Efficient Multiple-ISA Embedded Processor Core Design Based on RISC-V
Total Page:16
File Type:pdf, Size:1020Kb
Load more
Recommended publications
-

1 Assembly Language Programming Status Flags the Status Flags Reflect the Outcomes of Arithmetic and Logical Operations Performe
Assembly Language Programming Status Flags The status flags reflect the outcomes of arithmetic and logical operations performed by the CPU. • The carry flag (CF) is set when the result of an unsigned arithmetic operation is too large to fit into the destination. • The overflow flag (OF) is set when the result of a signed arithmetic operation is too large or too small to fit into the destination. • The sign flag (SF) is set when the result of an arithmetic or logical operation generates a negative result. • The zero flag (ZF) is set when the result of an arithmetic or logical operation generates a result of zero. Assembly Programs We are going to run assembly programs from (http://www.kipirvine.com/asm/) using Visual Studio. I have downloaded all of the example programs and placed them in CS430 Pub. Copy them onto your local machine and start up Visual Studio. The first program we are going to run is below. Copy this into the Project_Sample project in the examples folder. Run the program. Let’s talk about what this program does. TITLE Add and Subtract ; This program ; Last update: 06/01/2006 INCLUDE Irvine32.inc .code main PROC mov eax,10000h add eax,40000h sub eax,20000h call DumpRegs exit main ENDP END main 1 What’s the difference between the previous program and this one: TITLE Add and Subtract, Version 2 (AddSub2.asm) ; This program adds and subtracts 32-bit integers ; and stores the sum in a variable. ; Last update: 06/01/2006 INCLUDE Irvine32.inc .data val1 dword 10000h val2 dword 40000h val3 dword 20000h finalVal dword ? .code main PROC mov eax,val1 ; start with 10000h add eax,val2 ; add 40000h sub eax,val3 ; subtract 20000h mov finalVal,eax ; store the result (30000h) call DumpRegs ; display the registers exit main ENDP END main Data Transfer Instructions The MOV instruction copies from a source operand to a destination operand. -
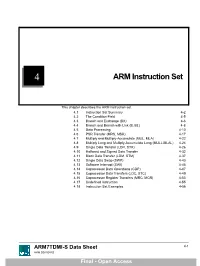
ARM Instruction Set
4 ARM Instruction Set This chapter describes the ARM instruction set. 4.1 Instruction Set Summary 4-2 4.2 The Condition Field 4-5 4.3 Branch and Exchange (BX) 4-6 4.4 Branch and Branch with Link (B, BL) 4-8 4.5 Data Processing 4-10 4.6 PSR Transfer (MRS, MSR) 4-17 4.7 Multiply and Multiply-Accumulate (MUL, MLA) 4-22 4.8 Multiply Long and Multiply-Accumulate Long (MULL,MLAL) 4-24 4.9 Single Data Transfer (LDR, STR) 4-26 4.10 Halfword and Signed Data Transfer 4-32 4.11 Block Data Transfer (LDM, STM) 4-37 4.12 Single Data Swap (SWP) 4-43 4.13 Software Interrupt (SWI) 4-45 4.14 Coprocessor Data Operations (CDP) 4-47 4.15 Coprocessor Data Transfers (LDC, STC) 4-49 4.16 Coprocessor Register Transfers (MRC, MCR) 4-53 4.17 Undefined Instruction 4-55 4.18 Instruction Set Examples 4-56 ARM7TDMI-S Data Sheet 4-1 ARM DDI 0084D Final - Open Access ARM Instruction Set 4.1 Instruction Set Summary 4.1.1 Format summary The ARM instruction set formats are shown below. 3 3 2 2 2 2 2 2 2 2 2 2 1 1 1 1 1 1 1 1 1 1 9876543210 1 0 9 8 7 6 5 4 3 2 1 0 9 8 7 6 5 4 3 2 1 0 Cond 0 0 I Opcode S Rn Rd Operand 2 Data Processing / PSR Transfer Cond 0 0 0 0 0 0 A S Rd Rn Rs 1 0 0 1 Rm Multiply Cond 0 0 0 0 1 U A S RdHi RdLo Rn 1 0 0 1 Rm Multiply Long Cond 0 0 0 1 0 B 0 0 Rn Rd 0 0 0 0 1 0 0 1 Rm Single Data Swap Cond 0 0 0 1 0 0 1 0 1 1 1 1 1 1 1 1 1 1 1 1 0 0 0 1 Rn Branch and Exchange Cond 0 0 0 P U 0 W L Rn Rd 0 0 0 0 1 S H 1 Rm Halfword Data Transfer: register offset Cond 0 0 0 P U 1 W L Rn Rd Offset 1 S H 1 Offset Halfword Data Transfer: immediate offset Cond 0 -

Multiplication and Division Instructions
