Misuse Patterns for the SSL/TLS Protocol
Total Page:16
File Type:pdf, Size:1020Kb
Load more
Recommended publications
-

The Transport Layer: Tutorial and Survey SAMI IREN and PAUL D
The Transport Layer: Tutorial and Survey SAMI IREN and PAUL D. AMER University of Delaware AND PHILLIP T. CONRAD Temple University Transport layer protocols provide for end-to-end communication between two or more hosts. This paper presents a tutorial on transport layer concepts and terminology, and a survey of transport layer services and protocols. The transport layer protocol TCP is used as a reference point, and compared and contrasted with nineteen other protocols designed over the past two decades. The service and protocol features of twelve of the most important protocols are summarized in both text and tables. Categories and Subject Descriptors: C.2.0 [Computer-Communication Networks]: General—Data communications; Open System Interconnection Reference Model (OSI); C.2.1 [Computer-Communication Networks]: Network Architecture and Design—Network communications; Packet-switching networks; Store and forward networks; C.2.2 [Computer-Communication Networks]: Network Protocols; Protocol architecture (OSI model); C.2.5 [Computer- Communication Networks]: Local and Wide-Area Networks General Terms: Networks Additional Key Words and Phrases: Congestion control, flow control, transport protocol, transport service, TCP/IP 1. INTRODUCTION work of routers, bridges, and communi- cation links that moves information be- In the OSI 7-layer Reference Model, the tween hosts. A good transport layer transport layer is the lowest layer that service (or simply, transport service) al- operates on an end-to-end basis be- lows applications to use a standard set tween two or more communicating of primitives and run on a variety of hosts. This layer lies at the boundary networks without worrying about differ- between these hosts and an internet- ent network interfaces and reliabilities. -
Moving to Ipv6(PDF)
1 Chicago, IL 9/1/15 2 Moving to IPv6 Mark Kosters, Chief Technology Officer With some help from Geoff Huston 3 The Amazing Success of the Internet • 2.92 billion users! • 4.5 online hours per day per user! • 5.5% of GDP for G-20 countries Just about anything about the Internet Time 3 4 Success-Disaster 5 The Original IPv6 Plan - 1995 Size of the Internet IPv6 Deployment IPv6 Transition – Dual Stack IPv4 Pool Size Time 6 The Revised IPv6 Plan - 2005 IPv4 Pool Size Size of the Internet IPv6 Transition – Dual Stack IPv6 Deployment 2004 2006 2008 2010 2012 Date 7 Oops! We were meant to have completed the transition to IPv6 BEFORE we completely exhausted the supply channels of IPv4 addresses! 8 Today’s Plan IPv4 Pool Size Today Size of the Internet ? IPv6 Transition IPv6 Deployment 0.8% Time 9 Transition... The downside of an end-to-end architecture: – There is no backwards compatibility across protocol families – A V6-only host cannot communicate with a V4-only host We have been forced to undertake a Dual Stack transition: – Provision the entire network with both IPv4 AND IPv6 – In Dual Stack, hosts configure the hosts’ applications to prefer IPv6 to IPv4 – When the traffic volumes of IPv4 dwindle to insignificant levels, then it’s possible to shut down support for IPv4 10 Dual Stack Transition ... We did not appreciate the operational problems with this dual stack plan while it was just a paper exercise: • The combination of an end host preference for IPv6 and a disconnected set of IPv6 “islands” created operational problems – Protocol -

Routing Loop Attacks Using Ipv6 Tunnels
Routing Loop Attacks using IPv6 Tunnels Gabi Nakibly Michael Arov National EW Research & Simulation Center Rafael – Advanced Defense Systems Haifa, Israel {gabin,marov}@rafael.co.il Abstract—IPv6 is the future network layer protocol for A tunnel in which the end points’ routing tables need the Internet. Since it is not compatible with its prede- to be explicitly configured is called a configured tunnel. cessor, some interoperability mechanisms were designed. Tunnels of this type do not scale well, since every end An important category of these mechanisms is automatic tunnels, which enable IPv6 communication over an IPv4 point must be reconfigured as peers join or leave the tun- network without prior configuration. This category includes nel. To alleviate this scalability