invest in Web- the IT infrastructure. In other words, not spending at based infrastructures and the associated personnel the right time and spending at the wrong place will to maintain them. By establishing a Web presence, a reduce the cost-benefit of the investment. -

Overview of the SPEC Benchmarks
9 Overview of the SPEC Benchmarks Kaivalya M. Dixit IBM Corporation “The reputation of current benchmarketing claims regarding system performance is on par with the promises made by politicians during elections.” Standard Performance Evaluation Corporation (SPEC) was founded in October, 1988, by Apollo, Hewlett-Packard,MIPS Computer Systems and SUN Microsystems in cooperation with E. E. Times. SPEC is a nonprofit consortium of 22 major computer vendors whose common goals are “to provide the industry with a realistic yardstick to measure the performance of advanced computer systems” and to educate consumers about the performance of vendors’ products. SPEC creates, maintains, distributes, and endorses a standardized set of application-oriented programs to be used as benchmarks. 489 490 CHAPTER 9 Overview of the SPEC Benchmarks 9.1 Historical Perspective Traditional benchmarks have failed to characterize the system performance of modern computer systems. Some of those benchmarks measure component-level performance, and some of the measurements are routinely published as system performance. Historically, vendors have characterized the performances of their systems in a variety of confusing metrics. In part, the confusion is due to a lack of credible performance information, agreement, and leadership among competing vendors. Many vendors characterize system performance in millions of instructions per second (MIPS) and millions of floating-point operations per second (MFLOPS). All instructions, however, are not equal. Since CISC machine instructions usually accomplish a lot more than those of RISC machines, comparing the instructions of a CISC machine and a RISC machine is similar to comparing Latin and Greek. 9.1.1 Simple CPU Benchmarks Truth in benchmarking is an oxymoron because vendors use benchmarks for marketing purposes. -

Opportunities and Open Problems for Static and Dynamic Program Analysis Mark Harman∗, Peter O’Hearn∗ ∗Facebook London and University College London, UK
1 From Start-ups to Scale-ups: Opportunities and Open Problems for Static and Dynamic Program Analysis Mark Harman∗, Peter O’Hearn∗ ∗Facebook London and University College London, UK Abstract—This paper1 describes some of the challenges and research questions that target the most productive intersection opportunities when deploying static and dynamic analysis at we have yet witnessed: that between exciting, intellectually scale, drawing on the authors’ experience with the Infer and challenging science, and real-world deployment impact. Sapienz Technologies at Facebook, each of which started life as a research-led start-up that was subsequently deployed at scale, Many industrialists have perhaps tended to regard it unlikely impacting billions of people worldwide. that much academic work will prove relevant to their most The paper identifies open problems that have yet to receive pressing industrial concerns. On the other hand, it is not significant attention from the scientific community, yet which uncommon for academic and scientific researchers to believe have potential for profound real world impact, formulating these that most of the problems faced by industrialists are either as research questions that, we believe, are ripe for exploration and that would make excellent topics for research projects. boring, tedious or scientifically uninteresting. This sociological phenomenon has led to a great deal of miscommunication between the academic and industrial sectors. I. INTRODUCTION We hope that we can make a small contribution by focusing on the intersection of challenging and interesting scientific How do we transition research on static and dynamic problems with pressing industrial deployment needs. Our aim analysis techniques from the testing and verification research is to move the debate beyond relatively unhelpful observations communities to industrial practice? Many have asked this we have typically encountered in, for example, conference question, and others related to it. -

