CIS 90 - Lesson 3
Total Page:16
File Type:pdf, Size:1020Kb
Load more
Recommended publications
-
Argosoft Mail Server Pro User Guide
http://www.argosoft.com Argosoft Mail Server Pro User Guide June 2002 1 Introduction Thank you for choosing Argosoft Mail Server Pro. This lightweight and extremely affordable mail server is robust, stable, easy to configure, easy to manage and is fully capable of competing head to head with any mail server on the market. It can perform all basic e-mail tasks, and much more. It is fully functional mail system, which supports most popular protocols, SMTP, POP3, Finger, and has a built-in Web server, to give users quick and easy access to their email via any Web browser, which supports HTTP 1.0 or later. The web interface can also be used to administer the mail server. While this easy to use mail server is pretty much obvious in terms of use there are few little things that even a seasoned e-mail expert may not stumble across immediately. This document is basic guide to getting started! Features • Has true support of multiple domains - you can create accounts with the same name, which belong to different domains • Supports multiple IP homes (virtual domains) • Has built in mailing list server • Has WAP interface • Allows setup of domain administrators - users who can change domain related information via the Web interface; • Filtering of mail according to IP addresses of server which attempts to relay mail to local users • ORDB and MAPS support • Supports distribution lists; • Supports auto responders; • Supports basic filters; • Unlimited message size (there is a limit of 5 Megs for freeware version); • Can listen on single IP address, rather than all addresses available on your computer; • Has built-in web server. -

Streamline the Process - a Real Life Example Yadong Zhang, Oxford Health Plans, Trumbull, CT
Streamline the Process - A Real Life Example Yadong Zhang, Oxford Health Plans, Trumbull, CT ABSTRACT This paper presents a real life example on the evolution of a A SHELL SCRIPT TO THE RESCUE monthly report application. The application uses SAS/SQLâ pass â Now you get the DBF report that needs to be sent to the through and Base SAS to develop report and email the final business user. In our case, we run SAS on a UNIX box, product to the end user. The application also archives the log and our business users are on an NT server. So we and report automatically. either FTP the report to a shared place, or if the file is small enough, we email it to the user. That's exactly INTRODUCTION what I did in the first two runs: I FTP’d the file to my PC It is common for a SAS programmer to develop reports running and emailed it as an attachment. Tedious and time on a regular basis. How do you simplify the process? How do consuming, I began to hate it the third time I did it. So I you make your program to do the 'thinking' for you? This paper called on a shell script to the rescue. will present some tips on this subject. report.sh #!/bin/ksh PROBLEM # Declare shell variables On the first day of each month, produce a report on transitional ¶PGMDIR=/project/pgms care in DBF format, using tables on an Oracleâ data warehouse. ·PROG=report ¸RPTDATE="`date '+%Y-%m-%d'`" SOLUTION ¹ADM="yzhang@exchange-server" ºMAILTO="USER1@exchange-server As always, there is more than one way to do it in SAS. -

Pipenightdreams Osgcal-Doc Mumudvb Mpg123-Alsa Tbb
pipenightdreams osgcal-doc mumudvb mpg123-alsa tbb-examples libgammu4-dbg gcc-4.1-doc snort-rules-default davical cutmp3 libevolution5.0-cil aspell-am python-gobject-doc openoffice.org-l10n-mn libc6-xen xserver-xorg trophy-data t38modem pioneers-console libnb-platform10-java libgtkglext1-ruby libboost-wave1.39-dev drgenius bfbtester libchromexvmcpro1 isdnutils-xtools ubuntuone-client openoffice.org2-math openoffice.org-l10n-lt lsb-cxx-ia32 kdeartwork-emoticons-kde4 wmpuzzle trafshow python-plplot lx-gdb link-monitor-applet libscm-dev liblog-agent-logger-perl libccrtp-doc libclass-throwable-perl kde-i18n-csb jack-jconv hamradio-menus coinor-libvol-doc msx-emulator bitbake nabi language-pack-gnome-zh libpaperg popularity-contest xracer-tools xfont-nexus opendrim-lmp-baseserver libvorbisfile-ruby liblinebreak-doc libgfcui-2.0-0c2a-dbg libblacs-mpi-dev dict-freedict-spa-eng blender-ogrexml aspell-da x11-apps openoffice.org-l10n-lv openoffice.org-l10n-nl pnmtopng libodbcinstq1 libhsqldb-java-doc libmono-addins-gui0.2-cil sg3-utils linux-backports-modules-alsa-2.6.31-19-generic yorick-yeti-gsl python-pymssql plasma-widget-cpuload mcpp gpsim-lcd cl-csv libhtml-clean-perl asterisk-dbg apt-dater-dbg libgnome-mag1-dev language-pack-gnome-yo python-crypto svn-autoreleasedeb sugar-terminal-activity mii-diag maria-doc libplexus-component-api-java-doc libhugs-hgl-bundled libchipcard-libgwenhywfar47-plugins libghc6-random-dev freefem3d ezmlm cakephp-scripts aspell-ar ara-byte not+sparc openoffice.org-l10n-nn linux-backports-modules-karmic-generic-pae -