problem, another type of ISATAP, 6to4 and Teredo. We present a novel class of tunnels was introduced – automatic tunnels. In automatic attacks that exploit vulnerabilities in these tunnels. These tunnels the egress entity’s IPv4 address is computationally attacks take advantage of inconsistencies between a tunnel’s derived from the destination IPv6 address. This feature overlay IPv6 routing state and the native IPv6 routing state. The attacks form routing loops which can be abused as a eliminates the need to keep an explicit routing table at vehicle for traffic amplification to facilitate DoS attacks. the tunnel’s end points. In particular, the end points do We exhibit five attacks of this class. One of the presented not have to be updated as peers join and leave the tunnel. attacks can DoS a Teredo server using a single packet. The In fact, the end points of an automatic tunnel do not exploited vulnerabilities are embedded in the design of the know which other end points are currently part of the tunnels; hence any implementation of these tunnels may be vulnerable. -

Lecture 11: PKI, SSL and VPN Information Security – Theory Vs
Lecture 11: PKI, SSL and VPN Information Security – Theory vs. Reality 0368-4474-01, Winter 2011 Yoav Nir ©2011 Check Point Software Technologies Ltd. | [Restricted] ONLY for designated groups and individuals What is VPN ° VPN stands for Virtual Private Network ° A private network is pretty obvious – An Ethernet LAN running in my building – Wifi with access control – A locked door and thick walls can be access control – An optical fiber running between two buildings ©2011 Check Point Software Technologies Ltd. 2 What is a VPN ° What is a non-private network? – Obviously, someone else’s network. ° Obvious example: the Internet. ° The Internet is pretty fast, and really cheap. ° What do I do if I have offices in several cities – And people working from home – And sales people working from who knows where ° We could use the Internet, but… – People could see my data – People could modify my messsages – People could pretend to be other people ©2011 Check Point Software Technologies Ltd. 3 What is a VPN ° I could run my own cables around the world. ° I could buy an MPLS connection from a local telco – Bezeq would love to sell me one. They call it IPVPN, and it’s pretty much a switched link just for my company – But I can’t get that to the home or mobile users – And it’s mediocre (but consistent) speed – And Bezeq can still do whatever it wants – And it’s really expensive – The incremental cost of using the Internet is zero ° A virtual private network combines the relative low-cost of using the Internet with the privacy of a leased line. -
Ipsec and IKE Administration Guide
IPsec and IKE Administration Guide Sun Microsystems, Inc. 4150 Network Circle Santa Clara, CA 95054 U.S.A. Part No: 816–7264–10 April 2003 Copyright 2003 Sun Microsystems, Inc. 4150 Network Circle, Santa Clara, CA 95054 U.S.A. All rights reserved. This product or document is protected by copyright and distributed under licenses restricting its use, copying, distribution, and decompilation. No part of this product or document may be reproduced in any form by any means without prior written authorization of Sun and its licensors, if any. Third-party software, including font technology, is copyrighted and licensed from Sun suppliers. Parts of the product may be derived from Berkeley BSD systems, licensed from the University of California. UNIX is a registered trademark in the U.S. and other countries, exclusively licensed through X/Open Company, Ltd. Sun, Sun Microsystems, the Sun logo, docs.sun.com, AnswerBook, AnswerBook2, SunOS, Sun ONE Certificate Server, and Solaris are trademarks, registered trademarks, or service marks of Sun Microsystems, Inc. in the U.S. and other countries. All SPARC trademarks are used under license and are trademarks or registered trademarks of SPARC International, Inc. in the U.S. and other countries. Products bearing SPARC trademarks are based upon an architecture developed by Sun Microsystems, Inc. The OPEN LOOK and Sun™ Graphical User Interface was developed by Sun Microsystems, Inc. for its users and licensees. Sun acknowledges the pioneering efforts of Xerox in researching and developing the concept of visual or graphical user interfaces for the computer industry. Sun holds a non-exclusive license from Xerox to the Xerox Graphical User Interface, which license also covers Sun’s licensees who implement OPEN LOOK GUIs and otherwise comply with Sun’s written license agreements. -
