Social Networking in Library Services
Total Page:16
File Type:pdf, Size:1020Kb
Load more
Recommended publications
-
Regional Use of Social Networking Tools
Regional Use of Social Networking Tools Kate Meeuf December 2014 TECHNICAL REPORT CMU/SEI-2014-TR-018 CERT® Division http://www.sei.cmu.edu Copyright 2014 Carnegie Mellon University This material is based upon work funded and supported by Department of Homeland Security under Contract No. FA8721-05-C-0003 with Carnegie Mellon University for the operation of the Software Engineering Institute, a federally funded research and development center sponsored by the United States Department of Defense. Any opinions, findings and conclusions or recommendations expressed in this material are those of the author(s) and do not necessarily reflect the views of Department of Homeland Security or the United States Department of Defense. This report was prepared for the SEI Administrative Agent AFLCMC/PZM 20 Schilling Circle, Bldg 1305, 3rd floor Hanscom AFB, MA 01731-2125 NO WARRANTY. THIS CARNEGIE MELLON UNIVERSITY AND SOFTWARE ENGINEERING INSTITUTE MATERIAL IS FURNISHED ON AN “AS-IS” BASIS. CARNEGIE MELLON UNIVERSITY MAKES NO WARRANTIES OF ANY KIND, EITHER EXPRESSED OR IMPLIED, AS TO ANY MATTER INCLUDING, BUT NOT LIMITED TO, WARRANTY OF FITNESS FOR PURPOSE OR MERCHANTABILITY, EXCLUSIVITY, OR RESULTS OBTAINED FROM USE OF THE MATERIAL. CARNEGIE MELLON UNIVERSITY DOES NOT MAKE ANY WARRANTY OF ANY KIND WITH RESPECT TO FREEDOM FROM PATENT, TRADEMARK, OR COPYRIGHT INFRINGEMENT. This material has been approved for public release and unlimited distribution except as restricted be- low. Internal use:* Permission to reproduce this material and to prepare derivative works from this material for internal use is granted, provided the copyright and “No Warranty” statements are included with all reproductions and derivative works. -

Archetypes of Enterprise Social Network Users
Proceedings of the 51st Hawaii International Conference on System Sciences j 2018 Archetypes of Enterprise Social Network Users Christian Oettl, Thomas Berger, Markus Böhm, Manuel Wiesche, Helmut Krcmar Technical University of Munich {c.oettl, thomas.berger}@tum.de, {markus.boehm, manuel.wiesche, krcmar}@in.tum.de Abstract organizations will promote the introduction and development of ESNs in the future [8]. Investments in enterprise social networks (ESNs) have However, even if ESNs are implemented in increased rapidly in recent years. However, an ESN organizations, their value contribution appears unclear utilization intensity develops slowly, and there are a because 80% of projects do not fulfill expectations few well-grounded approaches to understand ESN [16]. The typical ROI of any social technology usage. To elaborate on different archetypes of ESN becomes positive when 15% to 25% of employees use users, we conducted a case study that comprised 28 such technology extensively and companies should not interviews with a large IT services company. We assume that “If we build it, they will come” [3]. present a model to characterize ESN users and classify This was also observed in the company that was them as archetypes based on the following two considered in this study. In 2014, a large multinational dimensions: individual openness to ESNs and IT service provider started a radical metamorphosis perceived task-fit. We determine six archetypes of ESN from an email centered to an ESN centered users, namely, power users, limited users, reluctant organization. The implemented solution provides users, repudiators, hidden champions, and question typical key functionalities that characterize an ESN as marks. -

THE SIGNIFICANCE of SOCIAL SOFTWARE Danah Boyd UC