MultiplicationMultiplication andand DivisionDivision InstructionsInstructions • MUL Instruction • IMUL Instruction • DIV Instruction • Signed Integer Division • Implementing Arithmetic Expressions Irvine, Kip R. Assembly Language for Intel-Based Computers, 2003. 1 MULMUL InstructionInstruction • The MUL (unsigned multiply) instruction multiplies an 8-, 16-, or 32-bit operand by either AL, AX, or EAX. • The instruction formats are: MUL r/m8 MUL r/m16 MUL r/m32 Implied operands: Irvine, Kip R. Assembly Language for Intel-Based Computers, 2003. 2 MULMUL ExamplesExamples 100h * 2000h, using 16-bit operands: .data val1 WORD 2000h The Carry flag indicates whether or val2 WORD 100h not the upper half of .code the product contains mov ax,val1 significant digits. mul val2 ; DX:AX = 00200000h, CF=1 12345h * 1000h, using 32-bit operands: mov eax,12345h mov ebx,1000h mul ebx ; EDX:EAX = 0000000012345000h, CF=0 Irvine, Kip R. Assembly Language for Intel-Based Computers, 2003. 3 YourYour turnturn .. .. .. What will be the hexadecimal values of DX, AX, and the Carry flag after the following instructions execute? mov ax,1234h mov bx,100h mul bx DX = 0012h, AX = 3400h, CF = 1 Irvine, Kip R. Assembly Language for Intel-Based Computers, 2003. 4 YourYour turnturn .. .. .. What will be the hexadecimal values of EDX, EAX, and the Carry flag after the following instructions execute? mov eax,00128765h mov ecx,10000h mul ecx EDX = 00000012h, EAX = 87650000h, CF = 1 Irvine, Kip R. Assembly Language for Intel-Based Computers, 2003. 5 IMULIMUL InstructionInstruction • IMUL (signed integer multiply ) multiplies an 8-, 16-, or 32-bit signed operand by either AL, AX, or EAX • Preserves the sign of the product by sign-extending it into the upper half of the destination register Example: multiply 48 * 4, using 8-bit operands: mov al,48 mov bl,4 imul bl ; AX = 00C0h, OF=1 OF=1 because AH is not a sign extension of AL. -

Overview of IA-32 Assembly Programming
Overview of IA-32 assembly programming Lars Ailo Bongo University of Tromsø Contents 1 Introduction ...................................................................................................................... 2 2 IA-32 assembly programming.......................................................................................... 3 2.1 Assembly Language Statements................................................................................ 3 2.1 Modes........................................................................................................................4 2.2 Registers....................................................................................................................4 2.2.3 Data Registers .................................................................................................... 4 2.2.4 Pointer and Index Registers................................................................................ 4 2.2.5 Control Registers................................................................................................ 5 2.2.6 Segment registers ............................................................................................... 7 2.3 Addressing................................................................................................................. 7 2.3.1 Bit and Byte Order ............................................................................................. 7 2.3.2 Data Types......................................................................................................... -
Assembly Language: IA-X86
Assembly Language for x86 Processors X86 Processor Architecture CS 271 Computer Architecture Purdue University Fort Wayne 1 Outline Basic IA Computer Organization IA-32 Registers Instruction Execution Cycle Basic IA Computer Organization Since the 1940's, the Von Neumann computers contains three key components: Processor, called also the CPU (Central Processing Unit) Memory and Storage Devices I/O Devices Interconnected with one or more buses Data Bus Address Bus data bus Control Bus registers Processor I/O I/O IA: Intel Architecture Memory Device Device (CPU) #1 #2 32-bit (or i386) ALU CU clock control bus address bus Processor The processor consists of Datapath ALU Registers Control unit ALU (Arithmetic logic unit) Performs arithmetic and logic operations Control unit (CU) Generates the control signals required to