An Introduction to the Identifier-Locator Network Protocol (ILNP)
An Introduction to the Identifier-Locator Network Protocol (ILNP) Presented by Joel Halpern Material prepared by Saleem N. Bhatti & Ran Atkinson https://ilnp.cs.st-andrews.ac.uk/ IETF102, Montreal, CA. (C) Saleem Bhatti, 21 June 2018. 1 Thanks! • Joel Halpern: presenting today! • Ran Atkinson: co-conspirator. • Students at the University of St Andrews: • Dr Ditchaphong Phoomikiatissak (Linux) • Dr Bruce Simpson (FreeBSD, Cisco) • Khawar Shezhad (DNS/Linux, Verisign) • Ryo Yanagida (Linux, Time Warner) • … many other students on sub-projects … • IRTF (Routing RG, now concluded) • Discussions on various email lists. IETF102, Montreal, CA. (C) Saleem Bhatti, 21 June 2018. 2 Background to Identifier-Locator IETF102, Montreal, CA. (C) Saleem Bhatti, 21 June 2018. 3 “IP addresses considered harmful” • “IP addresses considered harmful” Brian E. Carpenter ACM SIGCOMM CCR, vol. 44, issue 2, Apr 2014 http://dl.acm.org/citation.cfm?id=2602215 http://dx.doi.org/10.1145/2602204.2602215 • Abstract This note describes how the Internet has got itself into deep trouble by over-reliance on IP addresses and discusses some possible ways forward. IETF102, Montreal, CA. (C) Saleem Bhatti, 21 June 2018. 4 RFC2104 (I), IAB, Feb 1997 • RFC2104, “IPv4 Address Behaviour Today”. • Ideal behaviour of Identifiers and Locators: Identifiers should be assigned at birth, never change, and never be re-used. Locators should describe the host's position in the network's topology, and should change whenever the topology changes. Unfortunately neither of the these ideals are met by IPv4 addresses. IETF102, Montreal, CA. (C) Saleem Bhatti, 21 June 2018. 5 RFC6115 (I), Feb 2011 • RFC6115, “Recommendation for a Routing Architecture”. -
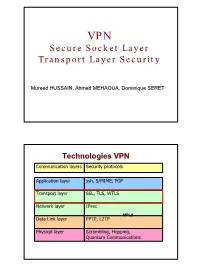
Secure Socket Layer Transport Layer Security
VPN Secure Socket Layer Transport Layer Security Mureed HUSSAIN, Ahmed MEHAOUA, Dominique SERET Technologies VPN Communication layers Security protocols Application layer ssh, S/MIME, PGP Transport layer SSL, TLS, WTLS Network layer IPsec MPLS Data Link layer PPTP, L2TP Physical layer Scrambling, Hopping, Quantum Communications 1 Agenda • Introduction – Motivation, evolution, standardization – Applications • SSL Protocol – SSL phases and services – Sessions and connections – SSL protocols and layers • SSL Handshake protocol • SSL Record protocol / layer • SSL solutions and products • Conclusion Sécurisation des échanges • Pour sécuriser les échanges ayant lieu sur le réseau Internet, il existe plusieurs approches : - niveau applicatif (PGP) - niveau réseau (protocole IPsec) - niveau physique (boîtiers chiffrant). • TLS/SSL vise à sécuriser les échanges au niveau de la couche Transport. • Application typique : sécurisation du Web 2 Transport Layer Security • Advantages – Does not require enhancement to each application – NAT friendly – Firewall Friendly • Disadvantages – Embedded in the application stack (some mis-implementation) – Protocol specific --> need to duplicated for each transport protocol – Need to maintain context for connection (not currently implemented for UDP) – Doesn’t protect IP adresses & headers Security-Sensitive Web Applications • Online banking • Online purchases, auctions, payments • Restricted website access • Software download • Web-based Email • Requirements – Authentication: Of server, of client, or (usually) -
Ipsec and IKE Administration Guide
IPsec and IKE Administration Guide Sun Microsystems, Inc. 4150 Network Circle Santa Clara, CA 95054 U.S.A. Part No: 817–2694–10 December 2003 Copyright 2003 Sun Microsystems, Inc. 4150 Network Circle, Santa Clara, CA 95054 U.S.A. All rights reserved. This product or document is protected by copyright and distributed under licenses restricting its use, copying, distribution, and decompilation. No part of this product or document may be reproduced in any form by any means without prior written authorization of Sun and its licensors, if any. Third-party software, including font technology, is copyrighted and licensed from Sun suppliers. Parts of the product may be derived from Berkeley BSD systems, licensed from the