Evaluation of AMD EPYC
Evaluation of AMD EPYC Chris Hollowell <[email protected]> HEPiX Fall 2018, PIC Spain What is EPYC? EPYC is a new line of x86_64 server CPUs from AMD based on their Zen microarchitecture Same microarchitecture used in their Ryzen desktop processors Released June 2017 First new high performance series of server CPUs offered by AMD since 2012 Last were Piledriver-based Opterons Steamroller Opteron products cancelled AMD had focused on low power server CPUs instead x86_64 Jaguar APUs ARM-based Opteron A CPUs Many vendors are now offering EPYC-based servers, including Dell, HP and Supermicro 2 How Does EPYC Differ From Skylake-SP? Intel’s Skylake-SP Xeon x86_64 server CPU line also released in 2017 Both Skylake-SP and EPYC CPU dies manufactured using 14 nm process Skylake-SP introduced AVX512 vector instruction support in Xeon AVX512 not available in EPYC HS06 official GCC compilation options exclude autovectorization Stock SL6/7 GCC doesn’t support AVX512 Support added in GCC 4.9+ Not heavily used (yet) in HEP/NP offline computing Both have models supporting 2666 MHz DDR4 memory Skylake-SP 6 memory channels per processor 3 TB (2-socket system, extended memory models) EPYC 8 memory channels per processor 4 TB (2-socket system) 3 How Does EPYC Differ From Skylake (Cont)? Some Skylake-SP processors include built in Omnipath networking, or FPGA coprocessors Not available in EPYC Both Skylake-SP and EPYC have SMT (HT) support 2 logical cores per physical core (absent in some Xeon Bronze models) Maximum core count (per socket) Skylake-SP – 28 physical / 56 logical (Xeon Platinum 8180M) EPYC – 32 physical / 64 logical (EPYC 7601) Maximum socket count Skylake-SP – 8 (Xeon Platinum) EPYC – 2 Processor Inteconnect Skylake-SP – UltraPath Interconnect (UPI) EYPC – Infinity Fabric (IF) PCIe lanes (2-socket system) Skylake-SP – 96 EPYC – 128 (some used by SoC functionality) Same number available in single socket configuration 4 EPYC: MCM/SoC Design EPYC utilizes an SoC design Many functions normally found in motherboard chipset on the CPU SATA controllers USB controllers etc. -

An Effective Dynamic Analysis for Detecting Generalized Deadlocks
An Effective Dynamic Analysis for Detecting Generalized Deadlocks Pallavi Joshi Mayur Naik Koushik Sen EECS, UC Berkeley, CA, USA Intel Labs Berkeley, CA, USA EECS, UC Berkeley, CA, USA [email protected] [email protected] [email protected] David Gay Intel Labs Berkeley, CA, USA [email protected] ABSTRACT for a synchronization event that will never happen. Dead- We present an effective dynamic analysis for finding a broad locks are a common problem in real-world multi-threaded class of deadlocks, including the well-studied lock-only dead- programs. For instance, 6,500/198,000 (∼ 3%) of the bug locks as well as the less-studied, but no less widespread or reports in the bug database at http://bugs.sun.com for insidious, deadlocks involving condition variables. Our anal- Sun's Java products involve the keyword \deadlock" [11]. ysis consists of two stages. In the first stage, our analysis Moreover, deadlocks often occur non-deterministically, un- observes a multi-threaded program execution and generates der very specific thread schedules, making them harder to a simple multi-threaded program, called a trace program, detect and reproduce using conventional testing approaches. that only records operations observed during the execution Finally, extending existing multi-threaded programs or fix- that are deemed relevant to finding deadlocks. Such op- ing other concurrency bugs like races often involves intro- erations include lock acquire and release, wait and notify, ducing new synchronization, which, in turn, can introduce thread start and join, and change of values of user-identified new deadlocks. Therefore, deadlock detection tools are im- synchronization predicates associated with condition vari- portant for developing and testing multi-threaded programs. -
BOOM): an Industry- Competitive, Synthesizable, Parameterized RISC-V Processor
The Berkeley Out-of-Order Machine (BOOM): An Industry- Competitive, Synthesizable, Parameterized RISC-V Processor Christopher Celio David A. Patterson Krste Asanović Electrical Engineering and Computer Sciences University of California at Berkeley Technical Report No. UCB/EECS-2015-167 http://www.eecs.berkeley.edu/Pubs/TechRpts/2015/EECS-2015-167.html June 13, 2015 Copyright © 2015, by the author(s). All rights reserved. Permission to make digital or hard copies of all or part of this work for personal or classroom use is granted without fee provided that copies are not made or distributed for profit or commercial advantage and that copies bear this notice and the full citation on the first page. To copy otherwise, to republish, to post on servers or to redistribute to lists, requires prior specific permission. The Berkeley Out-of-Order Machine (BOOM): An Industry-Competitive, Synthesizable, Parameterized RISC-V Processor Christopher Celio, David Patterson, and Krste Asanovic´ University of California, Berkeley, California 94720–1770 [email protected] BOOM is a work-in-progress. Results shown are prelimi- nary and subject to change as of 2015 June. I$ L1 D$ (32k) L2 data 1. The Berkeley Out-of-Order Machine BOOM is a synthesizable, parameterized, superscalar out- exe of-order RISC-V core designed to serve as the prototypical baseline processor for future micro-architectural studies of uncore regfile out-of-order processors. Our goal is to provide a readable, issue open-source implementation for use in education, research, exe and industry. uncore BOOM is written in roughly 9,000 lines of the hardware L2 data (256k) construction language Chisel. -

