Threat Spotlight: Protecting Your Business in 2021 Defend Against Evolving Phishing and Malware Attacks
Total Page:16
File Type:pdf, Size:1020Kb
Load more
Recommended publications
-
Email Security Gateway Keep Email-Borne Threats out of Your Network
DATASHEET Barracuda Email Security Gateway Keep email-borne threats out of your network. Get comprehensive email gateway security along with advanced capabilities that help you ensure business continuity—whether you host your email on-premises or in the cloud. Barracuda Email Security Gateway gives you industry-leading protection against spam, viruses, and advanced malware—including zero-day ransomware and other threats when Advanced Threat Protection is enabled. Outbound filtering prevents data loss, and 96-hour email spooling in the Barracuda Cloud ensures continuity in case of email server downtime. Email Security Gateway is available as a physical or virtual appliance, and in cloud-native versions on Amazon Web Services and Microsoft Azure. Comprehensive protection Complete email threat protection Unmatched ease of use for the long term The Barracuda Email Security Gateway Fast, easy set-up and simple, intuitive The Barracuda Email Security Gateway provides multi-layer security, email management keep time and resource includes spam and virus blocking, continuity, and data leakage prevention. needs low. The integration of the data protection, email continuity, DoS Advanced Threat Protection1 combines Barracuda Cloud Protection Layer prevention, encryption, and policy behavioral, heuristic, and sandboxing makes it easy to scale capacity as your management—combined to deliver a technologies to protect against zero business grows. complete solution. As new requirements hour, targeted attacks and ransomware. emerge, it is automatically -

Solution Brief Recovering from Ransomware with Barracuda Backup
Solution Brief Recovering from Ransomware with Barracuda Backup Ransomware is a malware variant that locks an end user’s computer or encrypts their files, then demands a sum of money to allow access or decryption. What’s worse, if an organization hands over the cash, there are often times when the attacker doesn’t play nice and still withholds the key even after payment. Ransomware is problematic for businesses because it not only results in financial loss, but also tainted credibility and lost productivity. However, this situation can be avoided if your organization has taken the steps to implement a ransomware prevention plan. In this solution brief, we will discuss some of the steps you can take to prevent ransomware attacks, as well as how to quickly recover from them using Barracuda Backup. Introduction Due to the sophistication of today’s threat landscape, ransomware can be difficult to catch right at the door. Once this malicious malware crosses the threshold, a business user is hit by a daunting message, informing the user that their computer and files have been seized, and payment is required. What’s equally perturbing is that ransomware doesn’t discriminate—it can happen to the mom and pop shops to large enterprises. It’s not a matter of if a business will get hit, but when. Protecting Your Organization from Ransomware Attackers have created many different variations of ransomware over the past few years, such as CryptoLocker, CryptoWall, TorrentLocker, TeslaCrypt, Locky, Petya, WannaCry, Bad Rabbit, and Samas. Each of these variations use new methods of infecting their victims’ computers, thereby compromising the data and network of many organizations worldwide. -

White Paper Barracuda • Barracuda’S Antivirus Technology
Barracuda’s Antivirus Technology White Paper Barracuda • Barracuda’s Antivirus Technology The Barracuda Networks anti-malware technology is purpose-built to solve the unique needs of email and Web security appliances. Unlike traditional antivirus technologies designed to work on desktop computers, Barracuda Networks anti-malware technology is specifically designed for: • Speed of response • Prioritizing malware threats that propagate quickly • Low false positives • Leveraging the resources of the free and open source (FOSS) security research community for maximum breadth With this combination of technologies specifically designed to meet these criteria over SMTP and HTTP protocols, Barracuda Networks is able to provide best-of-breed protection for customers of the Barracuda Email Security Gateway and Barracuda Web Security Gateway. In addition, Barracuda Networks also incorporates these technologies into Barracuda Message Archiver, Barracuda SSL VPN, and Barracuda Web Application Firewall. Speed of Response Like other antivirus research centers, Barracuda Labs, Barracuda Networks’ 24x7 threat operations center, maintains traps (or “honeypots”) on the Internet to collect threats and threat data. In addition, Barracuda Networks leverages aggregated and anonymous data from over 150,000 customer systems worldwide to collect and respond to data about the latest threats. These systems span small-to-medium businesses, educational institutions, government agencies, enterprises, and service providers that contribute to a diverse corpus of email and Web threat data on the Internet, representing over 1.5 billion emails and 75 billion Web requests per day. This threat data enables Barracuda Labs engineers to continually update the virus, spyware, and spam definitions that are offered as part of the Barracuda Energize Updates subscriptions on Barracuda Networks appliances. -