University of California. UNIX is a registered trademark in the U.S. and other countries, exclusively licensed through X/Open Company, Ltd. Sun, Sun Microsystems, the Sun logo, docs.sun.com, AnswerBook, AnswerBook2, Sun Crypto Accelerator 1000, Sun Crypto Accelerator 4000 and Solaris are trademarks, registered trademarks, or service marks of Sun Microsystems, Inc. in the U.S. and other countries. All SPARC trademarks are used under license and are trademarks or registered trademarks of SPARC International, Inc. in the U.S. and other countries. Products bearing SPARC trademarks are based upon an architecture developed by Sun Microsystems, Inc. The OPEN LOOK and Sun™ Graphical User Interface was developed by Sun Microsystems, Inc. for its users and licensees. Sun acknowledges the pioneering efforts of Xerox in researching and developing the concept of visual or graphical user interfaces for the computer industry. Sun holds a non-exclusive license from Xerox to the Xerox Graphical User Interface, which license also covers Sun’s licensees who implement OPEN LOOK GUIs and otherwise comply with Sun’s written license agreements. -

(12) Patent Application Publication (10) Pub. No.: US 2003/0223446A1 Lewin Et Al
US 2003O223446A1 (19) United States (12) Patent Application Publication (10) Pub. No.: US 2003/0223446A1 Lewin et al. (43) Pub. Date: Dec. 4, 2003 (54) SYSTEM FOR ENCAPSULATING (52) U.S. Cl. ............................................ 370/419,375/220 ETHERNET FRAMES OVERVERY HIGH SPEED DIGITAL SUBSCRIBER LINES (57) ABSTRACT (75) Inventors: Amit Lewin, Tel Aviv (IL); Opher An apparatus for and method of encapsulating Ethernet Yaron, Tel Aviv (IL); Alon Hurwitz, frame data in Very high speed Digital Subscriber Line Ramat Gan (IL); Yuri Poddobny, (VDSL) frames. The VDSL frames are transmitted over a Herzelia (IL) point to point VDSL link where they are subsequently extracted and forwarded as standard Ethernet frames. The Correspondence Address: VDSL facility transport system comprises an Ethernet to Edward K. Runyan VDSL Consumer Premises Equipment (CPE) coupled to a McDonnell Boehnen Hulbert & Berghoff DSL Access Multiplexor (DSLAM) over a VDSL transport 32nd Floor facility. The Ethernet to VDSL CPE functions to receive a 300 S. Wacker Drive 10BaseTEthernet signal and encapsulate the Ethernet frame Chicago, IL 60606 (US) into a VDSL frame for transmission over the VDSL facility. The DSLAM is adapted to receive VDSL frames, extract (73) Assignee: 3COM CORPORATION Ethernet frames therefrom and generate and output a stan dard Ethernet Signal. Ethernet frames are encapsulated (21) Appl. No.: 10/430,480 within VDSL frames and transmitted on the wire pair without regard to the state of the SOC signals. This over (22) Filed: May 6, 2003 comes the problems associated with Syncing the transmis Related U.S. Application Data sion of the Ethernet data with the SOC signals. -

Design Philosophy of the DARPA Internet Protocols
THE DESIGN PHILOSOPHY OF THE DARPA INTERNET PROTOCOL~S David D. Clark Massachusetts Institute of Technology Laboratory for Computer Science Cambridge, Ma. 02139 While specific information on the DOD protocols is fairly generally available’, 6. ‘, it is sometimes difficult to Abstract determine the motivation and reasoning which led to the design. The Internet protocol suite, TCP/IP, was first proposed fifteen years ago. It was developed by the Defense In fact, the design philosophy has evolved considerably Advanced Research Projects Agency (DARPA), and has from the first proposal to the current standards. For been used widely in military and commercial systems. example, the idea of the datagram, or connectionless While there have been papers and specifications that service, does not receive particular emphasis in the first describe how the protocols work, it is sometimes difficult paper, but has come to be the defining characteristic of to deduce from these why the protocol is as it is. For the protocol. Another example is the layering of the example, the Internet protocol is based on a architecture into the IP and TCP layers. This seems basic connectionless or datagram mode of service. The to the design, but was also not a part of the original motivation for this has been greatly misunderstood. This proposal. These changes in the Internet design arose paper attempts to capture some of the early reasoning through the repeated pattern of implementation and which shaped the Internet protocols. testing that occurred before the standards were set. The Internet architecture is still evolving. Sometimes a new extension challenges one of the design principles, I. -