A Randomized Dynamic Program Analysis Technique for Detecting Real Deadlocks
A Randomized Dynamic Program Analysis Technique for Detecting Real Deadlocks Pallavi Joshi Chang-Seo Park Mayur Naik Koushik Sen Intel Research, Berkeley, USA EECS Department, UC Berkeley, USA [email protected] {pallavi,parkcs,ksen}@cs.berkeley.edu Abstract cipline followed by the parent software and this sometimes results We present a novel dynamic analysis technique that finds real dead- in deadlock bugs [17]. locks in multi-threaded programs. Our technique runs in two stages. Deadlocks are often difficult to find during the testing phase In the first stage, we use an imprecise dynamic analysis technique because they happen under very specific thread schedules. Coming to find potential deadlocks in a multi-threaded program by observ- up with these subtle thread schedules through stress testing or ing an execution of the program. In the second stage, we control random testing is often difficult. Model checking [15, 11, 7, 14, 6] a random thread scheduler to create the potential deadlocks with removes these limitations of testing by systematically exploring high probability. Unlike other dynamic analysis techniques, our ap- all thread schedules. However, model checking fails to scale for proach has the advantage that it does not give any false warnings. large multi-threaded programs due to the exponential increase in We have implemented the technique in a prototype tool for Java, the number of thread schedules with execution length. and have experimented on a number of large multi-threaded Java Several program analysis techniques, both static [19, 10, 2, 9, programs. We report a number of previously known and unknown 27, 29, 21] and dynamic [12, 13, 4, 1], have been developed to de- real deadlocks that were found in these benchmarks. -
Specfp Benchmark Disclosure
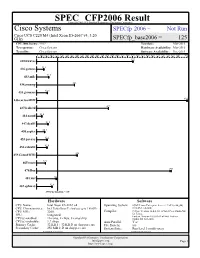
SPEC CFP2006 Result Copyright 2006-2016 Standard Performance Evaluation Corporation Cisco Systems SPECfp2006 = Not Run Cisco UCS C220 M4 (Intel Xeon E5-2667 v4, 3.20 GHz) SPECfp_base2006 = 125 CPU2006 license: 9019 Test date: Mar-2016 Test sponsor: Cisco Systems Hardware Availability: Mar-2016 Tested by: Cisco Systems Software Availability: Dec-2015 0 30.0 60.0 90.0 120 150 180 210 240 270 300 330 360 390 420 450 480 510 540 570 600 630 660 690 720 750 780 810 840 900 410.bwaves 572 416.gamess 43.1 433.milc 72.5 434.zeusmp 225 435.gromacs 63.4 436.cactusADM 894 437.leslie3d 427 444.namd 31.6 447.dealII 67.6 450.soplex 48.3 453.povray 62.2 454.calculix 61.6 459.GemsFDTD 242 465.tonto 52.1 470.lbm 799 481.wrf 120 482.sphinx3 91.6 SPECfp_base2006 = 125 Hardware Software CPU Name: Intel Xeon E5-2667 v4 Operating System: SUSE Linux Enterprise Server 12 SP1 (x86_64) CPU Characteristics: Intel Turbo Boost Technology up to 3.60 GHz 3.12.49-11-default CPU MHz: 3200 Compiler: C/C++: Version 16.0.0.101 of Intel C++ Studio XE for Linux; FPU: Integrated Fortran: Version 16.0.0.101 of Intel Fortran CPU(s) enabled: 16 cores, 2 chips, 8 cores/chip Studio XE for Linux CPU(s) orderable: 1,2 chips Auto Parallel: Yes Primary Cache: 32 KB I + 32 KB D on chip per core File System: xfs Secondary Cache: 256 MB I+D on chip per core System State: Run level 3 (multi-user) Continued on next page Continued on next page Standard Performance Evaluation Corporation [email protected] Page 1 http://www.spec.org/ SPEC CFP2006 Result Copyright 2006-2016 Standard Performance -