The Forrester Wave™: Enterprise Firewalls, Q3 2020 the 11 Providers That Matter Most and How They Stack up by David Holmes August 10, 2020
LICENSED FOR INDIVIDUAL USE ONLY The Forrester Wave™: Enterprise Firewalls, Q3 2020 The 11 Providers That Matter Most And How They Stack Up by David Holmes August 10, 2020 Why Read This Report Key Takeaways In our 34-criterion evaluation of enterprise firewall Palo Alto Networks And Cisco Lead The Pack providers, we identified the 11 most significant Forrester’s research uncovered a market in which ones — Barracuda Networks, Check Point Palo Alto Networks and Cisco are Leaders; Check Software Technologies, Cisco, Forcepoint, Fortinet, Point Software Technologies, Fortinet, Forcepoint, Huawei, Juniper Networks, Palo Alto Networks, Sophos, Juniper Networks, and Huawei are SonicWall, Sophos, and WatchGuard — and Strong Performers; and Barracuda Networks, researched, analyzed, and scored them. This WatchGuard, and SonicWall are Contenders. report shows how each provider measures up and Cloud And Zero Trust Are Key Differentiators helps security and risk professionals select the As legacy, on-premises technology becomes right one for their needs. outdated and less relevant, improved delivery and reach will dictate which providers will lead the pack. Vendors that can provide Zero Trust and cloud control position themselves to successfully deliver security and manageability to their customers. This PDF is only licensed for individual use when downloaded from forrester.com or reprints.forrester.com. All other distribution prohibited. FORRESTER.COM FOR SECURITY & RISK PROFESSIONALS The Forrester Wave™: Enterprise Firewalls, Q3 2020 The 11 Providers That Matter Most And How They Stack Up by David Holmes with Joseph Blankenship, Matthew Flug, and Peggy Dostie August 10, 2020 Table Of Contents Related Research Documents 2 Enterprise Firewalls Will Take Enterprises To The Forrester Wave™: Zero Trust eXtended The Zero Trust Edge Ecosystem Platform Providers, Q4 2019 3 Evaluation Summary Now Tech: Enterprise Firewalls, Q1 2020 8 Vendor Offerings 9 Vendor Profiles Leaders Share reports with colleagues. -
Capability Statement
Capability Statement About Barracuda Networks Barracuda simplifies IT with cloud-enabled solutions that empower customers to protect their networks, applications, and data, regardless of where they reside. These powerful, easy-to-use and affordable solutions are trusted by more than 150,000 organizations worldwide and are delivered in appliance, virtual appliance, cloud and hybrid deployments. Barracuda’s customer-centric business model focuses on delivering high-value, subscription-based IT solutions that provide end-to-end network and data security. Core Competencies Differentiators Security • Made in the USA Barracuda’s powerful, best-of-breed security products secure your organization's threat • Single source: one vendor for security, storage, vectors—email, web applications, remote access, web browsing, mobile Internet, and application delivery solutions and support network perimeters—whether on-premises or in the cloud. • Industry’s best customer service; email and phone support offered 24x7 Data Protection without any phone trees. You will actually speak to a live person. • Renowned ease-of-use makes Barracuda products and Easily secure your most important business data, emails, and applications while meeting users’ services fast to set up and easy to manage. needs for access across all their devices. The main concerns in this fast-growing category are in regards to compliance and business continuity. • Simple, competitive pricing makes Barracuda products affordable with no extraneous or unexpected costs, and provides low TCO and high ROI Application Delivery • FIPS 140-2 Consolidated Validation Certificate Enables organizations to provide reliable, fast, and secure access to applications through • Deployed in both NIPRNet and SIPRNet an integrated product family spanning traffic management, access control, and security for today’s modern and dispersed application deployment architectures. -
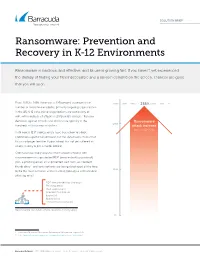
Ransomware: Prevention and Recovery in K-12 Environments
SOLUTION BRIEF Ransomware: Prevention and Recovery in K-12 Environments Ransomware is insidious, and effective, and its use is growing fast. If you haven’t yet experienced the dismay of finding your files inaccessible and a ransom demand on the screen, chances are good that you will soon. From 2018 to 2019, there was a 235-percent increase in the 235% number of ransomware attacks, primarily targeting organizations in the US. K-12 educational organizations are particularly at risk1, with hundreds of attacks in 2019 on US schools2. Ransom demands against schools and districts are typically in the Ransomware 200% hundreds of thousands of dollars. attack increase from 2018–2019 Until now, K-12 IT professionals have been slow to adopt protections against ransomware, but the data makes it clear that this is no longer tenable. If your school has not yet suffered an attack, it really is just a matter of time. Criminals have many ways to infect school networks with ransomware—an unprotected RDP (remote desktop protocol) port, a phishing email, an unprotected web form, an infected thumb drive—and new methods are being developed all the time. 100% By far the most common vector is email, typically a sophisticated phishing email. RDP (remote desktop protocol) Phishing email Web applications Infected thumb drive Exploit kit Malvertising Compromised websites Ransomware can infect school networks in many ways. 0% 1 Cybercrime Tactics and Techniques: Ransomware Retrospective, August 2019 2 https://www.infosecurity-magazine.com/news/hundreds-of-us-schools-hit-by/ Barracuda Networks • SOLUTION BRIEF • Ransomware: Prevention and Recovery in K-12 Environments Effective ransomware protection requires a three-pronged approach: 1. -