execute instructions Memory Address Space Address Space is the set of memory locations (bytes) that are addressable Next ... Basic Computer Organization IA-32 Registers Instruction Execution Cycle Registers Registers are high speed memory inside the CPU Eight 32-bit general-purpose registers Six 16-bit segment registers Processor Status Flags (EFLAGS) and Instruction Pointer (EIP) 32-bit General-Purpose Registers EAX EBP EBX ESP ECX ESI EDX EDI 16-bit Segment Registers EFLAGS CS ES SS FS EIP DS GS General-Purpose Registers Used primarily for arithmetic and data movement mov eax 10 ;move constant integer 10 into register eax Specialized uses of Registers eax – Accumulator register Automatically -

CS221 Booleans, Comparison, Jump Instructions Chapter 6 Assembly Language Is a Great Choice When It Comes to Working on Individu
CS221 Booleans, Comparison, Jump Instructions Chapter 6 Assembly language is a great choice when it comes to working on individual bits of data. While some languages like C and C++ include bitwise operators, several high-level languages are missing these operations entirely (e.g. Visual Basic 6.0). At times these operations can be quite useful. First we will describe some common bit operations, and then discuss conditional jumps. AND Instruction The AND instruction performs a Boolean AND between all bits of the two operands. For example: mov al, 00111011b and al, 00001111b The result is that AL contains 00001011. We have “multiplied” each corresponding bit. We have used AND for a common operation in this case, to clear out the high nibble. Sometimes the operand we are AND’ing something with is called a bit mask because wherever there is a zero the result is zero (masking out the original data), and wherever we have a one, we copy the original data through the mask. For example, consider an ASCII character. “Low” ASCII ignores the high bit; we only need the low 7 bits and we might use the high bit for either special characters or perhaps as a parity bit. Given an arbitrary 8 bits for a character, we could apply a mask that removes the high bit and only retains the low bits: and al, 01111111b OR Instruction The OR instruction performs a Boolean OR between all bits of the two operands. For example: mov al, 00111011b or al, 00001111b As a result AL contains 00111111. We have “Added” each corresponding bit, throwing away the carry. -
Instruction Set Architecture
Instruction Set Architecture EE3376 1 –Adapted from notes from BYU ECE124 Topics to Cover… l MSP430 ISA l MSP430 Registers, ALU, Memory l Instruction Formats l Addressing Modes l Double Operand Instructions l Single Operand Instructions l Jump Instructions l Emulated Instructions – http://en.wikipedia.org/wiki/TI_MSP430 2 –Adapted from notes from BYU ECE124 Levels of Transformation –Problems –Algorithms – C Instructions –Language (Program) –Programmable –Assembly Language – MSP 430 ISA –Machine (ISA) Architecture –Computer Specific –Microarchitecture –Manufacturer Specific –Circuits –Devices 3 –Adapted from notes from BYU ECE124 Instruction Set Architecture l The computer ISA defines all of the programmer-visible components and operations of the computer – memory organization l address space -- how may locations can be addressed? l addressibility -- how many bits per location? – register set (a place to store a collection of bits) l how many? what size? how are they used? – instruction set l Opcodes (operation selection codes) l data types (data types: byte or word) l addressing modes (coding schemes to access data) l ISA provides all information needed for someone that wants to write a program in machine language (or translate 4 from a high-level language to machine language). –Adapted from notes from BYU ECE124 MSP430 Instruction Set Architecture l MSP430 CPU specifically designed to allow the use of modern programming techniques, such as: – the computation of jump addresses – data processing in tables – use of high-level languages such as C. l 64KB memory space with 16 16-bit registers that reduce fetches to memory. l Implements RISC architecture with 27 instructions and 7 addressing modes. -