Managing Sendmail Services in Oracle® Solaris 11.4
® Managing sendmail Services in Oracle Solaris 11.4 Part No: E61008 November 2020 Managing sendmail Services in Oracle Solaris 11.4 Part No: E61008 Copyright © 2002, 2020, Oracle and/or its affiliates. License Restrictions Warranty/Consequential Damages Disclaimer This software and related documentation are provided under a license agreement containing restrictions on use and disclosure and are protected by intellectual property laws. Except as expressly permitted in your license agreement or allowed by law, you may not use, copy, reproduce, translate, broadcast, modify, license, transmit, distribute, exhibit, perform, publish, or display any part, in any form, or by any means. Reverse engineering, disassembly, or decompilation of this software, unless required by law for interoperability, is prohibited. Warranty Disclaimer The information contained herein is subject to change without notice and is not warranted to be error-free. If you find any errors, please report them to us in writing. Restricted Rights Notice If this is software or related documentation that is delivered to the U.S. Government or anyone licensing it on behalf of the U.S. Government, then the following notice is applicable: U.S. GOVERNMENT END USERS: Oracle programs (including any operating system, integrated software, any programs embedded, installed or activated on delivered hardware, and modifications of such programs) and Oracle computer documentation or other Oracle data delivered to or accessed by U.S. Government end users are "commercial computer software" -
Servidor De Correo X Ubuntu
UNIVERSIDAD NACIONAL DEL CAAGUAZÚ FACULTAD DE CIENCIAS Y TECNOLOGÍAS Servidor de Correo X Ubuntu Responsables Marcelo Abrahan Acuña Santander Mario Manuel Moreno González Profesor: Ing. Héctor Estigarribia Ingeniería en Informática Coronel Oviedo -2016- Resumen Un servidor de correo es una aplicación informática ubicada en una página web en internet cuya función es parecida al Correo postal solo que en este caso los correos (otras veces llamados mensajes) que circulan, lo hacen a través de nuestras Redes de transmisión de datos y a diferencia del correo postal, por este medio solo se pueden enviar adjuntos de ficheros de cualquier extensión y no bultos o paquetes al viajar la información en formato electrónico. Montar un servidor de correo electrónico a base de GNU/Linux y software libre está al alcance de cualquiera, pero mientras que para el usuario corriente no compensa el esfuerzo, en el ámbito de la empresa sí es una práctica extendida por razones de privacidad y control de la información. Para montar un servidor de correo electrónico son imprescindibles diferentes elementos entre los que destaca el propio software que hará las veces de “mensajero”, lo que técnicamente se denomina como Mail Transfer Agent (MTA) o agente de transporte de correo en español. Y como no podía ser de otra forma, son varias las alternativas disponibles en el mundo del Open Source. Por eso ofrecemos un somero repaso a alguna de las más populares. Palabras clave: Servidor de Correo, Correo postal, Redes de transmisión de Datos, Control de Información, Software, Agente de transporte de Correo, Open Source. Abstract A mail server is a computer application located on a web page on the internet whose function is similar to the Post only that in this case the mails (sometimes called messages) that circulate, they do it through our Data transmission networks and Unlike postal mail, by this means only attachments of files of any extension can be sent and not packages or packages when traveling the information in electronic format. -
APT HOWTO (Obsolete Documentation)
APT HOWTO (Obsolete Documentation) Gustavo Noronha Silva <[email protected]> 1.7.6 - 2002 年 1 月 ...要要要 こ.£書/、Debian .1#ケージ管理Fー&ィJ&ィ'あK APT ."き+$い&、 Fー ザ+深く理解し&BIうこ(R4¿し&い>す。そ.目¿/、新しい Debian Fーザ.生 aRS+したJ、シス&@管理+$い&理解R深Aたい(Áう®.±助け( *Kこ(' す。Debian Fーザが3ILKサ=ー(R改NすK目¿'、Debian 7M ジェク(.たA+ù 成されました。 QQQùùùñññJJJooo Copyright © 2001, 2002, 2003, 2004 Gustavo Noronha Silva This manual is free software; you may redistribute it and/or modify it under the terms of the GNU General Public License as published by the Free Software Foundation; either version 2, or (at your option) any later version. This is distributed in the hope that it will be useful, but without any warranty; without even the implied warranty of merchantability or fitness for a particular purpose. See the GNU General Public License for more details. A copy of the GNU General Public License is available as /usr/share/common-licenses/GPL in the Debian GNU/Linux distribution or on the World Wide Web at the GNU General Public Licence. You can also obtain it by writing to the Free Software Foundation, Inc., 59 Temple Place - Suite 330, Boston, MA 02111-1307, USA. i 目目目 hhh 1 //はじじじめAA+++ 1 2 ÇÇÇ%%%¿¿¿***設設設¡¡¡ 3 2.1 /etc/apt/sources.list ファイル .............................3 2.2 Mーカル'. APT .1いè ...............................4 2.3 sources.list 5ァ イ K+記述す 9き最Á*?Iーサ イ(.決¡: netselect, netselect-apt........................................5 2.4 sources.list ファイル+ CD-ROM R追加する .....................6 3 111##ッケケケーーージジジ...管管管理理理 9 3.1 利用可能*パッケージ.K覧Rf新する .......................9 3.2 パッケージ.インストーK ...............................9 3.3 パッケージ.ú! .................................... -
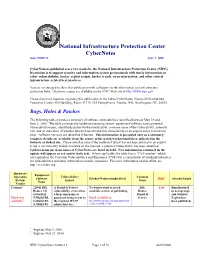
National Infrastructure Protection Center Cybernotes Issue #2000-11 June 5, 2000
National Infrastructure Protection Center CyberNotes Issue #2000-11 June 5, 2000 CyberNotes is published every two weeks by the National Infrastructure Protection Center (NIPC). Its mission is to support security and information system professionals with timely information on cyber vulnerabilities, hacker exploit scripts, hacker trends, virus information, and other critical infrastructure-related best practices. You are encouraged to share this publication with colleagues in the information and infrastructure protection field. Electronic copies are available on the NIPC Web site at http://www.nipc.gov. Please direct any inquiries regarding this publication to the Editor-CyberNotes, National Infrastructure Protection Center, FBI Building, Room 11719, 935 Pennsylvania Avenue, NW, Washington, DC, 20535. Bugs, Holes & Patches The following table provides a summary of software vulnerabilities identified between May 18 and June 2, 2000. The table provides the hardware/operating system, equipment/software name, potential vulnerability/impact, identified patches/workarounds/alerts, common name of the vulnerability, potential risk, and an indication of whether attacks have utilized this vulnerability or an exploit script is known to exist. Software versions are identified if known. This information is presented only as a summary; complete details are available from the source of the patch/workaround/alert, indicated in the footnote or linked site. Please note that even if the method of attack has not been utilized or an exploit script is not currently widely available on the Internet, a potential vulnerability has been identified. Updates from previous issues of CyberNotes are listed in bold. New information contained in the update will appear as red and/or italic text. -

