The Future of Extremism and Extremist Narratives in America
Total Page:16
File Type:pdf, Size:1020Kb
Load more
Recommended publications
-

The Whistleno. 96, October 2018
“All that is needed for evil to prosper is for people of good will to do nothing”—Edmund Burke The Whistle No. 96, October 2018 Newsletter of Whistleblowers Australia (ISSN 2205-0299) Reality Winner, imprisoned whistleblower Articles National Appreciation Day. The Senate resolu- tion encourages US federal agencies to Whistleblower Day inform IN 1777, ten sailors and marines from employees, contractors working on the ship Warren petitioned the US behalf of United States taxpayers, Continental Congress — the precursor and members of the public about the of the US Congress — to take action legal rights of citizens of the United against their commander, the first States to “blow the whistle” by commodore of the US Navy, who they honest and good faith reporting of alleged was war profiteering and misconduct, fraud, misdemeanors, mistreating prisoners of war. Congress or other crimes to the appropriate supported them, including when the authorities. commander took them to court. On July 30 the following year, the The resolution also acknowledges the US Continental Congress unani- After Whistleblowers Australia formed contributions whistleblowers have mously: in 1991, we were in contact with the made, at their own personal risk, NWC to support Australian whistle- “combating waste, fraud, abuse.” Resolved, That it is the duty of all blowers from the late 1980s, those who The US Congress has not yet desig- persons in the service of the United had forced the 1989 Queensland nated July 30 as National Whistle- States, as well as all other the in- Fitzgerald Inquiry and ones who later blower Day on a permanent basis. -

In the United States Court of Appeals for The
Case: 17-15458 Date Filed: 01/31/2018 Page: 1 of 5 IN THE UNITED STATES COURT OF APPEALS FOR THE ELEVENTH CIRCUIT _______________________ No. 17-15458 _______________________ UNITED STATES OF AMERICA, Plaintiff-Appellee, vs. REALITY LEIGH WINNER, Defendant-Appellant _______________________ On Appeal from the United States District Court for the Southern District of Georgia _______________________ BEFORE: MARTIN, JORDAN, and ROSENBAUM, Circuit Judges. PER CURIAM: Reality Winner, who is charged with violating 18 U.S.C. § 793(e) by allegedly providing a classified top-secret government document to a news organization without authorization, appeals from the district court’s pretrial detention order. The district court found by a preponderance of the evidence that no condition, or combination of conditions, would reasonably assure Ms. Winner’s presence at trial, which is currently scheduled for March of 2018. See 18 U.S.C. § Case: 17-15458 Date Filed: 01/31/2018 Page: 2 of 5 3142(e)(1). See also United States v. Medina, 775 F.3d 1398, 1402 (11th Cir. 1985) (holding that risk of flight under the Bail Reform Act is determined under a preponderance of the evidence standard). Generally speaking, cases arising under the Bail Reform Act present mixed questions of law and fact which receive plenary review on appeal, but purely factual findings are reviewed only for clear error. See United States v. King, 849 F.2d 485, 487 (11th Cir. 1988); United States v. Hurtado, 779 F.2d 1465, 1471-72 (11th Cir. 1985). As explained in Hurtado, conclusions concerning the nature and circumstances of the offense and the weight of the evidence under § 3142(g)(1)- (2), as well as the factors set forth in § 3142(c)(1)(B), require the exercise of judgment and are reviewed de novo. -