THE SIGNIFICANCE OF SOCIAL SOFTWARE danah boyd UC Berkeley School of Information, Berkeley, CA, USA [email protected] http://www.zephoria.org/ Social software… It’s a term that is thrown around frequently, rarely defined, completely elusive, and yet totally significant. What on earth does it mean? And should you care? (IMHO) Of course you should care! Social software is all around us now. It is altering the organization of social life. How do you communicate with loved ones? How do you find information? A lot of this hinges on social software. In this opening essay, I want to address the significance of „social software.” I will look at this from a few different angles, building on the attitudes and practices of creators, users, and researchers of social software. My goal is to lay out some possible approaches for thinking about the types of technologies and behaviors that emerge. What I’m offering is not some truth serum (nor even a proper analysis) – it can and should be contested, questioned, and wrestled with. Let’s begin. Social Software First… what constitutes „social software“? Where does this term come from? In 2002, Clay Shirky (re)claimed the term „social software“ to encompass „all uses of software that supported interacting groups, even if the interaction was offline.“1 His choice was intentional. Although other terms existed – groupware, social computing, computer-mediated communication, etc. – he felt that these older terms In: Burg, Thomas N. / Jan Schmidt (Eds.) BlogTalks Reloaded. Social Software - Research & Cases. Norderstedt: Books on Demand. BlogTalk Reloaded were either polluted or a bad fit to address certain new technologies. -

Social Media Why You Should Care What Is Social Media? Social Network
Social Media Why You Should Care IST 331 - Olivier Georgeon, Frank Ritter 31 oct 15 • eMarketer (2007) estimated by 2011 one-half Examples of all Internet users will use social networking • Facebook regulary. • YouTube • By 2015, 75% use • Myspace • Twitter • Del.icio.us • Digg • Etc… 2 What is Social Media? Social Network • Social Network • Online communities of people who share • User Generated Content (UGC) interests and activities, • Social Bookmarking • … or who are interested in exploring the interests and activities of others. • Examples: Facebook, MySpace, LinkedIn, Orkut • Falls to analysis with tools in Ch. 9 3 4 User Generated Content (UGC) Social Bookmarking • A method for Internet users to store, organize, search, • or Consumer Generated Media (CGM) and manage bookmarks of web pages on the Internet with the help of metadata. • Based on communities; • Defined: Media content that is publicly – The more people who bookmark a piece of content, the more available and produced by end-users (user). value it is determined to have. • Examples: Digg, Del.icio.us, StumbleUpon, and reddit….and now combinations • Usually supported by a social network • Examples: Blogs, Micro-blogs, YouTube video, Flickr photos, Wiki content, Facebook wall posts, reddit, Second Life… 5 6 Social Media Principles Generate an activity stream • Automatic • Who you are – Google History, Google Analytics – Personalization • Blog • Who you know • Micro-blog – Browse network – Twitter, yammer, identi.ca • What you do • Mailing groups – Generate an activity stream -

POPULAR SOCIAL MEDIA SITES Below Is a List of Some of the Most Commonly Used Youth and Teen Social Networking Sites and Tools
POPULAR SOCIAL MEDIA SITES Below is a list of some of the most commonly used youth and teen social networking sites and tools. Ask.fm (http://ask.fm) Participants log on, post a question anonymously and anyone may answer anonymously. “Do you think I am fat?” or “Would you date me?” are examples of questions posted in the past. There have also been examples in which individuals were encouraged to kill themselves. The site has courted controversy by not having workable reporting, tracking or parental control processes, which have become the norm on other social media websites. Twitter (https://twitter.com) An online social networking and microblogging service that enables users to send and read "tweets", which are text messages limited to 140 characters. Instagram (http://instagram.com) A photo-sharing app for iPhone. Kik (http://kik.com) Kik is as an alternative to email or text messaging and its popularity has grown in the last two years. Kik is accessible on smartphones and supports over 4 million users, called “Kicksters.” Users are not restricted to sending text messages with Kik. Images, videos, sketches, emoticions and more may be sent. A user can block users on Kik from contacting them. Wanelo (http://wanelo.com) Wanelo (from Want, Need, Love) sells unique products online, all posted by users. Products posted for sale range from dishes, clothing, intimate wear and other potentially “R-Rated” products. Vine (https://vine.co) Vine is used to create and share free and instant six-second videos. Topic and content ranges. Snapchat (http://www.snapchat.com) A photo messaging application. -