How Schools and Libraries Can Get CIPA Compliance Help Meeting Federal E-Rate Requirements Is Quick and Easy with Barracuda’S Cloudgen Firewall
How Schools and Libraries Can Get CIPA Compliance Help Meeting federal E-Rate requirements is quick and easy with Barracuda’s CloudGen Firewall. NETWORK AND APP SECURITY How Schools and Libraries Can Get CIPA Compliance Help Meeting federal E-Rate requirements is quick and easy with Barracuda’s CloudGen Firewall. Summary Additionally, ISPs must use technology measures to prevent unauthorized access (or so-called “hacking”) and other unlawful • Compliance with the Children’s Internet Protection Act (CIPA) is activities by minors online, including unauthorized disclosure, use, mandatory for any school or library seeking federal funding. and dissemination of personal information regarding minors, and • Barracuda CloudGen Firewall is an easy, affordable, and top- restricting minors’ access to any other materials deemed harmful rated product for help in certifying CIPA requirements. to them. • Additionally, CloudGen Firewall provides best-in-class In short, CIPA demands a lot from school and library cybersecurity to keep your organization and users safe from administrators, in addition to any technology they choose to help costly digital attacks and fraud. certify and enforce the law. Before receiving any government funding, said technology must restrict and monitor online activity, block or filter inappropriate images from Internet-connected Introduction computers, and (for schools) provide reasonable public notice At the turn of the century, Congress passed the Children’s and education on internet safety. Internet Protection Act (CIPA) into United States law. Five years after the world wide web went mainstream, the legislation was enacted to address and restrict access to offensive content over CIPA demands a lot from school the Internet from school and library computers. -

Health Information Security in the Age of Ehrs and the 3Rd Platform Learn More White Paper
Health Information Security in the age of EHRs and the 3rd Platform White Paper Barracuda • Health Information Security in the age of EHRs and the 3rd Platform Introduction The last time Health Information Technology (HIT) changed this quickly was when barcoding was introduced to HIT networks in the 1990s. While the federal government pushes adoption of Electronic Health Records (EHRs), patient engagements are migrating to smartphones, tablets, and social media. Healthcare providers are also using cloud computing to analyze “big data” collected about treatments and procedures. Together “big connectivity” and cloud computing along with social media are being hailed as the “3rd Platform;” the successors to mainframe and client-server computing architectures. The challenge is how to add EHRs and 3rd Platform services to HIT mainstay services like email, Web access, and other applications while maintaining privacy for HIPAA compliance in today’s high-risk environment. As evidence of today’s risk, the Department of Health and Human Services’ Office for Civil Rights reported that 2016 was a record-breaking year, with more data breaches reported since they started publishing healthcare data breach summaries in 2009.1 Since 2002, Barracuda Networks’ strategy has been to protect and simplify diversifying IT infrastructures by converging security, performance optimization, and data loss prevention (DLP) features in solutions that are easy to deploy and manage. This white paper deals with the security and DLP issues facing IT professionals in the healthcare industry and how Barracuda technology addresses these issues. EHRs: Security, Storage, and Compliance Three issues to consider when you deploy EHRs are: avoiding data breaches by blocking cyber- attacks on the EHR application, demonstrating “meaningful use” of EHRs for certification, and providing safe, economical backups for a fast-growing volume of EHR data. -

White Paper Barracuda • Comprehensive Email Filtering
Comprehensive Email Filtering White Paper Barracuda • Comprehensive Email Filtering Email has undoubtedly become a valued communications tool among organizations worldwide. With Spam History frequent virus attacks and the alarming influx of spam, email loses the efficiency to communicate. Spam Spam is one form of abuse messages represent the vast majority of email traffic on the Internet. Spam is no longer a simple annoyance; of the Simple Mail Transfer it is a significant security issue and a massive drain on financial resources. Protocol (SMTP), which is implemented in email systems This is simply astounding and unacceptable. It’s time to take control of spam and virus attacks. on the basis of RFC 524. First proposed in 1973, RFC 524 was Filtering Email in Two Advanced Processes developed during a time when computer security was not a Today, there are a number of solutions designed to help alleviate the spam problem. Barracuda Networks significant concern. As such, designed the affordable Barracuda Email Security Gateway as an easy-to-use, enterprise-class hardware and RFC 524 is no longer a secure software solution for businesses of all sizes that comprehensively evaluates each email, using two main command set, making it and classes of sophisticated algorithms and techniques: Connection Management and Mail Scanning. SMTP susceptible to abuse. During the connection management process, emails are filtered through five defense layers to verify Most spam-making tools authenticity of envelope information, and any inappropriate incoming mail connections are dropped exploit the security holes in even before receiving the message. Any emails that survive the connection verification process must then SMTP. -

