Netwalker Ransomware
Total Page:16
File Type:pdf, Size:1020Kb
Load more
Recommended publications
-

A Review of Fuzzing Tools and Methods 1 Introduction
A Review of Fuzzing Tools and Methods James Fell, [email protected] Originally published in PenTest Magazine on 10th March 2017 1 Introduction Identifying vulnerabilities in software has long been an important research problem in the field of information security. Over the last decade, improvements have been made to programming languages, compilers and software engineering methods aimed at reducing the number of vulnerabilities in software [26]. In addition, exploit mitigation features such as Data Execution Prevention (DEP) [65] and Address Space Layout Randomisation (ASLR) [66] have been added to operating systems aimed at making it more difficult to exploit the vulnerabilities that do exist. Nevertheless, it is fair to say that all software applications of any significant size and complexity are still likely to contain undetected vulnerabilities and it is also frequently possible for skilled attackers to bypass any defences that are implemented at the operating system level [6, 7, 12, 66]. There are many classes of vulnerabilities that occur in software [64]. Ultimately they are all caused by mistakes that are made by programmers. Some of the most common vulnerabilities in binaries are stack based and heap based buffer overflows, integer overflows, format string bugs, off-by-one vulnerabilities, double free and use-after-free bugs [5]. These can all lead to an attacker hijacking the path of execution and causing his own arbitrary code to be executed by the victim. In the case of software running with elevated privileges this can lead to the complete compromise of the host system on which it is running. -

Software Vulnerabilities Principles, Exploitability, Detection and Mitigation
Software vulnerabilities principles, exploitability, detection and mitigation Laurent Mounier and Marie-Laure Potet Verimag/Université Grenoble Alpes GDR Sécurité – Cyber in Saclay (Winter School in CyberSecurity) February 2021 Software vulnerabilities . are everywhere . and keep going . 2 / 35 Outline Software vulnerabilities (what & why ?) Programming languages (security) issues Exploiting a sofwtare vulnerability Software vulnerabilities mitigation Conclusion Example 1: password authentication Is this code “secure” ? boolean verify (char[] input, char[] passwd , byte len) { // No more than triesLeft attempts if (triesLeft < 0) return false ; // no authentication // Main comparison for (short i=0; i <= len; i++) if (input[i] != passwd[i]) { triesLeft-- ; return false ; // no authentication } // Comparison is successful triesLeft = maxTries ; return true ; // authentication is successful } functional property: verify(input; passwd; len) , input[0::len] = passwd[0::len] What do we want to protect ? Against what ? I confidentiality of passwd, information leakage ? I control-flow integrity of the code I no unexpected runtime behaviour, etc. 3 / 35 Example 2: make ‘python -c ’print "A"*5000’‘ run make with a long argument crash (in recent Ubuntu versions) Why do we need to bother about crashes (wrt. security) ? crash = consequence of an unexpected run-time error not trapped/foreseen by the programmer, nor by the compiler/interpreter ) some part of the execution: I may take place outside the program scope/semantics I but can be controled/exploited by an attacker (∼ “weird machine”) out of scope execution runtime error crash normal execution possibly exploitable ... security breach ! ,! may break all security properties ... from simple denial-of-service to arbitrary code execution Rk: may also happen silently (without any crash !) 4 / 35 Back to the context: computer system security what does security mean ? I a set of general security properties: CIA Confidentiality, Integrity, Availability (+ Non Repudiation + Anonymity + . -

Intrinsic Propensity for Vulnerability in Computers? Arbitrary Code Execution in the Universal Turing Machine