Model Checking an Entire Linux Distribution for Security Violations
Model Checking An Entire Linux Distribution for Security Violations by Benjamin W. Schwarz Research Project Submitted to the Department of Electrical Engineering and Computer Sciences, University of California at Berkeley, in partial satisfaction of the requirements for the degree of Master of Science, Plan II. Approval for the Report and Comprehensive Examination: Committee: David Wagner Research Advisor (Date) * * * * * * * Doug Tygar Second Reader (Date) Abstract Software model checking has become a popular tool for verifying pro- grams’ behavior. Recent results suggest that it is viable for finding and erad- icating security bugs quickly. However, even state-of-the-art model checkers are limited in use when they report an overwhelming number of false positives, or when their lengthy running time dwarfs other software development pro- cesses. In this paper we report our experiences with software model checking for security properties on an extremely large scale—an entire Linux distribu- tion consisting of 839 packages and 60 million lines of code. To date, we have discovered 108 exploitable bugs. Our results indicate that model checking can be both a feasible and integral part of the software development process. 2 Contents 1 Introduction 5 2 The MOPS Model Checker 6 2.1 Specification of Security Properties . 7 2.2 Scalability . 8 2.3 Error Reporting . 8 2.4 Efficient Model Checking with Pattern Variables . 9 2.4.1 Current implementation . 9 2.4.2 More Efficient Algorithms . 10 2.5 User Interface for Error Reporting . 11 2.6 Resource Usage . 12 3 Checking Security Properties 12 3.1 TOCTTOU . 13 3.2 A Standard File Descriptor Attack . -