Social Software and Learning Contents
Futurelab 1 Canons Road Harbourside Bristol BS1 5UH United Kingdom OPENING EDUCATION tel +44 (0)117 915 8200 fax +44 (0)117 915 8201 [email protected] Social software and learning www.futurelab.org.uk Contents This publication is available to download from the Futurelab website – Foreword 02 www.futurelab.org.uk/research/opening_education.htm. Executive summary 03 Also from Futurelab: 1 Introduction: How do we learn in an era of connection and collaboration? 07 2 What is social software? 12 Literature Reviews and Research Reports Written by leading academics, these publications provide comprehensive 3 Does learning change in an information society? 30 surveys of research and practice in a range of different fields. 4 How do we move towards ‘c-learning’? 46 Bibliography 60 Handbooks Drawing on Futurelab's in-house R&D programme as well as projects from Appendix 1: Some annotated links 64 around the world, these handbooks offer practical advice and guidance to support the design and development of new approaches to education. Opening Education Series Focusing on emergent ideas in education and technology, this series of publications opens up new areas for debate and discussion. We encourage the use and circulation of the text content of these publications, which are available to download from the Futurelab website – www.futurelab.org.uk/research. For full details of our open access policy, go to www.futurelab.org.uk/open_access.htm. g n i n r a e l d n a e r Martin Owen, Lyndsay Grant, Steve Sayers and Keri Facer a w t f o s l a Futurelab 2006 i c o S 01 Foreword Executive summary Opening Education is a new series of publications from Futurelab. -
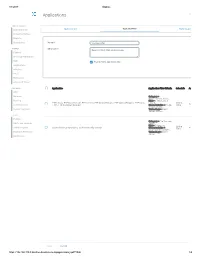
Applications Log Viewer
4/1/2017 Sophos Applications Log Viewer MONITOR & ANALYZE Control Center Application List Application Filter Traffic Shaping Default Current Activities Reports Diagnostics Name * Mike App Filter PROTECT Description Based on Block filter avoidance apps Firewall Intrusion Prevention Web Enable Micro App Discovery Applications Wireless Email Web Server Advanced Threat CONFIGURE Application Application Filter Criteria Schedule Action VPN Network Category = Infrastructure, Netw... Routing Risk = 1-Very Low, 2- FTPS-Data, FTP-DataTransfer, FTP-Control, FTP Delete Request, FTP Upload Request, FTP Base, Low, 4... All the Allow Authentication FTPS, FTP Download Request Characteristics = Prone Time to misuse, Tra... System Services Technology = Client Server, Netwo... SYSTEM Profiles Category = File Transfer, Hosts and Services Confe... Risk = 3-Medium Administration All the TeamViewer Conferencing, TeamViewer FileTransfer Characteristics = Time Allow Excessive Bandwidth,... Backup & Firmware Technology = Client Server Certificates Save Cancel https://192.168.110.3:4444/webconsole/webpages/index.jsp#71826 1/4 4/1/2017 Sophos Application Application Filter Criteria Schedule Action Applications Log Viewer Facebook Applications, Docstoc Website, Facebook Plugin, MySpace Website, MySpace.cn Website, Twitter Website, Facebook Website, Bebo Website, Classmates Website, LinkedIN Compose Webmail, Digg Web Login, Flickr Website, Flickr Web Upload, Friendfeed Web Login, MONITOR & ANALYZE Hootsuite Web Login, Friendster Web Login, Hi5 Website, Facebook Video -

Examples of Online Social Network Analysis Social Networks