Informational Materials
Received by NSD/FARA Registration Unit 06/15/2021 8:00:44 AM 06/14/21 Monday This material is distributed by Ghebi LLC on behalf of Federal State Unitary Enterprise Rossiya Segodnya International Information Agency, and additional information is on file with the Department of Justice, Washington, District of Columbia. ‘Summer of Winston Smith’: Car Attack Kills One, Wounds Three at Minneapolis Police Killing Vigil by Morgan Artvukhina At a Sunday protest on behalf of a black man killed by federal police in Minneapolis earlier this month, a car plowed into the crowd, killing one woman and wounding two others. The incident comes more than a year after George Floyd’s murder in the same city and just days after the city tried to dismantle a monument to his memory. Protesters had blocked off an intersection in Minneapolis, Minnesota’s Uptown district on Sunday to draw attention to the police killing of 32-year-old Winston Smith when a speeding SUV slammed into a parked car, sending it flying into a group of demonstrators. One woman, 31-year-old Deona Erickson, died at the hospital after being slammed into a light post by the impact; three others were also hospitalized with less serious injuries, according to local media. The driver of the car was taken to the hospital as well, having reportedly attempted to flee the scene, but was held until police arrived by other protesters, who detained him. Deona Marie. She positioned her vehicle in a way that would protect other protestors in case anyone would attempt to ram into them. -
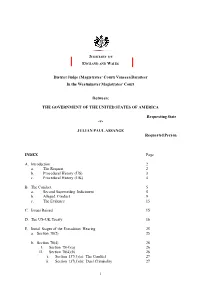
Julian Assange Judgment
JUDICIARY OF ENGLAND AND WALES District Judge (Magistrates’ Court) Vanessa Baraitser In the Westminster Magistrates’ Court Between: THE GOVERNMENT OF THE UNITED STATES OF AMERICA Requesting State -v- JULIAN PAUL ASSANGE Requested Person INDEX Page A. Introduction 2 a. The Request 2 b. Procedural History (US) 3 c. Procedural History (UK) 4 B. The Conduct 5 a. Second Superseding Indictment 5 b. Alleged Conduct 9 c. The Evidence 15 C. Issues Raised 15 D. The US-UK Treaty 16 E. Initial Stages of the Extradition Hearing 25 a. Section 78(2) 25 b. Section 78(4) 26 I. Section 78(4)(a) 26 II. Section 78(4)(b) 26 i. Section 137(3)(a): The Conduct 27 ii. Section 137(3)(b): Dual Criminality 27 1 The first strand (count 2) 33 The second strand (counts 3-14,1,18) and Article 10 34 The third strand (counts 15-17, 1) and Article 10 43 The right to truth/ Necessity 50 iii. Section 137(3)(c): maximum sentence requirement 53 F. Bars to Extradition 53 a. Section 81 (Extraneous Considerations) 53 I. Section 81(a) 55 II. Section 81(b) 69 b. Section 82 (Passage of Time) 71 G. Human Rights 76 a. Article 6 84 b. Article 7 82 c. Article 10 88 H. Health – Section 91 92 a. Prison Conditions 93 I. Pre-Trial 93 II. Post-Trial 98 b. Psychiatric Evidence 101 I. The defence medical evidence 101 II. The US medical evidence 105 III. Findings on the medical evidence 108 c. The Turner Criteria 111 I. -

Reality Gets a Harsh Sentence
REALITY GETS A HARSH SENTENCE With Update Below! As many of you may already know, this morning was the sentencing for Reality Winner. She was sentenced to 63 months of incarcerati on and three years of supervised release upon completion of her term. The supervised release term is rather standard. She will be housed at the Federal Medical Center, Carswell in Fort Worth, Texas. The stated reason was because she is bulimic, but it seems more like a nod to her, and her family, who requested a Texas posting so they would be near. There is no pecuniary fine. I have not seen the official sentencing order yet, but have little to no doubt she will be credited with the time served in pre-trial detention since her arrest on June 3, 2017; i.e. nearly 15 months. So, assuming that, she should be released in about 4 years. Okay, that is the hard nuts and bolts of Ms. Winner’s sentencing. If you want some more background, please see our old friend Kevin Gosztola at Shadowproof, who has been covering all the Reality Winner court appearances. All that said, let me address a couple of things. First, the sentence was not unexpected, indeed it was stipulated to in the plea agreement Ms. Winner both signed and allocuted to in open court. While the court technically “could” have deviated downward, there was little to no chance it would given the plea language. Anybody shocked by today’s sentencing has not been paying attention. Secondly, the government did not “block” Winner’s defenses. -