Intrinsic Propensity for Vulnerability in Computers? Arbitrary Code Execution in the Universal Turing Machine Pontus Johnson KTH Royal Institute of Technology Stockholm, Sweden [email protected] Abstract and Weyuker in [4], “Turing’s construction of a universal computer in 1936 provided reason to believe that, at least in The universal Turing machine is generally considered to be principle, an all-purpose computer would be possible, and the simplest, most abstract model of a computer. This paper was thus an anticipation of the modern digital computer.” Or, reports on the discovery of an accidental arbitrary code execu- in the words of Stephen Wolfram [16], ‘what launched the tion vulnerability in Marvin Minsky’s 1967 implementation whole computer revolution is the remarkable fact that uni- of the universal Turing machine. By submitting crafted data, versal systems with fixed underlying rules can be built that the machine may be coerced into executing user-provided can in effect perform any possible computation.” Not only code. The article presents the discovered vulnerability in de- the universality, but also the simplicity of the universal Tur- tail and discusses its potential implications. To the best of our ing machine has attracted interest. In 1956, Claude Shannon knowledge, an arbitrary code execution vulnerability has not explored some minimal forms of the universal Turing ma- previously been reported for such a simple system. chine [13], and posed the challenge to find even smaller such machines. That exploration has continued to this day [16]. 1 Introduction A common strategy for understanding a problem is to re- duce it to its minimal form. -
Security Threat Intelligence Report
Security Threat Intelligence Report December 2020 In this issue COVID-19 vaccine manufacturers and supply chain targeted RansomEXX ransomware targeting Linux systems Botnet targets Linux servers, Linux IoT devices NSA top 25 vulnerabilities exploited by Chinese APT groups VMware zero-day vulnerability exploited in the wild Security Threat Intelligence Report About this report Message from Mark Hughes Fusing a range of public and proprietary information feeds, Cyber criminals are opportunists, and including DXC’s global network with COVID-19 vaccines shipping in of security operations centers and cyber intelligence services, multiple countries, attackers are targeting this report delivers an overview manufacturers and their supply chains in an of major incidents, insights into effort to monetize ransomware attacks at key trends and strategic threat awareness. the worst possible time and steal intellectual property and patient data. This month’s report also documents This report is a part of DXC Labs | Security, which provides insights the expanding attacks against Linux, Windows, and internet of and thought leadership to the things (IoT) devices. Also, the SolarWinds hack is top of mind for security industry. everyone. This is a rapidly evolving situation, and we will share Intelligence cutoff date: more details next month. For the most up to date information, November 30, 2020 refer to CISA guidance. Mark Hughes Senior Vice President Offerings & Strategic Partners DXC Technology Table of Threat Updates contents RansomEXX ransomware targeting -

Check Point Threat Intelligence Bulletin
November 2-8, 2020 YOUR CHECK POINT THREAT INTELLIGENCE REPORT TOP ATTACKS AND BREACHES Check Point Research has alerted against a wave of ransomware attacks targeting Israeli companies and corporations, using known ransomware families such as REvil and Ryuk, as well as a new family called ‘Pay2Key’. The ransomware is capable of rapid lateral movement within the company network. Check Point SandBlast Agent provides protection against these threats (Ransomware.Win32.Pay2Key; Ransomware.Win32.REvil) Luxottica, the world's largest eyewear company, has admitted it has been breached. The giant’s appointment scheduling application has been hacked, leading to the exposure of protected health information (PHI) for patients of eye care practices such as LensCrafters, Target Optical and EyeMed. Japanese game developer Capcom has suffered a breach leading to the shutdown of some its systems, possibly by the Ragnar Locker ransomware. Attackers claim that 1TB of sensitive data has been stolen. Check Point SandBlast Agent provides protection against this threat (Ransomware.Win32.Ragnar) The Italian liquor company Campari Group has been hit by the Ragnar Locker ransomware, leading