Examples of online social network analysis Social networks • Huge field of research • Data: mostly small samples, surveys • Multiplexity Issue of data mining • Longitudinal data McPherson et al, Annu. Rev. Sociol. (2001) New technologies • Email networks • Cellphone call networks • Real-world interactions • Online networks/ social web NEW (large-scale) DATASETS, longitudinal data New laboratories • Social network properties – homophily – selection vs influence • Triadic closure, preferential attachment • Social balance • Dunbar number • Experiments at large scale... 4 Another social science lab: crowdsourcing, e.g. Amazon Mechanical Turk Text http://experimentalturk.wordpress.com/ New laboratories Caveats: • online links can differ from real social links • population sampling biases? • “big” data does not automatically mean “good” data 7 The social web • social networking sites • blogs + comments + aggregators • community-edited news sites, participatory journalism • content-sharing sites • discussion forums, newsgroups • wikis, Wikipedia • services that allow sharing of bookmarks/favorites • ...and mashups of the above services An example: Dunbar number on twitter Fraction of reciprocated connections as a function of in- degree Gonçalves et al, PLoS One 6, e22656 (2011) Sharing and annotating Examples: • Flickr: sharing of photos • Last.fm: music • aNobii: books • Del.icio.us: social bookmarking • Bibsonomy: publications and bookmarks • … •“Social” networks •“specialized” content-sharing sites •Users expose profiles (content) and links -
Opportunities and Challenges for Standardization in Mobile Social Networks
Opportunities and Challenges for Standardization in Mobile Social Networks Laurent-Walter Goix, Telecom Italia [email protected] Bryan Sullivan, AT&T [email protected] Abstract This paper describes the opportunities and challenges related to the standardization of interoperable “Mobile Social Networks”. Challenges addressed include the effect of social networks on resource usage, the need for social network federation, and the needs for a standards context. The concept of Mobile Federated Social Networks as defined in the OMA SNEW specification is introduced as an approach to some of these challenges. Further specific needs and opportunities in standards and developer support for mobile social apps are described, including potentially further work in support of regulatory requirements. Finally, we conclude that a common standard is needed for making mobile social networks interoperable, while addressing privacy concerns from users & institutions as well as the differentiations of service providers. 1 INTRODUCTION Online Social Networks (OSN) are dominated by Walled Gardens that have attracted users by offering new paradigms of communication / content exchange that better fit their modern lifestyle. Issues are emerging related to data ownership, privacy and identity management and some institutions such as the European Commission have started to provide measures for controlling this. The impressive access to OSN from ever smarter mobile devices, as well as the growth of mobile- specific SN services (e.g. WhatsApp) have further stimulated the mobile industry that is already starving for new attractive services (RCS 1). In this context OMA 2 as mobile industry forum has recently promoted the SNEW specifications that can leverage network services such as user identity and native interoperability of mobile networks (the approach promoted by “federated social networks”). -
Systematic Scoping Review on Social Media Monitoring Methods and Interventions Relating to Vaccine Hesitancy
TECHNICAL REPORT Systematic scoping review on social media monitoring methods and interventions relating to vaccine hesitancy www.ecdc.europa.eu ECDC TECHNICAL REPORT Systematic scoping review on social media monitoring methods and interventions relating to vaccine hesitancy This report was commissioned by the European Centre for Disease Prevention and Control (ECDC) and coordinated by Kate Olsson with the support of Judit Takács. The scoping review was performed by researchers from the Vaccine Confidence Project, at the London School of Hygiene & Tropical Medicine (contract number ECD8894). Authors: Emilie Karafillakis, Clarissa Simas, Sam Martin, Sara Dada, Heidi Larson. Acknowledgements ECDC would like to acknowledge contributions to the project from the expert reviewers: Dan Arthus, University College London; Maged N Kamel Boulos, University of the Highlands and Islands, Sandra Alexiu, GP Association Bucharest and Franklin Apfel and Sabrina Cecconi, World Health Communication Associates. ECDC would also like to acknowledge ECDC colleagues who reviewed and contributed to the document: John Kinsman, Andrea Würz and Marybelle Stryk. Suggested citation: European Centre for Disease Prevention and Control. Systematic scoping review on social media monitoring methods and interventions relating to vaccine hesitancy. Stockholm: ECDC; 2020. Stockholm, February 2020 ISBN 978-92-9498-452-4 doi: 10.2900/260624 Catalogue number TQ-04-20-076-EN-N © European Centre for Disease Prevention and Control, 2020 Reproduction is authorised, provided the -