Sending and Reading Email
Sending and Reading Email Get familiar with mailx, alpine, mutt, and mail. Creating a Signature file Automatically forwarding incoming messages Announcing an absence with vocation Configuring and managing email with procmail Using the Email An email message is identified by a sender and a receipt, both of which appear as headers in the message. mailx is a mail user agent for moving mails between users on the same host. Depending upon whether both sender and receipt are on the same host, an email address can take the following forms: 1. henry – user henry is on the same host 2. henry@saturn – henry is on a different host 3. [email protected] –henryis on the internet Internet Email Handling (1/3) Internet mail handling requires the works of at least three agencies: 1. Mail user agent –for reading the mailbox and sending mail, like mailx and pine. 2. Mail transport agent –for transporting mail between machines 3. Mail delivery agent –for delivering mail to the recipients’ mailboxes. MUA reads incoming mail from the mailbox and hands over outgoing mail to the MTA. MTA sends and receives mail. At the sending end, it identifies the recipient’s address and delivers the message directly to the MTA at the other end. At the receiving end, the MTA passes on mail to MDA. Internet Email Handling (2/3) MTA’s sending and receiving functions are handled universally by the simple mail transfer protocol (SMTP). The MTA doesn’t deliver mail. MDA does the delivery, like procmail. If the user’s host connects to the mail server intermittently, the user typically uses his ISP’s facilities to handle his mail. -

Linux Network Administrators Guide Remote Systems
Chapter 16. ManagingTaylor UUCP UUCP was designed in the late seventies by Mike Lesk at AT&T Bell Laboratories to provide a simple dialup network over public telephone lines. Despite the popularity of dialup PPP and SLIP connections to the Internet, many people who want to have email and Usenet News on their home machine still use UUCP because it is often cheaper, especially in countries where Internet users have to pay by the minute for local telephone calls, or where they do not have a local ISP and must pay long distance toll rates to connect. Although there are many implementations of UUCP running on a wide variety of hardware platforms and operating systems, overall, they are highly compatible. However, as with most software that has somehow become standard over the years, there is no UUCP that one would call the UUCP. It has undergone a steady evolution since the first version was implemented in 1976. Currently, there are two major species that differ mainly in their hardware support and configuration. Of these two, various implementations exist, each varying slightly from its siblings. One species is known as Version 2 UUCP, which dates back to a 1977 implementation by Mike Lesk, David A. Novitz, and Greg Chesson. Although it is fairly old, it is still frequently used. Recent implementations of Version 2 provide much of the comfort that the newer UUCP species do. The second species was developed in 1983 and is commonly referred to as BNU (Basic Networking Utilities) or HoneyDanBer UUCP. The latter name is derived from the authors' names (P. -

UNIX System Servicesuser's Guide
z/OS Version 2 Release 3 UNIX System Services User's Guide IBM SA23-2279-30 Note Before using this information and the product it supports, read the information in “Notices” on page 321. This edition applies to Version 2 Release 3 of z/OS (5650-ZOS) and to all subsequent releases and modifications until otherwise indicated in new editions. Last updated: 2019-02-16 © Copyright International Business Machines Corporation 1996, 2018. US Government Users Restricted Rights – Use, duplication or disclosure restricted by GSA ADP Schedule Contract with IBM Corp. Contents List of Figures...................................................................................................... xv List of Tables......................................................................................................xvii About this document...........................................................................................xix Who should use z/OS UNIX System Services User's Guide?....................................................................xix What is in z/OS UNIX System Services User's Guide?........................................................................ xix Tasks that can be performed in more than one environment.............................................................xix z/OS information.................................................................................................................................. xix How to send your comments to IBM.....................................................................xxi If you -

Interview with Mary Ann Horton RIK FARROWPROGRAMMING
Interview with Mary Ann Horton RIK FARROWPROGRAMMING Mary Ann Horton has been a met Mary Ann Horton at USENIX ATC ’19 in Seattle. I didn’t know who UNIX developer and sysadmin she was, but somehow discovered that she worked on the control systems since 1977. She contributed to for the grid in the San Diego area, and we exchanged email addresses so Berkeley UNIX, creating the I we could continue the conversation. Later, I read her Wikipedia page [1] and first email attachments and enhancing vi. Her PhD dissertation at Berkeley learned much more about her. led to IDE editors that check your program for Rik Farrow: You have been working with UNIX since its earliest days. errors. While at Bell Labs, she led the UUCP Mapping Project and brought .com domains Mary Ann Horton: I fell in love with UNIX earning my master’s degree at Wisconsin in to UUCP email. She led the growth of Usenet, 1977, but my big break came in 1978 when I transferred to Berkeley for my PhD. We got a an early social media network, in the early VAX, initially with VMS, but quickly changed to UNIX 32/V. There were many amazing grad 1980s. Her EMS email system allowed email students contributing tools to BSD, and it was a treat to get to be part of this effort. It seemed addressing by database query. As a transgender like about half the code was written by Bill Joy, including vi. I got to enhance vi, nurture activist in the 1990s, she convinced Lucent it, and port it to all sorts of UNIX clones.