CS107, Lecture 13 Assembly: Control Flow and the Runtime Stack
CS107, Lecture 13 Assembly: Control Flow and The Runtime Stack Reading: B&O 3.6 This document is copyright (C) Stanford Computer Science and Nick Troccoli, licensed under Creative Commons Attribution 2.5 License. All rights reserved. Based on slides created by Marty Stepp, Cynthia Lee, Chris Gregg, and others. 1 Learning Goals • Learn how assembly implements loops and control flow • Learn how assembly calls functions. 2 Plan For Today • Control Flow • Condition Codes • Assembly Instructions • Break: Announcements • Function Calls and the Stack 3 mov Variants • mov only updates the specific register bytes or memory locations indicated. • Exception: movl writing to a register will also set high order 4 bytes to 0. • Suffix sometimes optional if size can be inferred. 4 No-Op • The nop/nopl instructions are “no-op” instructions – they do nothing! • No-op instructions do nothing except increment %rip • Why? To make functions align on nice multiple-of-8 address boundaries. “Sometimes, doing nothing is the way to be most productive.” – Philosopher Nick 5 Mov • Sometimes, you’ll see the following: mov %ebx, %ebx • What does this do? It zeros out the top 32 register bits, because when mov is performed on an e- register, the rest of the 64 bits are zeroed out. 6 xor • Sometimes, you’ll see the following: xor %ebx, %ebx • What does this do? It sets %ebx to zero! May be more efficient than using mov. 7 Plan For Today • Control Flow • Condition Codes • Assembly Instructions • Break: Announcements • Function Calls and the Stack 8 Control • In C, we have control flow statements like if, else, while, for, etc. -

X86 Assembly Programming Part 2
x86 Assembly Programming Part 2 EECE416 uC Charles Kim Howard University Resources: Intel 80386 Programmers Reference Manual Essentials of 80x86 Assembly Language Introduction to 80x86 Assembly Language Programming WWW.MWFTR.COM Reminder – Coding Assignment Listing (.LST) File of Assembly Code (.asm) Registers for x86 Basic Data Types • Byte, Words (WORD), Double Words (DWORD) • Little-Endian • Align by 2 (word) or 4 (Dword) for better performance – instead of odd address Data Declaration • Directives for Data Declaration and Reservation of Memory – BYTE: Reserves 1 byte in memory •Example: D1 BYTE 20 D2 BYTE 00010100b String1 BYTE “Joe” ; [4A 6F 65] – WORD: 2 bytes are reserved • Example: num1 WORD -10 num2 WORD FFFFH – DWORD: 4 bytes are reserved •Example: N1 DWORD -10 – QWORD: 8 bytes • 64 bit: RAX RBX RCX ,etc • 32 bit: EDX:EAX Concatenation for CDQ instruction Instruction Format • Opcode: – specifies the operation performed by the instruction. • Register specifier – an instruction may specify one or two register operands. • Addressing-mode specifier – when present, specifies whether an operand is a register or memory location. • Displacement – when the addressing-mode specifier indicates that a displacement will be used to compute the address of an operand, the displacement is encoded in the instruction. • Immediate operand – when present, directly provides the value of an operand of the instruction. Immediate operands may be 8, 16, or 32 bits wide. Register Size and Data • Assuming that the content of eax is [01FF01FF], what would -

Arithmetic and Logical Operations Chapter Nine
Arithmetic and Logical Operations Chapter Nine There is a lot more to assembly language than knowing the operations of a handful of machine instructions. You’ve got to know how to use them and what they can do. Many instructions are useful for operations that have little to do with their mathematical or obvious functions. This chapter discusses how to convert expressions from a high level language into assembly language. It also discusses advanced arithmetic and logical opera- tions including multiprecision operations and tricks you can play with various instruc- tions. 