ISO-TSAP-C2, Page 73 • ISO-TSAP, Page 74 • ITM-MCELL-S, Page 75 • ITUNES, Page 76 • JARGON, Page 77
IAFDBASE through JARGON • I-NLSP, page 4 • IAFDBASE, page 5 • IAFSERVER, page 6 • IASD, page 7 • IATP, page 8 • IAX, page 9 • IBM-APP, page 10 • IBM-DB2, page 11 • IBM-DIRECTOR, page 12 • IBPROTOCOL, page 13 • ICLCNET-LOCATE, page 14 • ICLCNET_SVINFO, page 15 • ICLOUD, page 16 • ICMP, page 17 • ICQ-FILETRANSFER, page 18 • ICQ, page 19 • IDFP, page 20 • IDPR-CMTP, page 21 • IDPR, page 22 • IDRP, page 23 • IEEE-MMS-SSL, page 24 • IEEE-MMS, page 25 • IFMP, page 26 • IGRP, page 27 NBAR2 Protocol Pack 8.0.0 1 IAFDBASE through JARGON • IIOP, page 28 • IL, page 29 • IMAP, page 30 • IMSP, page 31 • INBUSINESS, page 32 • INFOSEEK, page 33 • INGRES-NET, page 34 • INTECOURIER, page 35 • INTEGRA-SME, page 36 • INTRINSA, page 37 • IP-MESSENGER, page 38 • IPCD, page 39 • IPCOMP, page 40 • IPCSERVER, page 41 • IPCV, page 42 • IPDD, page 43 • IPINIP, page 44 • IPIP, page 45 • IPLT, page 46 • IP-MESSENGER, page 47 • IPP, page 48 • IPPC, page 49 • IPSEC, page 50 • IPV6-FRAG, page 51 • IPV6-ICMP, page 52 • IPV6-NONXT, page 53 • IPV6-OPTS, page 54 • IPV6-ROUTE, page 55 • IPV6INIP, page 56 • IPX-IN-IP, page 57 • IRC-SERV, page 58 • IRC, page 59 • IRTP, page 60 NBAR2 Protocol Pack 8.0.0 2 IAFDBASE through JARGON • IS99C, page 61 • IS99S, page 62 • ISAKMP, page 63 • ISATAP-IPV6-TUNNELED, page 64 • ISCSI-TARGET, page 65 • ISCSI, page 66 • ISI-GL, page 67 • ISIS, page 68 • ISO-ILL, page 69 • ISO-IP, page 70 • ISO-TP0, page 71 • ISO-TP4, page 72 • ISO-TSAP-C2, page 73 • ISO-TSAP, page 74 • ITM-MCELL-S, page 75 • ITUNES, page 76 • JARGON, page 77 NBAR2 Protocol Pack 8.0.0 3 IAFDBASE through JARGON I-NLSP I-NLSP Name/CLI Keyword i-nlsp Full Name Integrated Net Layer Security Protocol Description Integrated Net Layer Security Protocol (i-nlsp) was a proposition that might have been used by End Systems (ESs) and Intermediate Systems (ISs) in order to provide security services in support of TUBA (TCP and UDP with Bigger Addresses). -

Packet Loss Internet Protocol Stack Chapter 2: Application Layer
Last Course Review: Delay in packet-switched networks Four sources of packet delay 3. Transmission delay: 4. Propagation delay: R=link bandwidth (bps) d = length of physical link 1. nodal processing: 2. queueing s = propagation speed in check bit errors time waiting at output L=packet length (bits) 8 determine output link link for transmission time to send bits into medium (~2x10 m/sec) deppgends on congestion link = L/R pppgropagation delay = d/s level of router transmission Note: s and R are very A different quantities! propagation transmission A propagation B nodal processing queueing B nodal processing queueing Introduction 1-1 Introduction 1-2 Packet loss Internet protocol stack application: supporting network queue (aka buffer) preceding link in buffer applications application has finite capacity FTP, SMTP, STTP when packet arrives to full queue, packet is transport: host-host data transfer transport dropped (aka lost) TCP, UDP lost packet may be retransmitted by network: routing of datagrams from network source to destination previous node, by source end system, or IP, routing protocols link not retransmitted at all link: data transfer between neighboring network elements physical PPP, Ethernet physical: bits “on the wire” Introduction 1-3 Introduction 1-4 Chapter 2: Application layer Chapter 2: Application Layer Our goals: learn about protocols 2.1 Principles of conceptual, by examining popular network applications implementation application-level 2.2 Web and HTTP aspects of network protocols 2.3 FTP application protocols HTTP 242.4 Elec tron ic Ma il transport-layer FPFTP SMTP, POP3, IMAP service models SMTP / POP3 / IMAP DNS 2.5 DNS client-server 2.6 P2p file sharing paradigm peer-to-peer paradigm Introduction 1-5 Introduction 1-6 1 Some network apps Creating a network app application Write programs that transport E-mail Internet telephone network run on different end data link Web Real-time video systems and physical Instant messaging conference communicate over a network.