A Real-World Benchmark Model for Testing Concurrent Real-Time Systems in the Automotive Domain
A Real-World Benchmark Model for Testing Concurrent Real-Time Systems in the Automotive Domain Jan Peleska1, Artur Honisch3, Florian Lapschies1, Helge L¨oding2, Hermann Schmid3, Peer Smuda3, Elena Vorobev1, and Cornelia Zahlten2 1 Department of Mathematics and Computer Science University of Bremen, Germany fjp,florian,[email protected] 2 Verified Systems International GmbH, Bremen, Germany fhloeding,cmzg@verified.de 3 Daimler AG, Stuttgart, Germany fartur.honisch,hermann.s.schmid,[email protected] Abstract. In this paper we present a model for automotive system tests of functionality related to turn indicator lights. The model cov- ers the complete functionality available in Mercedes Benz vehicles, com- prising turn indication, varieties of emergency flashing, crash flashing, theft flashing and open/close flashing, as well as configuration-dependent variants. It is represented in UML2 and associated with a synchronous real-time systems semantics conforming to Harel's original Statecharts interpretation. We describe the underlying methodological concepts of the tool used for automated model-based test generation, which was developed by Verified Systems International GmbH in cooperation with Daimler and the University of Bremen. A test suite is described as initial reference for future competing solutions. The model is made available in several file formats, so that it can be loaded into existing CASE tools or test generators. It has been originally developed and applied by Daimler for automatically deriving test cases, concrete test data and test proce- dures executing these test cases in Daimler's hardware-in-the-loop sys- tem testing environment. In 2011 Daimler decided to allow publication of this model with the objective to serve as a "real-world" benchmark supporting research of model based testing. -

Optimistic Hybrid Analysis: Accelerating Dynamic Analysis Through Predicated Static Analysis
Optimistic Hybrid Analysis: Accelerating Dynamic Analysis through Predicated Static Analysis David Devecsery Peter M. Chen University of Michigan University of Michigan [email protected] [email protected] Jason Flinn Satish Narayanasamy University of Michigan University of Michigan [email protected] [email protected] CCS Concepts • Theory of computation → Program anal- apply a much more precise, but unsound, static analysis that ysis; • Software and its engineering → Dynamic analysis; assumes these invariants hold true. Finally, we run the result- Software reliability; Software safety; Software testing and de- ing dynamic analysis speculatively while verifying whether bugging; the assumed invariants hold true during that particular exe- cution; if not, the program is reexecuted with a traditional ACM Reference Format: David Devecsery, Peter M. Chen, Jason Flinn, and Satish Narayanasamy. hybrid analysis. 2018. Optimistic Hybrid Analysis: Accelerating Dynamic Analysis Optimistic hybrid analysis is as precise and sound as tradi- through Predicated Static Analysis. In ASPLOS ’18: 2018 Architec- tional dynamic analysis, but is typically much faster because tural Support for Programming Languages and Operating Systems, (1) unsound static analysis can speed up dynamic analysis March 24–28, 2018, Williamsburg, VA, USA. ACM, New York, NY, much more than sound static analysis can and (2) verifi- USA, 15 pages. https://doi.org/10.1145/3173162.3177153 cations rarely fail. We apply optimistic hybrid analysis to race detection and program slicing and achieve 1.8x over Abstract a state-of-the-art race detector (FastTrack) optimized with Dynamic analysis tools, such as those that detect data-races, traditional hybrid analysis and 8.3x over a hybrid backward verify memory safety, and identify information flow, have be- slicer (Giri). -

Decoupling Dynamic Program Analysis from Execution in Virtual Environments
Decoupling dynamic program analysis from execution in virtual environments Jim Chow Tal Garfinkel Peter M. Chen VMware Abstract 40x [18, 26], rendering many production workloads un- Analyzing the behavior of running programs has a wide usable. In non-production settings, such as program de- variety of compelling applications, from intrusion detec- velopment or quality assurance, this overhead may dis- tion and prevention to bug discovery. Unfortunately, the suade use in longer, more realistic tests. Further, the per- high runtime overheads imposed by complex analysis formance perturbations introduced by these analyses can techniques makes their deployment impractical in most lead to Heisenberg effects, where the phenomena under settings. We present a virtual machine based architec- observation is changed or lost due to the measurement ture called Aftersight ameliorates this, providing a flex- itself [25]. ible and practical way to run heavyweight analyses on We describe a system called Aftersight that overcomes production workloads. these limitations via an approach called decoupled analy- Aftersight decouples analysis from normal execution sis. Decoupled analysis moves analysis off the computer by logging nondeterministic VM inputs and replaying that is executing the main workload by separating execu- them on a separate analysis platform. VM output can tion and analysis into two tasks: recording, where system be gated on the results of an analysis for intrusion pre- execution is recorded in full with minimal interference, vention or analysis can run at its own pace for intrusion and analysis, where the log of the execution is replayed detection and best effort prevention. Logs can also be and analyzed. stored for later analysis offline for bug finding or foren- Aftersight is able to record program execution effi- sics, allowing analyses that would otherwise be unusable ciently using virtual machine recording and replay [4, 9, to be applied ubiquitously.