to the theft of 2TB of unencrypted files. The attackers are demanding a $15 million ransom to retrieve the files. Check Point Research has uncovered an attack operation targeting the Sangoma and Asterisk VoIP phone systems at nearly 1,200 organizations. The attackers, most likely located in Gaza and the West Bank, target SIP servers to execute telecom fraud, sell phone number and gain access to the organizations’ VoIP servers. Check Point IPS provides protection against this threat (SIPVicious Security Scanner; Sangoma FreePBX Authentication Bypass (CVE- 2019-19006); Command Injection Over HTTP) North Korean surveillance campaign targeting the aerospace and defense sectors in Australia, Israel, Russia and India is spreading a new spyware called Torisma via fake job offers sent through social media. -

Subscription Pamplet New 11 01 18
Add More Titles Below: Vault # CONTINUED... [ ] Aphrodite V [ ] ___________________________ [ ] Auntie Agatha's Wayward Bunnies (6) [ ] James Bond [ ] Bitter Root [ ] Lone Ranger [ ] ___________________________ [ ] Blackbird [ ] Mars Attack [ ] Bully Wars [ ] Miss Fury [ ] ___________________________ [ ] Burnouts [ ] Project SuperPowers 625 N. Moore Ave., [ ] Cemetery Beach (of 7) [ ] Rainbow Brite [ ] ___________________________ [ ] Cold Spots (of 5) [ ] Red Sonja Moore OK 73160 [ ] Criminal [ ] Thunderbolt [ ] ___________________________ [ ] Crowded [ ] Turok [ ] Curse Words [ ] Vampirella Dejah Thores [ ] ___________________________ [ ] Cyber Force [ ] Vampirella Reanimator Subscription [ ] Dead Rabbit [ ] ___________________________ [ ] Die Comic Pull Sheet [ ] East of West [ ] ___________________________ [ ] Errand Boys (of 5) [ ] Evolution [ ] ___________________________ We offer subscription discounts for [ ] Exorisiters [ ] Freeze [ ] Adventure Time Season 11 [ ] ___________________________ customers who want to reserve that special [ ] Gideon Falls [ ] Avant-Guards (of 12) comic book series with SUPERHERO [ ] Gunning for Hits [ ] Black Badge [ ] ___________________________ BENEFITS: [ ] Hardcore [ ] Bone Parish [ ] Hit-Girl [ ] Buffy Vampire Slayer [ ] ___________________________ [ ] Ice Cream Man [ ] Empty Man Tier 1: 1-15 Monthly ongoing titles: [ ] Infinite Dark [ ] Firefly [ ] ___________________________ 10% Off Cover Price. [ ] Jook Joint (of 5) [ ] Giant Days [ ] Kick-Ass [ ] Go Go Power Rangers [ ] ___________________________ -

THE INCREDIBLE HULK FAST FORCES CHARACTER CARDS Original Text
THE INCREDIBLE HULK FAST FORCES CHARACTER CARDS Original Text ©2011 WIZKIDSizKids/N/NEECA,CA L LLC.LC. TM &TM © &2011 © DC2011 Com Maicsrvel & ( s11Subs) . PRINTING INSTRUCTIONS 1. From Adobe® Reader® or Adobe® Acrobat® open the print dialog box (File>Print or Ctrl/Cmd+P). 2. Click on Properties and set your Page Orientation to Landscape (11 x 8.5). 3. Under Print Range>Pages input the pages you would like to print. (See Table of Contents) 4. Under Page Handling>Page Scaling select Multiple pages per sheet. 5. Under Page Handling>Pages per sheet select Custom and enter 2 by 2. 6. If you want a crisp black border around each card as a cutting guide, click the checkbox next to Print page border. 7. Click OK. ©2011 WWiizKids/NECA LLLC.C. TM & TM© 2011& © 2011DC Com Maicsrvel & (Subss11). TABLE OF CONTENTS Abomination™, 7 General Thunderbolt Ross™, 8 Hulk™, 4 Hulkbuster Wrangler™, 5 The Leader™, 9 She-Hulk™, 6 ©2011 WWiizKids/NECA LLLC.C. TM & TM© 2011& © 2011DC Com Maicsrvel & (Subss11). 001 HULK™ Stronger the Angrier I Get Whenever a second action Avengers, Brute, Defenders token is placed on Hulk, if he would take pushing damage, you may instead heal him of 1 damage. A MILE EVERY LEAP (Leap/Climb) RAGING ENGINE OF DESTRUCTION (Charge) A TANK THROWN LIKE A JAVELIN (Super Strength) THE GIFT OF THE GAMMA BOMB (Impervious) REAL NAME: Bruce Banner SIGNIFICANT APPEARANCE: Incredible Hulk #1 (1962) HULK DOESN’T BLEED (Invulnerability) BACKGROUND: A veritable force of nature, the Hulk possesses near limitless strength and a deceptive cunning. -

Red Hulk - Marvel Universe Wiki: the Definitive Online Source for Marvel Super Hero Bios