Download Your Manual
From The Guv’nor’ Jim Marshall* ENGLISH I would like to personally congratulate you on choosing the all-valve, 100 Watt, JVM410HJS Joe Satriani Signature amplifi er. Joe worked very closely with my top R&D chap, Santiago Alvarez, on this amp for a number of years and the result of this collaboration is fantastic. As is the fact that Joe has quite literally road-tested the prototypes on tour all over the world and also in the recording studio. I’ve followed Joe’s career ever since his self-fi nanced debut album, Not of This Earth, came out in the mid ‘80s. I’m delighted that he recorded many of his classic instrumentals using Marshall amps. In fact, some of the sounds the JVM410HJS’s modes are capable of pay homage to many of those great old amps he relied on – from JMPs to the 30th Anniversary 6100 that he used for so many years. Like Joe, I’m extremely proud of the amp that he and Santiago have developed. I’d like to take this opportunity to wish you every success with your new Marshall JVM410HJS. I’m sure it will bring you countless hours of playing pleasure. Welcome to the Marshall family. Yours Sincerely, Jim Marshall *Footnote: this intro was the fi nal one Jim worked on before making Heaven a much louder place! Here’s what Joe had to say on hearing of Jim’s passing: 1 ENGLISH First and foremost, thanks for getting ones and eventually, by the end of that tour, I’d I was playing through mine and we both realized as a result of the JVM on the “Get Your Buzz On” realized that using a distortion box into a clean that our amps weren’t up to it. -

The Pas Educators' Companion
THE PAS EDUCATORS’ COMPANION Volume I Spring 2015 A resource from the PERCUSSIVE ARTS SOCIETY EDUCATION COMMITTEE THE PAS EDUCATORS’ Volume I COMPANION Spring 2015 The PAS Educators’ Companion is a publication of the Percussive Arts Society focusing on providing percussion education resources to the music education community. THE COMPANION STAFF Paul Buyer James Corcoran Pete DeSalvo Jonathan Latta Brian Nozny Josh Torres Michael Sammons Ben Stiers GRAPHIC DESIGN Adrian Valderrama PAS EXECUTIVE COMMITTEE Julie Hill, President Brian Zator, President-elect George Barrett, First Vice President Paul Buyer, Second Vice President Chris Hanning, Secretary John R. Beck, Immediate Past President Jeff Hartsough, Executive Director CONTACT PAS 110 W. Washington Street, Suite A, Indianapolis, IN 46204 Telephone: (317) 974-4488 Fax: (317) 974-4499 E-mail: [email protected] Web: www.pas.org COPYRIGHT © 2015 by the Percussive Arts Society. Reproduction of any part of this publication without permission from PAS is prohibited by law. LET’S ACCESSORIZE! CHOOSING TRIANGLES AND TAMBOURINES FOR YOUR SCHOOL PROGRAM 5 THE PAS Ben Stiers DEVELOPING EAR CHOPS 12 EDUCATORS’ Paul Buyer PERCUSSION POTPOURRI: 10 TIPS FOR HELPING YOUR COMPANION PERCUSSION SECTION 18 Brian Nozny Volume I Spring 2015 ESTABLISHING CONSISTENCY WITHIN YOUR MARCHING PERCUSSION SECTION 22 Gordon Hicken IT’S NOT ABOUT THE DRUMMING: INCORPORATING DRUM CIRCLE ACTIVITIES WITH YOUR CAMPUS SPECIAL NEEDS DEPARTMENT 29 Ralph Hicks PERCUSSION REPAIR 101 36 Christopher Davis Music Educators, Greetings, and welcome to the inaugural volume of the PAS Educators’ Companion! We at the Percussive Arts Society realize that the field of percussion has an extremely wide spectrum of subjects, many of which music educators must deal with on a daily basis. -