9.0 Chapter Overview This chapter discusses six main subjects: converting HLL arithmetic expressions into assembly language, logical expressions, extended precision arithmetic and logical opera- tions, operating on different sized operands, machine and arithmetic idioms, and masking operations. Like the preceding chapters, this chapter contains considerable material that you may need to learn immediately if you’re a beginning assembly language programmer. The sections below that have a “•” prefix are essential. Those sections with a “❏” discuss advanced topics that you may want to put off for a while. • Arithmetic expressions • Simple assignments • Simple expressions • Complex expressions • Commutative operators • Logical expressions • Multiprecision operations • Multiprecision addition operations • Multiprecision subtraction operations • Extended precision comparisons ❏ Extended precision multiplication ❏ Extended precision division ❏ Extended precision negation • Extended -

Term 2 Lecture 6
Assembly Language J. Vaughan Lecture Notes on Assembly Language - J. Vaughan 13. Instructions and data (ctd) From the NASM Manual: AND: Bitwise AND AND r/m8,reg8 ; 20 /r [8086] AND r/m16,reg16 ; o16 21 /r [8086] AND r/m32,reg32 ; o32 21 /r [386] AND reg8,r/m8 ; 22 /r [8086] AND reg16,r/m16 ; o16 23 /r [8086] AND reg32,r/m32 ; o32 23 /r [386] AND r/m8,imm8 ; 80 /4 ib [8086] AND r/m16,imm16 ; o16 81 /4 iw [8086] AND r/m32,imm32 ; o32 81 /4 id [386] AND r/m16,imm8 ; o16 83 /4 ib [8086] AND r/m32,imm8 ; o32 83 /4 ib [386] AND AL,imm8 ; 24 ib [8086] AND AX,imm16 ; o16 25 iw [8086] AND EAX,imm32 ; o32 25 id [386] AND performs a bitwise AND operation between its two operands (i.e. each bit of the result is 1 if and only if the corresponding bits of the two inputs were both 1), and stores the result in the destination (first) operand. The destination operand can be a register or a memory location. The source operand can be a register, a memory location or an immediate value. In the forms with an 8−bit immediate second operand and a longer first operand, the second operand is considered to be signed, and is sign−extended to the length of the first operand. In these cases, the BYTE qualifier is necessary to force NASM to generate this form of the instruction. CALL: Call Subroutine CALL imm ; E8 rw/rd [8086] CALL imm:imm16 ; o16 9A iw iw [8086] CALL imm:imm32 ; o32 9A id iw [386] CALL FAR mem16 ; o16 FF /3 [8086] CALL FAR mem32 ; o32 FF /3 [386] CALL r/m16 ; o16 FF /2 [8086] CALL r/m32 ; o32 FF /2 [386] CALL calls a subroutine, by means of pushing the current instruction pointer (IP) and optionally CS as well on the stack, and then jumping to a given address. -

Gnu Assembler
Using as The gnu Assembler (Sourcery G++ Lite 2010q1-188) Version 2.19.51 The Free Software Foundation Inc. thanks The Nice Computer Company of Australia for loaning Dean Elsner to write the first (Vax) version of as for Project gnu. The proprietors, management and staff of TNCCA thank FSF for distracting the boss while they gotsome work done. Dean Elsner, Jay Fenlason & friends Using as Edited by Cygnus Support Copyright c 1991, 92, 93, 94, 95, 96, 97, 98, 99, 2000, 2001, 2002, 2006, 2007, 2008, 2009 Free Software Foundation, Inc. Permission is granted to copy, distribute and/or modify this document under the terms of the GNU Free Documentation License, Version 1.3 or any later version published by the Free Software Foundation; with no Invariant Sections, with no Front-Cover Texts, and with no Back-Cover Texts. A copy of the license is included in the section entitled \GNU Free Documentation License". i Table of Contents 1 Overview :::::::::::::::::::::::::::::::::::::::: 1 1.1 Structure of this Manual :::::::::::::::::::::::::::::::::::::: 14 1.2 The GNU Assembler :::::::::::::::::::::::::::::::::::::::::: 15 1.3 Object File Formats::::::::::::::::::::::::::::::::::::::::::: 15 1.4 Command Line ::::::::::::::::::::::::::::::::::::::::::::::: 15 1.5 Input Files :::::::::::::::::::::::::::::::::::::::::::::::::::: 16 1.6 Output (Object) File:::::::::::::::::::::::::::::::::::::::::: 16 1.7 Error and Warning Messages :::::::::::::::::::::::::::::::::: 16 2 Command-Line Options::::::::::::::::::::::: 19 2.1 Enable Listings: `-a[cdghlns]'