Red Hulk - Marvel Universe Wiki: The definitive online source for Marvel super hero bios. 5/20/13 11:00 PM Red Hulk As a young man, Thaddeus Ross enlisted in the military and received his nickname from his troops because he "struck like a thunderbolt" when leading them into action. Now he has become the very thing he hated most in life. He is the Red Hulk. Military Man General Thaddeus E. Ross was born into a family with a proud tradition of military ser- vice. Both his father and his grandfather served heroically in past American wars. As a boy Thaddeus immersed himself in military history, and he learned how to fly by barn- storming at country fairs. When he came of age Ross enlisted in the military, graduating first in his class at West Point. He married Karen Lee, the daughter of his commanding officer at the time. Ross rapidly rose in rank to captain and then major while serving in his first war. Ross made a great reputation as a leader in combat, but after the war, he was stationed at the nu- clear research facility at Los Alamos, New Mexico. There he met nuclear physicist Brian Banner, the father of Robert Bruce Banner. Ross had risen to the rank of colonel by the time he was sent to his next war, during which he became a general in the U.S. Air Force (Ross never rose beyond three-star gen- eral). As he gloried in combat, he was dissatisfied with the "desk jobs" he was given be- fore and after the war. -
Conti Ransomware: Evasive by Nature and How It Works
BRAINTRACE THREAT ADVISORY REPORT APRIL 15, 2021 TABLE OF CONTENTS BACKGROUND ..................................................................................................................................................... 2 VULNERABILITIES PATCHED IN NETTLE'S SIGNATURE VERIFICATION ........................................................ 2 APPLE MAIL ZERO-CLICK VULNERABILITY ...................................................................................................... 2 FAKE NETFLIX APP CALLED FLIXONLINE LURING ANDROID USERS THROUGH WHATSAPP MESSAGES 3 CHARMING KITTEN APT GROUP TARGETING MEDICAL RESEARCHERS ...................................................... 4 GIGASET ANDROID UPDATE SERVER HACKED TO INSTALL MALWARE ON USERS' DEVICES .................. 5 'MORE_EGGS' MALWARE TARGETS PROFESSIONALS WITH LINKEDIN JOB OFFERS ................................ 6 SONICWALL EMAIL SECURITY VULNERABLE TO MALICIOUS HTTP REQUESTS .......................................... 7 CONTI RANSOMWARE: EVASIVE BY NATURE AND HOW IT WORKS. ......................................................... 8 REVIL RANSOMWARE NOW CHANGES PASSWORD TO AUTO-LOGIN IN SAFE MODE .............................. 9 NEW VULNERABILITY TARGETS POPULAR WINDOWS TIME SYNCH SOFTWARE ...................................... 9 RISING TIDE IN FIRMWARE CYBERATTACKS ................................................................................................. 10 UNPATCHED VULNERABILITY FOUND IN CISCO ROUTER MANAGEMENT INTERFACE ............................. 11 CRING RANSOMWARE -
Automated Scanning Vulnerability Report
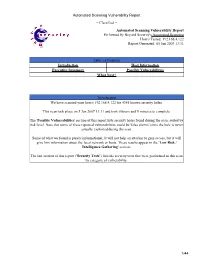
Automated Scanning Vulnerability Report − Classified − Automated Scanning Vulnerability Report Performed by Beyond Security's Automated Scanning Host/s Tested: 192.168.4.122 Report Generated: 05 Jun 2007 13:31 Table of Contents Introduction Host Information Executive Summary Possible Vulnerabilities What Next? Introduction We have scanned your host/s 192.168.4.122 for 4345 known security holes. This scan took place on 5 Jun 2007 13:31 and took 0 hours and 5 minutes to complete. The 'Possible Vulnerabilities' section of this report lists security holes found during the scan, sorted by risk level. Note that some of these reported vulnerabilities could be 'false alarms' since the hole is never actually exploited during the scan. Some of what we found is purely informational; It will not help an attacker to gain access, but it will give him information about the local network or hosts. These results appear in the 'Low Risk / Intelligence Gathering' section. The last section of this report ('Security Tests') lists the security tests that were performed in this scan by category of vulnerability. 