United States
JANUARY 2018 COUNTRY SUMMARY United States The strong civil society and democratic institutions of the United States were tested in the first year of the administration of President Donald Trump. Across a range of issues in 2017, the US moved backward on human rights at home and abroad. Trump has targeted refugees and immigrants, calling them criminals and security threats; emboldened racist politics by equivocating on white nationalism; and consistently championed anti-Muslim ideas and policies. His administration has embraced policies that will roll back access to reproductive health care for women; championed health insurance changes that would leave many more Americans without access to affordable health care; and undermined police accountability for abuse. Trump has also expressed disdain for independent media and for federal courts that have blocked some of his actions. And he has repeatedly coddled autocratic leaders and showed little interest or leadership in pressing for the respect of human rights abroad. The individuals most likely to suffer abuse in the United States—including members of racial and ethnic minorities, immigrants, children, the poor, and prisoners—are often least able to defend their rights in court or via the political process. Many vulnerable groups endured renewed attacks on their rights during the year. Other longstanding US laws and practices—particularly related to criminal and juvenile justice, immigration, and national security—continued to violate internationally recognized human rights. Harsh Criminal Sentencing On any given day in the US, there are 2.3 million people in state and federal prisons and jails, the world’s largest reported incarcerated population. -

Common Core Teaching and Learning Strategies ELA Grades 6-12
6-12 Reading Informational Text Cite strong and thorough textual evidence to support analysis of what the text says explicitly as well as RI.9-10.1 inferences drawn from the text. Strategy/Lesson Suggestions Assessment FOR Learning Suggestions The following strategy utilizes a CCSS text exemplar from the 9-10 grade band. Statement Starter. Students partner and provide each other objective This strategy can be adapted to fit a variety of texts with an aligned level of feedback on their completed tables. The teacher then presents the class with complexity. a statement: “Ladies and gentlemen, Patrick Henry was a pacifist!” Close Read. Students conduct a close read of a text such as Patrick Henry’s or “Speech to the Second Virginia Convention”. After reading the text each “Margaret Chase Smith believes people should have the right to criticize.” student obtains a citation table for recording data as they conduct a second read. Within the table, students write specific phrases or sentences from the Students then work collaboratively with their partner to generate a cited text and articulate the significance of each. The strategy is modeled prior to summary in agreement with or dispute of the statement starter. As students beginning the exercise and students are able to “read like a detective” write, they use the following questions to guide their responses: (PARCC, 2011, p. 86) to determine the specific message the author is trying to 1. Are we interpreting the text correctly? convey. This activity could also be used to conduct a close read of Margaret 2. Are we citing specific language from the text? Chase Smith’s “Remarks to the Senate in Support of a Declaration of 3. -

The Trump Administration and the Media: Attacks on Press Credibility Endanger US Democracy and Global Press Freedom
The Trump Administration and the Media: Attacks on press credibility endanger US democracy and global press freedom By Leonard Downie Jr. with research by Stephanie Sugars A special report of the Committee to Protect Journalists The Trump Administration and the Media: Attacks on press credibility endanger US democracy and global press freedom By Leonard Downie Jr. with research by Stephanie Sugars A special report of the Committee to Protect Journalists The Committee to Protect Journalists is an independent, nonprofit organization that promotes press freedom worldwide. We defend the right of journalists to report the news safely and without fear of reprisal. In order to preserve our independence, CPJ does not accept any government grants or support of any kind; our work is funded entirely by contributions from individuals, foundations, and corporations. CHAIR VICE CHAIR HONORARY CHAIRMAN EXECUTIVE DIRECTOR Kathleen Carroll Jacob Weisberg Terry Anderson Joel Simon DIRECTORS Jonathan Klein Norman Pearlstine getty images los angeles times Stephen J. Adler reuters Jane Kramer Lydia Polgreen the new yorker gimlet media Andrew Alexander Mhamed Krichen Ahmed Rashid al-jazeera Amanda Bennett David Remnick Isaac Lee Krishna Bharat the new yorker google Rebecca MacKinnon Maria Teresa Ronderos Diane Brayton Kati Marton Alan Rusbridger new york times company lady margaret hall, oxford Michael Massing Susan Chira Karen Amanda Toulon Geraldine Fabrikant Metz the marshall project bloomberg news the new york times Sheila Coronel Darren Walker columbia university Matt Murray ford foundation school of journalism the wall street journal and dow jones newswires Roger Widmann Anne Garrels Victor Navasky Jon Williams Cheryl Gould the nation rté Lester Holt Clarence Page Matthew Winkler nbc chicago tribune bloomberg news SENIOR ADVISERS David Marash Sandra Mims Rowe Christiane Amanpour Charles L. -