Protection, Not Barriers: Using Social Software Policies to Guide and Safeguard Students and Employees
Georgia State University ScholarWorks @ Georgia State University University Library Faculty Publications Georgia State University Library Fall 2010 Protection, Not Barriers: Using Social Software Policies to Guide and Safeguard Students and Employees Brian K. Kooy Georgia State University, [email protected] Sarah King Steiner Georgia State University, [email protected] Follow this and additional works at: https://scholarworks.gsu.edu/univ_lib_facpub Part of the Library and Information Science Commons Recommended Citation Kooy, B. & Steiner, K. (2010). Protection, not barriers: Using social software policies to guide and safeguard students and employees. Reference & User Services Quarterly, 50(1), 59-71. doi: 10.5860/ rusq.50n1 This Article is brought to you for free and open access by the Georgia State University Library at ScholarWorks @ Georgia State University. It has been accepted for inclusion in University Library Faculty Publications by an authorized administrator of ScholarWorks @ Georgia State University. For more information, please contact [email protected]. FeAture Protection, not Barriers Using Social Software Policies to Guide and Safeguard Students and Employees Academic librarians have been using social outreach to include online spaces as Brian k. kooy and software and networking sites for public well. One area in which librarians are Sarah k. Steiner services since they appeared on the Inter- providing online outreach is through net. While issues of privacy, identity man- the use of social software and social Brian K. Kooy is Philosophy, Religious agement, and self-disclosure when using networking websites such as Facebook Studies, and Middle East Studies such technologies have been written about, and MySpace. Even most library blogs Librarian and Sarah K. -

Perfiles De La Biblioteca En RRSS Y Redes Sociales De Lectura
Red Andaluza de bibliotecas escolares redes sociales Nuevos comportamientos. Uso de RRSS García Guerrero, J. (2012). Entornos para una lectura fomentada. Extracto DR 3 págs. 26-30: https://cutt.ly/DuKE72l AA.VV. (2013). Nuevos comportamientos y formas de leer. Extracto DR 5, págs. 124-143: https://cutt.ly/FuKTgGH AA. VV. (2013). Uso de las redes sociales en la biblioteca escolar. Extracto DR 5: https://cutt.ly/guKTOFU AA.VV. (2013). Gestión de plataformas virtuales para la comunidad de lectores. Extracto DR 5: https://cutt.ly/7uKTZ6s Identidad digital de la biblioteca escolar Olmos Olmos, D. (2016). Gestionar la identidad digital de la biblioteca : https://cutt.ly/cyCDEbR Olmos Olmos, D. (2016). Breve guía de estilo de las publicaciones de la biblioteca escolar: https://cutt.ly/0yCGkUC Red Andaluza de bibliotecas escolares redes sociales Perfiles de la biblioteca en RRSS Twitter. Microblogging en 280 caracteres. Difusión rápida de información destinada especialmente a profesionales, entidades y familias: https://twitter.com Facebook. Red social más utilizada destinada a un amplio abanico de edades. Muy recomendable para dirigirse a familas: https://es-es.facebook.com Pinterest. Tableros para interactuar con usuarios/as y profesionales: https://www.pinterest.es Instagram. Red social más utilizada por el público joven (junto con TiK Tok y Snapchat). Muy recomendable para dirigirse al alumnado: https://www.instagram.com En YouTube está el público. Canal de vídeo. Para difusión de reseñas, actividades, clubes de lectura, proyectos, tutoriales... Lo que recomendable es que la duración del vídeo no sea excesiva: https://www.youtube.com Aplicación de moda entre los más jóvenes.