1/44 Automated Scanning Vulnerability Report Executive Summary Learn more about how vulnerabilities are classified Vulnerabilities by Host and Risk Level Total IP Address High Medium Low Vulnerabilities 192.168.4.122 113 33 60 20 Vulnerabilities By Risk Level Top Vulnerabilities By Host 2/44 Automated Scanning Vulnerability Report Vulnerabilities by Service and Risk Level Service Total High Risk Medium Risk Low Risk Vulnerabilities netbios−ns (137/udp) 1 0 0 1 microsoft−ds 101 33 58 10 (445/tcp) general/tcp 8 0 1 7 ntp (123/udp) 1 0 0 1 netbios−ssn 1 0 1 0 (139/tcp) general/icmp 1 0 0 1 Top Vulnerabilities By Service Top Vulnerable Services 3/44 Automated Scanning Vulnerability Report Possible Vulnerabilities High Medium Low Risk Factor: High A Total of 33 High Risk Vulnerability/ies was/were discovered. -

Vs System 2PCG Rules
Issues and Arcs Our first two Arcs featured Beast Vs. System® 2PCG® has been Deadpool and the Marvel Note that Acrobatic doubles his reformatted from its small Cinematic Universe. This Arc DEF whether he is attacking and big box expansions into is all about Spider-Man and OR defending. a monthly release. From now his friends and enemies. The on every three months of Vs. previous two Issues featured ® System® 2PCG® content will the Spider-Friends and the 2 BEAST have a specific theme and dastardly Sinister Syndicate. SUPPORTING CHARA CTER be called an "Arc." There will This Issue introduces more be one new set almost every cards for an NYC team we’ve ® month. Most of these will be featured before – The Defenders ( ). 55-card “Issues” (like this one), Climb At the start of your Main Phase, you may exhaust a location. If you do, put a +1/+1 counter on Beast. and sometimes there will be a Acrobatic While in combat, Beast gets 200-card “Giant-Sized Issue,” 2 | 2 struck with double his DEF. DFX-010 ©2018 UDC. which is great for new players. 1 THE NEW DEFENDERS Namor Atlantis Rises adds a new row to Devil-Slayer When Devil-Slayer and the All three of Namor’s Rage powers your side, between your back row His Shadow Cloak lets him defender strike each other: DO count face-down exhausted and your resource row, for the attack hidden and stunned • Devil-Slayer can be stunned enemy characters as well. rest of the game. A player can’t characters. -
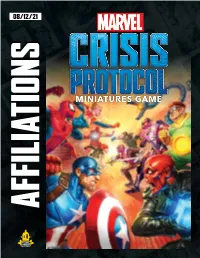
Affiliation List
AFFILIATIONS 08/12/21 AFFILIATION LIST Below you will find a list of all current affiliations cards and characters on them. As more characters are added to the game this list will be updated. A-FORCE • She-Hulk (k) • Blade • Angela • Cable • Black Cat • Captain Marvel • Black Widow • Deadpool • Black Widow, Agent of S.H.I.E.L.D. • Hawkeye • Captain Marvel • Hulk • Crystal • Iron Fist • Domino • Iron Man • Gamora • Luke Cage • Medusa • Quicksilver • Okoye • Scarlet Witch • Scarlet Witch • She-Hulk • Shuri • Thor, Prince of Asgard • Storm • Vision • Valkyrie • War Machine • Wasp • Wasp ASGARD • Wolverine BLACK ORDER • Thor, Prince of Asgard (k) • Angela • Thanos, The Mad Titan (k) • Enchantress • Black Dwarf • Hela, Queen of Hel • Corvus Glaive • Loki, God of Mischief • Ebony Maw • Valkyrie • Proxima Midnight AVENGERS BROTHERHOOD OF MUTANTS • Captain America (Steve Rogers) (k) • Magneto (k) • Captain America (Sam Wilson) (k) • Mystique (k) • Ant-Man • Juggernaut • Beast • Quicksilver • Black Panther • Sabretooth • Black Widow • Scarlet Witch • Black Widow, Agent of S.H.I.E.L.D. • Toad Atomic Mass Games and logo are TM of Atomic Mass Games. Atomic Mass Games, 1995 County Road B2 W, Roseville, MN, 55113, USA, 1-651-639-1905. © 2021 MARVEL Actual components may vary from those shown. CABAL DARK DIMENSION • Red Skull (k) • Dormammu (k) • Sin (k) DEFENDERS • Baron Zemo • Doctor Strange (k) • Bob, Agent of Hydra • Amazing Spider-Man • Bullseye • Blade • Cassandra Nova • Daredevil • Crossbones • Ghost Rider • Enchantress • Hawkeye • Killmonger • Hulk • Kingpin • Iron Fist • Loki, God of Mischief • Luke Cage • Magneto • Moon Knight • Mister Sinister • Scarlet Witch • M.O.D.O.K. • Spider-Man (Peter Parker) • Mysterio • Valkyrie • Mystique • Wolverine • Omega Red • Wong • Sabretooth GUARDIANS OF THE GALAXY • Ultron k • Viper • Star-Lord ( ) CRIMINAL SYNDICATE • Angela • Drax the Destroyer • Kingpin (k) • Gamora • Black Cat • Groot • Bullseye • Nebula • Crossbones • Rocket Raccoon • Green Goblin • Ronan the Accuser • Killmonger INHUMANS • Kraven the Hunter • M.O.D.O.K.