Ransomware Protection Checklist 3
Ransomware attackers are increasingly employing RANSOMWARE more sophisticated attacks and defeating existing PROTECTION defenses. Use this checklist to develop an effective CHECKLIST protection plan for your organization. 1. Protect your email. Ransomware attacks often start with a phishing email to capture admin or user credentials. 1a Block phishing attacks Attackers use social engineering tactics to bypass traditional email security. Use an email security solution that includes AI-enabled phishing and account takeover protection, as well as alerts when malicious activities are detected. 1b Train users Your users are your last line of defense against phishing attacks. Training needs to be an ongoing effort, as attacks often become more sophisticated over time. 1c Implement remediation Email attacks that evade email security and land in users’ inboxes need to be addressed quickly. Choose an email security solution that enables proactive threat discovery and automates remediation. 2. Secure your applications. Attackers hack your web applications to gain access to your data. 2a Protect web applications Applications often have open vulnerabilities that can be exploited to gain access to your data. Use an application security solution that defends against web application vulnerabilities such as OWASP Top 10, zero-day and brute force attacks. 2b Protect access to applications For internal applications, you should only allow access for authorized users and devices. Choose a zero trust access solution that enables role based access, multi-factor authentication and continuous verification of user and device identity. 2c Prevent lateral movement on your network If attackers gain access to your network, they often attempt to move laterally to find and infect data sources. -

White Paper Barracuda Networks Automating the Backup Process
Automating the Backup Process White Paper Barracuda Networks Automating the Backup Process Value RELEASE 1.1 Explosive increases in the quantity of data in digital format (i.e., email, faxes, application data, documents, and media files) is fueling small businesses and large enterprises to need data storage and backup technology like no other time in the history of the electronic age. Despite a sharp increase in affordability and availability of automated backup systems, many businesses still rely on unsecure tape devices to backup and restore vital information. Further, management may not fully appreciate the risk they take by neglecting backups in favor of 1 “The Changing Dynamics “more important” issues. Any non-expert can observe that data loss frequently occurs even with a of Backup and Recovery backup system in place. According to a 2004 Enterprise Storage Group survey, nearly one in four SMBs in the Small and Medium reported that at least 20 percent of their recovery attempts fail.1 Cited as the primary cause for data Business (SMB) Market,” John McKnight, loss: human error—in the backup process, or in the interchange and handling of tapes. The Enterprise Storage Group, June 2004. Automation is the “automatically controlled operation of an apparatus, process, or system by 2 mechanical or electronic devices that take the place of human labor.” Automation is widely 2 “automation” understood to be beneficial but perhaps misunderstood to be costly or difficult to implement or both. Merriam-Webster Online Dictionary. 2009. The Story Merriam-Webster Online. 25 June 2009 The following article, written for a Home Care Automation Report about healthcare providers, <http://www.merriam-webster. -

IP Reputation-Based Filters
Barracuda Web Application Firewall IP Reputation-Based Filters https://campus.barracuda.com/doc/4259852/ Overview In order to prevent geographically distributed DoS attacks that span multiple subnetworks, the Barracuda Web Application Firewall provides an IP reputation-based filter that can be applied to an entire geographic region or collection of regions spanning multiple countries and/or continents. This feature is available only in firmware version 7.7 or higher. You can configure a geo pool with one or more geographic regions and allow or deny requests from it. IP addresses can be filtered based on the following categories: Geo Pool – The IP address is from an included geographic region. Barracuda Reputation Blocklist – The IP addresses that are identified as potential originators of spam, malware, and bots. TOR Nodes – The IP addresses that are identified as TOR. Anonymous Proxy – The IP address is from an anonymizer that hides the IP address of the requesting client. Satellite Provider – The IP address is from a Satellite Internet Service Provider (ISP) so the IP address of the requesting client is unknown. Anonymous Proxy and Satellite Provider IP addresses are not specific to geographic regions. IP addresses are compared to the MaxMind database to determine if the requester is a known anonymizer or ISP address. Once a geo pool is created, it can be associated with one or more services using the IP Reputation Filter section on the WEBSITES > IP Reputation page. An IP Reputation Filter policy can be applied at the Network Layer or Application Layer. When set to Network Layer, the Barracuda Web Application Firewall applies the IP Reputation policy at the network layer.