December 1993
Features DAVE ABBRUZZESE With nary a note on Pearl Jam's breakthrough album, Ten, Dave Abbruzzese flew to the top of MD's 1993 Readers Poll in the Up & Coming category. Now the brand-new Five Against One is out, and Dave's really laying down his mark. • Matt Peiken 20 TONY REEDUS Can today's jazz drummer find happiness on both sides of the avant-garde/straight-ahead coin? Well, Tony Reedus has, making him one of the most sought-after skinsmen around. • Ken Micallef 26 ZILDJIAN AT 370 Zildjian certainly should be proud of their long history: Their cymbal design innovations often coincided with the major artistic leaps of our drumset masters. Since the company is celebrating their deep roots in a big way this year, we thought it a good time to check in. • Rick Van Horn 30 Volume 17, Number 12 Cover Photo By Lance Mercer EDUCATION NEWS EQUIPMENT 48 OFF THE 8 UPDATE RECORD Billy Cobham, Mike Portnoy Toss Panos, Lance Huff of David & the Giants, and the Bulletboys' 52 STRICTLY Jim D'Anda, plus News TECHNIQUE The Hi-Hat 138 INDUSTRY BY JOE MORELLO HAPPENINGS 62 DRIVER'S SEAT Big Bands & Bass Drums DEPARTMENTS BY CHARLIE PERRY 4 EDITOR'S 36 PRODUCT OVERVIEW 66 LATIN CLOSE-UP SYMPOSIUM Pearl Masters Maguinho's 6 READERS' Custom Drumkit BY RICK VAN HORN Brazilian Rhythms PLATFORM BY PETE MAGADINI 39 Rhythm Tech 12 ASK A PRO indexTension Drum 94 SHOW Tuners BY ADAM BUDOFSKY DRUMMERS' 16 IT'S SEMINAR QUESTIONABLE Pete Engelhart Crashers Trials & Tribulations BY ADAM BUDOFSKY Of A New York 50 DRUMLINE Show Drummer 40 LP Gajate Bracket BY LARRY CALLAHAN BY ADAM BUDOFSKY 102 CRITIQUE Taw Duplicate X 98 THE JOBBING Products NDEX DRUMMER 126 1993 I BY RICK VAN HORN The Clubdate Business UPDATE BY PETER J. -

Some Observations on the First Amendment and the War on Terror*
Tulsa Law Review Volume 53 | Issue 2 Article 6 Winter 2018 Observations on the First Amendment and the War on Terror Ofer Raban [email protected] Follow this and additional works at: https://digitalcommons.law.utulsa.edu/tlr Part of the Law Commons Recommended Citation Ofer Raban, Observations on the First Amendment and the War on Terror, 53 Tulsa L. Rev. 141 (2017). Available at: https://digitalcommons.law.utulsa.edu/tlr/vol53/iss2/6 This Article is brought to you for free and open access by TU Law Digital Commons. It has been accepted for inclusion in Tulsa Law Review by an authorized editor of TU Law Digital Commons. For more information, please contact [email protected]. Raban: Observations on the First Amendment and the War on Terror ARTICLE - RABAN, SOME OBSERVATIONS_FINAL (141) (CORRECTED) (DO NOT DELETE) 3/5/2018 8:29 AM SOME OBSERVATIONS ON THE FIRST AMENDMENT AND THE WAR ON TERROR* Ofer Raban† Freedom of speech has traditionally suffered at times of war, and the War on Terror—with its related wars in Iraq and Afghanistan—is no exception: since 9/11, formidable pressures have come to bear on the constitutional freedoms of speech and press. As this paper discusses, these pressures have come from all three branches of the federal government. They include increased executive enforcement of existing laws, new legislation targeting terrorism-related speech, and apparent judicial reluctance to vigorously enforce existing constitutional protections. Notably, these allegedly significant impingements on the freedom of speech were achieved without any apparent change in constitutional doctrine. With the War on Terror showing no signs of abating, and with Donald Trump in the White House, this is an opportune time to take stock of these recent impingements on the important freedoms of speech and press, and what we can learn from them.